Key Findings – 4
DDoS Protection Techniques Need to Continue to Evolve with Emergence of New Attack Vectors
NXNSAttack, a new vulnerability in DNS, can be exploited to launch massive DDoS attacks
In May 2020, Israeli researchers reported a new DNS server vulnerability and dubbed it NXNSAttack. This vulnerability exists in DNS’s recursive resolution process. Unlike other DDoS attacks that directly target hosts or services, NXNSAttack targets victims’ domain name resolution capabilities. It exploits DNS recursive resolvers to initiate DNS lookup requests to a malicious DNS server, which returns crafted responses, resulting in DNS recursive resolvers sending a large number of requests to the victim DNS server. This can achieve the amplification factor of 1620, making the DNS server stop responding, that is, deny service to legitimate users. After the DNS server is attacked, new clients cannot find IP addresses connecting to the service and so cannot know the host names. Compared with common attacks targeting random domain names, this new type of attacks can leverage fewer resources to achieve the same effect while hiding their traces, making it impossible to obtain attack signatures from the composition of domain names.
RangeAmp attacks
In May 2020, researchers from China discovered a new type of DDoS amplification attacks, namely RangeAmp, which exploits the Range field in the HTTP header to initiate malicious requests. By amplifying traffic between content delivery networks (CDNs) or between CDN and the target server by thousands or even tens of thousands of times, RangeAmp will finally exhaust the bandwidth. Such exploit attacks cannot be mitigated with traditional protection algorithms (such as 302 redirect). Keyword-based policies can be used, but require continuous packet capturing, which often lags far behind the attack process. NSFOCUS ADS provides smart protection, which can automatically learn normal traffic’s patterns and extract attack fingerprints, enabling the device to generate policies against unknown abnormal traffic and automatically block attack traffic.
Alarm sounded for HTTP 2.0 DDoS attacks and CC 2.0 era around the corner
Execution of DDoS attacks relies on network protocols. The more widely network protocols are adopted, the more vulnerable networks are. Each layer of network protocols means an attack surface for DDoS attacks. The more complicated a network protocol is, the more diversified potential DDoS attack methods are. With the gradual adoption of HTTP 2.0 comes new HTTP attack threats. Since the protocol’s initial application, a slew of vulnerabilities have been reported. More and more studies have found that, different from previous CC attacks, new CC attacks and low-and-slow attacks based on HTTP 2.0 are more devastating, with the potential of degrading server performance more effectively. Besides, HTTP 2.0 makes new attack approaches possible, for example, flood and low-and-slow attacks based on control frames and HTTP 2.0 header compression attacks, as demonstrated by a number of Common Vulnerabilities and Exposures (CVE) records. HTTP 2.0 attacks diversify in form, so simple protection solutions usually cannot work to a satisfactory effect. To address this problem, a multi-layer protection solution should be put in place.
To cope with these new types of attacks, DDoS attack researchers and mitigation operators should continually develop and improve their knowledge and skills so as to work out effective techniques and policies.
Key Findings 5 – The Average Attack Duration Shortened and Attack Cost
Continuously Declined
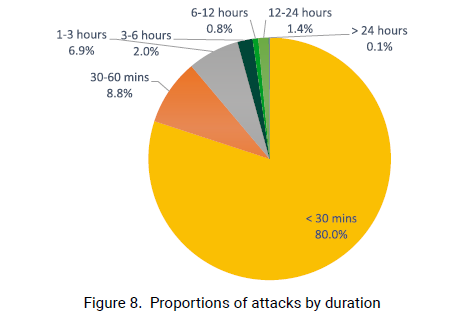
In 2020, the average duration of DDoS attacks registered 42 minutes, a 21% decrease from 2019. We noticed that the longest DDoS attack in 2020 lasted around 13 days, far longer than attacks detected in previous years.
In 2020, DDoS attacks lasting less than 30 minutes accounted for 80%, up 5 percentage points from the previous year (75%). The high proportion of short attacks signals that attackers are attaching more and more importance to the attack cost and efficiency and are more inclined to overwhelm the target service with floods of traffic in a short time, getting users offline and causing high latency and jitters. In addition, Botnet-as-a-Service (BaaS) and DDoS-as-a-Service (DDoS) have gained momentum for rapid development, which were also to blame for the prevalence of short attacks. Thanks to their availability, platform users are able to launch massive attacks in a very short time as long as they are willing to pay a certain amount of money for a whole lot of mercenary attack resources. In the long run, repeated burst attacks, which are under effective cost control, will greatly aggravate the quality of target services.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.