1 Introduction
According to the Statistical Report on China’s Internet Development[â‘ ] released by China Internet Network Information Center (CNNIC) in February 2019, China’s online population had reached 829 million, with an Internet penetration rate of 59.6%, by the end of 2018. The Internet has shown its presence in every segment of national economy, with a direct influence on national development and people’s work and livelihood. While the Internet technology is gaining momentum for rapid growth, cybersecurity incidents, powered by more and more novel attack methods, are becoming increasingly varied, endangering normal operations of governments and enterprises and affecting people’s daily lives.
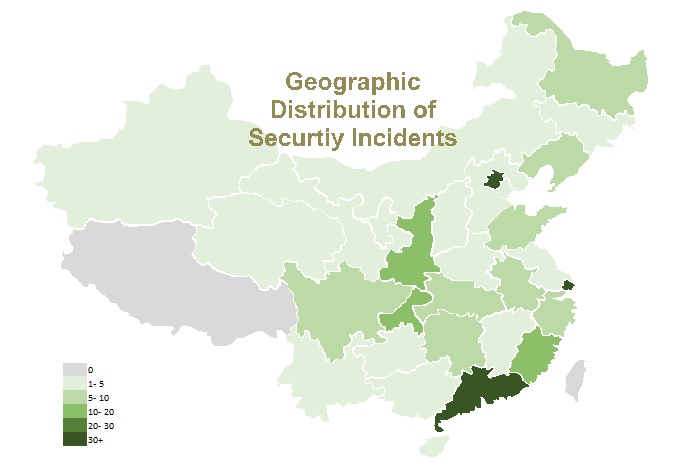
In 2018, NSFOCUS Incident Response Team (NIRT) handled a total of 338 emergency incidents across the country for customers from government, carrier, financial, and unclassified sectors in 30 provinces. The following figure shows the geographic distribution of security incidents.
Geographic distribution of security incidents
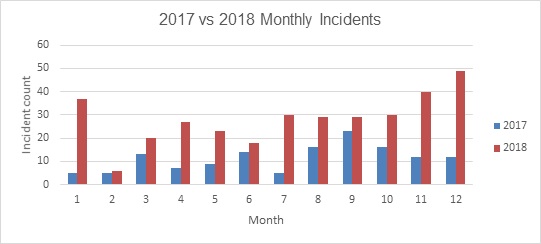
According to statistics, there were more security incidents at the beginning and end of 2018 than in other periods of the year, and the numbers were much greater than those in the same periods of 2017.
2017 vs 2018 monthly incidents
Upon an in-depth analysis of security incidents handled in 2018, NIRT produced this report as a sum-up of what had been observed in the past year. We wish more people would raise their awareness and pay more attention to the current cybersecurity landscape. Meanwhile, we are looking forward to cooperating with other security vendors and contributing to a more secure ecosystem.
-
Applicability
This report is intended for customers from government, carrier, financial, and unclassified sectors.
-
Limitations
This report is based on data collected in emergency response services of NSFOCUS and so inevitably has some limitations.
-
Special Statement
All data presented in this report is sourced from NSFOCUS’s own products and partners’ products and has been masked to avoid leakage. Besides, the report does not contain any information that may identify customers.
2 Cybersecurity Landscape
With the evolution of the cybersecurity landscape, more and more cyber criminals have turned from showing off their skills to garnering economic benefits when launching attacks. Perpetrators do not always resort to new techniques, but, more often than not, make minor changes to existing tools and ploys to break enterprises’ defenses. Compared with 2017, the year 2018 was relatively uneventful, with the shadow of the critical vulnerability of MS17-010 fading away. However, under the seemingly peaceful surface lies an underground industry chain that is growing without people’s knowledge.
Holistic View
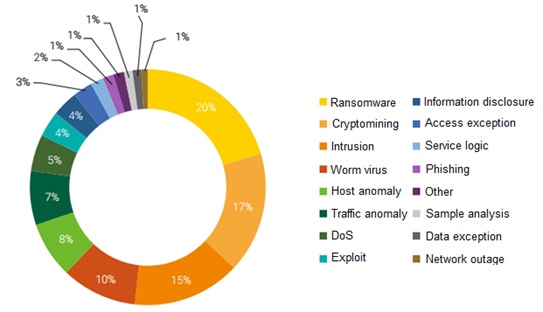
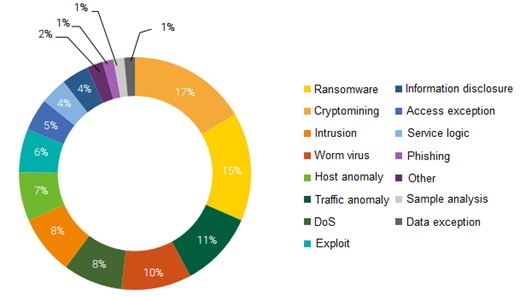
Of all security incidents dealt with by NSFOCUS in 2018, ransomware, cryptomining, and intrusion accounted for large proportions, 20%, 17%, and 15% respectively. Hack targets and methods keep changing, but the pursuit of financial gains remains the same. Cryptocurrencies are hard to trace and therefore considered the best medium of exchange through which hackers can obtain huge illegal gains via extortion and cryptomining. Typical examples of such attacks are crypto ransom, cryptocurrency theft, cryptomining, and fraud. The following figure shows the proportion of each incident type.
Distribution of incident types
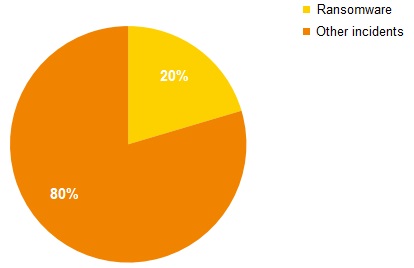
Compared with last year, the number of ransomware types and that of ransomware incidents both saw a sharp rise in 2018. Specifically, we handled 25 ransomware incidents in 2017 and this number jumped to 69 in 2018.
2017 vs 2018 ransomware incidents
In 2017, there were only a few ransomware types. In 2018, we spotted scores of them. Besides, ransomware has iterated by leaps and bounds and is gradually growing into families. For example, GandCrab and Cerber have more than five generations and GlobeImposter has the third generation coming into use.
2017 vs 2018 active ransomware types
| Year | Ransomware Types |
| 2017 | WannaCry, Petya, Crysis, RushQL, HDDCryptor, CRBR |
| 2018 | WannaCry, Petya, Crysis, RushQL, HDDCryptor, GlobeImposter, WannaMine, Rapid, Lucky, GandCrab, .Wallet, Crysis, PrincessLocker, Cerber, … |
Cryptomining incidents increased from last year’s 14 to 56. In 2018, cryptominers mostly took the form of worms.
2017 vs 2018 cryptomining incidents
Industry-specific View
Governments’ servers and websites are always the favorite target of hackers and often subject to web attacks.
Carriers have a close connection with network application services and terminal services. This makes them easy targets of hackers.
The financial sector is characterized by complicated business and high-value digital assets, and so is an ideal target for hackers outside of China.
In the unclassified sector, small and medium-sized businesses (SMBs), including Internet enterprises, are most severely attacked. This is because SMBs do not have much money to invest in cybersecurity, but on the other hand rely heavily on Internet information systems for their product sales and maintenance. Moreover, they fail to promptly fix vulnerabilities made known to the public, thus inviting a lot of hacker attacks.
2.2 Ransomware Remaining an Eye-Catcher Among Security Incidents and Starting Operating as Families
Ransomware attacks are nothing new, but do you know that ransomware and cryptocurrencies can make a perfect couple? In 2017, the ransomware WannaCry started a “carnage” that swept across the globe, opening the eyes of attackers to this unscrupulous “money-grabbing” way. From then on, incidents of ransomware have emerged in endless succession.
Of all emergency incidents we handled in 2018, ransomware attacks accounted for 20%, second to none. Obviously, ransomware still calls for special attention in cyber defenses. While handling and analyzing ransomware incidents, we found that ransomware displayed new characteristics in attack targets, propagation methods, technical skills required, and ransom payment methods, and some new families/variants emerged.
