Overview
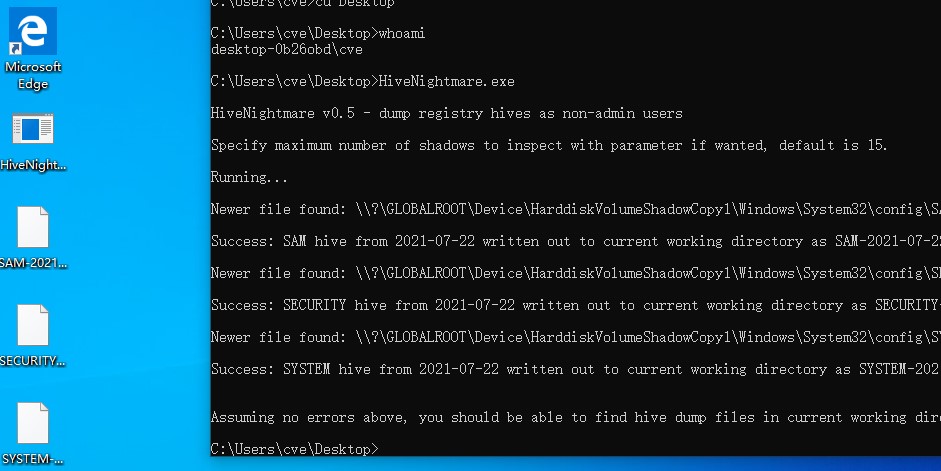
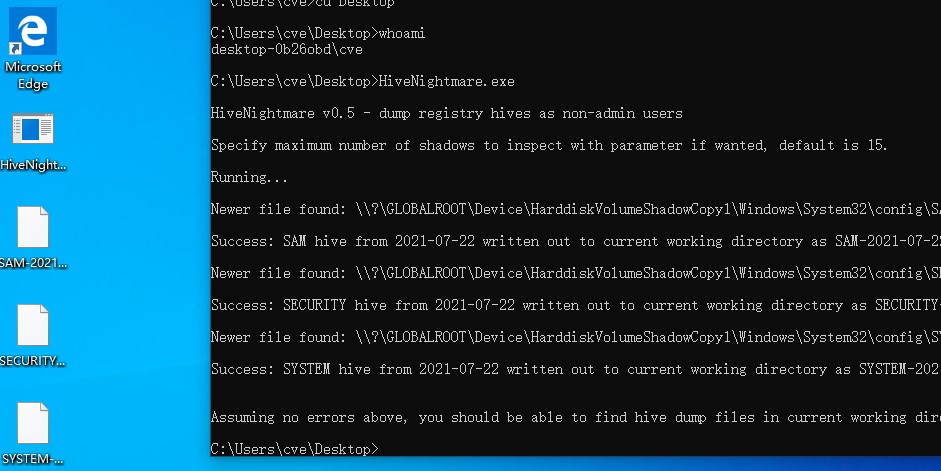
Recently, NSFOCUS CERT discovered a critical security bulletin released by Microsoft to disclose a privilege escalation vulnerability (CVE-2021-36934) in Windows. A privilege escalation vulnerability exists because of overly permissive Access Control Lists (ACLs) on multiple system files (including the Security Account Manager (SAM) database). When a built-in administrator account is enabled in the system, a common user could exploit this vulnerability to run arbitrary code with SYSTEM privileges, in combination with a Pass-the-Hash Attack (PtH). Currently, vulnerability details and the exploit have been made publicly available. Users are advised to check their own system and take preventive measures. NSFOCUS CERT has successfully reproduced this vulnerability:
Reference link: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-36934
Scope of Impact
Affected Versions
- Windows Server, version 20H2 (Server Core Installation)
- Windows Server, version 2004 (Server Core installation)
- Windows Server 2019 (Server Core installation)
- Windows Server 2019
- Windows 10 Version 21H1 for x64-based Systems
- Windows 10 Version 21H1 for ARM64-based Systems
- Windows 10 Version 21H1 for 32-bit Systems
- Windows 10 Version 20H2 for x64-based Systems
- Windows 10 Version 20H2 for ARM64-based Systems
- Windows 10 Version 20H2 for 32-bit Systems
- Windows 10 Version 2004 for x64-based Systems
- Windows 10 Version 2004 for ARM64-based Systems
- Windows 10 Version 2004 for 32-bit Systems
- Windows 10 Version 1909 for x64-based Systems
- Windows 10 Version 1909 for ARM64-based Systems
- Windows 10 Version 1909 for 32-bit Systems
- Windows 10 Version 1809 for x64-based Systems
- Windows 10 Version 1809 for ARM64-based Systems
- Windows 10 Version 1809 for 32-bit Systems
Check for the Vulnerability
Manual Check
Users with a vulnerable system version can run the following command with administrative privileges to check the VSS:
vssadmin list shadows
Users are vulnerable if they enable system protection and create a system restore point (apply the Windows update for the system drive disk (over 128 GB) or install MSI to create VSS shadow copies by default).
Mitigation
Protection Measures
The vendor has released patches to fix this vulnerability. Affected users are advised to take the following measures for temporary protection:
1. Restrict access to the following directory: %windir%\system32\config
Open a Command Prompt as an administrator and run the following command:
icacls %windir%\system32\config\*.* /inheritance:e
Alternatively, open PowerShell as an administrator to run the following command:
icacls $env:windir\system32\config\*.* /inheritance:e
2. Remove VSS shadow copies:
Delete any system restore points and Shadow volumes that exist prior to restricting access to %windir%\system32\config.
3. Disable the built-in administrator account provided that the normal system running is not affected.
Note: Removing VSS shadow copies may affect system restoration, including data restoration with a third-party backup application. However, the vulnerability exploitation is only prevented when access is restricted and VSS shadow copies are deleted.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA). A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.