The blocklist is matched based on the source IP address, destination IP address, or a combination of source and destination IP addresses of a packet. The blocklist works for TCP and UDP transport layer packets. That is to say, after an IP address is added to the blocklist, the ping is successful, but transport layer services cannot be accessed.
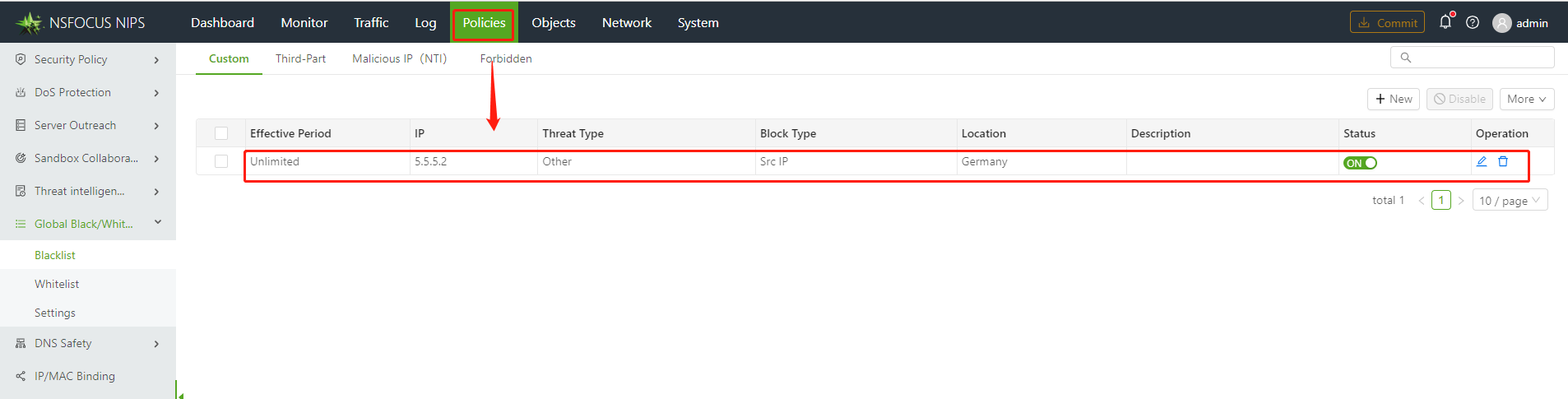
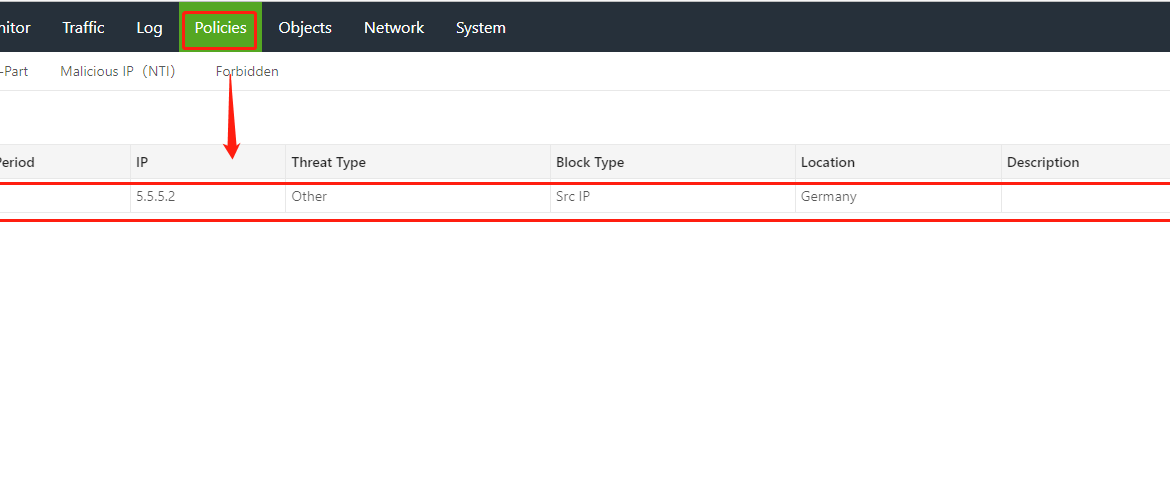
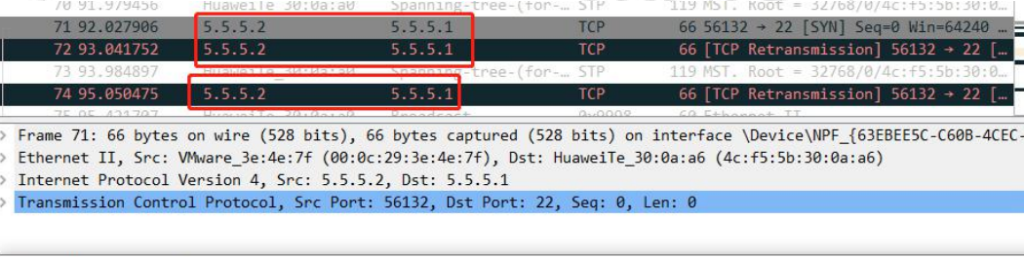
For example, after a source IP address 5.5.5.2 is on the blocklist, the source IP address 5.5.5.2 can ping the destination IP address 5.5.5.1 successfully, but cannot access port 22 of 5.5.5.1 by using Telnet.
The blocklist on NSFOCUS Network Intrusion Prevention System (NIPS) directly blocks the carried transport layer packets. When capturing packets, you can find that the outbound SYN packets are blocked by the NIPS, and the SYN-ACK response from the peer cannot be received.
The priority order of the blocklist and whitelist is as follows:
Manual whitelist > Manual blocklist > Blocklist issued by a platform —NSFOCUS Enterprise Security Platform Center (ESPC) or NSFOCUS Intelligent Security Operation Platform (ISOP).