Industry Macro Background and the Software Supply Chain Crisis
By 2026, the deepening of global digital transformation, coupled with the proliferation of Generative AI and large language models, is reshaping software development. The industry is shifting from being “efficiency-driven” to “governance-driven.” The root cause lies in the loss of visibility and engineering control within the modern software development lifecycle.
1. Shadow Engineering Caused by Architectural Decoupling
While cloud computing and microservices accelerate delivery, they have also led to fragmented and complex engineering environments: code, tools, and artifacts are scattered, and workload topologies are intricate. This results in a loss of code ownership, making it difficult to respond quickly to failures or vulnerabilities. Crash Override defines this behavior—development and deployment that occur outside centralized control, are unapproved, and are difficult to track—as Shadow Engineering. This is the fundamental cause of compliance failures, latent security vulnerabilities, and prolonged recovery times from incidents.
2. Ambient Programming and Shadow AI Risks Introduced by AI Penetration
The deep penetration of AI into development processes has become a catalyst for a visibility crisis. Developers are using coding assistants on a large scale, accelerating output but amplifying the exposure surface of the software supply chain. Enterprises face shadow AI risks: security departments are unable to track unauthorized use of external tools, nor can they trace whether the generated code contains malicious dependencies or high-risk functions. Traditional application security static analysis tools are ineffective, unable to distinguish between human and AI-generated code, nor can they dynamically track agent changes.
Founding Team Background
Crash Override was founded in 2022 and is headquartered in New York, USA. The company’s two core founders, John Viega and Mark Curphey, have, over more than two decades of their careers, participated in and led nearly every major technological revolution in the field of modern application security.
Crash Override’s current CEO, John Viega, is an early advocate of software security engineering. As early as late 2000, Viega co-authored the industry’s first security monograph aimed at developers, “Building Secure Software.” This book contributed to Microsoft’s “Trustworthy Computing” initiative, permanently altering the security baseline of the software industry. With both academic and engineering backgrounds, Viega is the co-designer of the AES-GCM encryption mode and the original author of Gnu Mailman. Prior to founding Crash Override, he established Secure Software, held key positions at companies like McAfee, and ran the cloud-native security startup, Capsule8.
Co-founder and CMO Mark Curphey is the founder of the globally influential open-source security organization OWASP, where he promoted the establishment of Web application security standards. Curphey has close ties with the “Foundstone Mafia” and possesses a strong professional network. He previously founded SourceClear (later acquired by Veracode) and OpenRaven.
The two founders met over twenty years ago. After interviewing hundreds of CISOs and VPs of Engineering, they concluded that continuing to patch existing security tools or develop new scanners was the wrong approach. Based on their insight into the loss of visibility in modern software engineering, the duo decided to join forces to tackle the biggest challenge in the DevOps field.
The naming of “Crash Override” carries subtle dual connotations within the cybersecurity industry: while it was once the codename for a type of malware, as a company name, its inspiration is derived purely from the protagonist’s hacker handle in the classic 1995 film “Hackers.” This choice reflects the founding team’s tribute to geek spirit, underlying technology, and disruptive innovation. This geek culture is also expressed in their public relations. For instance, in April 2023, Crash Override painted a graffiti mural in Amsterdam, parodying the “Hackers” movie poster but replacing the stars with computer science pioneers Grace Hopper and Alan Turing, as a tribute to code breakers.
Consensus in the Capital Market and Strategic Ecosystem Layout
With its technology directly targeting the core of the software supply chain and the founders’ exceptional track records, Crash Override quickly gained favor from top-tier global venture capital firms, setting new records in the sector for fundraising scale.
1. An Unconventional Mega Seed Round
In August 2025, Crash Override announced the completion of a $28 million seed funding round. Prior to this, the company had secured $5.8 million in initial seed funding to preliminarily validate its technology prototype aimed at eliminating complexity and information silos in security operations. Within just three years of its founding, and before the full commercialization of its product, Crash Override has accumulated over $33.8 million in capital.
Given the current trend of conservative startup fundraising, a single seed round of $28 million is rare, surpassing the Series B funding scale of many mature companies. This phenomenon not only reflects the capital market’s recognition of the urgency within the software supply chain security and AI code governance sectors but also underscores the investment community’s trust in the technical execution capabilities of the Crash Override founding team.
2. Top-Tier Investor Lineup and Blackstone’s Technology Infusion
Crash Override completed its funding round co-led by Google Ventures (GV) and SYN Ventures, with participation from Blackstone’s Innovation Investments group and Bessemer Venture Partners.
Erik Nordlander from GV and Jay Leek from SYN Ventures have joined the board of directors. The funds will be used to accelerate the R&D of the Engineering Relationship Management platform, expand global market reach, and strengthen ecosystem partnerships.
