Continuous Threat Exposure Management
Stay Ahead of Evolving Cyber Threats by Continuously Monitoring and Managing Your Exposure to Potential Attacks
CTEM
Continuous Threat Exposure Management
CTEM is a set of processes and capabilities for identifying, assessing, and mitigating risks within an organization’s digital environment. By adopting this strategy, organizations of all sizes can stay ahead of evolving cyber threats by continuously monitoring and managing their exposure to potential attacks, thus enhancing their overall security posture.
Proactively and predictively defend against threats
Inventory all digital assets and critical assets
Prioritize risks
Improve resilience and reinforce overall security
Get insights with evidence for making the right security decisions
Tools and Technologies Used in CTEM
CTEM requires a consolidated platform that integrates the necessary tools and technologies to streamline the entire process.
The following tools and technologies can be used to support the implementation and improvement of a CTEM program in the five stages:
- Scoping
- Discovery
- Prioritization
- Validation
- Mobilization
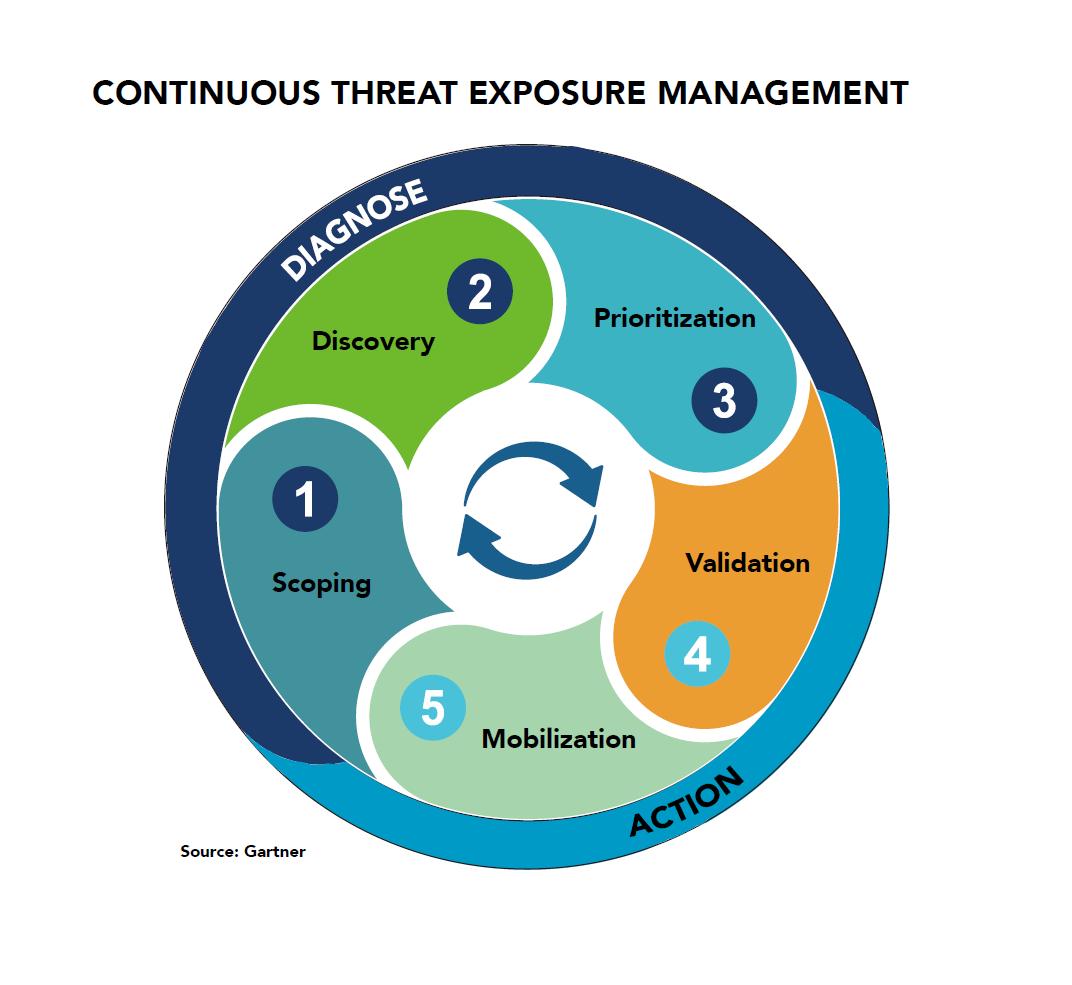
DIAGNOSE
NSFOCUS Offering
CTEM Value
NSFOCUS Offering
- CAASM – Cyber Asset Attack Surface Management
- EASM – External Attack Surface Management
- EM – Exposure Management
- RSAS – Remote Security Assessment System
- DRPS – Digital Risk Protection Service
- WebSafe
- Source Code Review
- VA – Vulnerability Assessment
- Configuration Verification
- VPT – Vulnerability Prioritization Technology
CTEM Value
- Identify your most valuable assets and data. By identifying the critical assets and data, organizations can prioritize their resources and focus their efforts on the areas that are most at risk.
- Gather data from all of your systems and networks. By collecting data from a variety of sources, organizations can get a more complete view of their security posture and identify threats that may not be detected by individual security products.
- Identify the threats that pose the greatest risk to your organization. By prioritizing threats based on their likelihood and impact, organizations can make the most of their resources and focus their efforts on the threats that pose the greatest risk
ACTION
NSFOCUS Offering
CTEM Value
NSFOCUS Offering
- BAS – Breach and Attack Simulation
- EM – Exposure Management
- PTaaS – Penetration Testing as a Service
- Red Teaming
- IR – Incident Response
- Consulting Service
- Security Awareness Training
CTEM Value
- Confirm that the threats you’ve identified are real and pose a risk to your organization. By validating threats, organizations can avoid wasting time and resources on threats that are not real or that do not pose a risk.
- Take action to mitigate the threats you’ve identified. By taking action to mitigate validated threats, organizations can reduce their risk of being attacked.
SECURITY MADE SMART AND SIMPLE
SEE HOW OUR SOLUTIONS PROTECT YOUR CUSTOMERS AND YOUR INFRASTRUCTURE
