
Vulnerability Description
On August 24, QEMU released a security patch to fix a VM escape vulnerability (CVE-2020-14364) which is the result of an out-of-bounds read/write access issue in the USB emulator in QEMU. This vulnerability resides in ./hw/usb/core.c. When the program handles USB packets from a guest, this vulnerability is deemed to exist if USBDevice ‘setup_len’ exceeds its ‘data_buf[4096]’ in the do_token_in and do_token_out routines. An attacker could exploit this vulnerability to cause out-of-bounds read of the 0xffffffff contents following the heap, forcibly terminating the virtual process and realizing VM escape.
An attacker with access to a VM operating system in the cloud environment could exploit this vulnerability to gain host privileges to target all tenant hosts within the resource pool that holds the VM. Worse still, the attacker, with his or her gained intranet privileges, could attack systems within the management domain.
QEMU (short for quick emulator) is an analog processor written by Fabrice Bellard and others to distribute GPL-licensed source code. It is an underlying commercial component used by numerous cloud vendors. This vulnerability affects most cloud vendors that use OpenStack. Users are advised to take precautionary measures as soon as possible to fix this vulnerability.
Reference link:
Scope of Impact
Affected versions
- Qemu 1.x – 5.1.0
Note: The prerequisite for triggering this vulnerability is that a VM needs to connect to at least one USB device.
Check for the Vulnerability
- Version Check
Users can use the following commands to check the current QEMU version:
kvm-version |
qemu-img-V |
If it is one of the affected versions, the application is vulnerable.
Mitigation
- Remediation Recommendations
Affected cloud vendors are advised to fix this vulnerability by downloading and applying patches from the following addresses:
Red Hat:
Debain:
- Workaround
The following takes QEMU 1.5.3 as an example to describe how to fix this vulnerability for the time being.
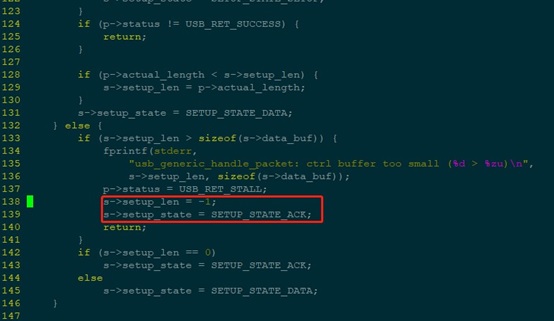
1. Modify the do_token_setup function in qemu-1.5.3/hw/usb/core.c by adding two lines in the following red frame:
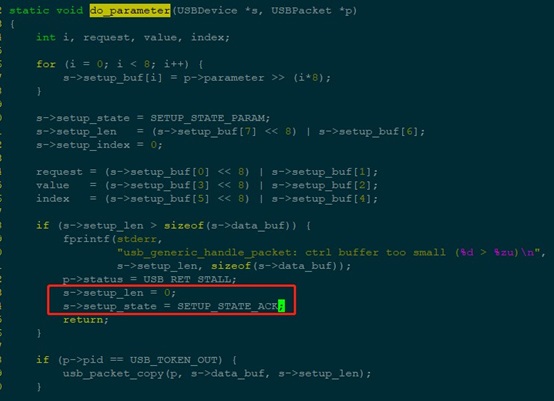
Modify the do_parameter function in qemu-1.5.3/hw/usb/core.c by adding two lines in the following red frame:
2. Recompile the QEMU software package.
Here, src.rpm is used as an example to describe how to recompile the QEMU software package:
(1) Run the “rpm-ivh“ command to decompress src.rpm.
(2) Modify code.
a. Edit the following file (or patch file) by reference to the preceding modifications:
~/rpmbuild/SOURCES/qemu-1.5.3/hw/usb/core.c
b. Edit the spec file by changing the version number and modifying the changlog description.
~/rpmbuild/SPEC/qemu-kvm
c. Run the “rpmbuild -ba ~/rpmbuild/SPEC/qemu-kvm” command to generate the RPM package.
3. Perform the upgrade.
After the update package is obtained, users need to apply it for the current QEMU software on the host and do a hard restart (if service disruption is not allowed, you should ask R&D personnel for the hotfix solution).
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.
