IoT Agenda - I am known for railing against IoT devices because I consider them the eventual destroyers of the internet as we know it. They are not secure, most people that use them do not realize they are not secure, and most vendors that make them have done little...
Category: NSFOCUS in the News
HelpNetSecurity: The correlation between DDoS attacks and cryptomining
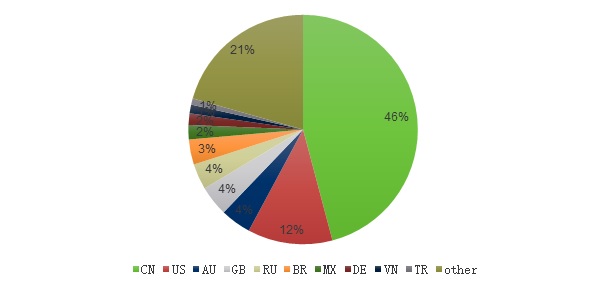
HelpNetSecurity - In NSFOCUS’ 2018 DDoS Attack Landscape report, NSFOCUS analyzed the threat landscape after a landmark year of technological growth related to cloud computing, big data, artificial intelligence (AI), Internet of Things (IoT), and Industry 4.0.
OODA Loop: The correlation between DDoS attacks and cryptomining
OODA Loop - A new NSFOCUS report indicates that the declining price of cryptocurrencies in 2018 prompted threat actors to stop using botnet resources for cryptomining attacks – as these were getting less and less profitable – and increasingly use them to launch distributed denial-of-service (DDoS) attacks instead.
The CyberWire: The Daily Briefing
The CyberWire - CISA has issued a joint Homeland Security/FBI Malware Analysis Report on the "HOPLIGHT" Trojan, attributed to North Korea's Hidden Cobra (a.k.a. the Lazarus Group). - See more at: https://thecyberwire.com/issues/issues2019/April/CyberWire_2019_04_11.html#.dpuf
Trouble at the federal CIO’s office
Politico - THE SAUCE ON DDoS — With cryptomining benefits on the decline, cyber attackers were more inclined to employ DDoS attacks in 2018, according to a report out this morning from NSFOCUS. However, the total number of DDoS attacks fell 28 percent from 2017, the company found. Most used...
NSFOCUS Unveils New DDoS Mitigation Solution with Contextual Analysis
Cyberwire - RSAC's 2019 edition of its Innovation Sandbox was held yesterday, with ten of the security sector's most interesting start-ups on display. NSFOCUS, a leader in holistic hybrid security solutions, today unveiled Attack Threat Monitoring, which provides real-time insights and contextual awareness of the global DDoS threat landscape.