ICS Information Security Assurance Framework
ICS Security Assurance Principles
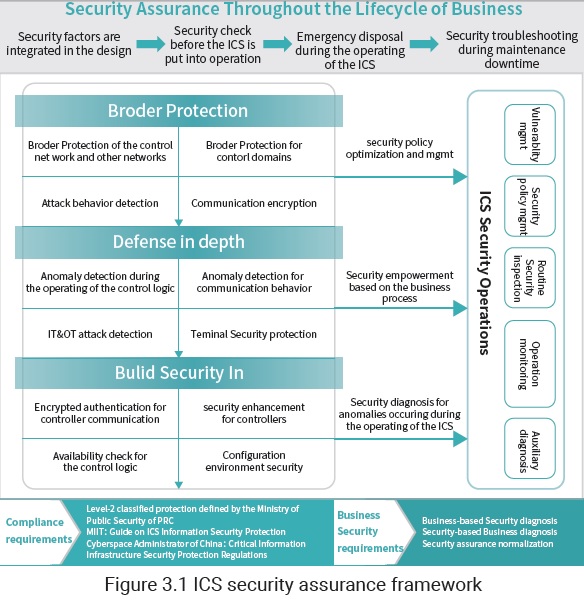
In response to related compliance requirements put forward by the industry and the country, the ICS information security assurance framework will be developed to combine both technology and management, taking full account of the enterprise’s business requirements and ICS operating characteristics. By switching ICS protection from deployment of security policies to that of security capabilities, such a framework aims to enable an all-around improvement in security technology and management capabilities for the purpose of integrating management, control, and defense. With this framework, enterprises’ security capabilities will gradually cover system go-live, operating, O&M, and inspection, achieving closed-loop security control and management for ICSs.
Working Principle of the ICS Information Security Assurance Framework
ICS security development should be conducted in line with compliance requirements while addressing business security requirements. For this reason, ICS security should run through the entire business lifecycle, including incorporating security requirements into system development, conducting security inspection before the system goes live, responding to incidents during system operation, and performing security troubleshooting during maintenance downtime. As industrial environment security is an objective existence, an efficient ICS security protection system needs to be built to provide robust security support.
Building an efficient ICS protection system covers three aspects: border protection, defense in depth, and Build Security In. Border protection requires security isolation between different zones. For instance, borders between OT and IT can be isolated using a security device like an industrial firewall or a GAP. Defense in depth should take full account of effective protection for connections between controllers in the controller connection domain to make sure that the communication process is controllable.
Sound security monitoring and protection measures should be deployed within the ICS to make it controllable and manageable and its monitoring results visual to users. The control logic needs to match the business profile. Efficiently perceiving behavior in the communication process, the deployed security measures can promptly discover and deal with known attack behavior and perceive what system anomaly is caused by unknown attack behavior, thus providing data support for system failure locating. Security technologies such as industrial invasion detection, industrial anomaly monitoring, and sandboxing should be employed for effective monitoring of communication traffic and files in the system, as well as various terminals such as industrial hosts, industrial databases, and OPC servers.
Build Security In should place emphasis on security reinforcements of firmware in controllers, including encrypting the firmware, checking the availability of control instructions, taking account of the selfcorrection of configuration software during the configuration process, so as to increase the security level of ICSs.
When it comes to security operations, this framework needs to meet the following requirements: reducing security risks for production enterprises while helping them increase the operation efficiency of production systems; addressing business security requirements to ensure that business is done in a compliant and continuous way; improving enterprises’ comprehensive business security capabilities on the basis of compliance assurance; incorporating security throughout the lifecycle of business.
Border Security Protection
Guidance on ICS Border Protection Provided by a Guide from MIIT
As the Guide on ICS Information Security Protection is released by MIIT, ICS security is raised to a new height. This guide indicates that industrial enterprises should do a good job in ICS security protection from 11 aspects. This guide expounds on border protection, a key section of ICS security control, as the third aspect, noting that borders between the industrial control network and the enterprise network or Internet should be protected by ICS network border protection devices, for instance, deploying an industrial firewall or GAP to logically isolate security zones of the industrial control network. So, to speak, this guide provides constructive suggestions on ICS border protection from an industry perspective.
Guidance on Border Protection of the Electrical Power Sector
The National Development and Reform Commission (NDRC) released the Provisions on the Security Protection of the Electric Power Monitoring Systems as early as in 2014 to normalize security protection of ICS systems of electrical power enterprises, making this industry a pioneer in ICS security.
In early 2015, the National Energy Administration issued a document (NEA No. 36) to further set forth ICS
security compliance requirements of electric power enterprises, putting forward security protection solutions and security assessment specifications for provincial electricity distribution, prefectural electricity distribution, power distribution networks, power generation plants, and substations. Both No. 34 and No. 36 documents push forward ICS security protection of electrical power enterprises.
