2019 Cybersecurity Insights -13

July 29, 2020
Cryptojacking Malware
In 2019, the pickup in cryptocurrency prices led to an increase in the number of cryptojacking malware families. Of all these families, Monero mining trojans still took a dominant place. EternalBlue and weak password cracking were the major methods for ransomware families to compromise large enterprises in financial and telecom sectors and spread themselves. At the same time, to defeat detection devices, cryptojacking malware families have been constantly upgraded to evolve into more variants that feature better stealth and a modular design.
(more…)2019 Cybersecurity Insights -12

July 22, 2020
Ransomware
In 2019, ransomware was still a major type of threats that haunted people around the world. The most prominent families were GlobeImposter, GandCrab, and WannaCry, which were extremely active and had far more variants than others. According to NSFOCUS Security Labs’ observation, the number of ransomware families and variants increased sharply in four months from May to August 2019, which was somewhat attributable to the soaring prices of major cryptocurrency types. These families used diverse compromise methods to attack a wide variety of sectors, posing a severe threat to organizations’ and individuals’ data. Through ongoing monitoring, NSFOCUS Security Labs finds that the following trends of ransomware took shape in 2019:
(more…)2019 Cybersecurity Insights -11

July 15, 2020
Cryptomining Traffic
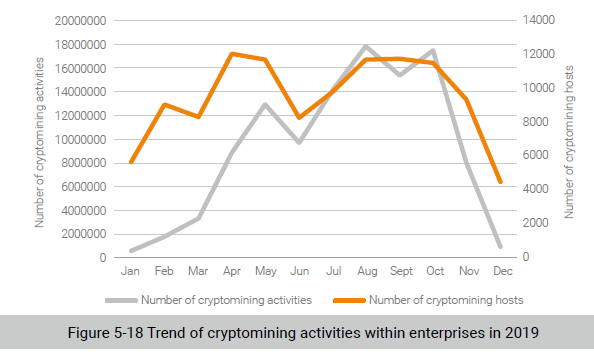
Based on all sorts of security alert data from NSFOCUS Managed Security Service (MSS), we made a quantitative analysis of cryptomining activities and hosts in enterprises in 2019 and found that the cryptomining topicality is positively correlated with the cryptomining market trend.
2019 Cybersecurity Insights -10

July 10, 2020
Second Largest Gang by the Number of Attack Sources
The second largest gang in terms of the number of attack sources generated the largest traffic. This gang had 23,000 recidivists and favored volumetric SYN flood attacks. According to historical attack records, 99.54% of recidivists had resorted to this kind of attack. This gang stayed active from January to October and was at its busiest in May.
Figure 5-14 shows the monthly quantity trend of attack sources and attack targets of this gang. We can see that this gang remained active from January to October, having more attack sources in January, April, May, and June. On average, 6000 active attack sources launched attacks against seven targets each month.
(more…)2019 Cybersecurity Insights -9

July 8, 2020
In 2019, 7% of recidivists1 were responsible for 78% of DDoS attacks. Obviously, recidivists are too menacing to overlook. Several groups of DDoS recidivists often work together to initiate attacks. Such groups are collectively referred to as an “IP gang”. In 2019, a total of 60 DDoS gangs were detected, including 15 ones that contained more than 1000 attack sources. The largest gang, formidably, consisted of 88,000 attack sources. On average, 35,000 attack sources remained active every month. Therefore, we should keep vigilant on gang behavior and attack gangs. In this section, we will profile and analyze major attack gangs.
(more…)2019 Cybersecurity Insights -8

