ICS Information Security Assurance Framework 3

January 17, 2020
Development of ICS Information Security
Since the Stuxnet virus explosion, countries all over the world have taken ICS security issues to a new height by actively working out and introducing related policies, standards, technologies, and solutions.
A look into ICS security developments around the world reveals that the USA is the first to research and implement ICS security standards. North America Electric Reliability Corporation has conducted security checks on electric power (including nuclear power) enterprises according to requirements defined in CIP series standards. Europe has inspected security of industrial control products in accordance with WIB standards. Some counties represented by Germany are diverting their efforts to ICS security in compliance with ISO 27009. Japan, in line with requirements of IEC 62443 and Achilles Certification, stipulated in 2013 that all ICS products can be applied in the country only after they are certified by national standards. Also, this country has conducted ICS security checks and construction in energy, chemical, and other critical sectors. Israel has set up a state-level ICS product security inspection center to perform security inspection on ICS products before they are connected to networks. (more…)
Cybersecurity Insights-13

January 16, 2020
Distribution of IoT-based Family Samples
We analyzed IoT-based malicious family samples captured by NSFOCUS threat hunting systems (see Figure 7-1), those captured by NSFOCUS Threat Intelligence (NTI) and those captured by VirusTotal (see Figure 7-2). The two figures, though presenting different data sources, both indicate that Gafgyt and Mirai take the first two places on the top list. We can see that IoT-based malware families tend to behave in a similar way. This is likely due to the source code of Gafgyt and Mirai families being published on the internet and can be modified at will. Their variants mainly change the C&C address and attack method, which is what tools-kids always do. Arguably, most attackers are tool users, with little technical expertise. (more…)
IP Reputation Report-01122020

January 15, 2020
-
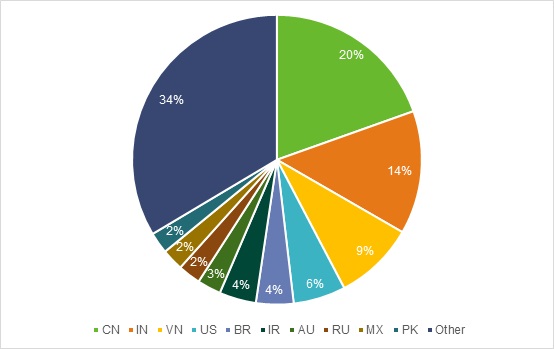
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at January 12, 2020.
ICS Information Security Assurance Framework 2

January 14, 2020
1.2 Development of ICS Information Security
As industrial informatization advances at a rapid pace and the industrial Internet, industrial clouds, and other new technologies spring up, information and network technologies and IoT technologies have found wide application in smart grid systems, intelligent transportation systems, and industrial production systems.
For the sake of inter-system collaboration and information sharing, ICSs are breaking out of the traditional model of previous dedicated systems that run in a closed-off manner and begin to incorporate some standard and universal communication protocols and software and hardware systems. Some ICSs can even connect to the Internet in one way or another, thus breaking the protection barrier formed by the enclosed network, but exposing those systems to more threats.
As ICSs are most commonly seen in a country’s critical industries such as electricity, transportation, petrochemical, and nuclear sectors, cyberattacks targeting those systems will cause a more serious social impact and economic loss. Out of political, military, economic, and religious reasons, adversary organizations and countries and terrorist criminals can make industrial control systems their attack targets for malicious intents. (more…)
ICS Information Security Assurance Framework 1

