Overview
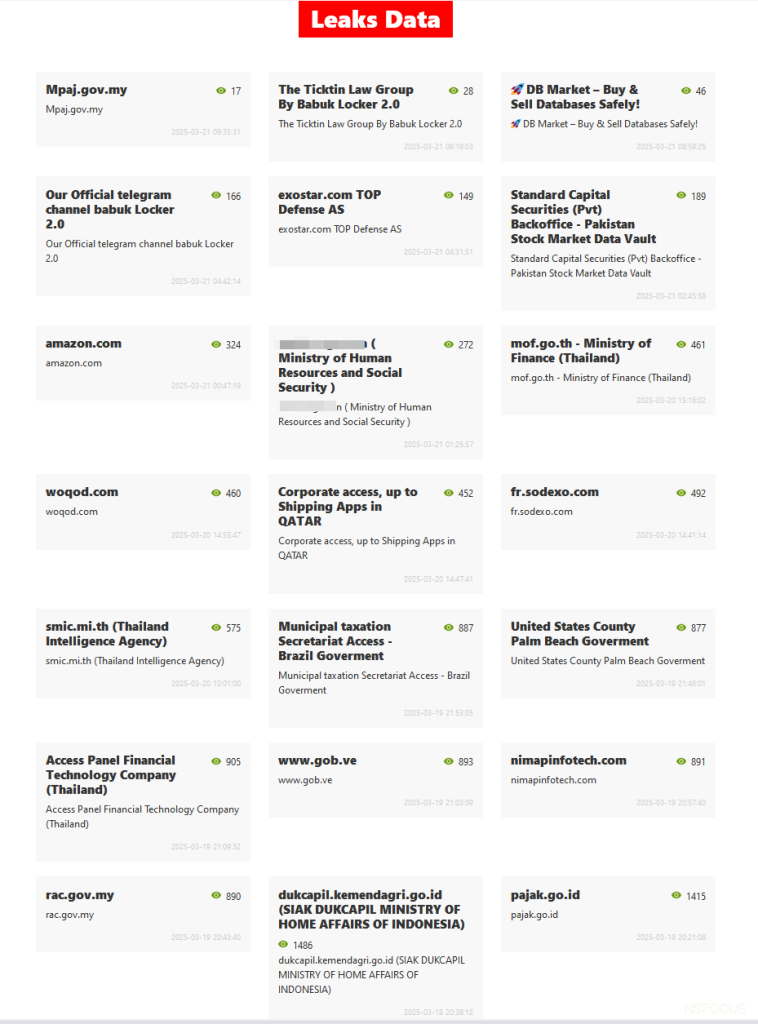
Recently, NSFOCUS CERT detected that the Babuk2 group has been frequently publishing sensitive data of several well-known organizations on its dark web site. The data is from multiple sectors, including government, finance, internet, healthcare, and education, across various countries and regions. Up to this month, at least 71 victims’ data has been disclosed, and it is shown that data from multiple organizations has been sold. The impact of the leakage is extensive and extremely detrimental.
About Babuk2
The hacker group Babuk2 (Babuk Locker 2.0), also known as Bjorka or SkyWave, has been publishing leaked data of various units on its dark web site for ransom since January 2025.
The ransomware group Babuk (Babyk) was first discovered active in January 2021. It primarily targets large corporations and government agencies in Europe and North America, including industries such as transportation, government, healthcare, industrial equipment suppliers, and more. It adopts the Ransomware as a Service (RaaS) model and uses a dual ransomware (encrypted files + data theft) strategy. The group prefers targets with strong payment capabilities and attacks Windows, ESXi and NAS devices.
In late April 2021, Babuk announced the stop of its operations and disclosed part of its source code under pressure from the U.S. law enforcement. However, it soon deleted this announcement and made a comeback.
After May 2021, Babuk announced that it would turn to pure data theft and extortion and establish a data leakage and trafficking platform;
In June 2021, Babuk released a ransomware generator on the Raidforums forum. Users can customize and generate encryptors and decryptors for systems such as ESXi and Windows.
