Written By:
Bruno Carvalho
System Engineer UK & Western Europe
Firstly, to become this information clearer is interesting to answer the question…What is GPRS Tunneling Protocol (GTP)?
GPRS Tunneling Protocol (GTP) is a 2.5G technology that provides interconnection between various network interfaces, enabling mobile users to roam seamlessly between networks of different generations. The GTP protocol is a tunneling protocol defined by the 3GPP standards to carry General Packet Radio Service (GPRS) within 3G/4G networks even part
of 5G networks as well. As the GPRS packet-oriented mobile data standard is integrated into GSM (G2) that allows mobile networks to transmit IP to external networks (i.e., the internet).
Also, the GPRS is the mobile communications service that enables SMS, MMS, IM, WAP, peer-to-peer, smartphone internet apps, and more.
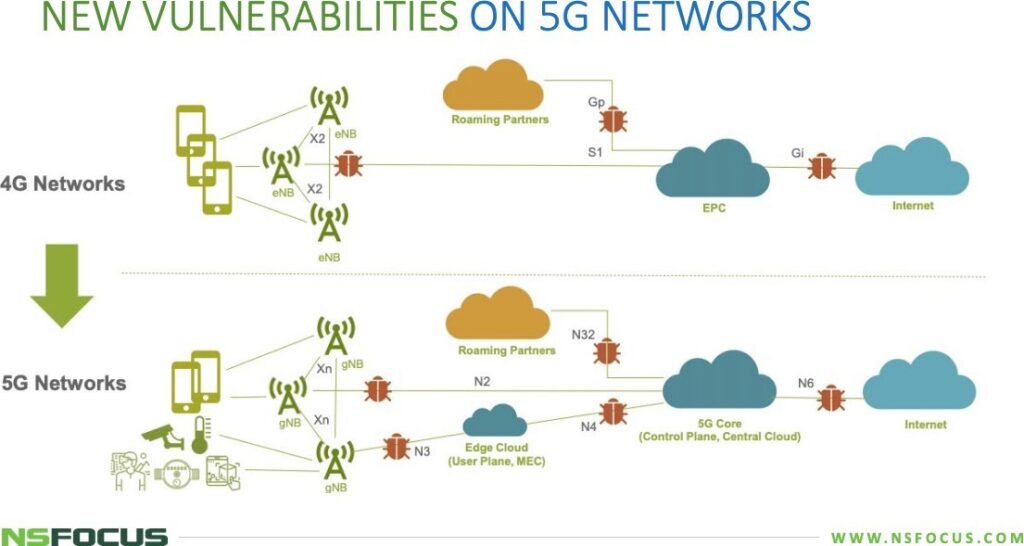
As with any complex network, 5G networks tend to have vulnerabilities and the GTP protocol is fundamentally flawed in that it does not check the user’s actual location, which is behind half of the successful attacks.
Testing confirmed that GTP vulnerabilities can be exploited via the inter-operator IPX network, and in some cases even from a mobile device, with adverse impacts on EPC.
One of the main flaws in the GTP protocol is that it does not check a user’s location, an attacker can use this flaw to send malicious traffic which the home network has trouble identifying the legitimacy of; subscriber credentials are also checked on S-GW (SGSN) equipment by default, which can be mimicked by an attacker to steal data, the security firm said in a new report. Obviously that 5G networks promise download speeds 10 to 20 times faster than legacy networks. In some instances, ensuring their confidentiality, integrity and availability will be a matter of national security.
The new 5G core, as defined by 3GPP, utilizes cloud-aligned, service-based architecture (SBA) that spans across all 5G functions and interactions including authentication, security, session management and aggregation of traffic from end devices.
Unfortunately, 5G networks are deployed on the Evolved Packet Core (EPC) which was also used to establish the 4G Long-Term Evolution network, it means as the increased use of 5G vastly growing a fast-paced the damage an attack such as a denial of service attack could do.
Additionally, cyber criminals have increased their capabilities, leveraging automation and cloud tools to easily weaponize Internet of Things (IoT) and other mobile devices to attack both from within the network and via the Internet. Once inside, cyber criminals can exfiltrate sensitive customer data, eavesdrop on subscribers, compromise core resources and even bring down the entire network.
Basically, the Gi Firewall & GTP Inspection are responsible to ongoing monitoring and analysis of signaling traffic to detect potential security threats that comes from Internet.
