1.2 Development of ICS Information Security
As industrial informatization advances at a rapid pace and the industrial Internet, industrial clouds, and other new technologies spring up, information and network technologies and IoT technologies have found wide application in smart grid systems, intelligent transportation systems, and industrial production systems.
For the sake of inter-system collaboration and information sharing, ICSs are breaking out of the traditional model of previous dedicated systems that run in a closed-off manner and begin to incorporate some standard and universal communication protocols and software and hardware systems. Some ICSs can even connect to the Internet in one way or another, thus breaking the protection barrier formed by the enclosed network, but exposing those systems to more threats.
As ICSs are most commonly seen in a country’s critical industries such as electricity, transportation, petrochemical, and nuclear sectors, cyberattacks targeting those systems will cause a more serious social impact and economic loss. Out of political, military, economic, and religious reasons, adversary organizations and countries and terrorist criminals can make industrial control systems their attack targets for malicious intents.
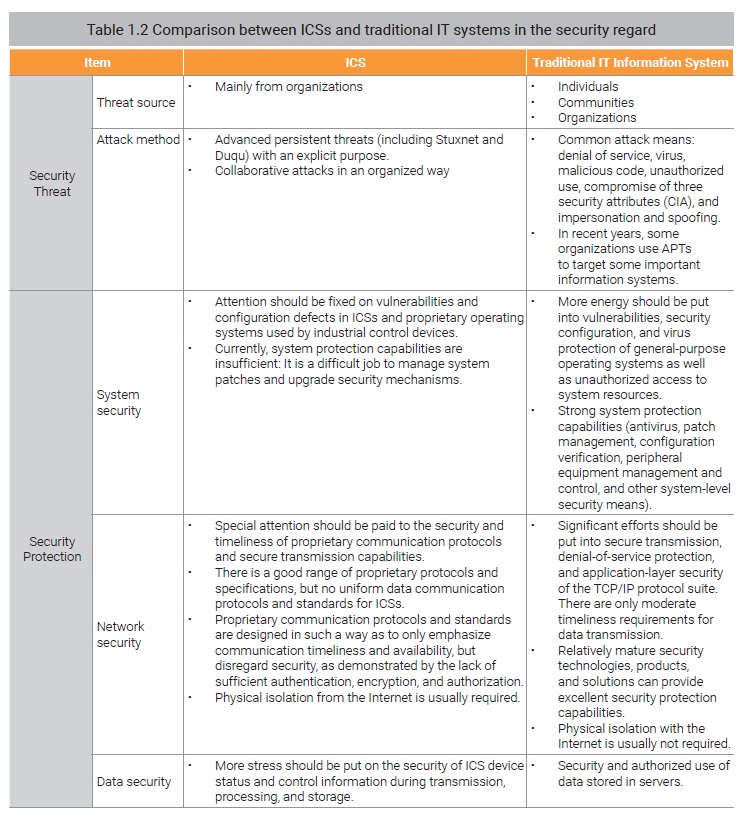
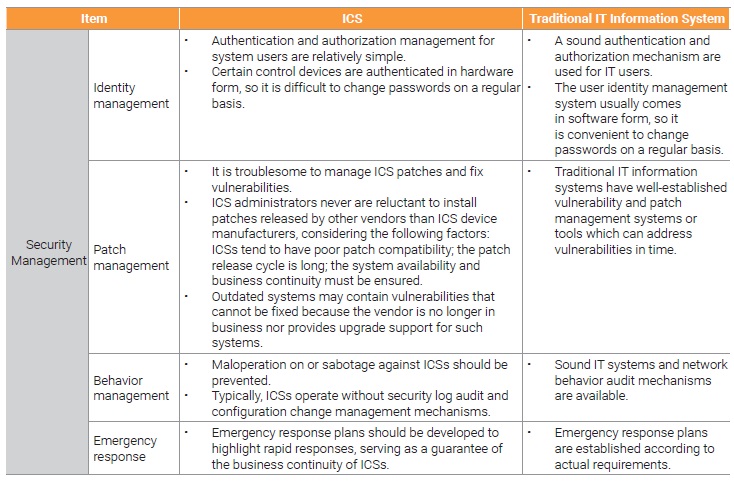
Information security incidents against ICSs, typically the Stuxnet virus, demonstrate that attackers are generally adopting a new attack means dubbed advanced persistent threat (APT). For APTs, attackers collaborate with each other to strike specific targets in an organized way. As China’s ICSs and their operating environments are relatively enclosed, security research teams in this country, who are overly concerned about the Internet and traditional information systems, fail to accumulate a lot of research findings and practical experience in ICS protection. Besides, ICS providers focus too much on system functions and too little on security factors. In particular, as owners tend to fail to put forward explicit security requirements, security solutions, though available, are not proactively implemented for ICSs in China to protect them.
Many countries have realized the vulnerable security situation of ICSs and increasingly serious attack threats faced by them, and begin to promote ICS security to the national security strategy level and take proactive measures by introducing policies, standards, technologies, and solutions. While putting forward information security management requirements for ICSs in key realms, many governments are carrying out ICS security assurance work regarding policies and scientific research.
- Difference Between ICSs and IT Information Systems in Information Security
With the rapid development of industrial informatization, ICSs have also employed up-to-date computer network technologies to promote inter-system integration, networking, and informatization management. This will allow IP-based communications to become basic communication means for ICSs, as demonstrated by the introduction of IT products such as PC servers and general-purpose operating systems and databases and the adoption of TCP/IP-based Ethernet ring networks and OPC communication protocols.