In a rare move, strategic investor Blackstone injected an internally developed and battle-tested modular scanning and orchestration framework codebase into Crash Override as part of the transaction. This codebase directly forms the core underlying architecture of Crash Override’s open-source project, Ocular. Concurrently, the framework’s lead engineer also left to join Crash Override. This technology infusion has equipped Crash Override with the practical ability to handle complex enterprise environments from its early stages, constructing a formidable and difficult-to-surpass technological barrier.
The Path to a Breakthrough: The Theoretical Reconstruction of Engineering Relationship Management
After in-depth interviews with hundreds of enterprise executives troubled by shadow engineering and alert fatigue, the Crash Override team recognized that attempting to resolve the DevSecOps dilemma by simply providing more and faster vulnerability scanners is merely a temporary fix. To fundamentally eliminate the sense of loss of control caused by infrastructure fragmentation and shadow AI, Crash Override has abandoned the traditional passive model of alerting and patching. It has pioneered the definition of a new category of enterprise tooling: the Engineering Relationship Management (ERM) platform.
1. Drawing Inspiration from CRM Systems: Reshaping the Engineering Collaboration Map
The most direct analogy for understanding the underlying logic of an ERM platform is the revolutionary product in the sales management field—the CRM system.
Before the advent of modern CRM systems, enterprise customer data was extremely fragmented: contact information was scattered in salespeople’s personal notes, sales funnel data was isolated in Excel spreadsheets, and communication records were buried within personal email systems. Management lacked visibility into sales progress, customer churn risks, and the overall business situation. When a key salesperson left, all customer knowledge would disappear with them.
Similarly, in today’s DevOps field, critical engineering data is in the same fragmented state as sales data once was. Code, build scripts, cloud configurations, vulnerability alerts, and developer behaviors are isolated across dozens of disparate SaaS tools.
The strategic value and mission of the ERM platform lie in its role as a piece of infrastructure that connects these isolated data points. It deeply weaves together dispersed code repositories, cloud infrastructure, third-party dependencies, build records, deployment trajectories, and every engineer involved in development, forming a relational graph with temporal evolution and spatial topology.
2. Ending Security Noise: Cryptographically Verifiable Change Records
The Crash Override ERM platform transforms static, isolated engineering assets into a dynamic relationship network, establishing a cryptographically verifiable single source of truth and an immutable change record.
This architectural upgrade changes how enterprises evaluate R&D efficiency and perceive security posture. It shifts from relying on manual cross-platform guesswork and passive alert response to strategic decision-making based on engineering relationship graphs. When a service goes down or a monitoring tool triggers an alert, security analysts no longer need to ask, “Who wrote this code?” The ERM platform enables instantaneous, automated traceability, pinpointing the code commit that caused the failure, the developer who triggered the build, and the environment variables that mutated. By establishing accountability, the ERM platform eliminates noise in security operations, reduces mean time to recovery (MTTR), and enables more efficient, low-friction cross-team collaboration and trust mechanisms.
Deconstructing the Core Underlying Technology: Deep Build Inspection and AI Governance Modules
The realization of the ERM concept relies on hardcore underlying data capture mechanisms. Crash Override provides probes deeply embedded in the modern software lifecycle.
1. Core Engine: Deep Build Inspection Technology
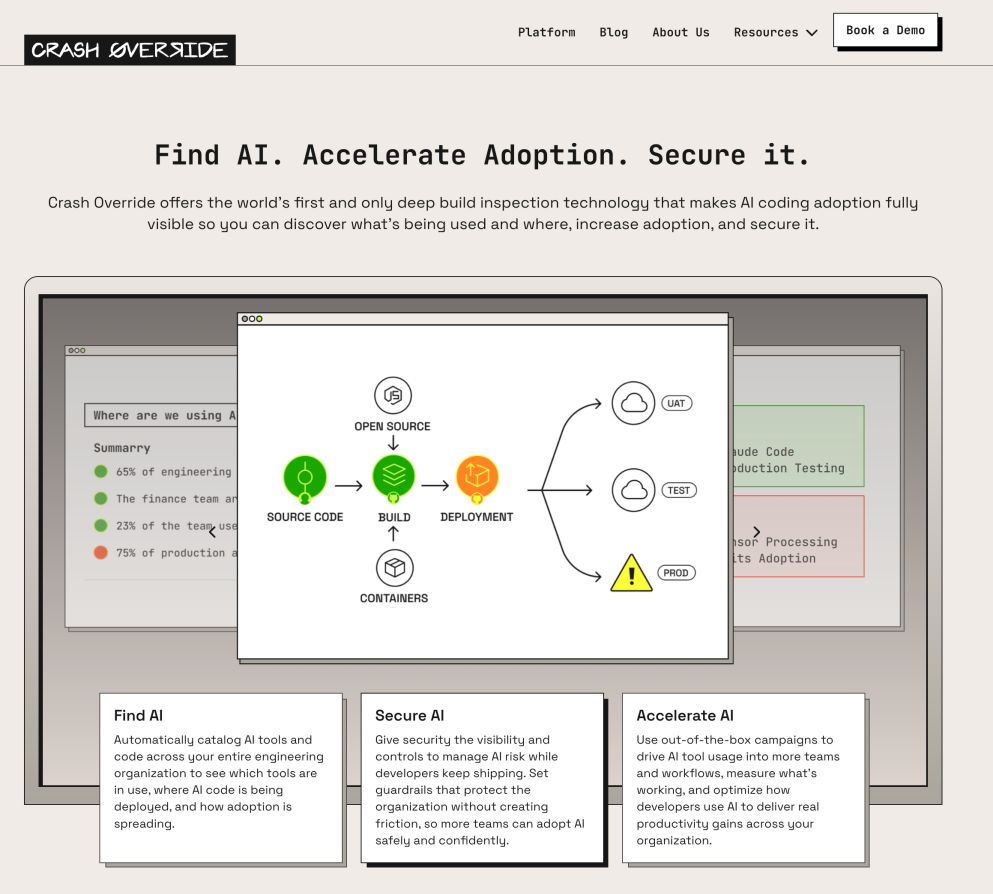
The core technology of the Crash Override platform is the world’s first Deep Build Inspection technology.