- Distribution of incident types
2.2.2 More Ransomware Families, Faster Updates
From WannaCry, Petya, and Satan that raged across the year of 2017 to Crysis, GandCrab, GlobeImposter, and PrinceLocker that were active in 2018, more ransomware families are seen perpetrating malicious activities. At the same time, individual viruses are updated at a faster rate. For example, Satan made its debut in January 2017, and had the second-generation variant in December of the same year. Subsequently in May, June, and November 2018, three more variants appeared. Moreover, Satan samples have more propagation methods and their users tend to demand more ransom. GandCrab V5, since its first appearance in September 2018, has evolved into multiple variants in a very short time, including 5.0, 5.0.2, 5.0.3, 5.0.4, and 5.0.5.
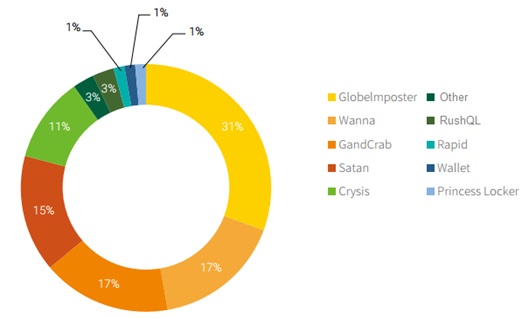
The following figure shows the proportion of total emergency incidents caused by each ransomware type. It can be clearly seen that GlobeImposter, Wanna series, GandCrab, Satan, and Crysis together caused 90% of ransomware incidents and GlobeImposter alone contributed 31%.
- Ransomware types
2.2.3 Windows Servers Calling for Particular Attention and Cross-Platform Ransomware Coming as a New Threat
Unlike 2017 in which remote control families, such as XOR and Billgates, were rampant, the year 2018 saw ransomware leading malware families. Ransomware mostly takes Windows servers as targets. On the one hand, servers run many complicated services, which contain various vulnerabilities that are almost impossible to fix in time. On the other hand, many services are using weak passwords. All these open a window to attackers.
- Ransomware propagation platforms
At the end of 2018, a brand new type of ransomware appeared, which could propagate on both Windows and Linux platforms. Through analysis, we found that this virus was a variant of Satan (with .lucky as the extension of encrypted files). Predictably, cross-platform propagation of ransomware will become a new trend.
2.2.4 RDP Weak Password Cracking Becoming a Major Attack Method
Traditionally, ransomware is spread by means of phishing, trojan planting, and program bundling. In 2018, RDP password cracking that new comers, such as GlobeImposter and GandCrab, adopt to propagate themselves, became a new norm. The following figure shows vulnerability types exploited by ransomware captured by NSFOCUS in 2018. Of all these types, weak password cracking contributed the largest proportion (65%) of emergency ransom incidents, occupying a dominant position in all types of exploitation.
- Vulnerability types exploited by ransomware
2.2.5 Viruses Becoming Easier to Create and Propagating like Worms
2018 saw the rampancy of ransomware, which became a big star on the stage. As the saying goes, rewards allure men to brave danger. Ransomware can generate good returns, which allures numerous virus developers at various technical levels into the game. As a result, viruses written by them are of varying quality. For example, WeChat Ransom that was first spotted in December 2018 performed XOR encryption on files by using only fixed keys. A simple script could decrypt the encrypted files. As WeChat Payment adopts a real-name registration mechanism that makes it easy to track attackers, the virus creator was arrested on December 5.
There is an obvious trend that ransomware begins to operate like worms. Most ransomware variants try to spread themselves by means of RDP brute-force attacks or various exploits. In 2017, WannaMine propagated by exploiting the only vulnerability, MS17-010. In contrast, Satan, an active variant in 2018, exploited about 10 vulnerabilities for propagation, including the JBoass deserialization vulnerability, WebLogic WLS component vulnerability (CVE-2017-10271), Windows SMB remote code execution vulnerability (MS17-010), and Apache Struts 2 remote code execution vulnerability (S2-045). Besides, unlike the previous version, the new version of Satan can propagate across platforms of Windows and Linux. Although it is still unstable, we predict that more robust variants will appear in 2019.
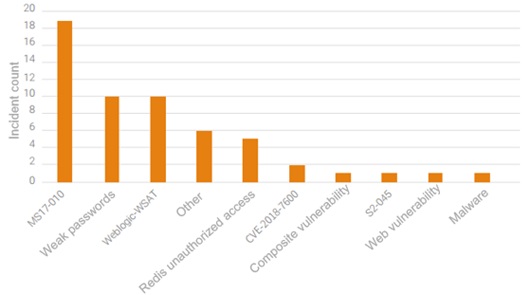
2.3 Cryptominers Propagating via Various Vulnerabilities
In 2018, NIRT handled 56 cryptomining events, most of which (81%) were for the mining of Monero. An analysis of these events reveals that hackers used a variety of methods. Specifically, 19 events exploited EternalBlue, 10 exploited the WebLogic component vulnerability, 10 exploited weak passwords, and 5 were conducted by compromising servers via Redis. In terms of viruses and tools used, 18 events used WannaMine, 5 used cpuminer, 4 used Redis Miner, 4 used DDG, and 8 used PowerGhost. Currently, WannaMine and PowerGhost are the two most popular viruses for cryptomining.
- Vulnerabilities exploited for cryptomining
2.3.2 WannaMine Remaining a Popular Virus
Emergency incidents caused by WannaMine in 2018 plummeted, but still troubled some organizations, especially health care and education sectors. This virus still uses the MS17-010 vulnerability for propagation and cryptomining. Although official patches are already available, some organizations fail to install them in time because of low security awareness or deficient security mechanisms. This explains why such events still happen from time to time.
2.3.3 Monero Becoming the Top Target of Cryptominers
Monero, which boasts the highest degree of anonymity, has always been favored by anonymous users. General anonymity can be achieved by Bitcoin, but complete anonymity can only be achieved by Monero currently. Because of such feature, Monero has a close connection with money laundering. Untraceability makes Monero a convenient currency for purchase of illegal commodities on the sly. Naturally, it has survived years of fierce competition and begins to dominate the cryptocurrency market. 5% of Monero circulating on the market is produced by cryptominers.
The allurement of easy money causes a steady increase in cryptomining events. In 2018, the proportion of cryptomining events for which NSFOCUS provided emergency support reached 17%. Of all such events, 81% were associated with Monero.
2.4 Cyber Threats Showing Sector-specific Characteristics
Of all security incidents handled in 2018, most were found in financial, unclassified, government, carrier, and Internet sectors. Organizations in these sectors are generally big in size and widely distributed, and hold data that is more sensitive. Therefore, they become the favorite targets of attackers. Each sector has its distinctive scope of business, and so may be subject to different kinds of security incidents. Despite that, ransomware, cryptomining, and intrusion incidents are common for various sectors.
Ransomware attacks often affect financial, unclassified, government, carrier, and energy sectors. Cryptomining attackers often target financial, transportation, and government sectors. Intrusion incidents are a common trouble to government, financial, and Internet sectors. Host anomalies are often seen in unclassified and Internet sectors.
- Distribution of cyber threats by sector
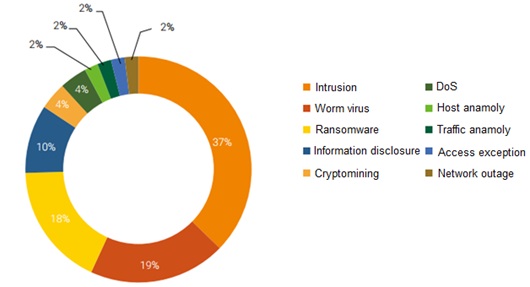
2.4.2 Government Departments’ Web Servers Frequently Attacked
The development of the Internet technology makes it an urgent need to transform the current protection of e-government networks. While conveniencing people’s lives, networks expose people to more threats. Government departments have very sensitive information on hand, making themselves an interesting target for hackers.
Of all security incidents handled by NSFOCUS in 2018, 37% were intrusions related to government departments’ networks, most of which led to web defacements. Governments’ web servers have become an attraction to hackers.