The group then split into two factions over the Washington D.C. Police Department incident, resulting in the emergence of Ramp and Babuk V2.
In September 2021, a 17-year-old core member, who claimed to have cancer, leaked the complete source code of the hacker group on a Russian hacking forum. This led to a proliferation of ransomware variants based on that code family (Play and RTM Locker).
According to investigations on public information, Babuk2 is not a continuation of the original Babuk ransomware group. Instead, it is an independent hacker group named Bjorka who has adopted Babuk’s name and attack templates. Moreover, much of the data it claim to have actually originated from previous leaks by other ransomware groups (the original Babuk, RansomHub, Sodinokibi, and KillSec). Babuk2’s operational model has sparked widespread controversy because it sells databases on BreachForums and Telegram. Babuk2 announced its return in January 2025 and launched a data leak site on the dark web to post extortion messages targeting victims. However, multiple security research institutions, analysts, and media outlets have questioned the authenticity of its claims.
Event analysis
Cases of the three Chinese e-commerce giants:
On the evening of March 19, Babuk2 posted data leak posts from three Chinese e-commerce companies on a dark web leak site, and sample files were provided for each. The group currently claims to have sold relevant data. (Hereinafter, the companies are referred to as E-commerce One, Two, and Three.)
E-commerce One: The group claims to have 14.5 billion pieces of data, with a zip file of approximately 892 GB. This includes 1.4 billion orders and information on 690 million individuals. The data includes names, phone numbers, addresses, order numbers, product names, prices, and dates. Due to what appears to be a typographical error, the post mistakenly describes the data as belonging to E-commerce Two.
The download link for its sample file is currently invalid:
E-commerce Two: It claims to have 815 million pieces of data, with a zip file of approximately 600GB, and CSV files of 1.8TB, involving 8.1 billion orders and information on 600 million people. The data included platform, ID, mobile phone, name, address, shopping details, price, date.
After analyzing the sample files, it is found that among the hundred data entries, many are duplicates, and all the order dates are February 27, 2025.
E-commerce Three: It claims to have 141 million pieces of data, with a zip file of approximately 11.5GB. The data fields involved include real name, username, password, email address, QQ number, mobile phone number, ID card and other information.
After analyzing the sample file, it is found that most of the field names do not match the information content. The password field appears to contain hash value. The QQ number field is either empty or filled with repeated digits. The ID card number field contains contact information.
In summary, the sample data provided by Babuk2 is limited in volume and poor in quality. There is no evidence to prove that the group actually infiltrated these e-commerce companies. It may have fabricated the data to make it look like the data was stolen through ransomware attacks, while actually using leaked data from third-party channels, data transactions, or previous data. Moreover, the data size of E-commerce Three is not on the same scale as that of the first two. Judging by the release sequence, it seems that Babuk2 might have deliberately included all three e-commerce companies just to expand public influence.