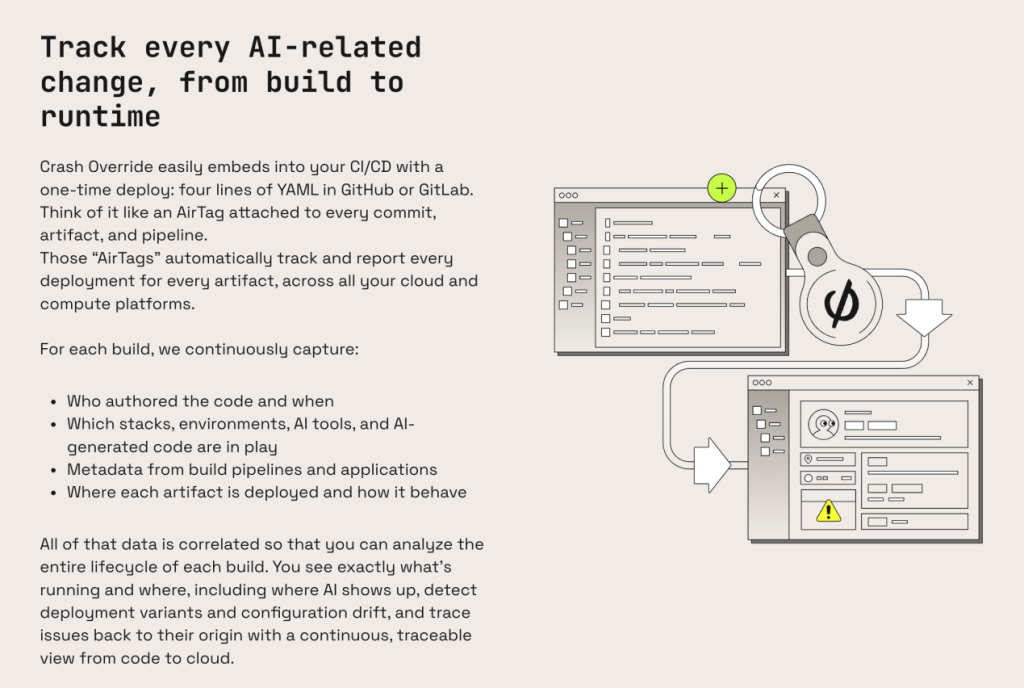
Existing system monitoring primarily focuses on runtime state, inferring causes of system crashes through massive log analysis. Deep Build Inspection shifts the monitoring dimension forward, objectively recording how a system was built, who triggered the pipeline, and the covert changes that occurred during code compilation.
Lightweight Integration and Global Coverage: This technology is extremely lightweight to deploy and causes zero disruption to developers. Security or engineering teams simply need to inject four lines of YAML code into configuration files for GitHub Actions, GitLab CI, or other mainstream CI/CD pipelines. Enterprise-wide global probe deployment can be completed in minutes, without the need to install traditional agent clients on every server.
Digital Tracing: This mechanism effectively injects a highly tamper-resistant digital tracer into every line of code change flowing through the pipeline and every third-party library file pulled. During each build process triggered by a code commit, the Deep Build Inspection engine delves deep into the pipeline’s memory and process levels, continuously and silently capturing rich contextual data:
- Provenance and Identity Verification: Precisely verifies the true author of a code commit, records immutable nanosecond-precision timestamps, and uses cryptographic methods to prevent forgery of commit records and audit logs.
- Environment Variables and Implicit Dependencies: Records the activated tech stack versions at build time, the instantaneous state of all environment variable configurations, each shell command step executed by the pipeline, and even captures temporarily downloaded and executed third-party scripts.