July 7, 2020
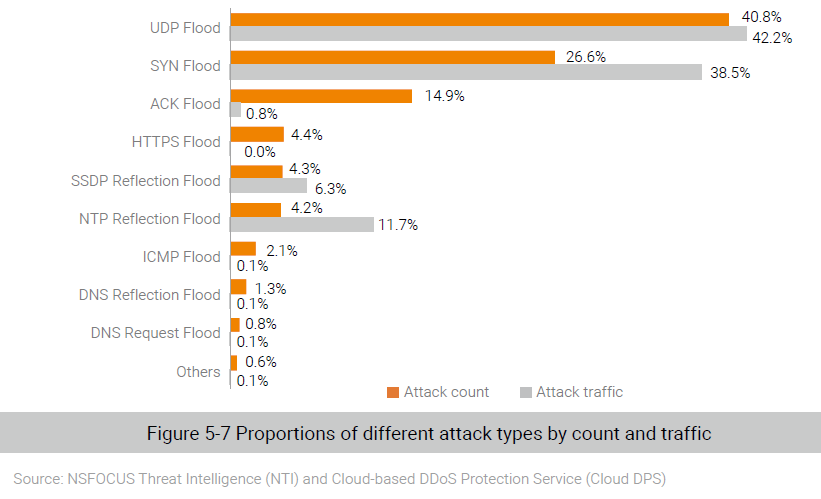
In 2019, most frequently seen attacks were UDP floods, SYN floods, and ACK floods, which together accounted for 82% of all DDoS attacks. By contrast, reflection attacks took up only 10%. Compared with 2018, reflection attacks rose slightly in number, but remained small in proportion.
2019 Cybersecurity Insights -7

July 3, 2020
Key Findings:
Maturity: The technical maturity of attackers keeps growing, opening more possibilities than DDoS attacks for attackers to garner profits.
Combination: Of all DDoS attacks in 2019, 12.5% employed multiple vectors. This percentage was even higher among super-sized attacks (> 300 Gbps) to reach more than one-third. These factors have posed a greater challenge to the performance of cleaning devices, the stability of cleaning lines, and the effectiveness of defense operations.
Recidivists: In 2019, a total of 1.3 million DDoS recidivists (involved in more than 20 attacks) were spotted, 7% of whom were responsible for 78% of attacks. Recidivist behavior deserves continuous attention.
Gangs: In 2019, a total of 60 DDoS gangs were detected, including 15 ones that contained more than 1000 attack sources. The largest gang, formidably, consisted of 88,000 attack sources. On average, 35,000 attack sources remained active every month. Therefore, we should keep vigilant on gang behavior and attack groups.
(more…)2019 Cybersecurity Insights -5

June 29, 2020
Web Attack Trend
Websites, which enterprises or individuals use to provide services for users, are usually the first choice of hackers during attacks. Web attacks in 2019 clung to traditional patterns and methods, including server information disclosure, resource leeching, cross-origin resource sharing (CORS), SQL injection, and cookie poisoning, which together accounted for 89% of web attacks. Given their high popularity, these traditional methods will continue to be a top concern for defenders.
(more…)2019 Cybersecurity Insights -2

June 17, 2020
Key Findings [Vulnerabilities] 2019 saw a steady increase in high-risk vulnerabilities and in Internet of Things (IoT) vulnerability exploits. Of server-related vulnerabilities, web vulnerabilities stole the spotlight and the Windows remote desktop vulnerability CVE-2019-0708 had a far-reaching impact. [Malware] Ransomware and cryptojacking malware were two most active types of malware in 2019. In this year, […]
Cybersecurity Insights -1

June 11, 2020
Executive Summary
2019 witnessed more intense challenges in global political and economic orders. Restricted by various conventions, agreements, and protocols, traditional military means are now the last resort. In this context, attacks on the financial sector and on the cyberspace become the first choices for rival countries to try on their modern military strategies. Predictably, these attacks will probably become regular approaches in the future. By the time when the 2018 Cybersecurity Insights was released, the following trends had taken shape regarding cybersecurity: The window between the discovery of a vulnerability and the effective exploitation of this vulnerability was shortened; the DDoS attack size steadily grew; emerging threats like those from the Internet of Things (IoT) rose sharply; such malware as backdoors, cryptojackers, worms, trojans, and botnets were still active. When it comes to information disclosure, the AcFun website was hacked, leading to a leak of nearly 10 million pieces of user data; India’s Aadhaar (India’s national ID database) number leak affected 1.1 billion citizens. Information disclosure events have hit record highs for six years in a row since 2013. The four enterprises, namely Facebook, Equifax, British Airways, and Marriott International, together were fined approximately USD 9 billion for privacy and information leaks, more than the aggregate market value of the cybersecurity industry in China in that year.
(more…)