- Distribution of incident types – government departments
2.4.3 Carriers Harassed by Ransomware and Traffic Anomaly Incidents
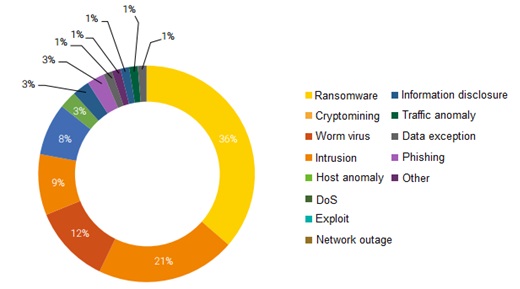
As entities responsible for development, operation, and maintenance of network facilities, carriers play a fundamental and critical role in network operations. Meanwhile, carriers have a close connection with network application services and terminal services. This makes them easy targets of hackers. Generally speaking, carrier-related security incidents declined in 2018, but ransomware incidents went against this trend to rise a bit. Besides, traffic anomalies remained a problem that concerned carriers most.
- Distribution of incident types – carriers
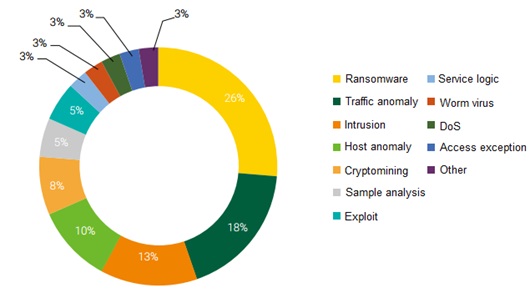
2.4.4 Financial Institutions Becoming a Major Target of Cybercrime
The financial sector is characterized by business complexity and high value of digital assets, thus becoming a major target of cybercrime. For this reason, this sector should be put on top of the list in terms of cybersecurity. In 2018, the financial sector contributed 40% of security incidents of diverse types, including cryptomining (17%) and ransomware attacks (15%).
At the end of November 2018, multiple financial customers of NSFOCUS in China were targeted by a cross-platform variant of the ransomware Satan, which exploited EternalBlue and several middleware vulnerabilities to propagate like worms on Linux and Windows. After infecting hosts, the variant will download a Monero mining program and ransomware.
On December 11, an account suspected to be related with the famous hacker group Anonymous took to Twitter to declare a campaign named OpIcarus and claim that they had compromised some foreign banks. The target list released by the group included websites of some banks in China. Judging from network information collected, this campaign was mainly for the launch of DDoS attacks.
Reputation is extremely important to the financial sector. Besides mainstream ransomware, cryptomining, and intrusion incidents, financial institutions are also sensitive to information disclosure, service logic, and other events that may blemish their reputation.
- Distribution of incident types – financial sector
2.4.5 Unclassified Sector Mainly Troubled by Ransomware Attacks
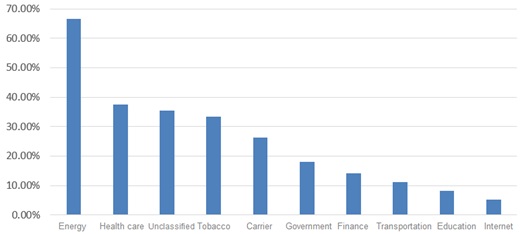
Energy, health care, and unclassified sectors give much regard to service continuity and are very sensitive to security incidents that may affect their normal business operations and reputation. Their data files concern the normal operation of business and are therefore very valuable. If these files are encrypted, the business will probably be affected. For this reason, customers in these areas tend to pay the demanded ransom once their files are infected with ransomware. Lured by the potential great returns, hackers are inclined to launch attacks against these targets.
- Sectors affected by ransomware
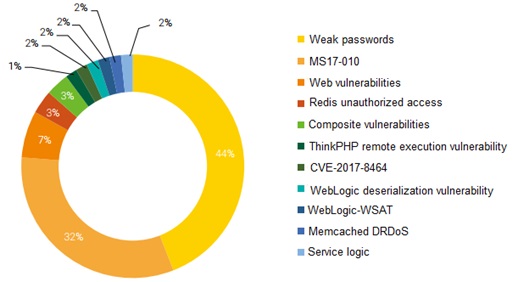
Of all security incidents handled for the unclassified sector in 2018, ransomware incidents took up a large proportion (36%).
- Distribution of incident types – enterprises
As for vulnerability-related incidents, exploitation of weak passwords accounted for 44% of all incidents encountered by the unclassified sector, far higher than other sectors. This means that customers from this sector should increase the security budget to improve cybersecurity management and raise employees’ security awareness.
- Distribution of vulnerabilities exploited against the unclassified sector
2.5 Vulnerable Systems to Be Exposed to More Threats
Along with the continuous development of computer systems, more application programs are emerging, exposing Internet assets to more threats. Attackers can discover public assets on the Internet with such tools as Nmap, Masscan, and Metasploit and reduce related services to their victims. The availability of RDP, SSH, Redis, Memcached, Tomcat, and FTP makes various attacks possible.
2.5.1 1-Day Vulnerabilities Exploited to Preempt Zombie Resources
0-day vulnerabilities are difficult to discover and costly to acquire, so attackers seldom use them for large-scale attacks. However, for 1-day vulnerabilities disclosed through various channels, attackers can quickly develop various automated exploitation tools to scan the whole network for zombie resources. There is a window between vulnerability disclosure and breakout of related incidents. Before a security incident happens, most organizations do not keep tabs on and follow up with the related vulnerability, nor do they load related patches in time, leading to their networks being compromised soon after the vulnerability is disclosed. For example, in January 2018, a cryptomining incident was discovered exploiting the WebLogic WLS component remote command execution vulnerability. Soon after that, similar incidents broke out, affecting a wide range of sectors including the financial and carrier sectors.
If a user takes proper preventive measures by watching for vulnerability and threat alerts released by vendors, for example, by following the official security alert account of a security vendor like NSFOCUS on WeChat, such attacks can effectively be prevented.
The following tables list some new vulnerabilities frequently seen in NSFOCUS’s emergency response services in 2018.
- WebLogic deserialization vulnerability
| WebLogic Deserialization Vulnerability (CVE-2018-2628) | |
| Scope of Impact | Oracle WebLogic Server 10.3.6.0, 12.1.3.0, 12.2.1.2, 12.2.1.3 |
| Type | Remote code execution, deserialization |
| Impact | An unauthorized attacker can remotely attack a vulnerable WebLogic component via the T3 protocol and obtain all privileges for the target system. |
- Struts2-057 remote command execution vulnerability
| Struts2-057 Remote Code Execution Vulnerability (CVE-2018-11776) | |
| Scope of Impact | Struts 2.3 – Struts 2.3.34
Struts 2.5 – Struts 2.5.16 |
| Type | Remote command execution |
| Impact | If the namespace value is not set in the XML configuration and is not set in the Action Configuration or a wildcard namespace is used, Struts 2 may allow remote code execution. |
- Drupal remote command execution vulnerability
| Drupal Remote Code Execution Vulnerability (CVE-2018-7600) | |
| Scope of Impact | Drupal 6.x Drupal 7.x Drupal 8.x |
| Type | Remote Code Execution |
| Impact | An attacker can insert malicious code in a renderable array and then the malicious code submits the renderable array to the Drupal system via the POST method. In the course of page rendering, the malicious code in the renderable array can be taken out via a method call and passed to the call_user_func function, leading to execution of the malicious code. |
2.5.2 N-Day Vulnerabilities Remaining a Threat
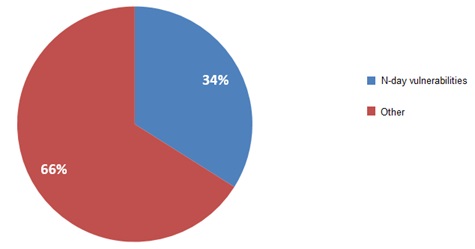
Of all incidents handled in 2018, 34% were caused by historical vulnerabilities, including MS17-010, Struts2-045, Struts2-046, and deserialization vulnerabilities. N-day attacks are usually achieved because of users’ lack of security awareness. Since official patches fail to be updated or installed promptly, cyber criminals can easily use exploits publicly available on the Internet to launch attacks at a low cost but with great damages.
- Proportion of n-day vulnerabilities
The following tables list some n-day vulnerabilities frequently seen in NSFOCUS’s emergency response services in 2018.
