Regional APT Threat Situation
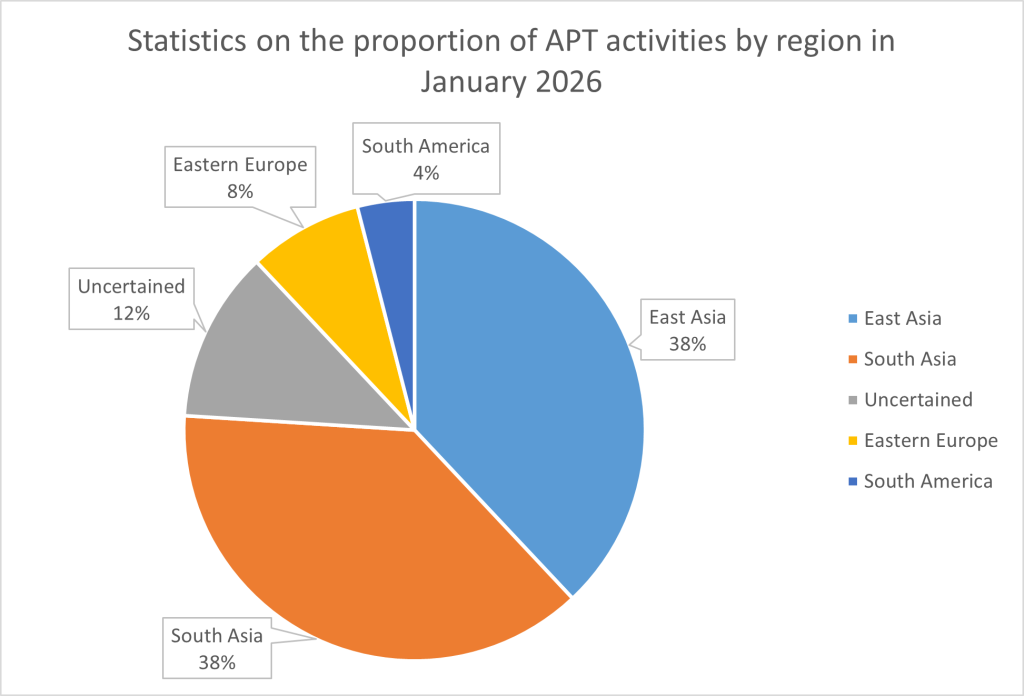
In January 2026, the global threat hunting system of Fuying Lab detected a total of 26 APT attack activities. These activities were primarily concentrated in regions including East Asia, South Asia, and Eastern Europe, as shown in the figure below.
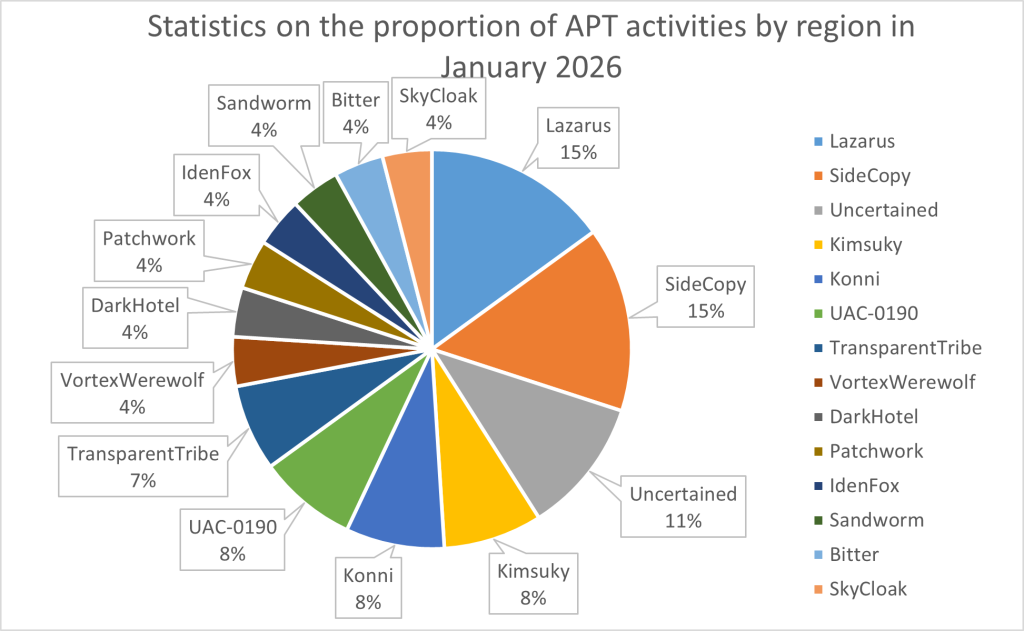
Regarding the activity levels of different groups, the most active APT groups in this month were Lazarus from East Asia, while other relatively active groups included SideCopy and TransparentTribe from South Asia, and Kimsuky from East Asia.