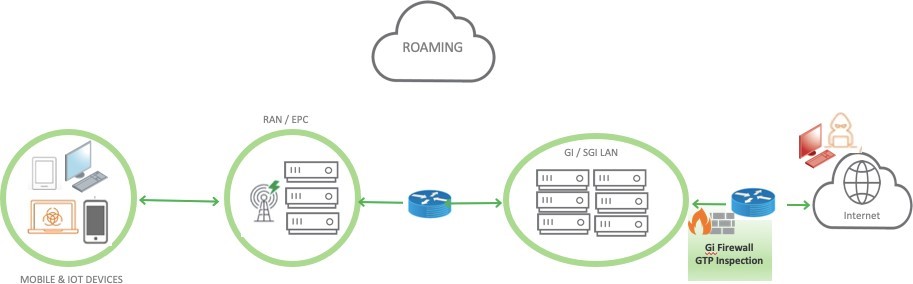
However, when it comes to roaming, GTP connects the local (home) and visited network, allowing subscribers to shift between networks easily. Its extensive use between mobile networks (e.g, roaming) makes GTP an attractive target for attackers. Be prepared only to provide a protection of internet points definitely isn’t good enough.
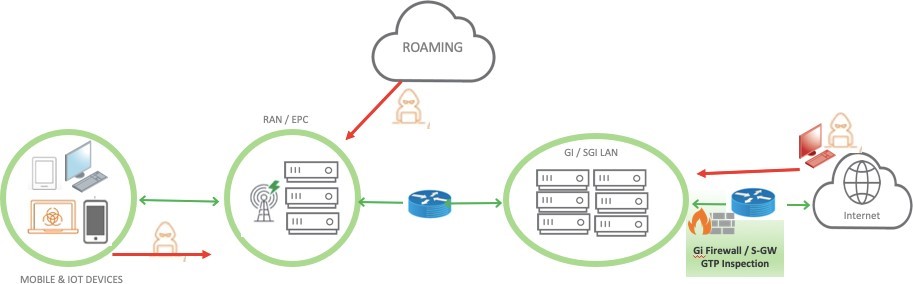
Gathering more about the Roaming IoT — Inefficient and unprotected IoT devices create security risks and can cause an exponential increase in network signaling traffic when deployed on a massive scale. Signaling storms can be caused by botnet-driven DoS attacks or triggered by power failures, natural disasters, and coverage problems in a given service area.
When roaming smart meters and IoT endpoint devices lose connectivity, they attempt to roam to another network. Numerous, simultaneous roaming requests create signaling storms that can bring a mobile network down.
Also, the 5G network architecture will incorporate emerging techniques, including network slicing, software-defined network (SDN), network functions virtualization (NFV), and edge computing.
SDN and NFV enables building of logically isolated network slices to support differentiated requirements of the preceding 5G usage scenarios. However, this also adds to the challenge of securing networks because it blurs their boundaries, rendering previous security mechanisms relying on physical perimeter protection useless. That is why we say that a new security mechanism is in urgent need to meet virtualization and cloud-based development requirements.
However, to provide the EPC protection have a feasible option is to use virtual anti-DDoS products to effectively protect the edge data center from both network-layer and application- layer attacks and at the same time to ensure fast response of the defense process. These devices will be located at the egress of the core data center to filter out DDoS attack traffic before such traffic reaches application services.
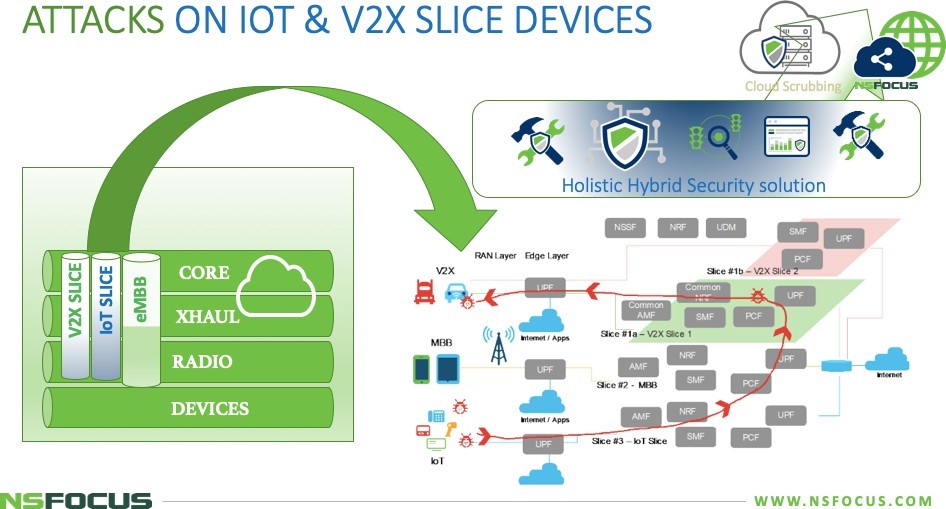
On the 5G networks are observed a new concept that emerges to allows mobile operators to create unique network “slices†(independent networks running on top of the shared mobile infrastructure) with their own unique security requirements to support diverse use-case scenarios (e.g., video conferencing, V2X applications). Named as Network Slicing Security, which provides mobile operators with segmentation capabilities that were not possible with previous generations.
