Overview
Recently, NSFOCUS Labs discovered that the South Asian APT organization SideWinder launched phishing attacks with documents used Pakistan National Day-related content as the bait. The domain name of command and control (C2) server was forged as a Pakistani government website. Since SideWinder ‘s targets include Pakistan and China, it has always been considered an APT group from India.
Attack activity analysis
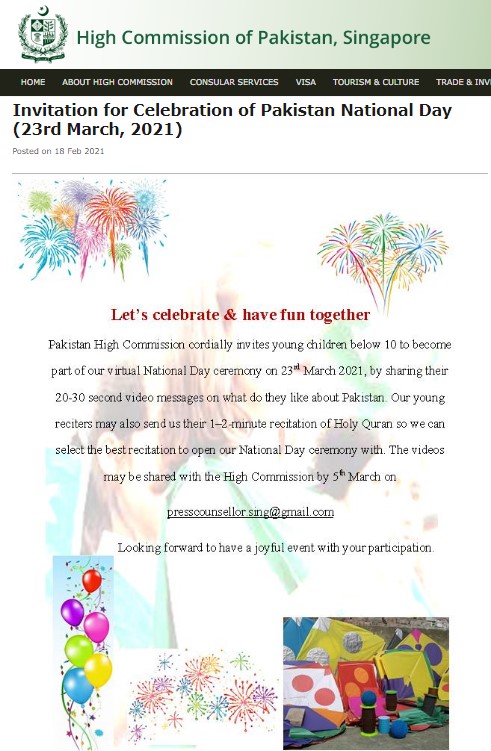
Decoy Documentation
The threat actor used RTF documents Pakistan National Day-related topic to lure the target to open it. The Pakistan National Day is on March 23 every year, just over a month left from now. The body is an invitation to participate in the celebration and prepare a patriotic speech.
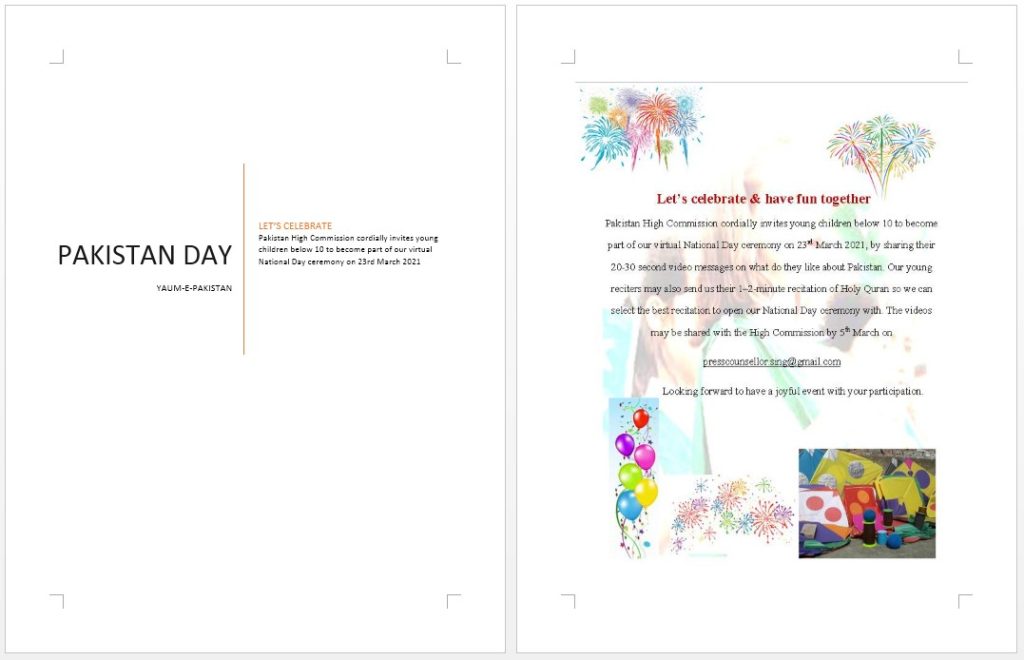
However, the time mentioned in the text is 2021, which may be because the attacker were not careful enough in making the bait, and directly quoted the content of last year.
Attack process
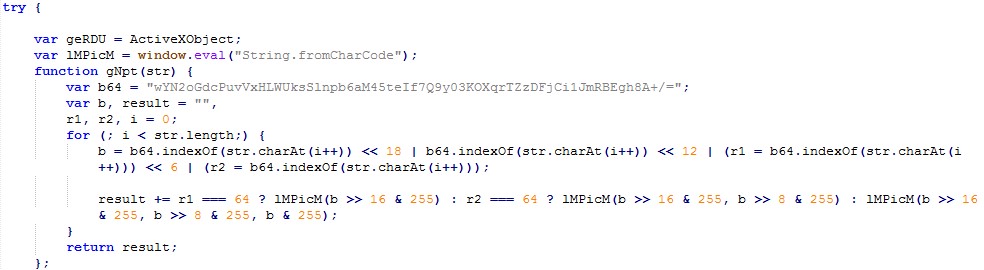
When the document is opened, a formula editor vulnerability (CVE-2017-11882) embedded in the document is exploited to trigger a set of codes in JavaScript and load an executable a .NET file in memory after decoding for the purpose of connecting the C2 server to download the subsequent files.
Instead of using powershell, the attacker used ActiveXObject and DotNetToJScript method to load. NET program, which is probably because of concern about detection of security software on the target hosts.
