Overview
Recently, NSFOCUS CERT detected that Vite issued a security announcement and fixed the arbitrary file reading vulnerability of Vite (CVE-2025-30208). Since the Vite development server does not strictly verify the path when processing URL requests, unauthenticated attackers can bypass path access restrictions by constructing special URLs to obtain sensitive files outside the project root directory. At present, the vulnerability details and PoC have been made public. Relevant users are requested to take measures for protection as soon as possible.
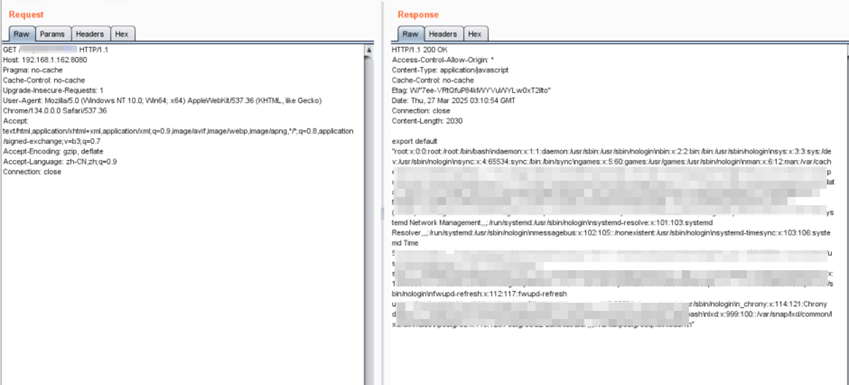
NSFOCUS has successfully replicated this vulnerability:
Reference link: https://github.com/vitejs/vite/security/advisories/GHSA-x574-m823-4x7w
Scope of Impact
Affected version
- 6.2.0 <= Vite <= 6.2.2
- 6.1.0 <= Vite <= 6.1.1
- 6.0.0 <= Vite <= 6.0.11
- 5.0.0 <= Vite <= 5.4.14
- Vite <= 4.5.9
Note: Affects applications that expose the Vite development server to the network (enable –host or configure server.host).
Unaffected Version
- Vite >= 6.2.3
- 6.1.2 <= Vite < 6.2.0
- 6.0.12 <= Vite < 6.1.0
- 5.4.15 <= Vite < 6.0.0
- 4.5.10 <= Vite < 5.0.0
Detection
Manual detection
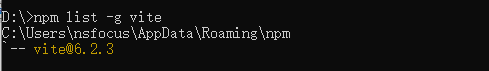
Relevant users can check whether the current service is affected by this vulnerability by checking whether the current Vite version is within the affected range. The following commands can be used to view the npm global installation:
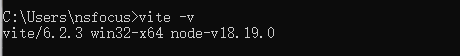
Users can also run the vite -v command in the terminal command line to view:
Tool detection
NSFOCUS Automated Penetration Test Tool (EZ) has supported Vite’s fingerprint identification and CVE-2025-30208 vulnerability risk detection (Note: For the enterprise version, please contact NSFOCUS sales personnel).
Users can use the following command for vulnerability detection:
| ./ez webscan –pocs vite -u https:192.168.1.41:443/ |
Download link of the tool: https://github.com/m-sec-org/EZ/releases
Cloud detection
NSFOCUS External Attack Surface Management (EASM) supports the Internet asset investigation of CVE-2025-30208 vulnerability risks. It has helped service customers complete exposure surface investigation and risk verification, and timely conduct vulnerability early warning and closed-loop disposal before threats occur.
Interested customers can contact NSFOCUS’s local regional colleagues or send an email to rs@nsfocus.com for detailed consultation.
Local screening
NSFOCUS CTEM solution can proactively discover and troubleshoot Vite-related assets and CVE-2025-30208 vulnerabilities:
The user uses the external attack surface discovery function to synchronize CVE-2025-30208 vulnerability clues to the cloud, and obtain the affected assets of the target unit by asset mapping. The mapping supports fingerprinting or PoC scanning, and the calling of various vulnerability scanning devices.
Mitigation
Official upgrade
At present, a new version has been officially released to fix this vulnerability. Please upgrade the protection for affected users as soon as possible. Download link: https://github.com/vitejs/vite/releases
Temporary protective measures
If relevant users cannot perform the upgrade operation for the time being, access restrictions can be imposed on Vite development servers to temporarily relieve the problem without affecting services.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.
