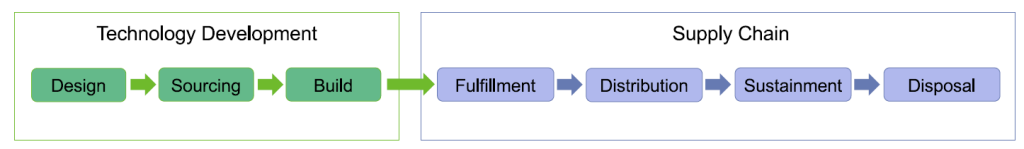
To deal with threats from supply chains and ensure the security of their own IT infrastructure, companies shall set a list of software compositions to sort out the supply chain products, identify and manage key software suppliers, control security risks through security assessments at all stages of the life cycle of supply chains, and reduce the threats caused by supply chain attacks.
Development Process Security Assessable
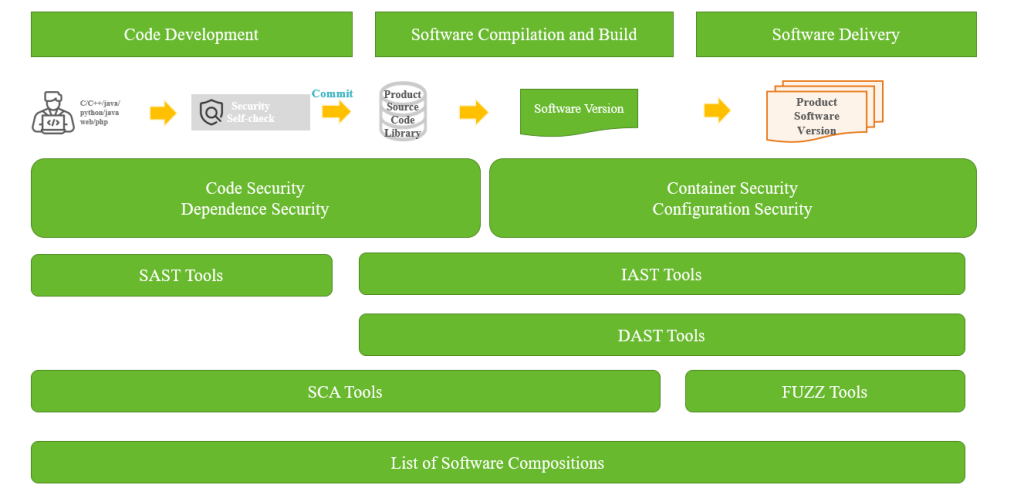
In the development life cycle of software, vulnerabilities are introduced not only by the source code written by developers but also by the open-source components and development and construction tools that the software depends on. Based on the development and construction process of software, companies shall build the security assessment capabilities of the development process from the following aspects.
• Security control of open-source component introduction
Due to the advantage of development cost, the wide use of open-source components (including development frameworks and functional components) in projects has become the mainstream development method. In the process of system development, the risks of introduced open-source components shall be strictly controlled to eliminate known vulnerabilities before software delivery and operation.
The security assessment capability of open-source components is provided by Software Composition Analysis (SCA). During code writing, vulnerability analysis is carried out for third-party components, on which the software relies, through SCA tools. Developers will deal with the components with vulnerabilities in a timely manner.
• Source code vulnerability control
During system development, non-standard secure code will also bring vulnerability risks, such as SQL injection vulnerabilities caused by SQL statement splicing.
In order to reduce source code vulnerabilities in the development process and improve security, Static Application Security Testing (SAST) can be used to scan the source code in the development of IDE tools, and Continuous Integration or Interactive Application Security Testing (IAST) can be used to detect source code vulnerabilities through taint analysis when the system is running.
Delivery Security Assessable
Software y refers to developers completing the packaging of finished products and delivering them to downstream users. It is the starting point for downstream companies to introduce supply chain products. As a supplier, in addition to ensuring the security of delivered software, it shall also deliver the list of software compositions. After obtaining the list, downstream companies in the supply chain can also provide their downstream companies and end users with the list maintained by themselves, so that end users can analyze and assess the security of the software supply chain according to third-party information such as security advisory and threat intelligence monitoring.
Operation Security Assessable
After the software is delivered and put into operation, suppliers shall provide security assurance services within the life cycle and fix the vulnerabilities in a timely manner. End users shall also incorporate products into the company asset management according to the SBOM from suppliers, regularly conduct asset security assessments, and reinforce and fix the affected products in combination with vulnerability warnings.
In terms of implementation technology, there are many similarities between the assessable capabilities of software supply chain compositions and the security development governance within the company. It should be noted that the software supply chain security focuses more on the characteristics, such as different components and dependencies, involved in each iteration or each construction in the whole software life cycle, and also on the security assessment status of the whole system.
Previous posts on software supply chain security:
- Software Supply Chain Security: Overview
- Threats against Software Supply Chain Security
- The Increasing Trend of Software Supply Chain Attacks
- The Increasingly Complex and Varied Vectors to Attack Software Supply Chain
- Security Concept for Software Supply Chain (Part 1) — Transparency of Software Supply Chain Compositions
