On December 7, 2018 security experts from NSFOCUS Fu Ying Labs delivered a speech at Botconf 2018, presenting WASM security threat analysis technologies with researchers from security firms, media personnel, and security practitioners from CERTs (Computer Emergency Response Teams) of various countries. Their striking insights were highly accepted and acknowledged...
Year: 2018
ThinkPHP Remote Code Execution Vulnerability Handling Guide
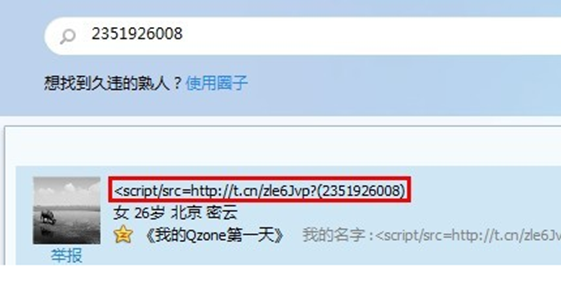
1 Vulnerability Overview Recently, ThinkPHP posted a blog, announcing the release of an update that addresses a high-risk remote code execution (RCE) vulnerability. This vulnerability stems from the framework's insufficient checks on controller names, which, in case forced routing is not enabled, would allow arbitrary code execution or even access...
Personal Computer——File Deletion
Case AnalysisCase Analysis When you delete files from a computer or USB flash drive, just clicking the deletion button or doing a quick formatting does not completely remove files because you can easily recover them using data recovery software. Even after you clear the recycle bin, those deleted files can...
NSFOCUS 2019 Predictions: Email Attachments, IoT, and Cryptominers to be Security Pain Points in 2019
VMblog.com - It's no surprise that 2018 continued to bring an increase in fraud attacks and data security breaches, including those of Facebook and now Marriott. In the past two years, the average number of overall daily searches for keywords such as "personal information disclosure" and "hacker" have been fluctuating...
ThinkPHP 5.x Remote Code Execution Vulnerability Threat Alert
Overview Recently, ThinkPHP posted a blog, announcing the release of an important update that addresses a critical vulnerability. This security update fixes a getShell vulnerability caused by the framework's insufficient checks on controller names in case forced routing is not enabled. The vulnerability, which affects ThinkPHP 5.0 and 5.1, is...
The missing leg – integrity in the CIA triad
Linkedin Eric Vanderburg Information security is often described using the CIA Triad. The CIA stands for Confidentiality, Integrity, and Availability and these are the three elements of data that information security tries to protect. If we look at the CIA triad from the attacker’s viewpoint, they would seek to compromise confidentiality by stealing...