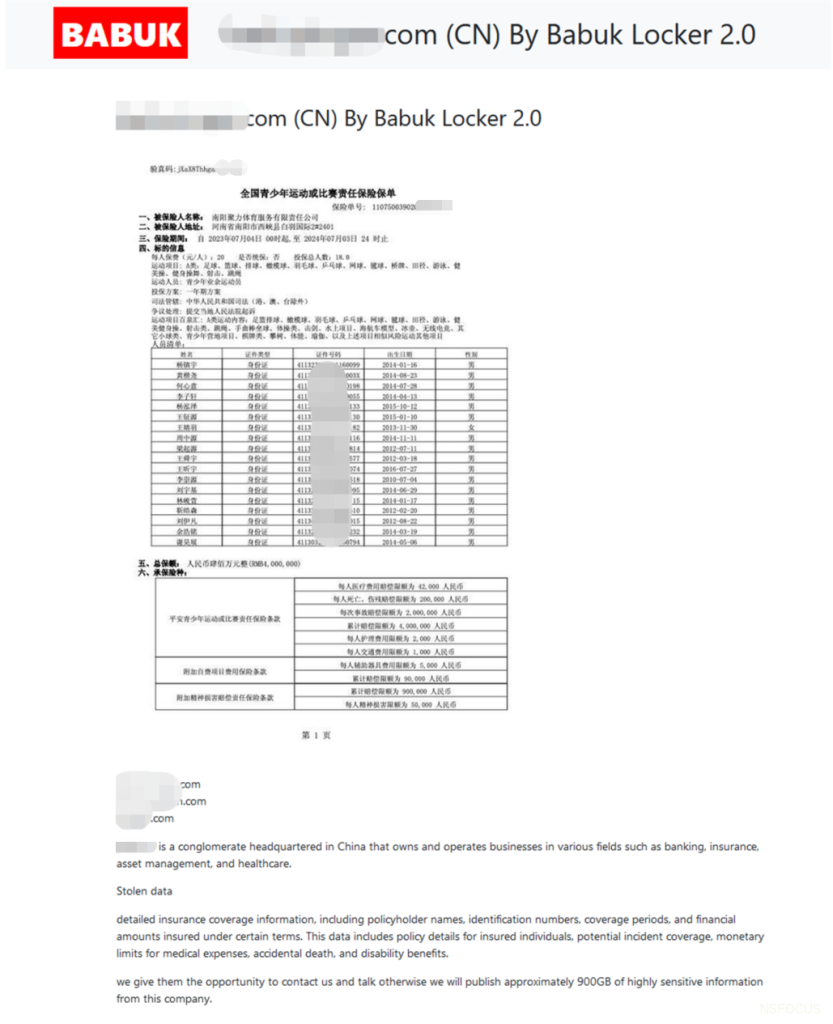
Case of a large Chinese financial institution:
On March 11, Babuk2 released a post about a domestic financial institution’s data leakage on the dark web leak site, claiming to have successfully hacked into multiple business systems of a domestic financial institution and stolen highly sensitive data of 900GB. In the post, it also provided a download link for some of the leaked data (sample data included two 500M zip files).
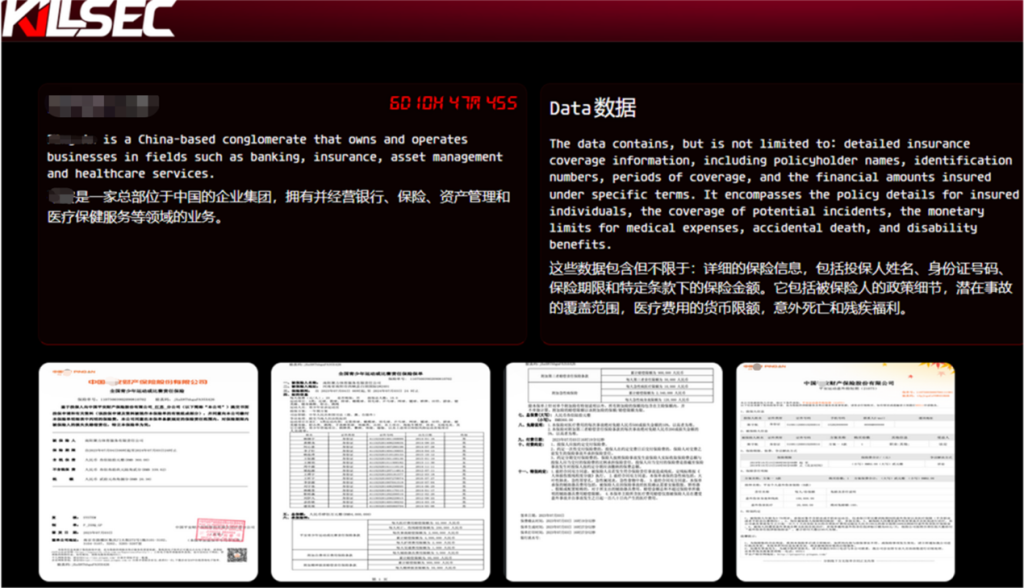
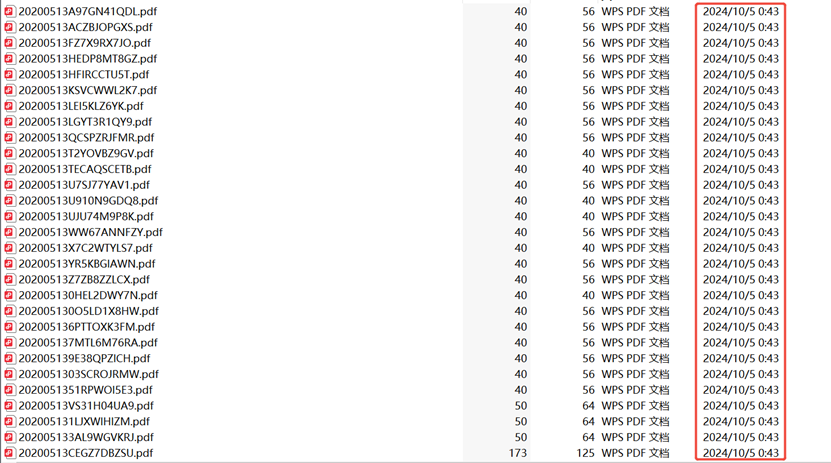