- Shadow System Detection and Beacon Interception: Identifies unauthorized open-source components called and downloaded during the build process. More critically, by analyzing the characteristics of generated code patterns and sniffing vendor beacon traffic, it accurately detects which AI coding assistants are being used (e.g., unauthorized outbound connections to large model APIs).
- Lifecycle Tracking: From the moment source code is compiled into a binary container image or executable artifact, its digital lineage is tracked throughout its entire lifecycle. When that artifact is ultimately pushed to and run on compute nodes in AWS, Azure, or GCP, the ERM platform can establish a direct mapping link from the cloud runtime back to the source code branch.
2. A Closed-Loop AI Governance Framework: Discover, Deepen, and Safeguard
To accelerate output, developers are extensively using unauthorized AI coding assistants or public large model APIs, creating a “Shadow AI” blind spot that bypasses security oversight. This not only prevents security teams from tracing whether generated code contains malicious dependencies or “logic hallucination” glue code—leading to compliance audits and intellectual property crises—but also renders traditional static analysis tools, which cannot distinguish between human and machine code, completely ineffective.
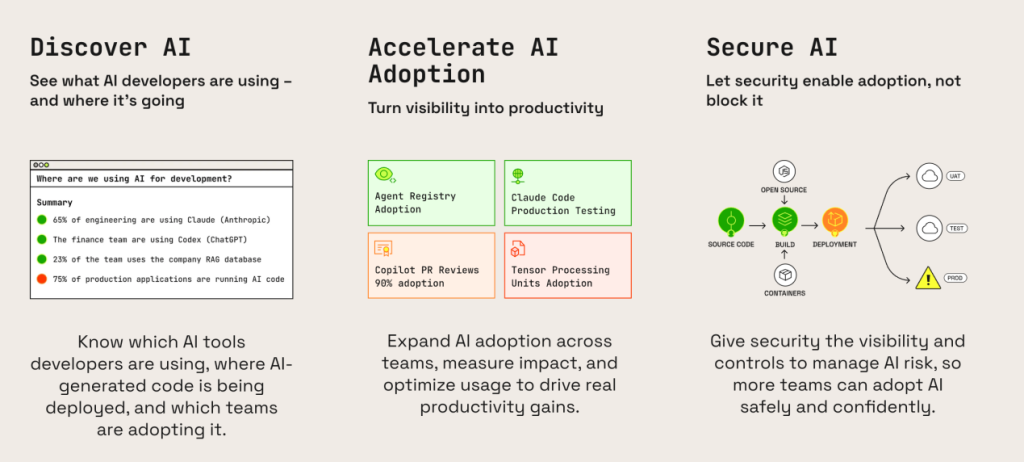
Confronting the chaos brought by AI, the platform presents a structured three-step closed-loop governance framework of “Discover, Deepen, Safeguard” through an intuitive UI interaction. After Crash Override collects telemetry data, it aggregates it into two core data pillars: a global dynamic directory and an immutable change record. Based on this foundation, it supports the full-lifecycle AI governance module.
- Discover AI Traces: Eliminate Shadow AI Blind Spots: The platform automatically inventories the usage of all AI tools within the organization and presents them in real-time on a dashboard: which development teams are compliantly using GitHub Copilot Enterprise, and which outsourced personnel are using unvetted public LLM APIs. It traces which critical production environments AI-generated code fragments have penetrated, eliminating audit blind spots and IP risks caused by Shadow AI.
- Deepen AI Application: Quantify Productivity Gains: Security tools are no longer a hindrance to business development. Crash Override transforms security visibility into a productivity tool. The platform includes built-in operational activity templates to help engineering executives accurately measure and compare the productivity improvements brought by specific AI assistance tools to different development teams in terms of code output, build success rates, and other metrics. Based on this data, management can optimize resource and budget allocation, promoting the safe adoption of legitimate and efficient AI tools within the enterprise.
- Safeguard AI Security: Low-Friction, Full-Chain Guardrails: To manage AI risks without impacting development velocity, the platform provides automated, low-friction security guardrails. For example, when a build task containing AI-generated code flows through the pipeline, the platform can automatically generate an SBOM (Software Bill of Materials) with zero latency at the CI/CD stage, preventing the compilation of non-compliant functions. This achieves SLSA Level 2 build provenance compliance and automatically manages certificates and intercepts tracking before problematic code can disrupt the production environment.
Building an Industry-Standard Open Source Ecosystem: The Chalk and Ocular Projects
The high value of the commercial ERM platform lies in its unique underlying technological ecosystem. To seize the initiative in setting standards for cloud-native security technology and give back to the open-source community, Crash Override has launched two open-source projects, Chalk and Ocular, focused on tracing and orchestration engineering implementation.
1. The Chalk Project: A Global Marking and Tracing Framework
Chalk is positioned as the “GPS” or “digital tracer” for the software development lifecycle, enabling code provenance and lifecycle correlation with a minimalist mechanism.