Codes in JavaScript
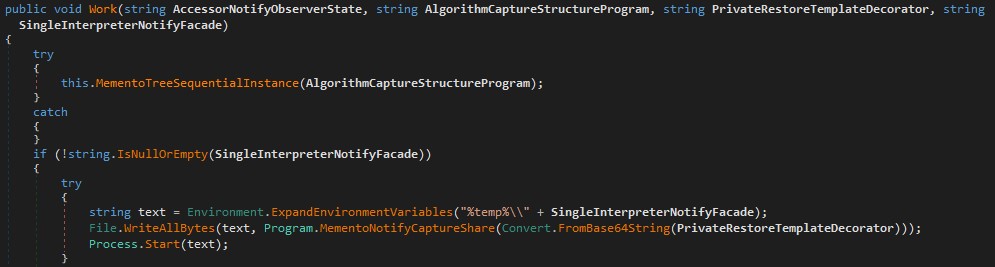
.NET Components:
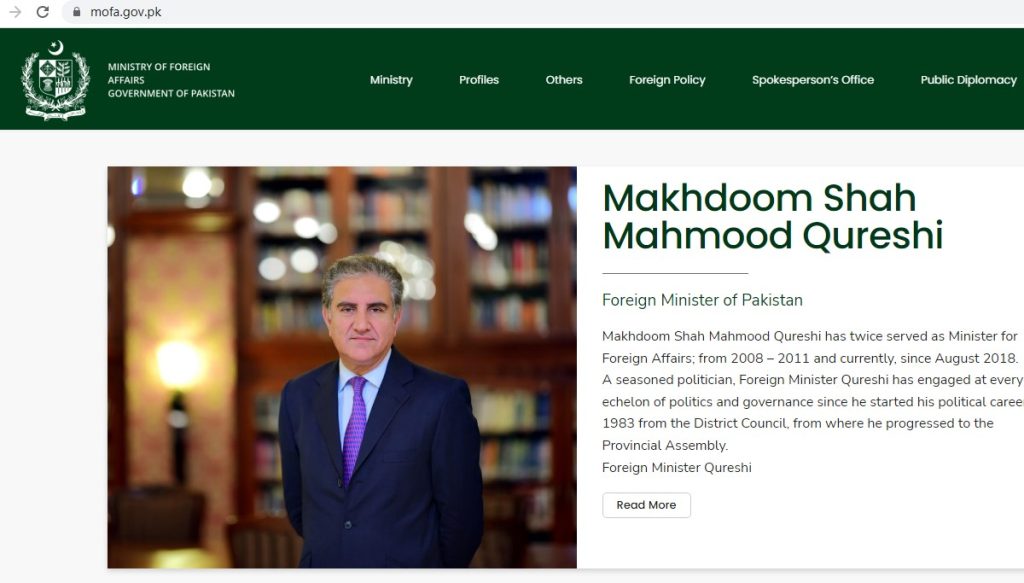
Command and control (C2) server
The domain name of C2 server used by the attacker contains the string mofa-gov-pk, directing to the website of the Ministry of Foreign Affairs of the Pakistan. Using the whitelist mechanism and the habit of people reading domain names from left to right, the attacker added a normal domain name after others and tried to escape detection by the multi-level domain name.
Conclusion
In recent years, border disputes between South Asian countries have continued, and APT attacks have occurred from time to time. Powershell has attracted much attention because of its convenient loading of .NET components, but Sidewinder uses DotNetToJScript instead of powershell, which requires defenders to pay more attention.
The Knowledge Graph of SideWinder
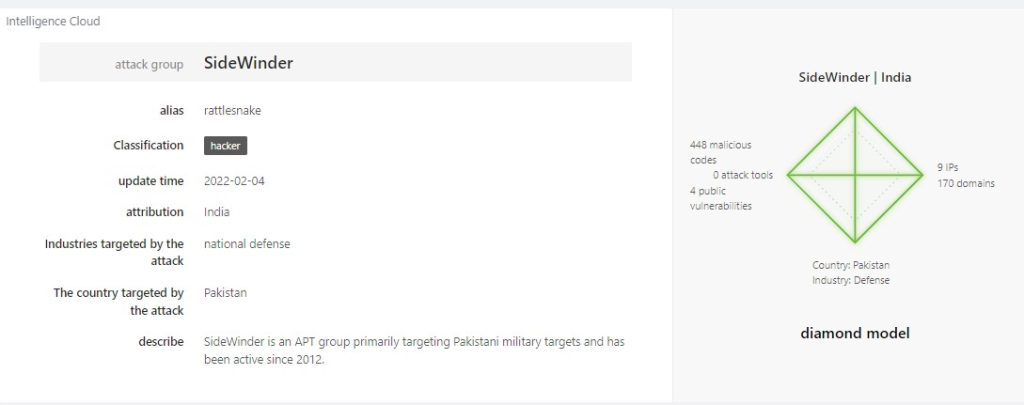
Associated IoCs detected using NSFOCUS Threat Intelligence (NTI)
MD 5 (section):
| 2db1ddd612010baf707bafe71cff3ecd |
| 2f4adea4665929d8a4b6d936c2f120c1 |
| 5ac0946ed702e6d01e699b8060fc907e |
| 5aec4856ebe472b53a74cbe210b32a48 |
| 5e575681a2eeed2036e556f7733d4e7c |
| 6a85fe72f098db4de4b2ae11f614e6b9 |