Network slice is a complete logical network (providing Telecommunication Services and Network Capabilities) including Access Network (AN) and Core Network (CN). Network slicing enables the management of multiple logical networks as virtually independent business operations on a common physical infrastructure. In practice, this corresponds to the idea that the mobile network could be partitioned into a set of resources that might be virtual. Each one is called a “slice†that can be allocated for different purposes. To protect each slice of attacks such slice faking, CUPS hijacking, a DDoS solution should be inserted in order to elevate the protection and even adding multi-virtual DDoS systems being responsible to provide high-density of scalability and performance.
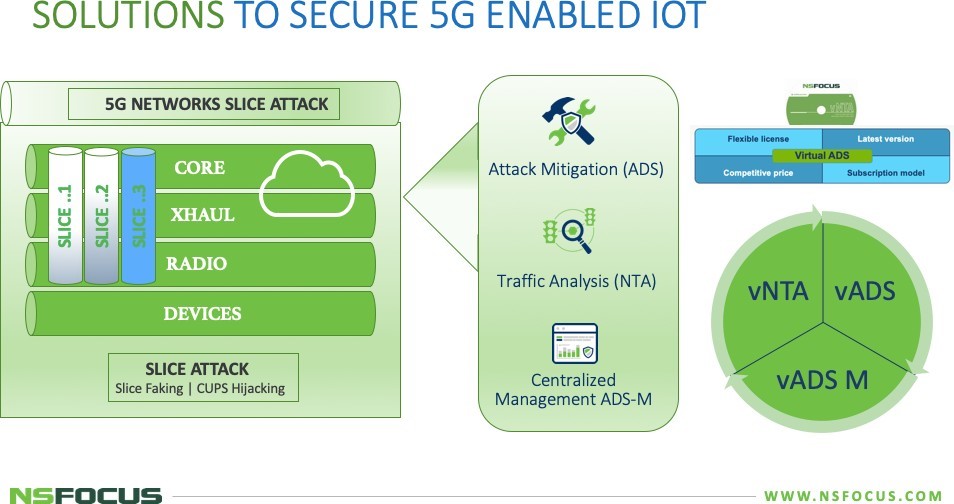
Each slice’s role as an isolated logical network or network part clearly needs state-of-the-art network security measures.
This may include measures such as: perimeter security and network, separation of different traffic types, intrusion and anomaly detection, the use of cryptographic traffic protection, etc. Slices allow security measures to adapt to the individual needs of the application(s) supported by that slice.
For example, an IoT slice may provide a different choice of authentication and/or encryption mechanisms than an eMBB slice. NSFOCUS elevate the security level to efficient DDoS mitigation, APT Detection, Vulnerability Management, Situation Awareness, Traceability analysis and Asset Management as demonstrate on the picture below.