When developing Chalk, the Crash Override team adopted a pragmatic engineering philosophy. 68.0% of the core code is written in Nim (a systems programming language that compiles to efficient C code), supplemented by Python, TypeScript, and C. Founder Mark Curphey emphasizes that this choice returns to the essence of “choosing the right tool for performance problems,” ensuring Chalk’s injection operations on high-concurrency build servers do not slow down CI/CD pipelines. It boasts excellent performance, millisecond startup speed, and extremely low memory overhead.
Chalk is open-sourced under the GPL v3 license, featuring a flexible architecture and simple deployment. A typical deployment involves a global symlink within a Docker container that silently intercepts and wraps underlying build commands (like docker build), forcing the injection of a metadata-rich “chalk.” This chalk is a UTF-8 encoded JSON object embedded within the compiled artifact, and its opening section must contain the magic value: “MAGIC” : “dadfedabbadabbed” for subsequent retrieval and authenticity verification.
When a container image or binary carrying this “magic chalk” runs in a production environment, the chalk extract command can retrieve the hidden JSON metadata. Combined with the runtime environment, it generates an execution report. The report includes environment variables at build time, the CI/CD triggerer’s identity, and parses CODEOWNERS/AUTHORS files to precisely link the code to its responsible developer. Based on this data, the system constructs a connectivity graph, allowing developers to clearly visualize the infrastructure structure.
2. The Ocular Project: Blackstone DNA and Out-of-Band Scanning Orchestration
The goal of Ocular is to solve the orchestration challenge of gracefully executing heavyweight security scans.
As mentioned earlier, Ocular’s underlying framework code originates from the internal, battle-tested assets of the world’s largest private equity firm, Blackstone. Facing its own complex and rapidly iterating fintech environment, Blackstone deeply experienced a pain point: forcing various slow, high-false-positive SAST and SCA tools into developers’ CI/CD pipelines not only blocks code merge velocity but also frequently breaks pipelines due to false positives, generating strong resistance from development teams towards security.
Scanning Architecture Disruption: To fundamentally resolve this conflict, Ocular is designed as a fully Kubernetes-native, out-of-band security scanning orchestration system. Its core logic completely decouples the scanning action from the main CI/CD pipeline, allowing security checks to run asynchronously and silently on an independent execution platform. This entirely eliminates the intrusiveness of security into the development process.
Four-Layer Decoupled Containerized Module Design: Written primarily in Go (accounting for up to 90.3% of the codebase), Ocular leverages Kubernetes Custom Resource Definitions (CRDs) to configure and run various scanning tools, demonstrating high enterprise-grade extensibility. It perfectly decouples complex full-link security scanning tasks into four independently developable, configurable, and extensible containerized module interfaces.
- Crawler (Discovery Layer): Acting as the system’s sensory antenna, it is responsible for discovering and enumerating the target asset pool that needs to be scanned based on predefined rules. For example, it can automatically traverse all repository branches under a specific GitHub organization or perform deep traversal of update entries in enterprise-level container image registries.
- Downloader (Acquisition Layer): Based on the intelligence provided by the Crawler, it uses efficient methods (such as executing optimized git clone commands or performing concurrent docker pull operations) to securely pull the target assets into an isolated temporary scanning sandbox environment.
- Scanner (Execution Layer): The analytical heart of the system. Ocular itself is not bound to any specific security scanning engine. Instead, it provides a unified B.Y.O.S (Bring Your Own Scanner) mounting interface. Security engineers can package any static analysis tool as a container image and mount it here, flexibly injecting custom command-line arguments and runtime environment variables via API. Whether directing it to analyze GenAI code generation patterns or to trace high-risk, high-entropy functions, the Scanner module executes these tasks faithfully and in isolation.
- Uploader (Routing Layer): After the scan is complete and the sandbox is cleaned, this module is responsible for standardizing, parsing, and cleaning the fragmented results (such as various XML/JSON reports) produced by different security engines. It then accurately routes them to the final target destination based on business needs. The destination can be configured as an AWS S3 bucket, a backend graph database, or a trigger for real-time webhook security alert systems.
Through the combined strength of these two major open-source projects, Crash Override has effectively built a technological moat around the cloud-native security foundation, complementing its commercial platform from the ground up.
Market Ecosystem and Competitive Landscape
To define the position of the Crash Override ERM platform within the current DevOps and security ecosystem, amidst the plethora of emerging technological concepts in the cybersecurity market, its capability model must be systematically compared and analyzed against mainstream security products (such as SCA, CNAPP) and traditional system observability platforms.
1. Disruptive Advantage Over Traditional Software Composition Analysis (SCA) and Static Code Testing Tools
Driven by the “shift left” movement, tools represented by Snyk, Aqua Security, and Trivy dominate the application security testing and container dependency analysis market. These products, especially Snyk, have gained favor with global development teams due to their excellent developer experience, very low entry barrier, and ability to scan dependencies directly within IDEs and command-line interfaces.
