ICS Information Security Assurance Framework 16

February 11, 2020
System Introduction
The computer monitoring system of the hydropower plant adopts a hierarchical distributed open system structure totally controlled by the computer, which consists of the main control layer of functions and the local control unit (LCU) layer of objects. The main control layer consists of the operator station, data server station, external communication station, internal communication station, engineering station, voice alert station, GPS time synchronization system, UPS power supply, and network devices. (more…)
ICS Information Security Assurance Framework 15

February 10, 2020
Wind Power
System Introduction
Based on computers, communication devices, and test control units, the wind power monitoring system provides a basic platform for real-time data collection, switch status monitoring, and remote control of wind power plants. It can work with detection and controls devices to form an arbitrarily complex monitoring system. It plays a vital role in the monitoring of wind power plants by helping enterprises eliminate information silos, reduce operating costs, improve production efficiency, and accelerate the speed of responding to anomalies in the process of power transformation and distribution. Figure 4.4 shows its system architecture Currently, the electric power monitoring system is vertically connected to dispatching planes 1 and 2 and the centralized control center of the wind power plant. (more…)
ICS Information Security Assurance Framework 14

February 7, 2020
ICS Security Solutions for Typical Industrial Scenarios
System Introduction
Based on computers, communication devices, and test control units, the electric power monitoring system provides a basic platform for real-time data collection, switch status monitoring, and remote control of thermal power plants. It can work with detection and controls devices to form an arbitrarily complex monitoring system. It plays a vital role in the monitoring of thermal power plants by helping enterprises eliminate information silos, reduce operating costs, improve production efficiency, and accelerate the speed of responding to anomalies in the process of power transformation and distribution. (more…)
IP Reputation Report-02022020

February 6, 2020
-
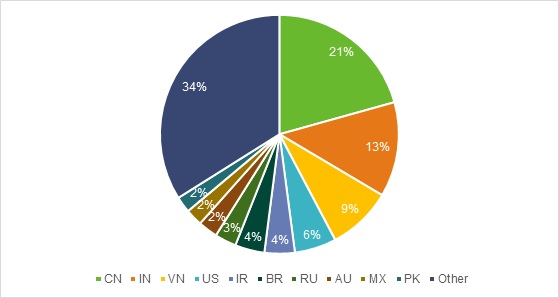
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at February 2, 2020.
ICS Information Security Assurance Framework 13

February 5, 2020
Policies for Building the Defense-in-Depth System for Industrial Control Networks
For the sake of ICS security protection, we can build a defense-in-depth system by implementing the following policies:
ICS Information Security Assurance Framework 12

February 4, 2020
ICS Information Security Assurance Framework
ICS Security Assurance Principles
In response to related compliance requirements put forward by the industry and the country, the ICS information security assurance framework will be developed to combine both technology and management, taking full account of the enterprise’s business requirements and ICS operating characteristics. By switching ICS protection from deployment of security policies to that of security capabilities, such a framework aims to enable an all-around improvement in security technology and management capabilities for the purpose of integrating management, control, and defense. With this framework, enterprises’ security capabilities will gradually cover system go-live, operating, O&M, and inspection, achieving closed-loop security control and management for ICSs. (more…)
ICS Information Security Assurance Framework 11

February 3, 2020
2.4 ICS Security Trend
All in all, with IT and OT converging at a rapid pace, ICSs will be exposed to more threats that are evolving faster and faster. The threat evolution is reflected in the following aspects: (more…)
ICS Information Security Assurance Framework 10

February 2, 2020
2.3.2 ICS Vulnerability Trend
As industrial control has been delving deeper in recent years, more and more ICS vulnerabilities are discovered by researchers. As vulnerabilities publicly available are only a small portion of those hidden in ICSs, the possibility of ICS vulnerabilities being stashed as potential cyber weapons cannot be ruled out. The following sections analyze the trend of ICS vulnerabilities by reference to data publicly available. (more…)
ICS Information Security Assurance Framework 9

February 1, 2020
2.3 Vulnerabilities in ICS Assets
Most ICS security mechanisms are short of authentication, encryption, and audits, and therefore such ICS assets are rather vulnerable. When connecting to the Internet, ICSs are susceptible to external probes or identification via special fields included in information returned through public or private communication protocols, web services, telnet, and FTP. In this way, ICS assets can be easily controlled by attackers. In addition, more and more ICS vulnerabilities are identified by researchers, leaving ICS assets exposed on the Internet rather vulnerable. (more…)
Microsoft Security Update for January 2020 Fixes 49 Security Vulnerabilities
January 31, 2020
Overview
Microsoft released the January security update on Tuesday, fixing 49 security issues ranging from simple spoofing attacks to remote code execution, discovered in products like .NET Framework, Apps, ASP.NET, Common Log File System Driver, Microsoft Dynamics, Microsoft Graphics Component, Microsoft Office, Microsoft Scripting Engine, Microsoft Windows, Microsoft Windows Search Component, Windows Hyper-V, Windows Media, Windows RDP, Windows Subsystem for Linux, and Windows Update Stack.
(more…)