Overview Recently, NSFOCUS CERT found a remote code execution vulnerability in Apache ActiveMQ Jolokia (CVE-2022-41678). In the configuration of ActiveMQ, jetty allows org.holokia.http.AgentServlet to process requests for/api/Jolokia. An authenticated attacker can send a specially crafted HTTP request to write a malicious file through the Jolokia service, thus implementing remote code...
Blog
O que é Phishing? Tipos e dicas para evitar golpes
O mundo digital está constantemente sob ameaça de um dos mais perigosos golpes cibernéticos: o phishing. Trata-se de uma técnica maliciosa utilizada por cibercriminosos para enganar usuários e obter informações pessoais e sensíveis. Vamos explorar o que é, como funciona e como se proteger desses ataques. Continue a leitura! O...
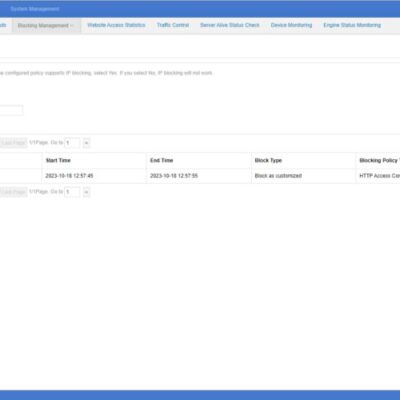
Introduction to NSFOCUS WAF Blocking Method
When you configure a protection policy for your protected website and set the protection action to block, NSFOCUS WAF supports three methods to execute blocking actions: Source IP Block, Session Block, and UA Block. Session Block and UA Block are newly added on system version 6073. Each block supports three...
NSFOCUS WAAP: A Future-Ready Solution for Web and API Security Challenges
In the digital age, Web application and API security (WAAP) has demonstrated the importance of the development of the web application and API economy, and it is becoming the new standard of the next generation of WAF. WAAP is essential in today's digital environment. As organizations increasingly rely on web...
Confidential Computing: Guardian of Privacy in the Big Data Era
The Future of Data Protection: The Emergence of Confidential Computing In today's information age, data has become an invaluable resource ubiquitous across various sectors, from financial institutions to healthcare and scientific research. However, as data continues to grow, concerns about data privacy and security become increasingly prominent. Incidents of data...
Ransomware: o que é, prevenção e como diminuir sua exposição?
O termo ransomware é um tema frequente nas discussões sobre segurança cibernética. Trata-se de um tipo de malware que pode causar sérios danos a indivíduos e organizações, restringindo o acesso a dados vitais e sistemas inteiros. Neste artigo, vamos entender o que é ransomware, mitigações e formas de assegurar sua...