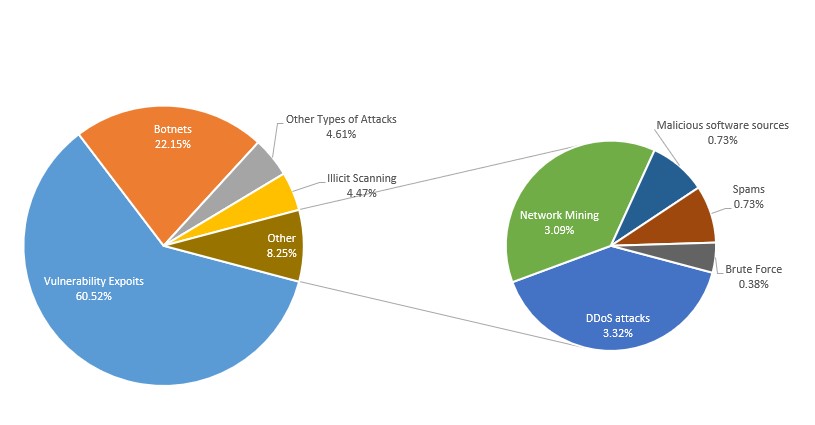
On December 9, 2021, the Log4j vulnerability was disclosed and had a huge impact. According to monitoring of NSFOCUS Threat Intelligence, hundreds of thousands of assets were affected by the vulnerability. A week after the vulnerability was disclosed, the NTI detected tens of thousands of malicious IP addresses using the Log4j vulnerability to launch various types of attacks, including illicit scanning, botnets, exploits, network mining, and remote execution of Trojan Horses, just name a few:
When similar major vulnerabilities or major security incidents occur, management of organizations will quickly make decisions and respond in a short period of time –remedy security vulnerability or respond to security incidents – to reduce risks and losses. Here it is hard to ignore NSFOCUS’s emergency response to this sudden incident. NSFOCUS’s MDR team set off the alarm and provided attack detection policies and traceback analysis to customers at the first time by leveraging three-level experts team, automatic cloud operations platform and standardized workflow, helping customers improve their detection and analysis capabilities shortly and accurately.
We often hear the concept of “combat operations” for security operations, which is mostly used in the process of attack and defense drills to detect and trace threats. However, the emergency response to such major vulnerabilities or security incidents is also part of the combat operations as it takes a lot of resources to complete a specific task in a short period of time.
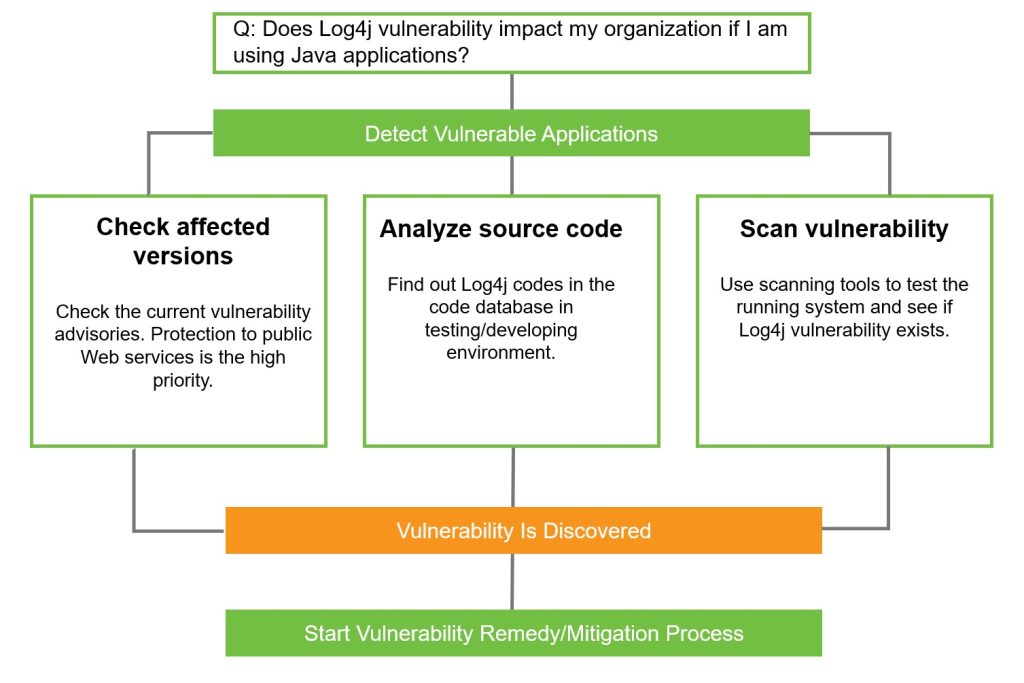
In the process of vulnerability repair, we also need to consider the measurement of security operations, or to measure the effectiveness and efficiency of operations. For example, how many assets are there currently and what is the proportion of vulnerabilities – these are indicators of impact scope; What is the average time to discover and confirm a vulnerable asset and how long it will take to fix it – these are indicators of operational efficiency.