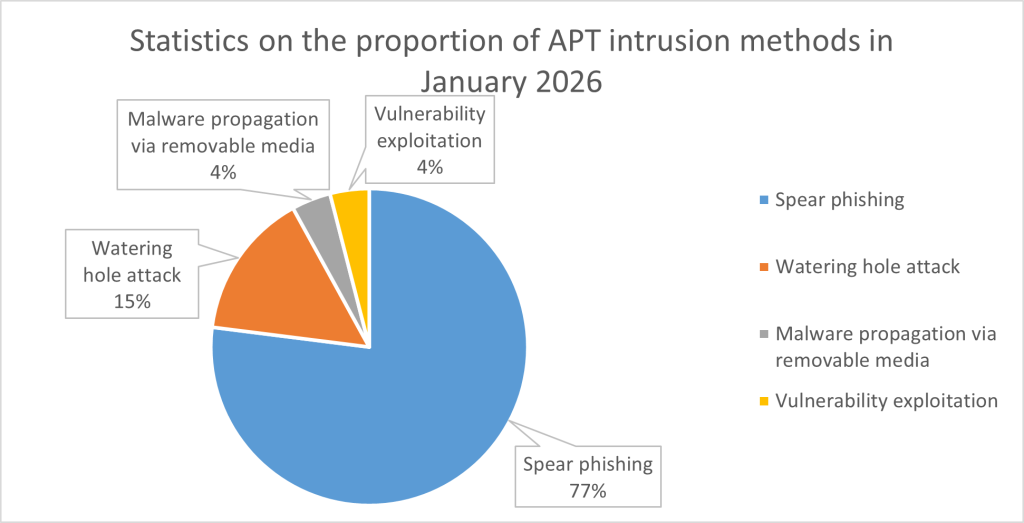
The most prevalent intrusion method in this month’s incidents was spear-phishing email attacks, accounting for 77% of all attack events. A small number of threat actors also utilized watering hole attacks (15%) for infiltration and vulnerability exploitations (4%). Additionally, 4% of this month’s incidents involved malware propagation via removable media.
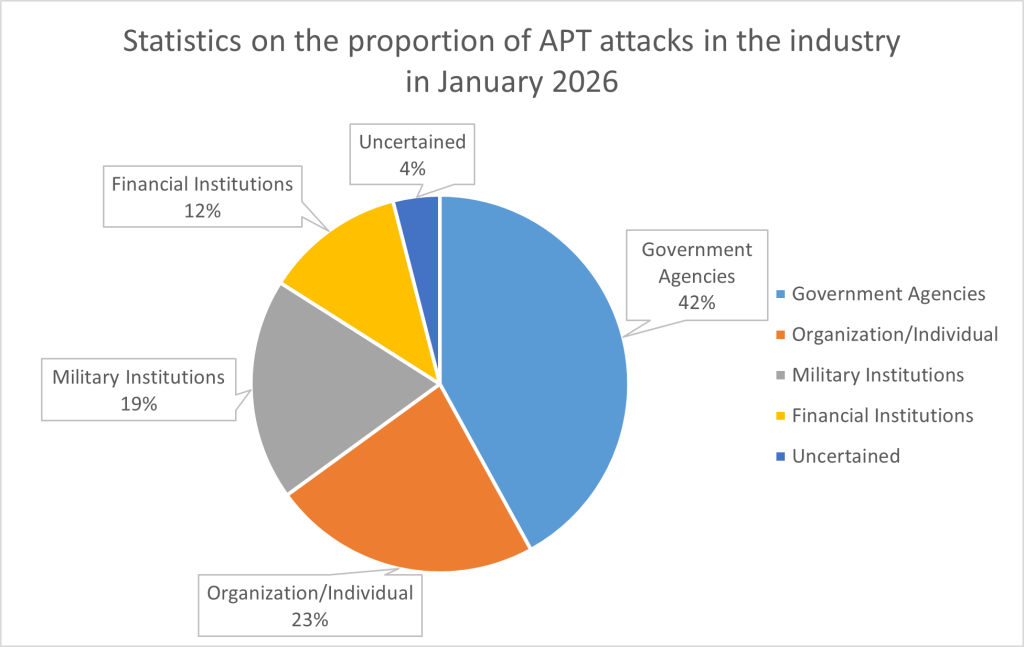
In January 2026, the primary target industries for APT groups were government agencies, accounting for 42%, followed by organizations or individuals accounting for 23%. Other attack targets included military institutions and financial institutions.
