1 Vulnerability Overview
Recently, the NSFOCUS M01N team released the Analysis of Privilege Escalation Attacks by Exploiting Resource-based Constrained Delegation, in which they describe the principle of attacks launched by exploiting the resource-based constrained delegation, so as to escalate privileges of domain hosts. For details, click the following link:
http://blog.nsfocus.net/analysis-attacks-entitlement-resource-constrained-delegation/
Several days ago, a security researcher, Dirk-jan Mollema, discovered that, a delegation attack, combined with NTLM relaying, can get code execution as SYSTEM on any Windows computer in Active Directory without any credentials, if they are in the same network segment. The NSFOCUS M01N team has reproduced the attack and analyzed its techniques. This attack can inflict a great damage, and users are therefore advised to stay wary.
Reference link:
https://dirkjanm.io/worst-of-both-worlds-ntlm-relaying-and-kerberos-delegation/
2 Scope of Impact
The attack can be launched only when the following two conditions are met:
- The operating system of the domain controller is Windows Server 2012 or later.
- LDAPS is enabled on the domain controller.
3 Threat Detection
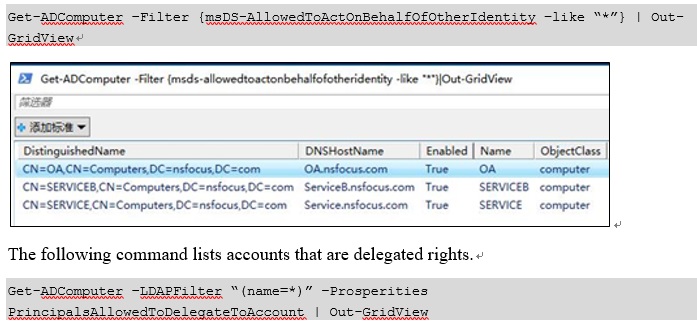
The following command checks which computer resources allow delegation. The Active Directory module of PowerShell lists computers delegated to other machines.
4 Mitigations
The attack method involves multiple components, and therefore various preventative measures are available. Any of the following preventative measures is sufficient for protection.
- If no IPv6 address is required in the customer’s environment, configure a group policy to shield all DHCPv6 traffic and inbound router advertisements in the firewall.
- If WPAD is not required, configure a group policy to disable it and disable the WinHTTPAutoProxySvc service at the same time.
- Enable both LDAP signing and LDAP channel binding. For details, click the following links:
- https://docs.microsoft.com/en-us/windows/security/threat-protection/security-policy-settings/domain-controller-ldap-server-signing-requirements
- https://support.microsoft.com/en-us/help/4034879/how-to-add-the-ldapenforcechannelbinding-registry-entry
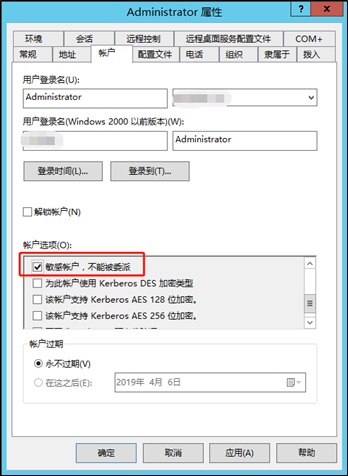
- Set the administrative account to “Account is sensitive and cannot be delegated”.
- Add the most privileged domain user to the Protected Users group.
For details, click the following link:
- Add an access control entry (ACE) to prevent computer accounts from modifying their msDS-AllowedToActOnBehalfOfOtherIdentity attribute. If resource-based constrained delegation is unnecessary, forbid everybody to modify the msDS-AllowedToActOnBehalfOfOtherIdentity attribute.
For details about ACEs, click the following link:
https://docs.microsoft.com/en-us/windows/desktop/SecAuthZ/access-control-entries
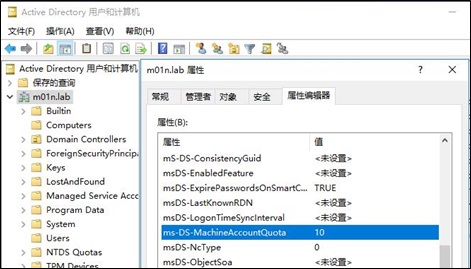
- Configure ms-DS-MachineAccountQuota. According to the default Windows policy, all authenticated users can add 10 hosts in a working group to the active directory or create 10 computer accounts.
If ms-DS-MachineAccountQuota is set to 0, common users cannot add any computer account to the active directory, and attacks by exploiting resource-based constrained delegation can be mitigated accordingly.Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.