I.Principle
Cross-site scripting (XSS) is a website attack approach in which a hacker or tester tampers with web pages by inserting malicious scripts via HTML injection, in a bid to direct the user’s browser to carry out malicious operations when the user browses web pages.
II. Impacts
XSS poses different threats in different scenarios. Usually, XSS can bring the following types of threat:
- Stealing various user accounts such as online banking accounts and various administrator accounts
- Controlling enterprise data, including reading, tampering, adding and deleting sensitive data of enterprises
- Illegal transfer
- Forcing users to send emails
- Web page trojan
- Taking control of victims’ machines and instructing them to launch attacks against other websites
III. Examples
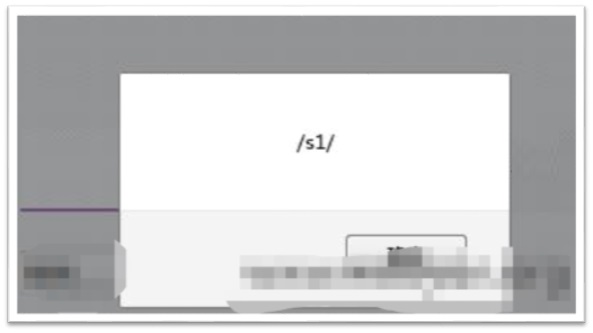
First, find where the user can input and enter test statements. Enter the test statement “/><script>alert(/s1/)</script>” in the “Developer Name” text box on the registration page.
After the registration succeeds, if the test statement is successfully triggered in the personal information area, we can confirm that an XSS vulnerability exists in the website.
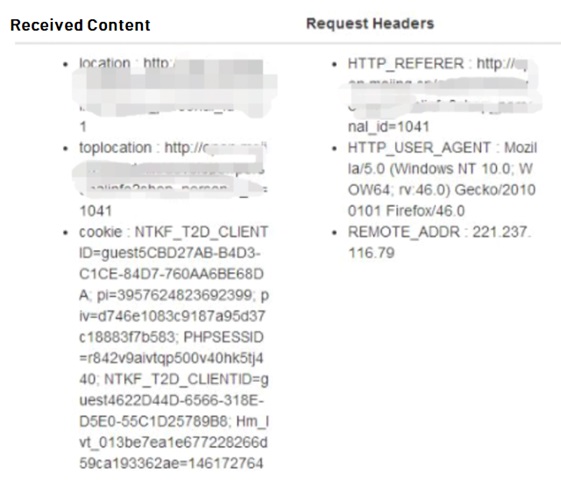
Replace the test statement with the statement used by the XSS platform to obtain cookies and repeat the above steps. Then the statement will execute to obtain cookies as long as as someone is able to check your name. In this way, we can obtain others’ cookies. The following figure shows the cookies of administrators obtained by the XSS platform.
Through a successful login to the system via obtained cookies, we can access to others’ various information.
IV.Protection Methods
Usually, XSS attacks can be defended in one of the following ways:
- Input check. Strictly check the user’s input by filtering the less-than sign (<) and the greater-than sign (>) and enclosing the input in quotation marks in a bid to basically isolate data from code; filter double quotation marks to prevent users from adding custom tags that are not allowed; filter tabs and spaces to prevent keywords from being split; filter script keywords; filter hashtags (#) and ampersands (&) to prevent attackers from tampering with HTML attributes to bypass the check. The input check must be performed on the server, or it can be easily bypassed by attackers.
- Output check. When variables are output to the HTML pages, we can defend against XSS attacks through encoding or escaping, for example, escaping the ampersand (&) to “&”, less than sign (<) to “⁢”, greater-than sign (>) to “>”, a single quotation mark (‘) to “'”, a double quotation mark to “"”, and a slash (/) to “F;”.
- Turn on HttpOnly so that the browser does not allow web pages’ JavaScript to access cookies with HttpOnly attributes. Using HttpOnly can only mitigate XSS attacks, so we still need the above two solutions to defend against XSS attacks.