However, there is a fundamental difference between traditional SCA tools and the Crash Override platform. SCA essentially provides a static SBOM, and its core value is limited to answering one static question: Does the current static code or container image layer contain any disclosed, known vulnerabilities?
But in the complex and rapidly changing landscape of modern engineering practice, merely knowing that a vulnerability exists is far from sufficient and only increases the anxiety of security teams. Crash Override’s Deep Build Inspection technology elevates the perspective. It answers a series of dynamic, complex questions with timeline continuity and attribution: Through which dependency path was that third-party component with a severe CVE vulnerability introduced into the build pipeline? Who (which specific developer) mistakenly triggered the automated pipeline that included that vulnerable component at 4 PM yesterday? During the introduction process, was an AI-assisted tool used to generate glue code with logical hallucinations to call that component?
SCA tools, like Snyk, focus on the vulnerability characteristics of static components, while the Crash Override ERM platform masters the global traceability trail of the dynamic engineering lifecycle. While their functions are complementary, ERM demonstrates a disruptive, dimension-reducing advantage over traditional static analysis in terms of the problem-solving dimension.
2. Complementarity and Context Bridging with CNAPP
In recent years, with the explosion of cloud-native architectures, CNAPP platforms exemplified by Wiz and Orca Security have, through disruptive cloud API integration and snapshot scanning technology, completely dismantled the traditional host-agent-based security software business model and redefined the CSPM market. Wiz, in particular, excels at building complex graph databases to deeply reveal attack paths hidden within cloud infrastructure, such as precisely identifying an exposed public bucket that happens to be associated with an active role possessing excessive IAM privilege escalation permissions.
Although CNAPP platforms demonstrate strong capabilities in runtime infrastructure risk discovery and graph correlation within cloud environments, they inevitably encounter the industry-wide challenge of context discontinuity when attempting to extend their reach leftwards back into the development phase.
In a business scenario, when the Wiz console alerts that a running production container has a critical network port misconfiguration, the cloud security engineer still faces a dilemma. This is because the CNAPP platform lacks the continuous historical and physical trajectory—from the vast source code repository branch, through layers of compilation, packaging, testing, and eventual evolution and deployment to the cloud. Security engineers cannot quickly trace back to the corresponding Git commit hash based solely on a running cloud image ID.
Crash Override precisely bridges this critical context gap. It provides a code-to-cloud visibility with absolute temporal continuity. The moment a CNAPP triggers a runtime alert, Crash Override can retrieve the telemetry data captured by its Deep Build Inspection and fill in all the missing critical engineering context within a second, precisely pointing out to the CISO: the anomalous cloud workload that triggered this serious alert was packaged and deployed by a specific business team, on a specific pipeline, at a specific time.
By providing this ownership mapping network, Crash Override effectively multiplies the return on investment for expensive CNAPP platforms like Wiz. It successfully transforms isolated risk discovery alerts into actionable, efficient traceability and precise remediation actions.
3. Distinction from the Core Mission of System Observability Platforms
Within the DevOps community, organizations often harbor the misconception that existing top-tier system observability platforms (such as Datadog, Dynatrace, etc.) can substitute for specialized security engineering visibility tools. These platforms excel at instrumenting application code extensively, aggregating massive volumes of application logs, performance metrics, and distributed tracing data.
However, this deluge of performance telemetry data still fails to answer the most critical and damaging question in engineering management: What specific operation actually caused this widespread outage?
Crash Override aims to establish strict engineering accountability within the chaotic development ecosystem. Through its digital tracer and Chalk Mark mechanism, it cryptographically verifiably records every addition, deletion, modification, and query of environment variables within the build sandbox environment. It ensures that even if the security team faces an incident where the source code appears unchanged during post-mortem analysis, they can consult the ERM platform’s immutable records to capture the stealthy environment variable mutation or build dependency tampering that caused the production incident.
Customer Cases and Capital Support
The Engineering Relationship Management (ERM) concept and technological capabilities advocated by Crash Override have been tested in the global business environment, earning recognition and high praise from enterprise executives.
1. Toyota and AWS Case Studies
Crash Override’s product logic has achieved breakthroughs in key areas such as traditional high-end manufacturing with extremely high software supply chain security requirements (e.g., automotive manufacturing) and internet cloud services with demanding high-concurrency continuous delivery requirements. Gabriel Lawrence, Vice President of Information Security at Toyota Motor North America, a global automotive manufacturing giant, has publicly endorsed Crash Override’s technological approach on behalf of large traditional enterprises. Simultaneously, Wael Ghandour, a senior security engineer from Amazon, has also expressed agreement from the frontline实战 perspective of a major internet company.