January 13, 2020
Development of ICS Security
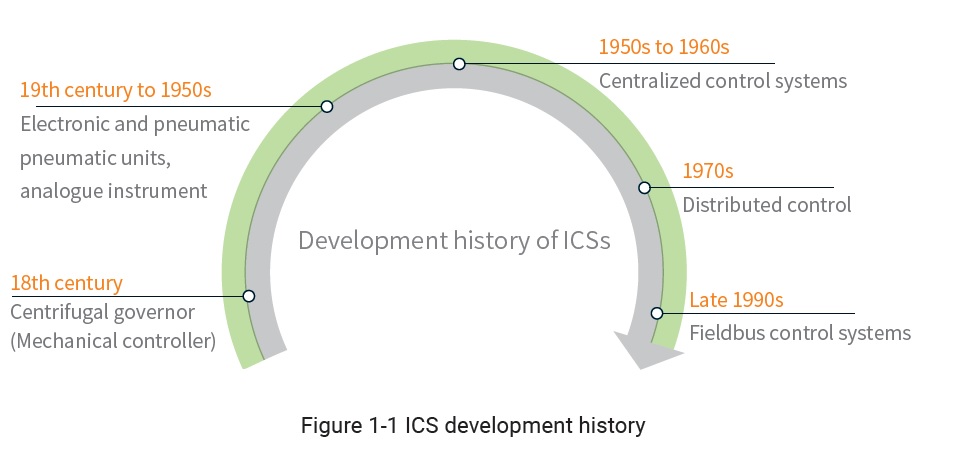
1.1 Development of Industrial Intelligence
The following figure shows the development history of industrial control systems (ICSs).
The history of ICSs can date back to the 18th century when James Watt improved the steam engine by adding a throttling controller, i.e., a centrifugal governor. The centrifugal governor works like this: It obtains feedback signals by using a shaft around which it rotates with the steam engine. Also, it adjusts the positions of flyballs with the aid of centrifugal force, so as to regulate the steam throttle for control of the rotational speed of the steam engine. It is believed that this kind of centrifugal governor marks the beginning of automatic regulation and automatic control. (more…)
Information Security in the Workplace- Distribution of Sensitive Documents-v
January 10, 2020
With the advancement of IT-based transformation and the rapid development of IT, various network technologies have seen more extensive and profound applications, along with which come a multitude of cyber security issues. Come to find out what information security issues you should beware of in the workplace. (more…)
Cybersecurity Insights-12

January 9, 2020
6.3 Worm In the 2018 H1 Cybersecurity Insights , we pointed out that most worm viruses were discovered more than five years ago. This indicates how capable these viruses are of propagating and evolving and how difficult it is to remove them completely from the network. According to data throughout the year, this was still […]
IP Reputation Report-12292019

January 8, 2020
-
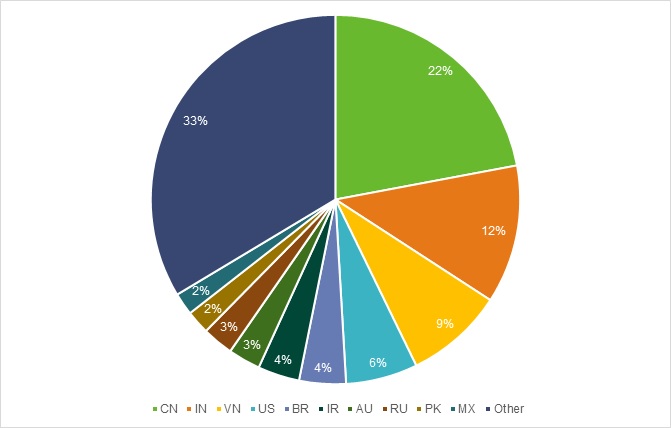
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at January 5, 2020.
Apache Log4j Deserialization Remote Code Execution (CVE-2019-17571) Vulnerability Threat Alert
January 6, 2020
Vulnerability Description
On December 19 local time, Apache Software Foundation (ASF) officially released a security advisory, announcing that Apache Log4j has a deserialization issue that could cause remote code execution (CVE-2019-17571). Log4j is a Java-based open-source logging tool from the Apache Software Foundation. Log4j 1.2 includes a SocketServer class which can easily accept serialized log events and deserialize them without authentication. With the aid of deserialization tools, an attacker could use this class to remotely execute arbitrary code. (more…)
IP Reputation Report-12292019

January 3, 2020
-
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at December 29, 2019.