Coincidentally, the KillSec ransomware group also published a post targeting this financial institution on its dark web blog in October 2024:
By comparing and analyzing the data samples and pictures released by the two groups, it is found that there is a high degree of overlap between their file timestamps and content information.
Analysis of Babuk2 Features
Recruitment under the name of Babuk group:
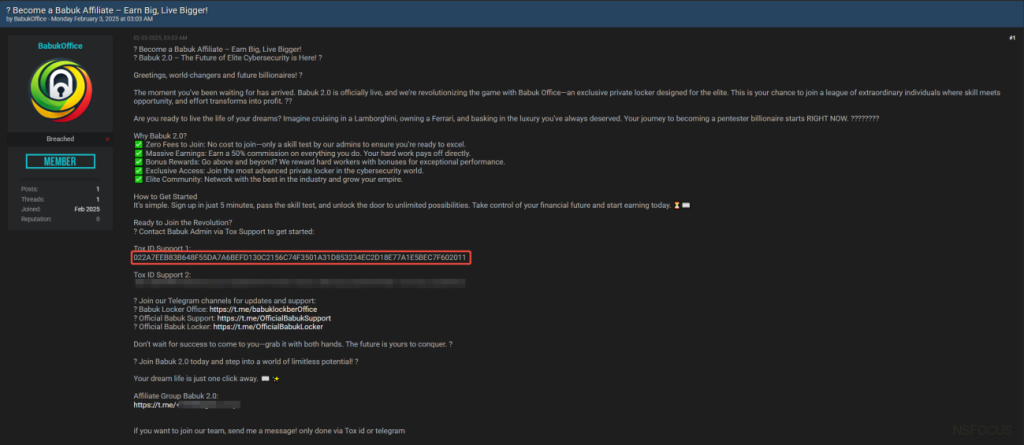
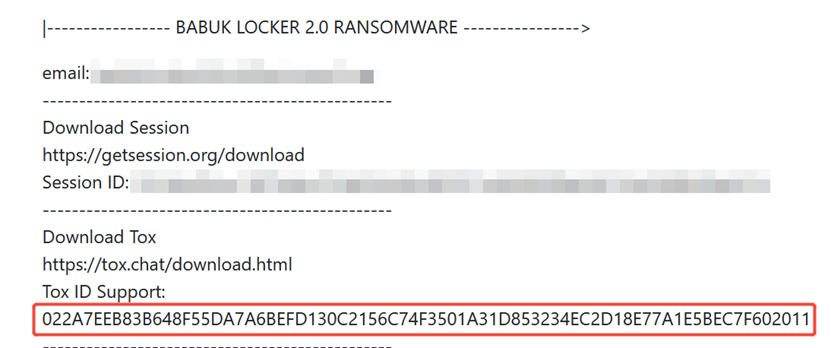
On February 3rd, 2025, someone registered an account on the Breachforums and published a recruitment post in the name of Babuk, but most of the data in the post was confirmed to be previously leaked data.