2. RSAC 2026 Innovation Sandbox
After gaining customer recognition, Crash Override reached a highlight moment in terms of industry influence—it was named a finalist in the top 10 of the RSAC 2026 Innovation Sandbox global competition, known as the “global cybersecurity trendsetter and innovation incubator.”
At the RSAC 2026 conference held in San Francisco on March 23, 2026, the cybersecurity industry’s discussions broadly focused on macro topics such as machine identity, agent governance, and Shadow AI risk control. On this stage of technological competition, Crash Override competed fiercely with companies like Charm Security (focusing on anti-fraud AI defense), Clearly AI (specializing in AI-assisted automated code review), and Fig Security (focusing on security operations resilience remediation).
The judging panel, composed of Wall Street capital leaders including David Chen, Head of Global Technology Investment Banking at Morgan Stanley, and Larry Feinsmith, Global Head of Technology Strategy and Innovation at JPMorgan Chase, paid close attention to Crash Override. The logic behind the judges’ and capital market’s favor was clear: while many startups remained at the API level for宏观 risk monitoring, Crash Override demonstrated a unique capability—using Deep Build Inspection technology to deploy probes deep within CI/CD pipelines, capture execution details, fundamentally prevent malicious tampering, and proactively address certificate management and build provenance compliance before problematic code could materially impact the production environment.
As a reward for being a top ten finalist, Crash Override not only gained a platform to showcase its ERM vision in front of tens of thousands of global security experts but also directly secured entry to the competition’s $5 million SAFE strategic investment program, providing momentum for its subsequent global expansion to capture large enterprise customers.
Summary and Strategic Outlook
Crash Override represents a fundamental reconfiguration of next-generation DevSecOps principles. In response to the three major structural crises—shadow engineering, AI infiltration, and the loss of control over the software supply chain—Crash Override has pioneered the Engineering Relationship Management (ERM) platform, fundamentally transforming how enterprises manage engineering risk.
1. Core Technology and Value Proposition
Engineering Relationship Management (ERM): Drawing on the successful experience of CRM, it aims to weave dispersed code, tools, dependencies, and personnel behaviors into a cryptographically verifiable dynamic relationship graph, thereby achieving absolute visibility and engineering control over the SDLC.
Deep Build Inspection: Different from traditional runtime monitoring, this technology captures and records end-to-end details from code commit to cloud deployment by injecting lightweight probes into CI/CD pipelines, enabling zero-friction, instantaneous traceability.
AI Governance Closed Loop: Through the “Discover, Deepen, Safeguard” three-step process, it effectively addresses Shadow AI risks, deeply capturing unauthorized AI coding assistant usage while providing low-friction guardrails for the secure implementation of compliant AI tools.
Open Source Ecosystem Foundation: Through Chalk (a minimalist global marking and tracing framework) and Ocular (a Kubernetes-native out-of-band scanning orchestration system), Crash Override has not only built a technological moat but is also actively leading the discourse in cloud-native security standards.
2. Market Positioning and Competitive Advantages
Crash Override has successfully bridged the context gap between CNAPP (e.g., Wiz) and traditional SCA (e.g., Snyk) tools, transforming isolated runtime alerts into actionable engineering traceability actions. It shifts the focus of “shift left” from passive vulnerability scanning to proactive engineering accountability.
Leveraging the profound expertise of application security pioneers John Viega and Mark Curphey, the technology infusion from Blackstone, and a substantial $28 million seed funding round, Crash Override has gained recognition from benchmark customers like Toyota and AWS, and has been strongly shortlisted as a top ten finalist for the RSAC 2026 Innovation Sandbox. It is regarded by the capital market as a key infrastructure-level provider capable of solving the loss of control challenges in modern software delivery and AI governance.