- MS17-017 vulnerability (EternalBlue)
| MS17-010 Vulnerability (EternalBlue) | |
| Scope of Impact | Windows Vista, Windows Server 2008, Windows 7, Windows Server 2008 R2, Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows 10, and Windows Server 2016 |
| Type | Remote code execution |
| Impact | An attacker can exploit this vulnerability by sending a specially crafted message to the Windows SMBv1 server. In the worst-case scenario, this may allow remote code execution. |
- Struts2-045 remote command execution vulnerability
| Struts2-045 Remote Code Execution Vulnerability (CVE-2017-5638) | |
| Scope of Impact | Struts 2.3.5 – Struts 2.3.31
Struts 2.5 – Struts 2.5.10 |
| Type | Remote command execution |
| Impact | The Jakarta Multipart parser in Struts does not properly handle exceptions during file upload attempts. A remote attacker can exploit this vulnerability to remotely execute commands via a crafted Content-Type. |
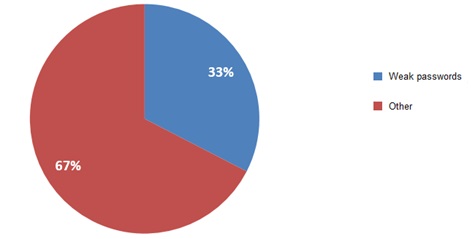
2.5.3 Weak Passwords Remaining the Shortest Plank
In 2018, 33% of security incidents handled by NSFOCUS were achieved by exploitation of weak passwords, which have become one of the most important reasons why security incidents keep emerging. RDP, SSH, Redis, Memcached, and Tomcat services are especially vulnerable to weak passwords. Such attacks affect a range of sectors, including carrier, unclassified, government, financial, and energy sectors, by employing such methods as worms, brute-force cracking, and manual penetration. To conduct weak password attacks, cyber criminals often resort to RDP brute force.
- Proportion of weak passwords among all vulnerabilities
3 Security Recommendations
In the cybersecurity realm, the most fundamental security controls often play a very important role. A majority of security incidents can be protected against with basic controls like the following:
- Effective and modern management system and process mechanism
- Effective network isolation and protection
- Regular/irregular security assessments
- Strict role-based privilege control
- Normalized configuration operations and security audits
- Discovery and remediation of security vulnerabilities
- Desktop security protection
- Continuous staff security training
- 3rd-party service and supply chain security controls
- Security emergency planning and drills
4 Case Study
4.1 Ransomware Attacks
4.1.1 GlobeImposter
Of all emergency incidents handled by NSFOCUS in 2018, ransomware attacks took up a large proportion. Among all ransomware samples, GlobeImposter was the most active.
4.1.1.1 Background
GlobeImposter, in its early days, propagated and infected machines mainly via phishing. Specifically, the attacker sent an email with a JavaScript attachment that would be executed to download the ransomware virus. The first breakout of this virus happened in November 2017. In March 2018, a variant dubbed GlobeImposter 2.0 was spotted, which added the antivirus evasion technique and trace removal function. In August 2017, version 3.0 appeared, functioning like version 2.0, but with an addition of the extension for encrypted files. Besides, it is found that this new variant adopts a manual way of penetration for virus spreading.
4.1.1.2 Virus Analysis
- Propagation Method
GlobeImposter cannot spread on its own, but is delivered via spam and RDP brute-force attacks.
- Step 1 Obtain passwords.
Use mimikatz.exe to obtain all user names and passwords of a host.
Obtain other passwords, including those for access to browsers, Wi-Fi, databases, and email accounts. (passrecenc toolkit)
https://github.com/AlessandroZ/LaZagne
- Step 2 Scan port 3389.
Use the LAN scanning tool nasp.exe to scan port 3389.
Use NetworkShare V2 to scan shared class B IP addresses on the intranet.
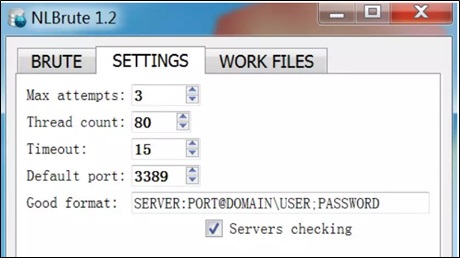
- Step 3 Use NLBrute.exe to brute force RDP.
- NLBrute 1.2
—-End
- Virus Behavior
- Copies the virus to %AppDataLocal%\{Malware Name}.exe.
- Generates a file of SHA-256 values for RSA public keys in the %SystemRoot%\Users\Public\ directory, like:
- B26A340109A0081ADF57D63647533B8681DC0B8E159BE 052385ED4024E9CFFBC
- Adds the virus to the registry as an auto-start item: HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce BrowserUpdateCheck = %Application Data%\{Malware name}.exe.
- Generates a ransom note in the directory of to-be-encrypted files: html
- After initiation, starts encrypting files.
Before encryption, GlobeImposter 1.0 traverses processes and terminates some processes as required. In version 2.0, the virus directly encrypts files without any traversal actions. - After the encryption operation is complete, generates a randomly named .bat file, such as tmpADF9.tmp.bat, in the temporary directory, clears historical records of RDP logins, and deletes itself.
4.1.1.3 Troubleshooting
- Determine the time:
Check the time when the first file was encrypted.
- Locate the process:
Check executables created or modified at the time of intrusion.
Find which processes have high CPU usage.
- Check auto-start items:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- Locate the attack source:
A successful RDP brute-force incident gives rise to four successful audit log messages, with incident IDs of 4672, 4624, 4776, and 4634 respectively. We can obtain the source IP address and login account from these messages.
4.1.1.4 Expert Recommendations
- Try not to expose the RDP port to the Internet and protect this port using IPS, firewalls, or the like.
- Enable the Windows firewall and secure the access to RDP and SMB services through controls such as ACL.
- Configure Windows group policy settings to form an account lockout policy so that accounts with a certain consecutive number of failed login attempts in a short period will be locked.
- Increase the complexity of host account passwords and set the password change cycle to a short period. Besides, avoid using common passwords or passwords with logical meanings.
- Change the default user name of the system administrator to avoid using common ones such as admin, administrator, and test.
- Install antivirus software with self-protection to avoid being shut down or terminated by hackers, and keep the virus database up to date.
- Step up training on employee security awareness. Do not open emails from unknown senders or run programs from unidentifiable sources.
- Promptly apply security patches to the operating system and other applications to fix high-risk vulnerabilities.
- Back up mission-critical business data regularly to avoid issues incurred by data corruption or loss.
4.1.2 GandCrab
4.1.2.1 Background
Since its first appearance in January 2018, GandCrab ransomware has undergone several updates within one year to evolve to V5. This virus employs a variety of methods to attack enterprise networks for propagation. Once a host is infected, databases, files, images, compressed packages, and other files on the host will be encrypted. If there is no backup of related data or files, the normal business operation will be disrupted.
Since September 2018 when V5 came to light, GandCrab has experienced repeated iterations to deliver a series of variants from 5.0.1 to 5.0.5. The virus uses Salsa20 and RSA-2048 algorithms to encrypt files and change file extensions to .gdcb, .grab, .krab, or a string of 5–10 random letters. The ransom note files are GDCB-DECRYPT.txt, KRAB-DECRYPT.txt, and [5–10 random letters]-DECRYPT.html\txt. Besides, the virus changes the desktop wallpaper of the infected host to display a ransom note.
- Desktop wallpaper changed by GandCrab V5.0.5 to a ransom note
4.1.2.2 Virus Analysis
- Propagation Method
The GandCrab family propagates mainly via RDP brute-force attacks, phishing, malware bundling, botnets, and exploits. It does not have the propagation capability that characterizes worms, but can encrypt network-shared resources by means of enumeration. Besides, attackers often try to penetrate intranets to attack other hosts by using such methods as password extraction, port scanning, and password cracking for the purpose of dropping this virus.
- Scope of Impact
Windows operating systems
- Recent Version Changes
V5.0:
The first release requires a call of xpsprint.dll, which, however, does not exist on Windows Vista and XP. Therefore, it cannot be executed on these systems. The second release does not use a fixed .crab or .krab extension for encrypted files, but uses strings of five random letters as extensions.
V5.0.1:
This version fixes some internal errors, without major changes.