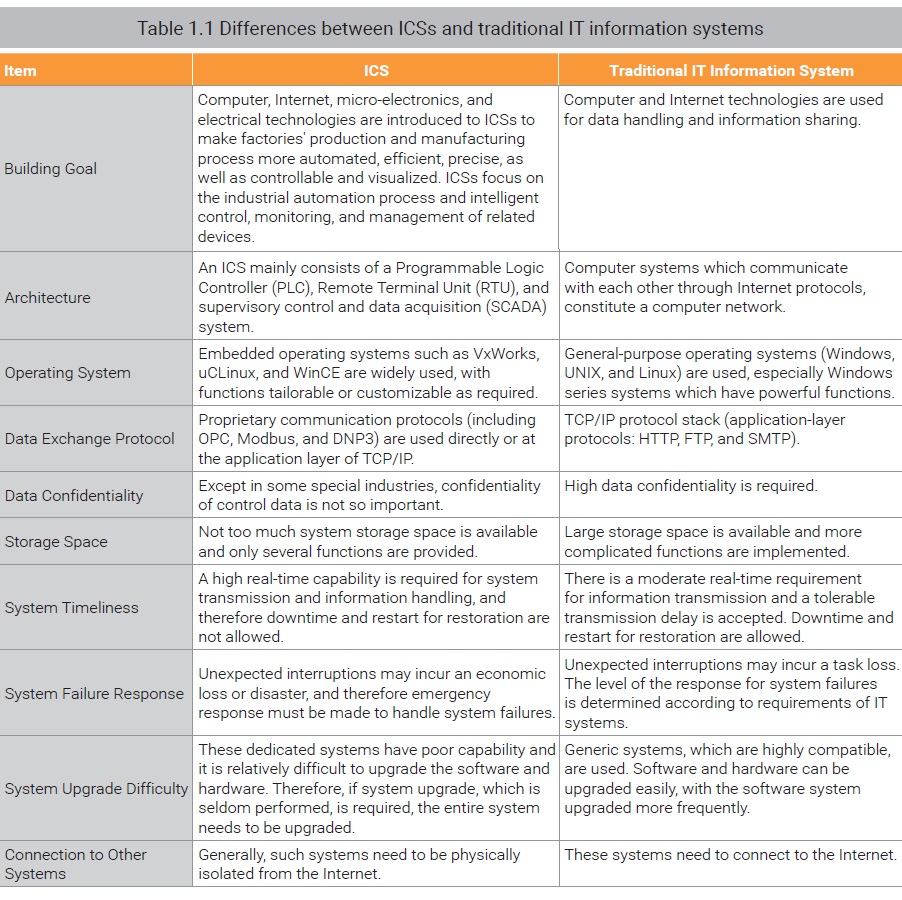
To ensure the compatibility of ICSs, the application layer of the network will gradually use dedicated industrial control protocols. Applying Internet technologies will break the barriers between enterprises’ production systems to implement centralized enterprise management and control and improve informatization, thus laying a solid foundation for efficient integration of production systems and management systems of enterprises. However, ICSs and traditional IT information systems are built for different purposes, and therefore they differ greatly in such aspects as technology, management, and service. Table 1.1 describes typical differences between the two types of systems.
In the traditional information security realm, confidentiality, integrity, and availability, which are collectively referred to as CIA, are regarded as three basic security attributes. In most cases,
confidentiality matters the most. However, this is not the case in the ICS domain which highlights the degree of industrial automation and intelligent control, monitoring, and management capabilities of related devices. ICSs are quite different from common IT information systems in terms of system architecture, device’s operating system, and data exchange protocols and are focused more on system’s real-time capability and business continuity.
Therefore, it is essential to ensure the availability and integrity of the equipment on which ICSs are installed. The data transmitted in ICSs is typically control commands and collected raw data, which are mostly real-time data and need to be analyzed together with the context. Therefore, we have the lowest requirement for confidentiality of such data.
ICSs, as core production and operations systems of industrial enterprises, usually operate in an environment where a strict management mechanism is established. Except ICS suppliers, other external personnel are not admitted to ICSs’ physical operating environment. Meanwhile, measures are typically in place to isolate ICSs from office networks (ordinary IT systems) of enterprises. Also, ICSs are physically isolated from the Internet. Obviously, ICSs’ operating environment is relatively enclosed. ICSs are mainly composed of a wide variety of industrial control devices and systems, like PLC, RTU, DCS, and SCADA, which function on embedded operating systems (VxWorks, uCLinux, and WinCE) that are different from general-purpose Internet operating systems and communicate with each other through proprietary communication protocols or standards (including OPC, Modbus, and DNP3).
These proprietary industrial control systems and devices and communication protocols as well as relatively enclosed environments make it hard for Internet hackers or hacker organizations to obtain useful data concerning ICS defense research environments and related systems. This is why hackers’ defense research is mostly limited to Internet-facing systems or ordinary IT information systems, but seldom on ICSs. Therefore, security defects (or vulnerabilities) are rarely discovered in ICSs and related communication protocols. In addition, ICS providers fail to give sufficient considerations to security issues and protective measures or inform security in O&M policies, while putting too much energy on system availability and timeliness.
Since 2000, there have been numerous ICS operations problems resulting from information security issues. Security incidents represented by Stuxnet uncovered in 2010 and a series of subsequent ICS incidents all suggest that ICSs are no longer immune from security risks but faced with increasingly serious threats which lead to even more adverse impact.
In view of above, ICSs and traditional IT information systems are immensely disparate in security threats, security issues, and security protections. Table 1.2 analyzes those differences.
To be continued.