Revolving around security zone division, dedicated network building, horizontal isolation, and vertical encryption, the two documents put emphasis on border security. The subsection for security of borders between the control zone (security zone 1) and non-control zone (security zone II) specifies that a network device that provides the access control function, a secure and reliable firewall hardware device, or a security device that provides similar functions can be deployed at the border of both zones to implement logical isolation, packet filtering, and access control. The inter-system security protection subsection specifies that logical access control measures of a certain strength should be taken between different systems in either security zone 1 or security zone 2. In these security protection scenarios, industrial firewalls, isolation devices, or VLAN technology can be deployed to meet compliance requirements while ensuring business continuity, delivering satisfactory border security protection for ICSs of electrical power systems.
Guidance on Border Protection of the Petrochemical Industry
In the petroleum and petrochemical industry, Chinese National Petroleum Corporation and Sino Petroleum Corporation have released the Outline of the Thirteenth Five-Year Plan to clarify the importance of ICS security. For instance, an ICS system network on an oil field, which covers the wellhead, stations, pipelines, and related facilities on the oil production field, is used for real-time production data collection, remote control, and automatic control. This network is susceptible to external attacks as it has a wide coverage, including many devices that are deployed in the wild and use multiple networking methods such as cable and wireless. Ensuring that the ICS can operate in a secure way is a fundamental purpose for protecting security of the industrial control network on an oil field.
For the industrial control network of an oil field, a key issue to solve is how to prevent theft, corruption, or tampering of business information, especially instructions, in a bid to stop hackers or malware from using a remote device or an internal LAN terminal to attack devices deployed on the industrial control network in the oil field. Security risks in these information infrastructures can be resolved by deploying an industrial firewall or GAP, thus ensuring that the industrial control network on the oil field can operate in a secure and stable way.
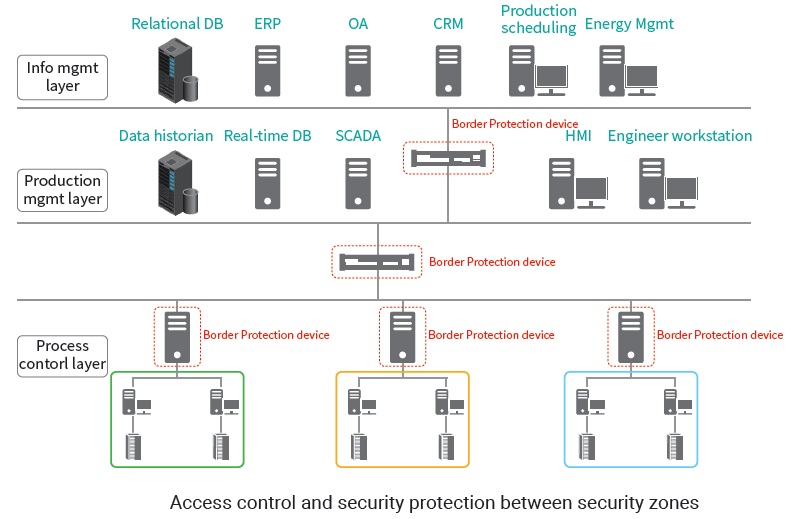
Access Control and Security Protection Between Security Zones
Firewalls are deployed between different layers of network to control cross-layer access and implement deep sanitization of inter-layer data exchanges, preventing attackers from penetrating into or attacking a lower-layer network from an upper-layer one.
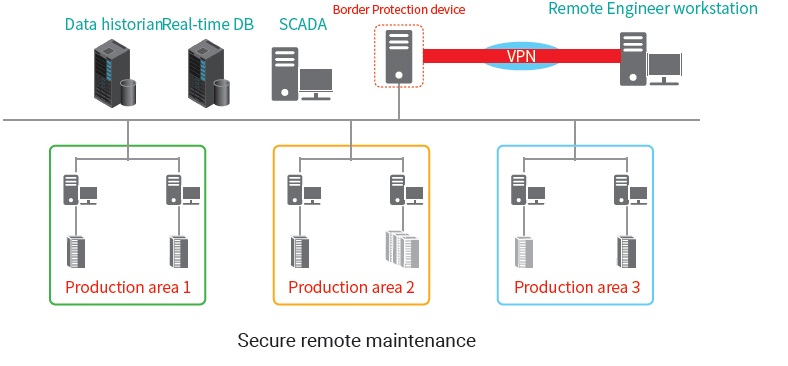
Security-Aware Remote O&M Management
Deploy a firewall at the border between the industrial network and the public network and enable the VPN function on the firewall to use it as a bastion device for remote maintenance. Remote maintenance personnel connect to the firewall through the VPN to perform identity authentication and implement encrypted protection for remote maintenance operations performed through the public network, thus achieving secure remote maintenance.
To be continued.