Upon analysis, it is found that the Tox ID of the released encrypted chat tool matches the one leaked on the dark web by Babuk2. It can be confirmed that they belong to the same group:
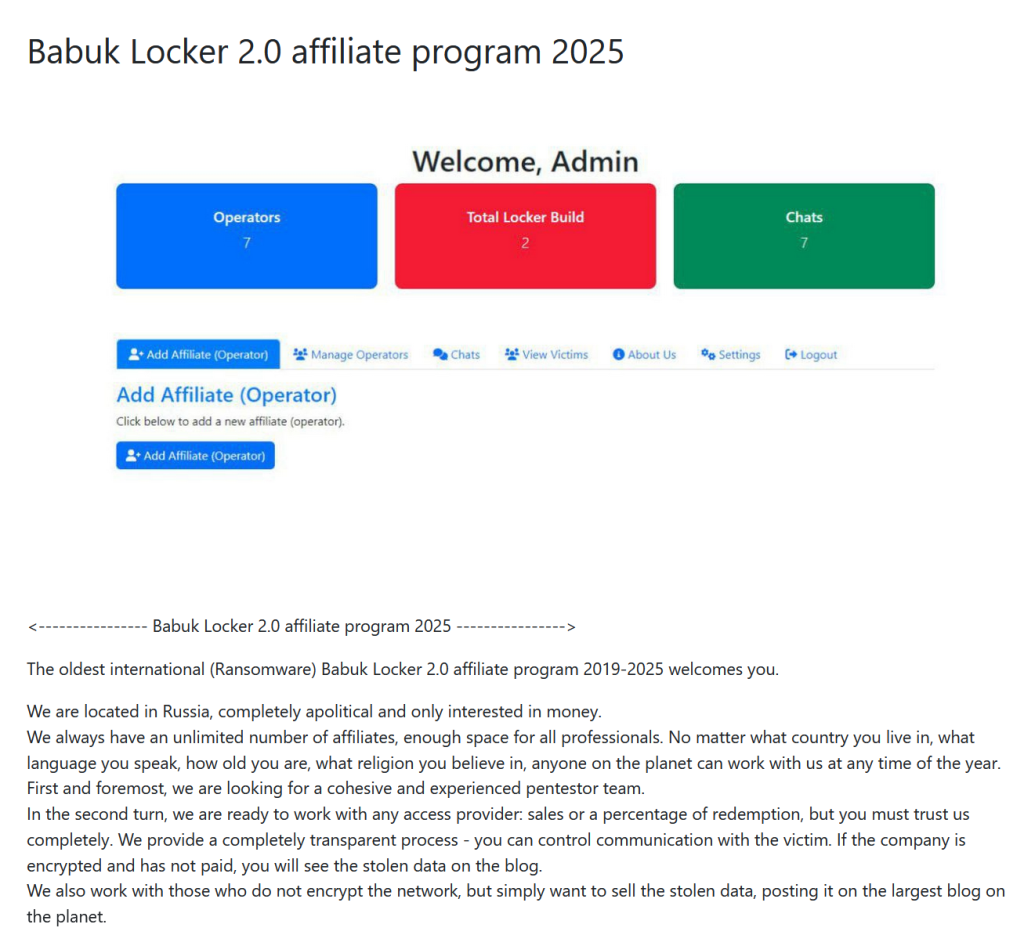
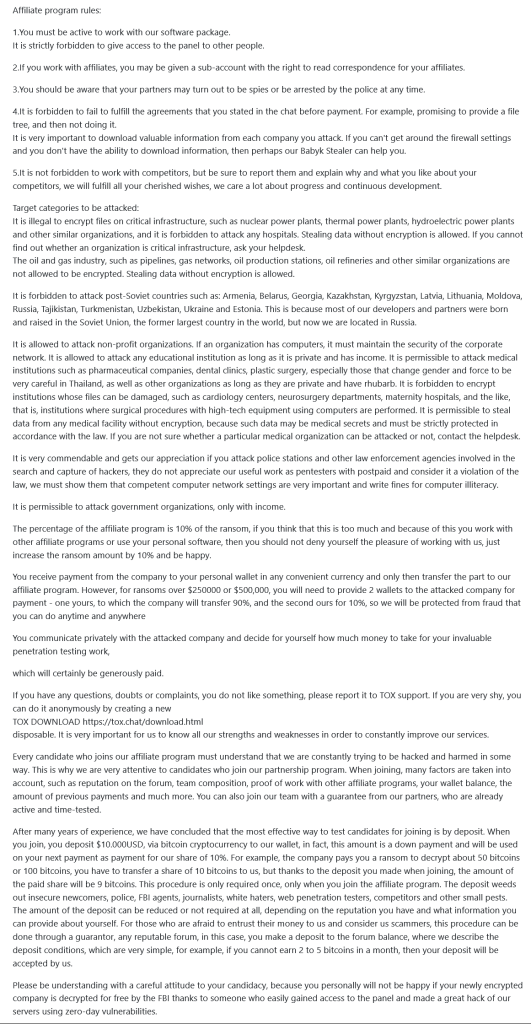