V5.0.2:
This version changes the length of random extensions from 5 to 10 characters and fixes some internal errors.
V5.0.3:
This version drops a malicious program named wermgr.exe to perform encryption operations.
V5.0.4:
This version fixes the error of not being able to be executed on Windows Vista and XP, hardcodes a photo of someone, and drops it to disks when the virus is executed.
V5.0.5:
This version changes the encryption key to counter decryption tools provided by Bitdefender and other vendors.
- Virus Behavior
- Terminates the following processes of databases, the Office suite, and game clients:
mysqld.exe, mysqld-nt.exe, mysqld-opt.exe, dbeng50.exe, sqbcoreservice.exe, excel.exe, infopath.exe, msaccess.exe, mspub.exe, onenote.exe, outlook.exe, powerpnt.exe, steam.exe, sqlservr.exe, thebat.exe, thebat64.exe, thunderbird.exe, visio.exe, winword.exe, and wordpad.exe
- Checks the keyboard layout and excludes hosts in regions of specified languages, such as Russian, from being encrypted. Hosts in China are not excluded.
- Encrypts files.
- Calls the system command exe shadowcopy delete to delete volume shadow copies from the disk.
- Changes the current user’s desktop wallpaper to a ransom note, which contains virus version information.
- Attempts to access ports 80 and 443 of the specified domains.
- After the encryption process is complete, deletes itself.
4.1.2.3 Mitigation
GandCrab deletes itself after completing file encryption. That is to say, it does not reside on the system or add itself to the registry as an auto-start item.
If file encryption is ongoing, the virus process does not exit. In this case, we can use a process management tool, such as Process Explorer, to check whether there is a suspicious process and, if so, terminate it immediately to stop file encryption and reduce losses.
4.1.2.4 File Decryption
On October 16, a Syrian user took to the social media Twitter to protest that GandCrab encrypted his files. As he could not afford the high amount of ransom, he could not see photos of his youngest son who had died in the war. This event soon went viral after media reports. The hacker apologized for it and disclosed the decryption keys of earlier versions of GandCrab for hosts in Syria.
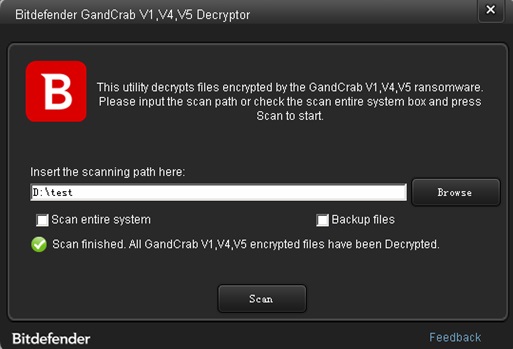
After these decryption keys were disclosed, a number of security vendors released decryption tools. To counter these decryption tools, virus developers soon launched V5.0.5 on October 26.
On October 25, Bitdefender released BDGandCrabDecryptTool on its website https://labs.bitdefender.com/wp-content/uploads/downloads/gandcrab-removal-tool-v1-v4-v5.
This tool works like this: A user submits encryption IDs online to the server, which returns available decryption keys (RSA-2048). According to our test, the tool can decrypt some files encrypted by GandCrab before V5.0.3. When we used BDGandCrabDecryptTool to decrypt files encrypted by V5.0.3, the decryption succeeded.
- GandCrab decryption test
However, BDGandCrabDecryptTool failed to decrypt files encrypted by V5.0.5.
4.1.2.5 Expert Recommendations
See section 4.1.1.4 Expert Recommendations.
4.1.3 Satan
4.1.3.1 Background
GlobeImposter and GandCrab first appeared in November 2017 and January 2018 respectively. Compared with them, Satan is a “big brother”.
Satan made its debut in January 2017. Its creator allows users to generate their own Satan variants via a website. From January 2017 to November 2018, the Satan virus kept updating. The following table lists characteristics of each Satan version. Obviously, the virus has gradually grown from a simple ransomware virus to a mature virus that can spread like worms.
- Table 4-7 Satan version changes
| Version | V1 | V2 | V3 | V4 | V5 |
| First time of appearance | January 2017 | December 2017 | May 2018 | June 2018 | November 2018 |
| Propagation vector | RaaS | EternalBlue | EternalBlue
JBoss deserialization vulnerability JBoss default configuration vulnerability PUT arbitrary file upload vulnerability Tomcat web admin console backstage weak passwords WebLogic Server (WLS) component vulnerability Apache struts 2 remote code execution vulnerability Spring Data Commons remote code execution vulnerability |
RaaS
JBoss deserialization vulnerability JBoss default configuration vulnerability PUT arbitrary file upload vulnerability Tomcat web admin console backstage weak passwords WebLogic Server (WLS) component vulnerability Apache struts 2 remote code execution vulnerability Spring Data Commons remote code execution vulnerability |
EternalBlue
JBoss deserialization vulnerability JBoss default configuration vulnerability PUT arbitrary file upload vulnerability Tomcat web admin console backstage weak passwords WebLogic Server (WLS) component vulnerability Apache struts 2 remote code execution vulnerability Spring Data Commons remote code execution vulnerability Spread via Windows and Linux platforms |
| Ransom amount | 0.3 Bitcoin | 0.3 Bitcoin | 0.3 Bitcoin | 1 Bitcoin | 1 Bitcoin |
| Extension of encrypted files | stn | satan | satan | dbger | lucky |
In early November 2018, NSFOCUS discovered that some of its financial customers had been infected with a worm virus ft.exe that could affect both Linux and Windows platforms. Like the ransomware Satan, the virus spreads itself by exploiting multiple application vulnerabilities. However, this virus, after breaking into the system, does not do anything obviously damaging, but only spreads itself.
At the end of November 2018, a number of financial customers of NSFOCUS were infected with some cross-platform ransomware, which was believed to be a variant of ft.exe with the capability of dropping Monero miners and ransomware. This variant can propagate via Linux and Windows platforms like a worm. In addition, it encrypts local files and appends .lucky to their names besides dropping a ransom note file with the name of _How_To_Decrypt_My_File_.Dic.
4.1.3.2 Virus Analysis
- Propagation Method
The Satan family propagates by exploiting 10 common vulnerabilities listed below. Our current finding is that Satan scans for these vulnerabilities on the Linux and Windows platforms by means of IP address and port listing.
- JBoss deserialization vulnerability
- JBoss default configuration vulnerability (CVE-2010-0738)
- Tomcat arbitrary file upload vulnerability (CVE-2017-12615)
- Tomcat web admin console backstage weak password brute-force attack
- WebLogic arbitrary file upload vulnerability (CVE-2018-2894)
- WebLogic WLS component vulnerability (CVE-2017-10271)
- Windows SMB remote code execution vulnerability (MS17-010)
- Apache Struts 2 remote code execution vulnerability (S2-045)
- Apache Struts 2 remote code execution vulnerability (S2-057)
- Spring Data Commons remote code execution vulnerability (CVE-2018-1273)
- Scope of Impact
Windows and Linux
- Virus Behavior
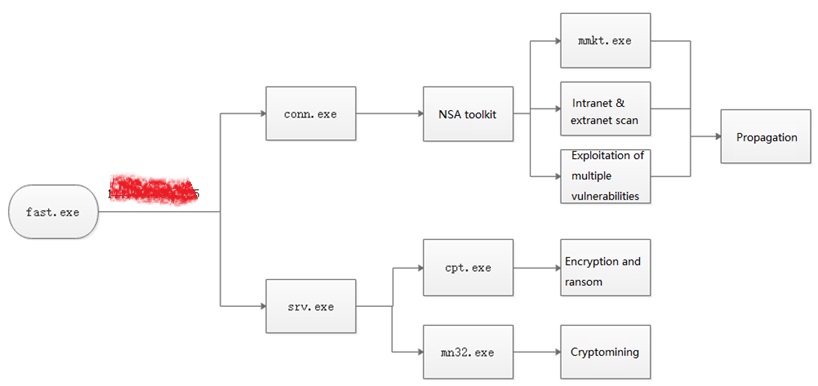
The following figure shows the propagation process of the latest Satan variant.