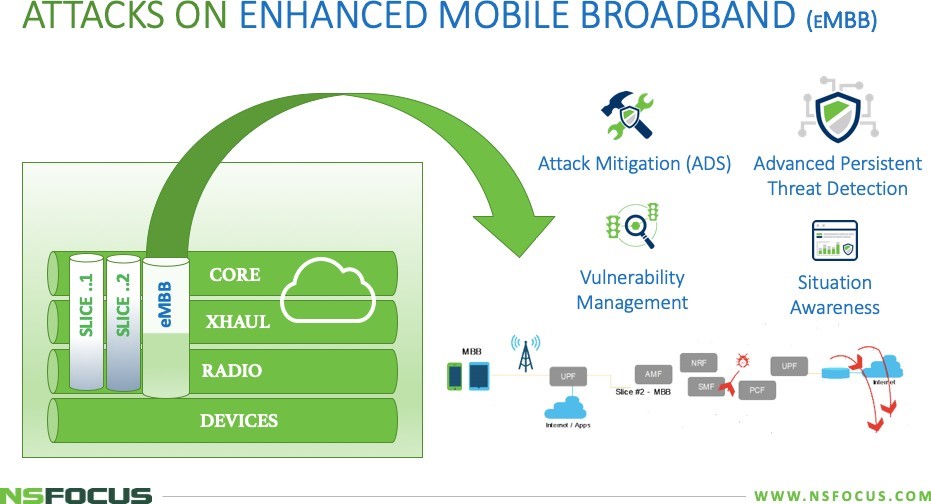
The attack could be multi-factored by allowing the malware to have the ability to deplete the resources of the slice, therefore causing DoS (Denial of Service) to the actual subscriber. An attacker may also exhaust resources common to multiple slices, causing denial of service or service degradation in other slices as well. This leads to severe degradation in the offered network services. As a cloud native architecture, 5GC (5G Core) has all the functions virtualized that provide the added flexibility required for network slicing.
On the picture below, it also explores how 5G differs from 4G and 3G in terms of radio and core network architectures, and how those differences affect the security mechanisms available to mobile operators, their business partners and their customers.
Different vectors and point of attacks are reachable now. Be prepared to protect the network against it and allowing the high 5G traffic could be cleaning and completely secure is the challenge. The new technology has bringing more exposure points.
Due to a large number of infected mobile devices, controlled by malicious Command and Control (C&C) servers, can launch both user plane and signaling plane attacks on 5G core network functions to degrade or make critical services unavailable for legitimate users.
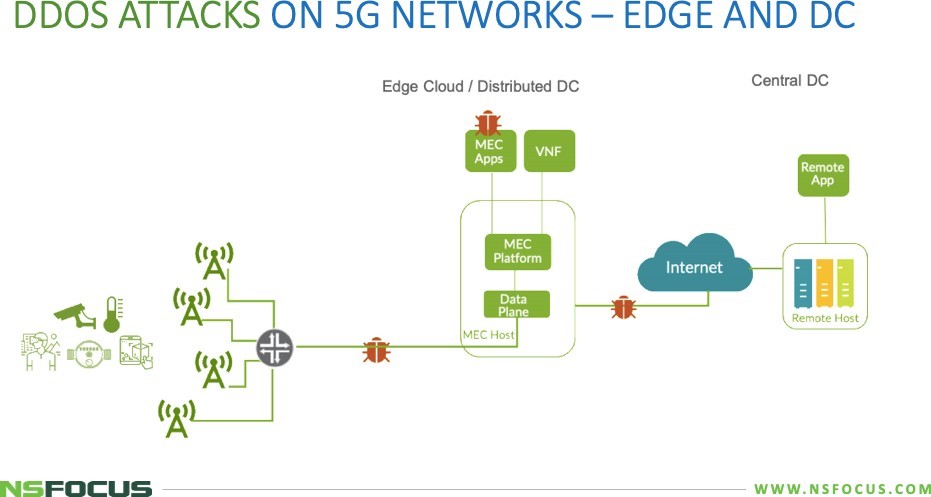
As conclusion, the mobile operators will need to deploy a GTP firewall to protect against GTP-based attacks coming in from access networks, roaming partners, IoT, and must have additional security platform to enabling the DDoS protection effectively based in multiple- virtual instances and that can be deployed in tenant side for customized policies; absorbing all application & attacks with a Tbps-level cleaning capacity.
In collaboration with cloud-based cleaning services, Gi/GTP-Firewalls the solution can filter out DDoS attack traffic to the best effect. Moreover, by incorporating a threat intelligence system, the solution can implement active defense to block source devices marked by the threat intelligence system as dangerous, nipping potential DDoS attacks in the bud and improving the DDoS protection efficiency.
NSFOCUS Threat Intelligence can be integrated with NTA (sensor) and ADS/vADS (mitigation).
For ADS (mitigation) is enabling to pull the latest IP reputation from the NSFOCUS Threat Intelligence System and consume the intelligence to remove the traffic from known botnets immediately. – TACTICAL INTEL
For NTA (sensor) on the other hand, leveraging the communication between device and NTI cloud, allows user to query and verify the anomaly traffic source for further information. – STRATEGIC INTEL.