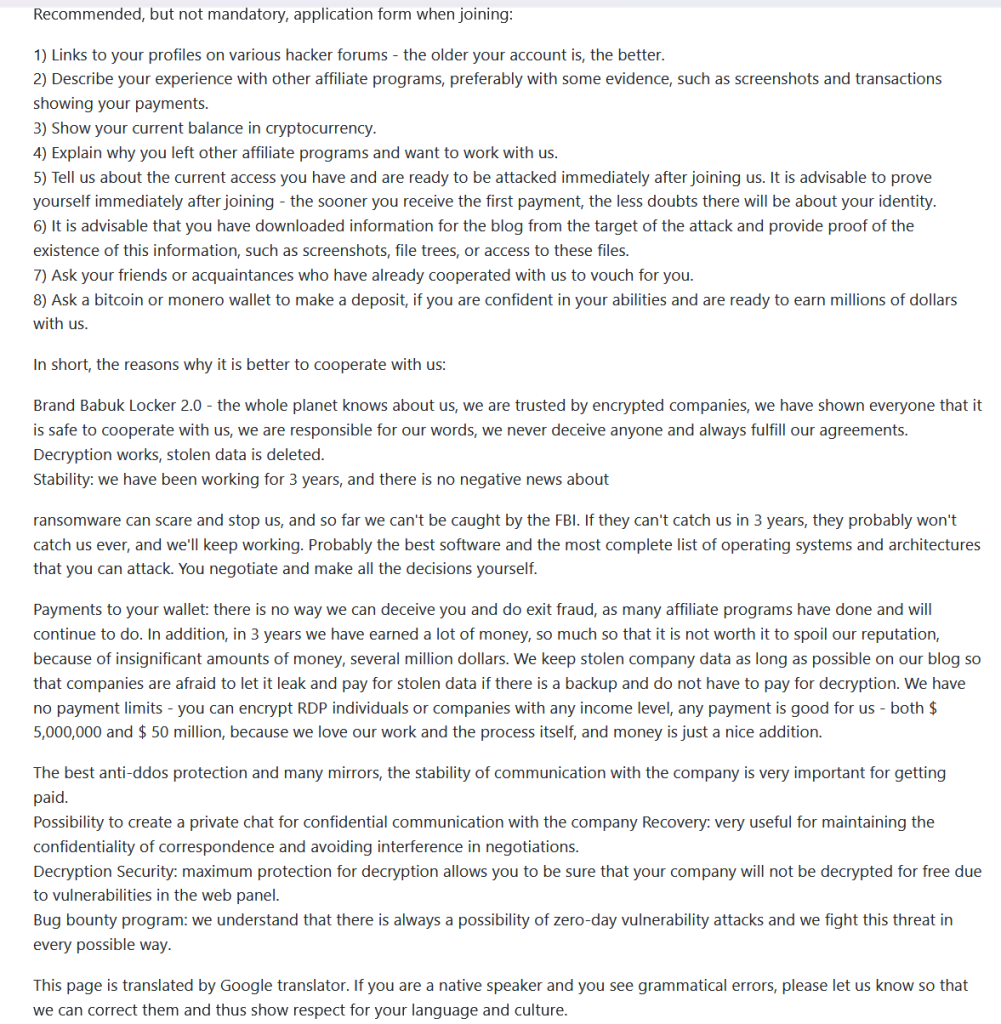
Babuk2’s Affiliate Program is suspected of plagiarism:
Babuk2 launched the 2025 Babuk Locker 2.0 Affiliate Program on its dark web site to seek extensive cooperation, including penetration testing, ransomware operators, data traffickers, etc.