- Satan propagation process
4.1.3.3 Mitigation
Linux
- Get the machine offline and isolate it from other machines on the same network to avoid a secondary infection during trojan removal.
- Check crontab and local files and delete startup information of the Lucky virus (if any).
- Use kill -9 pid to terminate .loop, .conn32/64, and .cry32/64
- Check where the /etc/rc6.d/S20loop directory points and delete the sample program files from this directory, including .loop, .conn32/64, and .cry32/64 before deleting /etc/rc6.d/S20loop.
- Change the password of the SSH service on the operating system to a strong one.
Manual removal of the trojan from Windows:
- Get the machine offline and isolate it from other machines on the same network to avoid a secondary infection during trojan removal.
- As the trojan incorporates the weak password scanning capability and the password capture tool mmkt.exe, it is necessary to change the system password to avoid a secondary infection during trojan removal.
- Terminate exe, fast.exe, star.exe, srv.exe, conn.exe, and mmkt.exe processes.
- Delete exe from the C:\ directory.
- Delete exe and srv.exe from C:\Program Files\Common Files\System.
- Delete the EternalBlue toolkit from C:\user\all users or C:\ProgramData (note the write time to avoid mistakenly deleting normal system files).
- Delete the registry key/value created by the trojan: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\Logs Service.
- Install the operating system patch specially developed to address the MS17-010 vulnerability (EternalBlue exploit).
- Change the operating system password to a strong one.
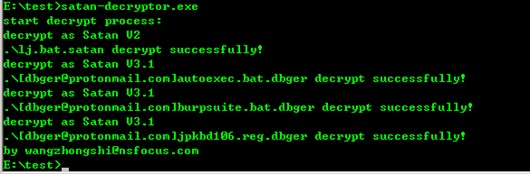
4.1.3.4 File Decryption
On the premise of obtaining the encryption algorithm and key, it is possible to decrypt the files that have been encrypted. NSFOCUS’s Xi’an Network Attack and Defense Laboratory developed a decryptor against this virus. According to tests, this tool works for V2 through V4 and supports file name restoration and bulk file decryption.
How to use this tool:
- Double-click the tool name in the current directory to decrypt all encrypted files in this directory.
- After completing the decryption, the tool automatically restores original file names while retaining encrypted files.
- The tool traverses three-level child directories by default. If the directory level is greater than three, users can specify a directory by using a command line.
- In the command line window, users can specify a directory and the traversal level, for example, exe D:\test 5.
Satan decryption test
.debger file successfully decrypted
4.1.3.5 Expert Recommendations
- Upgrade Apache Struts 2 to the latest version that has fixed S2-045, S2-046, and S2-057 vulnerabilities.
- Upgrade JBoss to the latest version that has fixed CVE-2013-4810 and CVE-2010-0738 vulnerabilities.
- Upgrade Tomcat to fix the arbitrary file upload vulnerability (CVE-2017-12615).
- Upgrade WebLogic to fix the arbitrary file upload vulnerability (CVE-2018-2894) and WLS component vulnerability (CVE-2017-10271).
- Patch the operating system to fix the MS17-010 vulnerability or disable the SMB service if it is unnecessary.
- Increase the complexity of host account passwords and set the password change cycle to a short period. Besides, avoid using common passwords or passwords with logical meanings.
- Change the default user name of the system administrator to avoid using common ones such as admin, administrator, and test.
- Install antivirus software with self-protection to avoid being shut down or terminated by hackers, and keep the virus database up to date.
- Step up training on employee security awareness. Do not open emails from unknown senders or run programs from unidentifiable sources.
- Promptly apply security patches to the operating system and other applications to fix high-risk vulnerabilities.
- Back up mission-critical business data regularly to avoid issues incurred by data corruption and loss.
- Use VLANs or port isolation to separate different business networks to prevent the virus from spreading across network segments.
- Keep track of vulnerability alerts, for example, by following the official WeChat account of NSFOCUS for security alerts, so as to be able to fix critical vulnerabilities in time.
4.2 Cryptomining Incidents
4.2.1 Cryptomining by Exploiting the WebLogic Component Vulnerability
4.2.1.1 Background
In early 2018, NIRT received reports from customers of various sectors, including finance, health care, and education sectors, and found that a number of hosts running WebLogic of various versions were planted with the same malware, which could consume large quantities of host CPU resources. Analyzing the captured attack code, we found that this was a large-scale attack against the wls-wsat component of WebLogic for remote code execution.
4.2.1.2 Troubleshooting Process
In the tmp directory of all infected hosts, there was an executable watch-smartd or Carbon. Analysis of these files led us to believe that they were two versions of cpuminer, a cryptocurrency mining program. After being executed, they would consume large quantities of server CPU and memory resources. This cryptominer could not maintain and revive processes, but could reappear sometime after being removed.
According to information collected, the owners and users of the cryptominer were the same as those of WebLogic. A further check found that the parent process of watch-smartd is WebLogic. Obviously, this incident was associated with vulnerabilities in WebLogic.
According to the attack code revealed in packets captured from infected hosts and the analysis of WebLogic logs, it turned out that the attacker exploited the WebLogic wls-wsat component remote code execution vulnerability (CVE-2017-10271) to download and execute a cryptominer.
The following figure shows the intrusion process.
- Intrusion process
At the beginning, the attacker executes a cURL command via this vulnerability to download a shell script named setup-watch, which is to download and execute the cryptominer. This shell script specifies the download address, download mode, storage location, and operating parameters of the cryptominer.
By analyzing the samples on the server, NSFOCUS’s security researchers concluded that watch-smartd and Carbon were two versions of the same cryptominer, which, connecting to mining pools of minexmr.com and minergate.com, is mainly used to mine Monero (XMR) circulating on the underground market.
4.2.1.3 Mitigation
At the host layer, it is advisable to detect the cryptominer by monitoring host system resources or analyzing processes. At the network layer, we can monitor C&C addresses and domains/IP addresses of mining pools to discover other infected hosts.
For a Linux host, first, check the /tmp directory for suspicious files owned by any WebLogic account, such as watch-smartd, Carbon, and default.
Then analyze processes and system resources to check whether there are suspicious processes launched by any WebLogic account.
Vulnerability remediation and verification:
- First, check which WebLogic hosts have the T3 port publicly accessible. If unnecessary, use a network border device to block this port.
T3 protocol detection
- Install Oracle’s October 2017 patches that fix the WebLogic vulnerability. For the vulnerability advisory and related patches, please visit http://www.oracle.com/technetwork/security-advisory/cpuoct2017verbose-3236627.html.
- If the preceding patches cannot be installed, delete or rename the following WAR packages and directories in the WebLogic directory:
- /home/WebLogic/Oracle/Middleware/wlserver_10.3/server/lib/wls-wsat.war
- /home/WebLogic/Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/tmp/.internal/wls-wsat.war
- /home/WebLogic/Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_internal/wls-wsat
After restarting WebLogic, we can access wls-wsat via the console port (T3 protocol) and check whether the response status code is 404.
4.2.1.4 Expert Analysis
This attack was aimed at downloading and executing a cryptominer. Although this vulnerability was fixed in Oracle’s October 2017 patches, a large number of hosts were compromised because of not installing the latest patches. This indicates that many organizations have long neglected cybersecurity. Disregard for high-risk known vulnerabilities, such as the WebLogic vulnerability, leads to a breakout of this cryptomining incident, costing organizations an arm and a leg. A vulnerability, once discovered, may be exploited by cyber criminals at any time, sometimes resulting in significant asset loses or even legal liabilities.
Today, more and more hacking incidents are occurring, attacking servers by exploiting 1-day or n-day vulnerabilities to garner illegal gains. Organizations should attach importance to and enhance the security of their systems to ensure business continuity while protecting users’ private information.
4.2.1.5 Expert Recommendations
- Organizations should make more efforts to develop a robust security mechanism and at the same time make it a routine to cooperate with security vendors to jointly counter cyberattacks, thereby ensuring their business continuity.
- Organizations should have proper security management regulations in place and install patches in time. When critical vulnerabilities are disclosed, it is particularly important to promptly install related patches and ensure that all related servers are patched. Only with preventive measures properly deployed, can we nip security hazards in the bud.