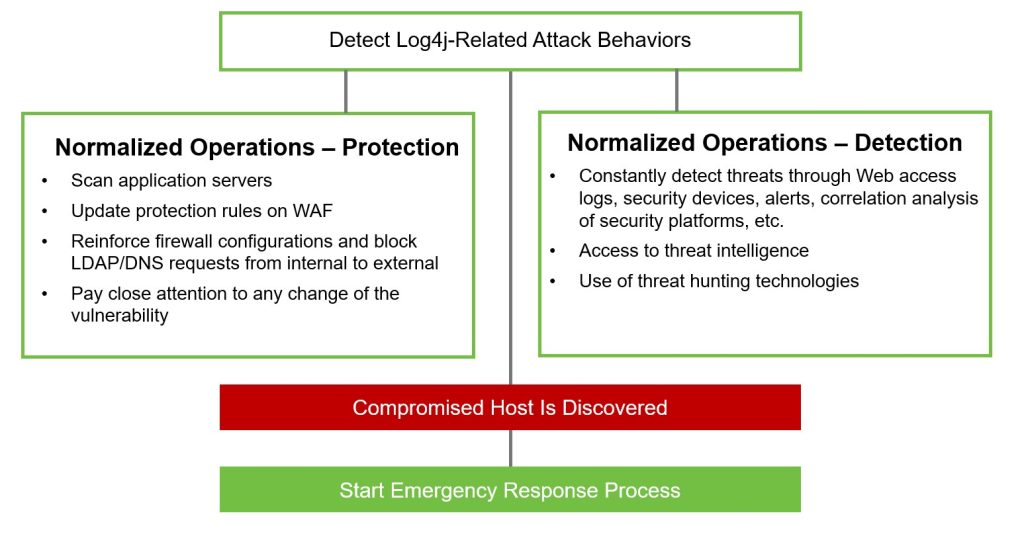
Once the actual combat operation is over, the security operation model should be transformed from actual combat to normalized detection and protection swiftly.
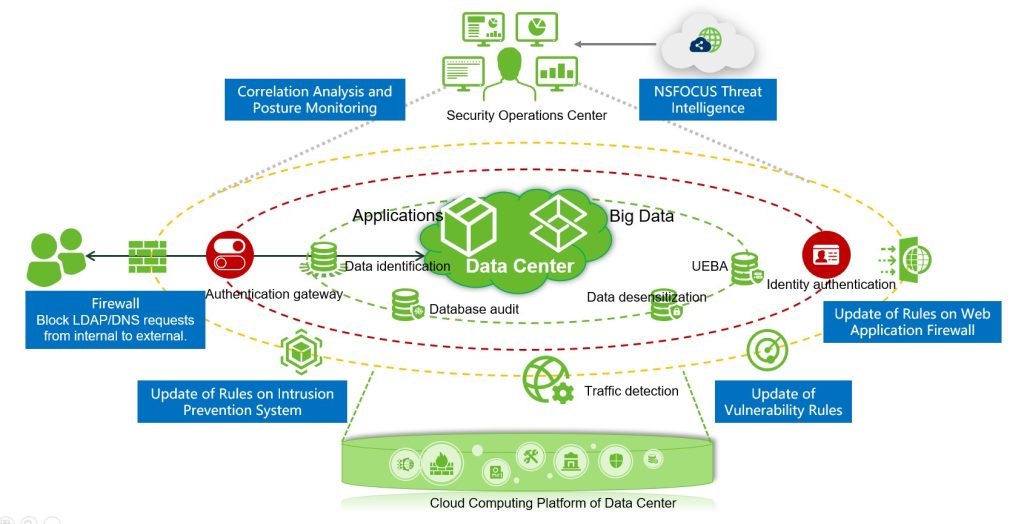
In a nutshell, it needs to be back to the routine, the daily security monitoring and protection – adopting an in-depth security architecture to assess assets, fill in gaps, and troubleshoot hosts with problems. For example, using security sensors and security analysis & management platform to continuously detect and analyze the Log4j vulnerability for timely response.
NSFOCUS can transform sudden security work into normalized, practical and systematic security operation capabilities with the help of security operation services, establish a closed-loop security process that runs through early warning, proactive detection, response and threat mitigation, and provide users with full value-chain services from planning, building to operation to continuously reduce customers’ security risks during their business growth.