fter analysis, the introduction and rules of Babuk2’s Affiliate Program are highly overlapped with those released by the ransomware group LockBit, such as “the self-proclaimed oldest ransomware (2019-2025)”, “has been in operation for 3 years”, “involving FBI remarks”, and “vulnerability bounty programs”, etc. Therefore, it seems likely that Babuk2 has simply adapted the content copied from LockBit with minor changes. In addition, Babuk2 once publicly posted a message seeking database merchants to trade data (now deleted).
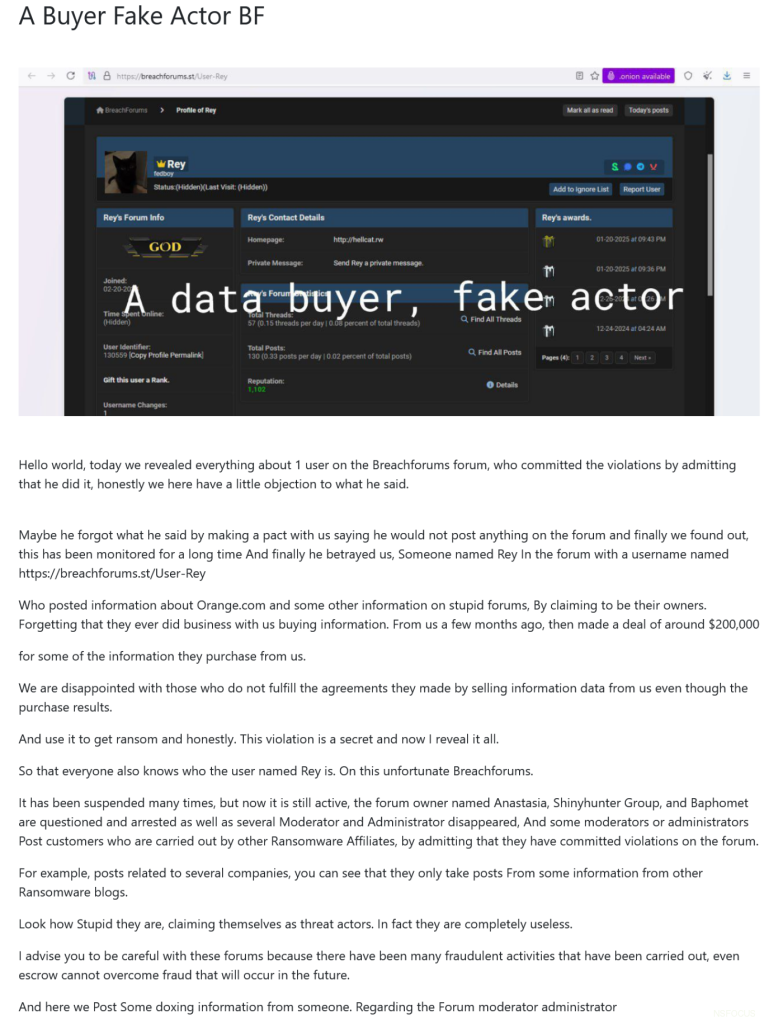
Disputes with members of other ransomware groups:
Recently, Babuk2 has posted a post exposing the user information of the data breach forum (Breachforums), pointing out that there was a data transaction dispute with the user:
According to investigation, the user turns out to be Rey, a core member of the Hellcat ransomware group:
Because Rey posted on X (formerly Twitter): “The so-called Babuk2 is actually the Bjorka/SkyWave group. After failing to sell public data, it released data leaks in the name of the Babuk ransomware group for blackmail. The cases it claimed to have breached, such as the Florida Department of Transportation, Belarusian e-commerce energy system, and French Orange Telecom, were actually the work of Rey himself (Pryx, another member of the Hellcat ransomware group has spoken up to provide relevant evidence).” This is why Babuk 2 publicly released a post online to retaliate against and defame Rey.