4.2.2 WannaMine and Its Variants
4.2.2.1 Background
In 2018, NIRT received a series of reports on WannaMine incidents. This worm, after infecting a computer, plants a cryptominer in it, resulting in consumption of large amounts of computer resources and significantly affecting the normal running of the computer. In this sense, it is a very harmful worm. Today, however, a large number of hosts are still not patched and thus exposed to the risk of being infected by variants of the Wanna series virus.
In March 2018, the cryptomining virus WannaMine, as a variant of the ransomware WannaCry, was detected.
In May 2018, a WannaMine variant, WannaMine 2.0, appeared.
In November 2018, another WannaMine variant, WannaMine 3.0, surfaced.
On a local area network (LAN), WannaMine can exploit vulnerabilities in the SMB protocol to achieve fast lateral movement. WannaMine 2.0 and 3.0 spread like WannaCry, but have some new features to evade antivirus detection.
4.2.2.2 Troubleshooting Process
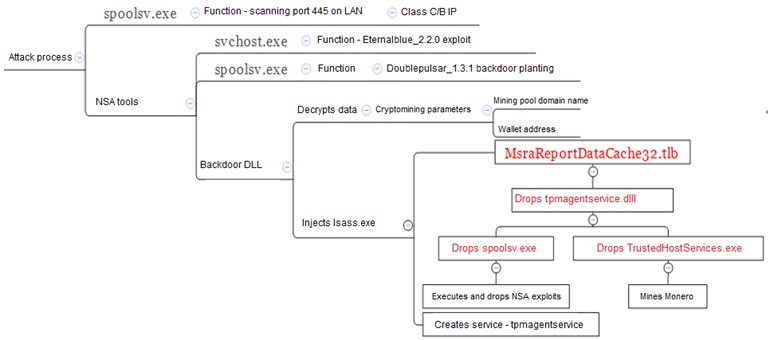
WannaMine exploits the EternalBlue vulnerability to break into a server, plants a cryptominer in this server, and scans hosts in the same network segment to spread the infection. The following figure shows the virus signature.
- Virus signature
WannaMine spreads as follows:
- srv (tpmagentservice.dll) is launched upon computer startup to load spoolsv.
- spoolsv (spoolsv.exe) scans port 445 on the LAN to find vulnerable intranet hosts. At the same time, the cryptominer with the alias of hash (TrueServiceHost.exe) and the exploit programs svchost.exe and spoolsv.exe (NSA’s toolkit) are launched.
- exe implements an overflow attack by exploiting EternalBlue (the target IP address is identified in step 2). If successful, DoublePulsar (a tool from NSA) is then executed via a file called spoolsv.exe to install and load backdoor DLLs.
- After being executed, DLLs (x86.dll and x64.dll) copy MsraReportDataCache32.tlb from the local machine to the host of a target IP address before decompressing it, registering the srv service, and triggering spoolsv to launch an attack.
For every server compromised, WannaMine will repeat the preceding steps. The following figure shows the attack process.
- Attack process
Troubleshooting – network layer:
Use the egress firewall or other similar security devices to monitor requests for access to the backdoor domains, mining pool domains, and kill switch domain (www.iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com) to discover other infected hosts on the intranet.
The following table lists some of these domain names:
- Part of the requested domains
| No. | Domain Name | Mapping IP Address |
| 1 | swt.njaavfxcgk3.club | 31.0.0.0 |
| 2 | tar.kziu0tpofwf.club | 127.0.0.1 |
| 3 | rer.njaavfxcgk3.club | 127.0.0.1 |
| 4 | acs.njaavfxcgk3.club | 127.0.0.1 |
| 5 | nicehash.com | 104.17.60.220 |
| 6 | p3.qsd2xjpzfky.site | 179.61.233.32 |
| 7 | p1.mdfr6avyyle.online | 136.243.102.157 |
| 8 | p1.qsd2xjpzfky.site | 179.61.233.32 |
| 9 | p5.qsd2xjpzfky.site | 179.61.233.32 |
Troubleshooting – host layer:
- Check whether the following processes are active on the host:
- exe (WannaMine 1.0-2.0 Monero cryptominer)
- exe (WannaMine 3.0 Monero cryptominer)
- exe (scanning port 445)
- Check whether the following services exist on the host:
Tpmagentservice (WannaMine 1.0)
wmassrv (WannaMine 2.0)
snmpstorsrv (WannaMine 3.0)
- Check whether the following directories or files exist on the host:
WannaMine 1.0 directories:
- C:\windows\SecureBootThemes
C:\windows\System32\SecureBootThemes
- WannaMine 2.0 directory:
C:\windows\SpeechsTracing
- WannaMine 3.0 directory:
C:\windows\appdiagnostics
- Related files are listed as follows:
- C:\Windows\system32\tpmagentservice.dll (related to WannaMine 1.0)
- C:\windows\system32\TrustedHostServices.exe (related to WannaMine 1.0)
- C:\Windows\System32\MsraReportDataCache32.tlb (related to WannaMine 1.0)
- C:\Windows\system32\wmassrv.dll (related to WannaMine 2.0)
- C:\windows\system32\EnrollCertXaml.dll (related to WannaMine 2.0)
- C:\windows\system32\HalPluginsServices.dll (related to WannaMine 2.0)
- C:\windows\system32\snmpstorsrv.dll (related to WannaMine 3.0)
- C:\windows\system32\trustedhostex.exe (related to WannaMine 3.0)
- C:\windows\system32\marstracediagnostics.xml (related to WannaMine 3.0)
4.2.2.3 Mitigation
At the host layer, we can detect the virus by monitoring host system resources or analyzing processes.
At the network layer, we can monitor C&C addresses and domains/IP addresses of mining pools to find other infected hosts.
Vulnerability remediation and virus removal:
Manual Removal
- Disable and delete related backdoor services, including tpmagentservice, wmassrv, and snmpstorsrv.
- Delete executables of and files dropped by the preceding services.
Virus Removal Script
For the Wanna series virus, NSFOCUS’s WannaMine removal script can be used to remove the virus.
4.2.2.4 Expert Analysis
Microsoft released a security bulletin on the MS17-010 vulnerability on March 14, 2017. But now incidents caused by the Wanna series of ransomware and cryptomining worms still happen from time to time, affecting various sectors. This indicates that organizations trust in luck or are not aware enough of the impact of known vulnerabilities being exploited against them. They may have an ungrounded assumption that similar incidents will not happen again since the vulnerability has been known for quite a while and so let their guard down. However, a vulnerability, once known to the public, can be exploited by perpetrators whenever it is possible. Still worse, variants or other new methods may emerge to exploit this vulnerability.
Nowadays, more and more incidents exploiting known 1-day or n-day vulnerabilities against servers are reported, aimed at data theft, extortion, cryptomining, or DDoS attacks for the ultimate end of garnering illegal gains. Organizations should attach importance to and enhance the security of their systems to ensure business continuity while protecting users’ private information.
4.2.2.5 Expert Recommendations
- During network construction, organizations should conduct proper planning by dividing their networks into security zones to strictly separate the office network and production network.
- Firewalls should be enabled on servers and unnecessary ports should be disabled.
- Organizations should have proper endpoint security management regulations in place and install patches in time. When critical vulnerabilities are disclosed, it is particularly important to promptly install related patches and ensure that all related hosts are patched. Only with preventive measures properly deployed, can we nip security hazards in the bud.
4.3 Intrusion Incidents
4.3.1 Hidden Links to a Gambling Website
4.3.1.1 Background
In early October 2018, a WAF device was found to have blocked a large number of gambling pages. The system is a commercial application TRS built on the architecture of one backend production server plus two frontend publishing servers (master + slave). Editors publish news and generate static pages at the backend and then use the synchronization process to synchronize articles to the master and slave servers at the frontend. Through analysis, we found the gambling files on the two frontend servers were exactly the same.
4.3.1.2 Troubleshooting Process
A vertical comparison of normal HTML files revealed that these files were identical in content between the backend and frontend servers. Therefore, our preliminary deduction was that the entry point may be the backend server.
