Overview
Recently, NSFOCUS CERT detected that Kubernetes issued a security announcement and fixed the Kubernetes Ingress-nginx remote code execution vulnerability (CVE-2025-1974). The Ingress controller deployed in Kubernetes Pod can be accessed through the network without authentication. When the Admission webhook is open, an unauthenticated attacker can remotely inject any nginx configuration by sending a special AdmissionReview request to Ingress-nginx. This allows arbitrary code execution on Ingress-nginx. The CVSS score is 9.8. At present, the vulnerability details and PoC have been made public. Relevant users are requested to take measures for protection as soon as possible.
Ingress-nginx is an open source ingress controller provided by the Kubernetes project. It is implemented based on nginx and used to manage network traffic in a Kubernetes cluster. It is powerful, easy to use, and highly adaptable.
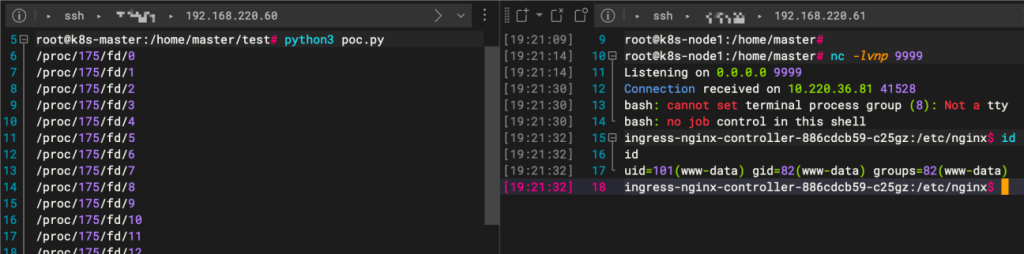
NSFOCUS has successfully replicated this vulnerability:
Scope of Impact
Affected version
- Ingress-nginx <= 1.11.4
- 1.12.0-beta.0 <= Ingress-nginx < 1.12.1
Note: In the default installation configuration, the Ingress Controller has access to all Secrets within a cluster.
Unaffected Version
- Ingress-nginx >= 1.11.5
- Ingress-nginx >= 1.12.1
Detection
Manual detection
Users can first use the following command to confirm whether K8s uses the ingress-nginx controller:
| kubectl get pods –all-namespaces –selector app.kubernetes.io/name=ingress-nginx |
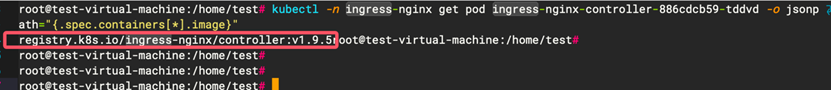
Then enter the following command to view the version of ingress-nginx:
| kubectl -n ingress-nginx get pod <ingress-nginx-pod-name> -o jsonpath=”{.spec.containers[*].image}” |
Tool detection
NSFOCUS Automated Penetration Test Tool (EZ) has supported fingerprint identification for K8s ingress and vulnerability detection for CVE-2025-1974 (Note: For the enterprise version, please contact NSFOCUS sales personnel).
The following commands can be used for product fingerprinting:
| ./ez webscan –disable-pocs all -u https:192.168.1.41:4443/ |
The following commands can be used to detect vulnerabilities on a single host or in batches:
| ./ez webscan –pocs ingress -u https:192.168.1.41:4443/ |
| ./ez webscan –pocs ingress -uf url.txt |
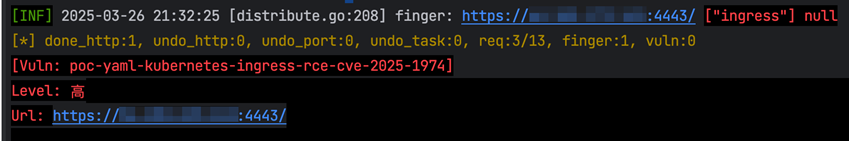
Download link of the tool: https://github.com/m-sec-org/EZ/releases
Risk Investigation of Exposed Surface
The NSFOCUS CTEM solution can actively and passively identify and troubleshoot K8s-related assets and CVE-2025-1974 vulnerabilities:
1. It can directly match the asset name and version of K8s;
2. Check whether the Admission Controller in the ingress-nginx configuration file is exposed by issuing a configuration verification task;
Vulnerability scanning can be carried out by calling PoC.
Mitigation
Official upgrade
A new version has been officially released to fix this vulnerability. Please upgrade the protection for affected users as soon as possible. Download link: https://github.com/kubernetes/ingress-nginx/releases
Temporary protective measures
If relevant users cannot upgrade temporarily, the following measures can also be taken for temporary relief.
1. Perform access control on the Admission Controller.
2. Disable the function of Validating Admission Controller in ingress-nginx without affecting services.
(1) ingress-nginx mounted with Safety Helm:
You can reinstall and set the Helm property to controller.admissionWebhooks.enabled=false.
(2) Manually installed ingress-nginx:
Remove the configuration ingress-nginx-admission named ValidatingWebhook; Edit the Deployment or Daemonset to remove ingress-nginx-controller–validating-webhook from the parameter list of the controller container.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.