Event Summary
1. The Babuk ransomware group was active in 2021, and experienced source code leakage and internal division in the same year. No further activities have been observed since then. The Babuk2 hacker group appeared in January this year. Unlike traditional ransomware attacks, it blackmails its victims mainly by publishing data on newly built dark web leak sites.
2. Babuk2 has released a large number of data leak extortion posts targeting various organizations in a short period of time. The fact that most of these organizations have previously been claimed as victims by other ransomware groups suggests that Babuk2 may not have actually infiltrated their systems. Instead, they could be using data obtained through various means to falsely claim these as their own ransomware successes in order to carry out secondary extortion attempts.
3. Judging from the data of three domestic e-commerce companies released by Babuk2 this time, it should be a patchwork of third-party channel data and historical data, not a recent real intrusion and theft. Moreover, the data leaked by the domestic financial institution and released by Babuk2 is identical to the data content disclosed by the ransomware group KillSec last year.
4. The sample files provided by Babuk2 are all pure formatted data or historical data, lacking proof such as original files and intrusion screenshots. They are suspected to be obtained from third-party channels, underground market transactions or historical data cleaning. Such data is very common on dark web/anonymous platforms.
5. Unlike mature ransomware groups, Babuk2’s behavior is more chaotic (making contradictory remarks, deleting posts, etc.), since the group tries to use the media and public cognition to create influence by impersonating a well-known ransomware group.
In summary, Babuk2, the operator of this incident, has nothing to do with the previous Babuk ransomware group. Instead, it uses previously stolen/disclosed data from well-known companies and units and the Babuk brand to expand its influence and maximize its profits. In recent years, the Ransomware as a Service (RaaS) model has led to the emergence of a large number of cybercrime groups. In addition to traditional ransomware groups, some black and gray market gangs are also moving in this direction. They seek to profit through indirect extortion and bluffing. Therefore, it is essential to remain vigilant and carefully distinguish their activities.
NSFOCUS Recommendations
The data breach involved many units from various industries and multiple countries, with a wide range of impacts. Leaked data information is likely to be used and re-spread by criminals, which is common in identity theft, harassment and spam, social engineering attacks, etc. It may cause economic and privacy harm to users, and may also cause economic and reputational losses to related companies or units.
It is recommended that relevant units take the following measures to deal with it:
1. Investigate the leakage incident so as to determine the cause, scope and impact of the leakage, and take timely measures to limit the loss.
2. If the user’s personal information is leaked, the relevant units should notify the affected users as soon as possible and provide necessary help and support.
3. Companies and organizations should enhance their employees’ awareness and training on security issues, and increase their employees’ attention to data security to prevent such incidents from happening again.
4. For the falsification or use of historical public data for extortion and dissemination, timely announcement clarification shall be made and law enforcement agencies shall be contacted to assist in handling.
5. Invest in or establish professional data breach monitoring and early warning services/capabilities to promptly detect potential data leak risks involving the organization on the dark web and other anonymous channels.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.