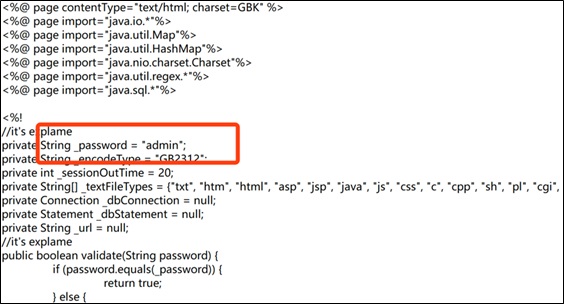
Web Shell Check on the Backend Server
Scan the web directory of the backend server. The following web shell trojans were found:
- /wcm/js/yjh.jsp
- /wcm/logo/yjh.jsp
- /wcm/WCMV6/editor/editor/index.jsp
These files were last modified on July 22, 2018.
/wcm/logo/yjh.jsp is a web shell trojan, with admin as the password. This trojan has the function of creating and deleting files.
- Web shell trojan
When we attempted to directly access http://****/wcm/logo/yjh.jsp, a popup window was displayed, prompting that a login was required. So the attacker must have obtained the backend login account and password before being authorized to access the web shell. A second attempt to log in to the web shell with the administrator account succeeded. Thus, the trojan was successfully exploited.
A look into the log of backend logins showed that only recent logs were retained. Therefore, it was impossible to determine who logged in when the incident happened.
Backdoor Check on the Backend Server
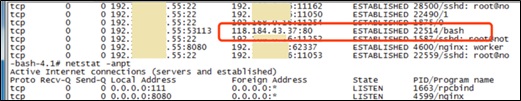
Next, it was necessary to check whether malicious processes were running on the server. In the check, a suspicious connection was spotted.
- Suspicious connection
The server connected to port 80 of 118.184.43.37 (located in Hong Kong) without being requested.
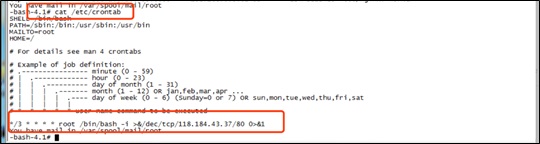
This seemed to be caused by an SSH daemon. A check of scheduled tasks on the server found a scheduled task.
- Scheduled task identified
The function of this task was to project SSH sessions to port 80 of the target server in a scheduled manner so that users can log in to the server without needing to type the SSH password.
Frontend Server Check
We were told that all the passwords were the same. Therefore, it was possible that the attacker breached the backend server and then connected to frontend servers via SSH by using the password of the backend server. As these servers did not have any O&M audit system, historical logins and operations were not logged.
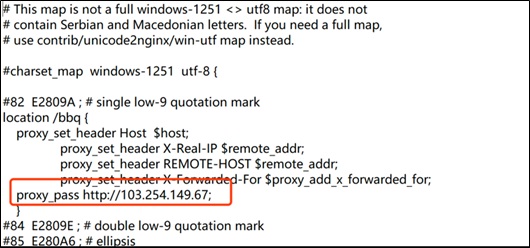
We were also told by system O&M personnel that configuration files were modified. A new configuration file appeared in the nginx folder of a frontend server.
- Suspicious configuration file
proxy_pass http://103.254.149.67 is mainly for route redirection, which explains why we found WAF had blocked sensitive words but could not find a related HTML file on servers..
A vertical comparison of the master frontend server 192.***.***.51 and the slave server 192.***.***.81 showed that the new configuration file created on the master server did not exist on the slave server. This somehow told us that the master server was also breached or possibly planted with backdoors.
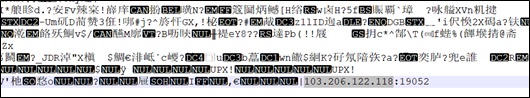
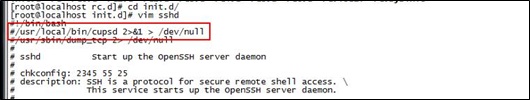
When checking the /usr/local/bin/cupsd file, we found such a backdoor.
- Backdoor
The IP address (103.206.122.118) was also located in Hong Kong. Besides, reverse shells were found.
- Reverse shell
The attacker used these shells to remotely control servers. We checked HTML pages of the gambling website. Overall they looked normal, with changes to only titles and some words. This led us to believe that a bulk script was executed on servers.
4.3.1.3 Expert Analysis
- The attacker uploaded web shells via the admin console and successfully exploited these web shells.
- The attacker used web shells to create a backdoor on the backend server for the purpose of listening for port 22.
- The attacker obtained the server password via listening and exploited the vulnerability of the same password used for both the backend and frontend servers to successfully log in to frontend servers.
- The attacker also left a backdoor on frontend servers to facilitate reverse shells’ control of servers.
- By controlling servers, the attacker achieved script execution, which made it possible to tamper with static files in batches.
4.3.1.4 Expert Recommendations
- There are still some gambling pages on frontend servers. Technical personnel should replace HTML pages of frontend servers with static HTML pages of the backend server.
- Stricter controls should be exercised over server passwords. Different servers must have different passwords, which must be changed once a month and be more complex than those for other types of machines.
- Controls should be tightened over server O&M audits. O&M personnel’s and employees’ operations should be under strict audits and controls for future attribution in case a problem occurs.
- The backend management system should never be deployed on the Internet.
- The two-factor (password + CA, password + fingerprint, password + SMS, …) authentication should be strictly implemented for the backend management system.
- Server privileges should be under strict controls. A port-level access control policy should be adopted for external-to-internal access and an IP- or port-level access control policy should be adopted for internal-to-external access.
- Logs must be properly managed. All logs should be retained for at least 180 days.
Emergency response is a task that requires response personnel to have technical expertise as well as rich experience. Emergency response personnel should be equipped with sufficient basic knowledge of operating systems, databases, and network devices and necessary security skills to cope with common intrusion approaches and popular attack methods. Besides, they should have a certain level of traceback, communication, and coordination capabilities.
NSFOCUS has a professional emergency response team built on years of security research and capable of tracking security dynamics in real time. The team, powered by mature analytics and rich experience, can analyze and handle various major security vulnerabilities and incidents, providing customers with end-to-end emergency response services from incident defining to handling and conclusion.
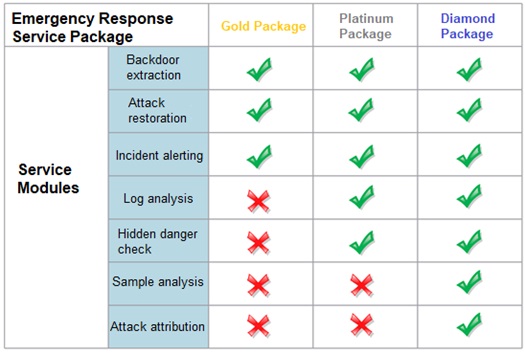
The service consists of incident alerting, backdoor extraction, sample analysis, log analysis, data recovery, hidden danger checking, attack attribution, attack reproduction, emergency response drill, emergency response training, response system development, and security solution modules, which are described in the following table.
- Description of emergency response service modules
| Service Module | Description |
| Common incident response | Response to traditional security incidents, including common web intrusion, host intrusion, viruses and trojans, and DDoS attacks |
| Significant incident response | Response to significant incidents against specific business or of intrusions, such as information disclosure, business loss, and APT attacks |
| Backdoor extraction | Check for and extraction of backdoors in systems or applications, such as virus trojans, system trojans, and web shell scripts |
| Sample analysis | Dynamic and static analysis of samples captured from such platforms as x86, ARM, and MIPS |
| Log analysis | Analysis of log data, including the web log, operating system log, application log, and device-related log |
| Attack attribution | Incident traceback to find out attackers, including the IP address, geographic location, and personal information |
| Emergency response training | Technical training on emergency response for organizations’ security teams or O&M technicians |
| Emergency response drill | Drills on emergency response for specific security scenarios, including plan design and environment setup |
| Security solution | Provisioning of effective solutions for typical security incidents known to the public or security incidents that have just happened |
| Emergency response system development | Provisioning of consultancy on or overall scheme for development of an emergency response system and emergency management process |
Besides, in response to requirements for handling different security incidents, NSFOCUS offers gold, platinum, and diamond emergency response packages. Different levels of service packages contain different modules. The diamond package covers all modules.
- Emergency response service packages
[â‘ ] http://www.cac.gov.cn/wxb_pdf/0228043.pdf