By default, NSFOCUS NIPS identifies the protocols and detects attacks on standard ports only. For example, File Transfer Protocol (FTP) operates on ports 20 and 21, Telnet protocol operates on port 23, and HTTP protocol uses port 80. However, the traffic using preceding protocols on non-standard ports will not be identified by NIPS by default, for example, in some business cases where the HTTP port is changed to 8080.
To prevent attacks arising from non-standard ports, you need configure an application management policy to identify specific applications and protocols.
Follow these steps to configure an application management policy:
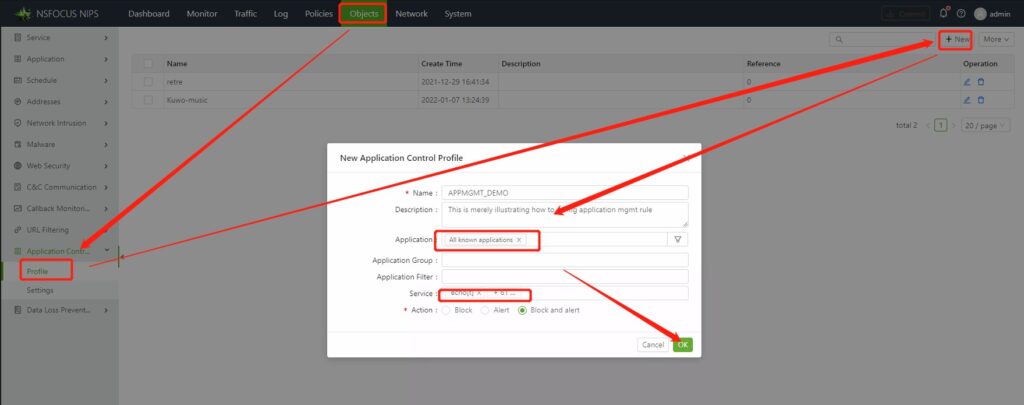
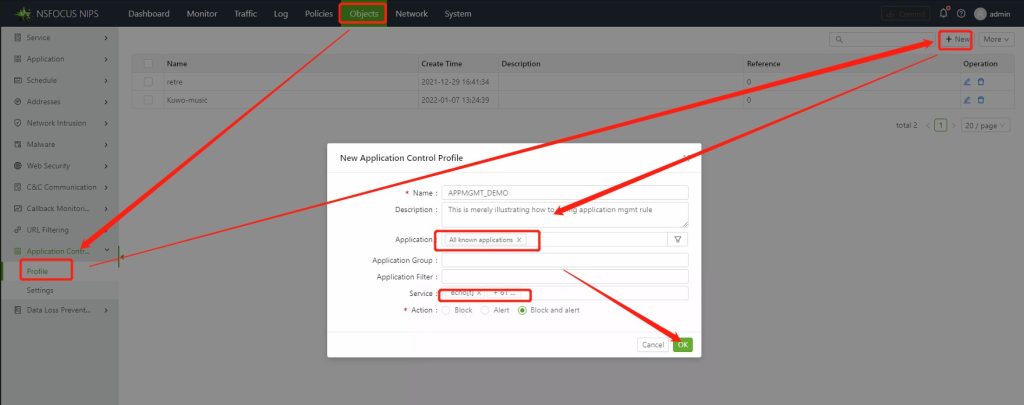
Step 1: Click Objects on the navigation bar.
Step 2: In the navigation pane, from the Application Control drop-down list, choose Profile.
Step 3: Click New at the top right corner of the displayed page.
Step 4: In the New Application Control Profile dialog box, fill in the Application field. For Demo purpose, All Known Applications is selected here.
Step 5: Click OK.
Step 6: Click Commit at the upper right of the window.
After that, choose System > System Settings > Advanced > Modify Configuration.
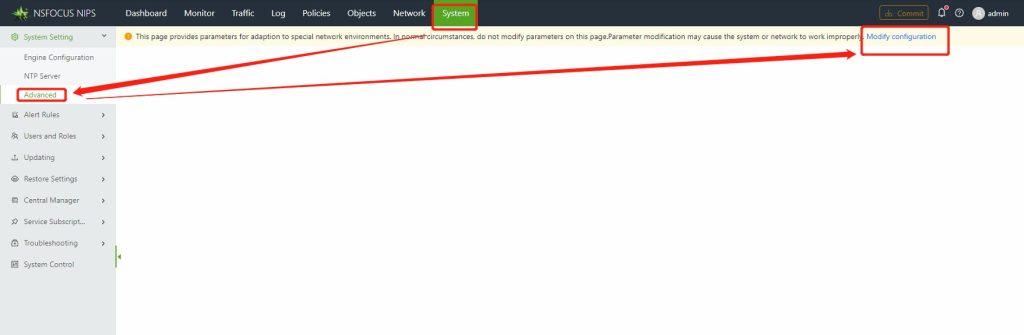
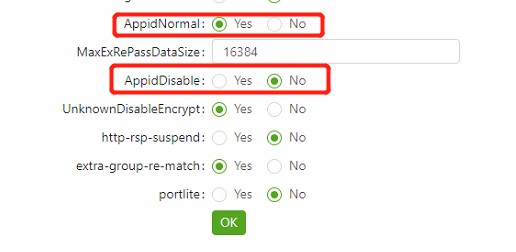
In the displayed dialog box, select Yes for AppidNormal and No for AppidDisable. Then traffic using the protocol on non-standard ports will be listened.
Note that those two parameters are set to Yes by default, which indicates that traffic using the protocol only on standard ports can be identified.