IP Reputation Report-12232019

December 26, 2019
-
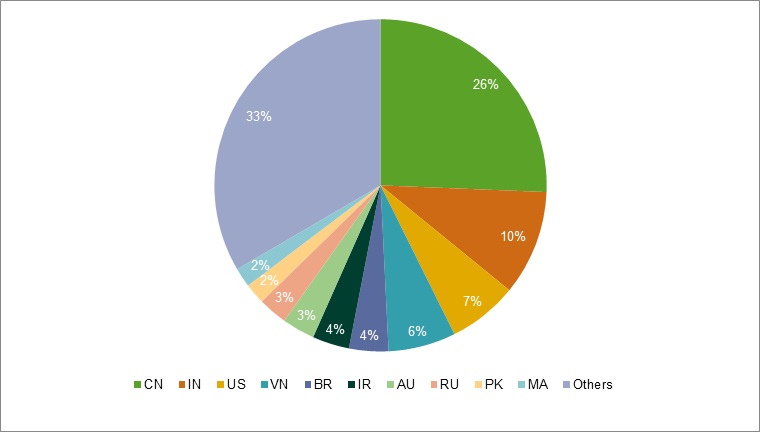
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at December 23, 2019.
Cybersecurity Insights-10

December 25, 2019
5.3.2 Attack Type Distribution
In 2018, the most frequent attacks seen814 were SYN flood, UDP flood, ACK flood, HTTP flood and HTTPS flood attacks, which altogether accounted for 96% of all DDoS attacks. In contrast, reflection attackers contributed to no more than 3% of attacks. Compared with 2017, the year 2018 witnessed a 80% decrease in the number of reflection attacks, but a 73% increase in other attacks. This is because of effective governance measures taken against reflectors. (more…)
Advisory: Gitlab EE multiple high-risk vulnerabilities

December 24, 2019
Vulnerability Description
On December 10, 2019 local time, GitLab officially released an important version update notice, announcing three high-risk vulnerabilities in GitLab EE (Enterprise Edition). GitLab is an open source and web-based Git-repository management project. (more…)
Advisory: Two high-risk vulnerabilities in GoAhead web server
December 23, 2019
Vulnerability Description
On December 2, 2019, Cisco Talos publicly released reports of a remote code execution vulnerability (CVE-2019-5096) and a denial of service vulnerability (CVE-2019-5097) for the GoAhead web server. GoAhead is an open source, simple, lightweight, and powerful embedded Web Server. It is a Web server tailored for embedded real-time operating systems (RTOS) and can run on multiple platforms. (more…)
VMware ESXi Remote Code Execution Vulnerability (CVE-2019-5544) Threat Alert

December 20, 2019
Overview
On December 5, local time, VMware officially released a security advisory that revealed a remote code execution vulnerability (CVE-2019-5544) in VMware ESXi and Horizon DaaS. The vulnerability is due to a heap overwrite issue in OpenSLP used in ESXi and Horizon DaaS appliances. Malicious users with access to port 427 on the ESXi host or any Horizon DaaS platform through the network may overwrite the heap of the OpenSLP service, eventually causing remote code execution. (more…)
IP Reputation Report-12152019

December 19, 2019
-
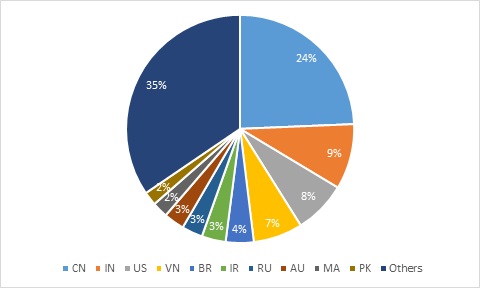
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at December 15, 2019.
Cybersecurity Insights-9

December 18, 2019
5.3 DDoS Attacks
5.3.1 Attack Trend
In 2018, we observed 148,000 DDoS attacks (down 28.4% from 2017), which generated a total of 643,100 TB of attack traffic, about the same volume as observed in 2017. This trend suggests that
while the number of DDoS attacks is lower, the size of the attack are growing. Large and medium-size attacks are on the rise.
Harbor Multiple Vulnerabilities Threat Alert

December 17, 2019
Overview
Today, VMware released five vulnerabilities for Harbor Container Registry, including two officially classified as critical vulnerabilities (CVE-2019-19025, CVE-2019-19023), and two high-risk vulnerabilities (CVE-2019-19029, CVE- 2019-19026), and a medium-risk vulnerability (CVE-2019-3990). (more…)
SDN-based Intelligent DDoS Cleaning System

December 16, 2019
Traditional DDoS protection solutions are designed to address flexibility, scheduling, and value addition requirements. However, the advent of the software-defined networking (SDN) technology, especially its combination with network virtualization, provides a new way to deploy security devices. NSFOCUS’s SDN-based intelligent cleaning system discussed here can intelligently detect DDoS attacks and work out an optimal cleaning policy before selecting the most appropriate cleaning resources in real time, thus implementing intelligent traffic cleaning on demand to effectively protect users from DDoS attacks. (more…)
Information Security in the Workplace- Business Chat Groups-v
December 13, 2019
With the advancement of IT-based transformation and the rapid development of IT, various network technologies have seen more extensive and profound applications, along with which come a multitude of cyber security issues. Come to find out what information security issues you should beware of in the workplace. (more…)