East Asia
This month, APT activities in East Asia were primarily initiated by known APT groups, with victims mainly targeting South Korean entities, including South Korean military institutions, financial sectors, organizations, or individuals.
In terms of attack tactics, most APT activities in East Asia this month utilized spear-phishing emails, while some groups employed USB drop tactics (using USB media to propagate attack payloads)……
Subscribe NSFOCUS Threat Intelligence for full details of APT incident insights.
South Asia
This month, APT activities in South Asia were primarily initiated by known APT groups, targeting government agencies in Pakistan, military and government institutions in India, and government agencies in Bangladesh.
In terms of attack tactics, spear-phishing emails remained the dominant method in South Asia this month. A typical decoy involved a phishing email targeting the Directorate of Finance and Accounts of the Indian Ministry of Defense. The decoy was an official document purporting to be an administrative notice for updating and revising the qualification rankings of officials in the Indian defense accounting system.
Subscribe NSFOCUS Threat Intelligence for full details of APT incident insights.
Eastern Europe
This month, APT activities in Eastern Europe were primarily initiated by known APT groups, targeting government agencies in Poland and military institutions in Ukraine.
In terms of attack tactics, APT activities in Eastern Europe this month primarily utilized watering hole attacks and spear-phishing.
This month, Eastern European threat actors conducted targeted attacks against the Ukrainian military by posing as charitable foundations, leveraging phishing websites, or employing watering hole attacks. Notably, the group was observed using a PIF loader written in Rust, further enhancing its stability and resilience……
Subscribe NSFOCUS Threat Intelligence for full details of APT incident insights.
Global Key APT Event
APT28 launched Operation Neusploit, exploiting the Office zero-day vulnerability CVE-2026-21509
In January 2026, security researchers disclosed a cyberattack operation named “Operation Neusploit.” In this operation, the Russian APT group APT28 exploited the Microsoft Office zero-day vulnerability CVE-2026-21509 to create malicious documents, targeting entities in multiple Eastern European countries.
The CVE-2026-21509 vulnerability is a remote code execution (RCE) vulnerability that bypasses the internal OLE object filtering mechanism in Office. The CVSS score for this vulnerability is 7.8. Microsoft publicly disclosed CVE-2026-21509 and released a patch on January 26, 2026. CISA added this vulnerability to its list of actively exploited vulnerabilities at the same time, confirming it as a zero-day exploit already used in the wild. APT28 applied CVE-2026-21509 in it cyberattack campaign on January 29, 2026, representing a typical 1-day vulnerability exploitation scenario. The attack flow of this operation by APT28 is shown in the following figure……
| Group Name | APT28, Sofacy, Fancy Bear |
| Appear Time | 2004 |
| Attack Targets | Afghanistan, Armenia, Australia …… |
Subscribe NSFOCUS Threat Intelligence for full details of APT incident insights.
About CVE-2026-21509
CVE-2026-21509 is a simple, easy-to-implement, and highly effective Remote Code Execution (RCE) vulnerability in Microsoft Office products. The high adoption rate of Microsoft Office further amplifies the threat posed by this vulnerability. Shortly after vulnerability was disclosed, NSFOCUS FUYING Lab captured a large number of in-the-wild exploitation samples. We speculate that this vulnerability will be exploited by multiple APT groups, and it deserves close attention from all users of Office products. The principle of CVE-2026-21509 is very simple and easy to understand it exploits……
Subscribe NSFOCUS Threat Intelligence for full details of APT incident insights.