References
[1] Crash Override | Find AI, Accelerate and Secure It, accessed March 10, 2026, https://crashoverride.com/
[2] Crash Override Turns to ERM to Combat Visibility Challenges – Security, accessed March 10, 2026, https://www.darkreading.com/application-security/crash-override-erm-combat-visibility-challenges
[3] Announcing Chalk™ Alpha – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog/announcing-the-alpha-release-of-the-chalk-open-source-project
[4] An Introduction to Engineering Relationship Management- ERM – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog/introducing-engineering-relationship-management
[5] Builds Don’t Lie. Unless You’re Not Watching Them. – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog/builds-dont-lie-unless-youre-not-watching-them
[6] Newsroom – AI Discovery, Adoption & Security – Crash Override, accessed March 10, 2026, https://crashoverride.com/newsroom
[7] The Hackers Mural – Amsterdam April 2023 – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog/the-hackers-mural-amsterdam-april-2023
[8] AI Coding Adoption & Security Insights – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog
[9] Are we trusting AI too much? – CyberArk, accessed March 10, 2026, https://www.cyberark.com/resources/agentic-ai-security/are-we-trusting-ai-too-much
[10] The Dark Twin of Autonomy: Shadow AI in Agentic Ecosystems | by Sreelatha S – Medium, accessed March 10, 2026, https://medium.com/@sreelathas/the-dark-twin-of-autonomy-shadow-ai-in-agentic-ecosystems-7ae44e658b40
[11] AI Governance 101: The New Compliance Requirement Companies Overlook – Kinetic, accessed March 10, 2026, https://kinetictg.com/ai-governance-101-the-new-compliance-requirement-companies-overlook/
[12] Slopsquatting: When AI Agents Hallucinate Malicious Packages | Trend Micro (US), accessed March 10, 2026, https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/slopsquatting-when-ai-agents-hallucinate-malicious-packages
[13] Find AI, Accelerate Adoption, & Secure It | Crash Override, accessed March 10, 2026, https://crashoverride.com/platform
[14] Crash Override Raises $28M in Seed Funding – FinSMEs, accessed March 10, 2026, https://www.finsmes.com/2025/07/crash-override-raises-28m-in-seed-funding.html
[15] FOSDEM 2024 – John Viega, accessed March 10, 2026, https://archive.fosdem.org/2024/schedule/speaker/LYSFY9/
[16] John Viega – CEO and Co-Founder at Crash Override | The Org, accessed March 10, 2026, https://theorg.com/org/crash-override/org-chart/john-viega
[17] Mark Curphey – OWASP Foundation, accessed March 10, 2026, https://owasp.org/www-board-candidates/2022/mark_curphey_2022
[18] Building Security Tools is the Wrong Approach – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog/building-security-tools-is-the-wrong-approach
[19] John Viega on Building Impact Beyond Security – Aspiron Search, accessed March 10, 2026, https://aspironsearch.com/behind-the-scenes-with-john-viega-ceo-and-co-founder-of-crashoverride-building-impact-beyond-security/
[20] Crash Override Chronicles: Background | by Scott J Roberts – Medium, accessed March 10, 2026, https://sroberts.medium.com/crash-override-chronicles-background-6b7d95d04377
[21] Crash Override Raises $28 Million in Seed Round | The SaaS News, accessed March 10, 2026, https://www.thesaasnews.com/news/crash-override-raises-28-million-in-seed-round
[22] Why We Built Ocular | Out-of-Band Security Scanning at Scale – Crash Override, accessed March 10, 2026, https://crashoverride.com/blog/why-we-built-ocular
[23] Crash Override Raises $28 Million Seed Round to Launch First Engineering Relationship Management Platform – Business Wire, accessed March 10, 2026, https://www.businesswire.com/news/home/20250715794118/en/Crash-Override-Raises-%2428-Million-Seed-Round-to-Launch-First-Engineering-Relationship-Management-Platform
[24] How to Design an ERM-Friendly Risk Data Architecture – GARP.org, accessed March 10, 2026, https://www.garp.org/risk-intelligence/culture-governance/how-to-design-an-erm-friendly-risk-data-architecture
[25] FAQ | Crash Override | AI Discovery, Adoption & Security, accessed March 10, 2026, https://crashoverride.com/faqs
[26] crashappsec/chalk: Chalk allows you to follow code from development, through builds and into production. – GitHub, accessed March 10, 2026, https://github.com/crashappsec/chalk
[27] Chalk™ User Guide | Chalk Community Site – The Chalk Project, accessed March 10, 2026, https://chalkproject.io/docs/getting-started/user-guide/
[28] About Ocular | Open-Source Security Scanning Platform, accessed March 10, 2026, https://ocularproject.io/about/
[29] Snyk vs Wiz Comparison | Wiz Best Alternatives, accessed March 10, 2026, https://snyk.io/comparison/snyk-vs-wiz/
[30] Snyk vs Wiz vs Cycode: Pros & Cons, and How to Choose the Best Solution, accessed March 10, 2026, https://cycode.com/blog/snyk-vs-wiz-3-key-differences/
[31] Wiz vs. Snyk: Why It’s Not Always Either/Or, accessed March 10, 2026, https://www.wiz.io/academy/application-security/wiz-vs-snyk
[32] Compare Snyk vs. Wiz – G2, accessed March 10, 2026, https://www.g2.com/compare/snyk-vs-wiz-wiz
[33] Snyk vs Wiz Comparison in 2026 | Aikido Security, accessed March 10, 2026, https://www.aikido.dev/blog/snyk-vs-wiz
[34] Finalists Announced for RSAC Innovation Sandbox Contest 2026, accessed March 10, 2026, https://www.rsaconference.com/library/press-release/finalists-announced-for-rsac-innovation-sandbox-contest-2026
[35] Innovation Sandbox | RSAC Conference, accessed March 10, 2026, https://www.rsaconference.com/usa/programs/innovation-sandbox
[36] 07:57 ETFinalists Announced for RSAC Innovation Sandbox Contest 2026 – Longbridge, accessed March 10, 2026, https://longbridge.com/en/news/275461577