Overview
In 2022 Q2, NSFOCUS Security Labs detected a series of cyberattacks against Turkey. After analysis, the researchers confirmed that this round of attacks originated from Actor210426, a new threat entity identified by NSFOCUS Security Labs in April 2021. Through the clues of behavior pattern, attack method, attack tool, attack target and so on, NSFOCUS Security Labs conducted an in-depth investigation on the threat entity, and confirmed its independence and nature of advanced threat.
Based on the threat entity’s area of activity and recent attack target (Turkish Navy project ” MÃœREN “), NSFOCUS Security Labs officially named it MurenShark, and assigned an identifier APT-N-04.In the monitored activities, the main target areas of MurenShark include Turkey and Northern Cyprus, and the attack range covers numbers of sensitive targets in the fields of universities, research institutes and the military. In particular, it shows obvious interest in military projects, and has carried out successful cyber espionage activities.
MurenShark organization has rich experience in confrontation, counter-analysis and reverse-traceability. The investigation shows that the exposed attacks are only the tip of the iceberg of the group’s operations, with a discontinuous iterative trajectory of targets and components suggesting that many of the group’s activities remain unknown.
NSFOCUS will share the characteristics of the organization, the relationship with known APT organizations and other findings during the detection.
Organization Information
MurenShark organization is a new threat entity active in the Middle East. The main target country is Turkey. The discovered targets include universities in Northern Cyprus, Turkey’s army and Turkey’s national scientific research institutions.
The main attack methods of MurenShark include delivering phishing documents and attacking online services. The direct purpose includes expanding attack resources, penetrating target networks and stealing key data. The organization’s known Spear Phishing first appeared in April 2021, while the intrusion into the university website was earlier than that date.
MurenShark has rich experience in confrontation, and is good at hiding attacker information through springboard nodes, blocking process recurrence through component splitting, and reducing code features using third-party solutions.
The attacker information is well-hidden in the implemented activities. At present, it is impossible to confirm the geographical affiliation of the organization.
Attack Tactic Matrix
The following figure shows the attack tactic matrix of MurenShark, including the capabilities mastered by the attackers and developers, and the capabilities realized with the help of third-party tools.
| Intrusion | Lingering | Authority Access | Defense Break | Information Gathering | Lateral Movement | Command Control | Data Theft |
| Phishing | Scheduled Task | Privilege Promotion | Claim Rights | User Account Collection | Remote Service | Application Layer Protocol | Steal Channel |
| User Execution | Bits Task | Manipulation Token | Manipulation Token | File Directory Collection | User Authentication Abuse | Data Coding | Timed Theft |
| Utilization of Third-Party Credit | System Task | Create Modification Process | Hide Components | Service Scan Collection | Data Obfuscation | Transport Protocol | |
| Vulnerability Execution in Client | Office Application Startup | Exploit Loopholes to Claim Rights | Damage Defense | Network Share Collection | Encrypted Channel | ||
| System Function Abuse | Scheduled Tasks | Remove Intrusion Traces | Permission Group Collection | Protocol Channel | |||
| Create/Change System Process | Valid Account | Modify Registry | Process Collection | Agent | |||
| Confusing File Information | Registry Collection | Custom Tool Delivery | |||||
| Process Injection | Remote System Collection | ||||||
| Reflection Injection | Software Collection | ||||||
| Break Trust Control | Network Configuration Collection | ||||||
| Signature Binary Proxy Execution | Network Connection Collection | ||||||
| Valid Account | Browser Middleman Collection | ||||||
| User Authentication Abuse | Information Base Collection | ||||||
| System Dump | System Data Collection | ||||||
| Virtualization Escape | Keyboard Input Collection | ||||||
| Anti-Debugging | Screen Capture Collection |
Typical Activities
MurenShark is not a very active attacker, and its attack activity distribution has obvious aggregation.
The latest round of activities of MurenShark was concentrated in the early August 2022. The attackers delivered various forms of phishing documents in Turkish to attack specific targets in Turkey.
The phishing documents are named as below:
| File name |
| Birlestirilmis_GORUSLER.doc |
| MURENPRVZ-KYP-03-EK5-YKS.doc |
| MURENPRVZ-KYP-03-EK5-YKS.doc |
| MURENPRVZ-STB-XX-XX(Surum Tanimlama Belgesi).doc |
| Birlestirilmis_GORUSLER-Tubitak’a Gonderilen2 2022.08.05 14.41.22.doc |
| KGB Numaralari ve Gecerlilik Tarihleri.xlsx |
The first type of phishing document is titled as “Feedback of MÃœREN’s Critical Design File ” (MÃœREN KRÄ°TÄ°K TASARIM DOKÃœMANINA YÖNELÄ°K GÖRÜŞLER), the heading of the document shows that its source is “Command of TCG Sakarya of the 1st Submarine Fleet of the Naval Command”:
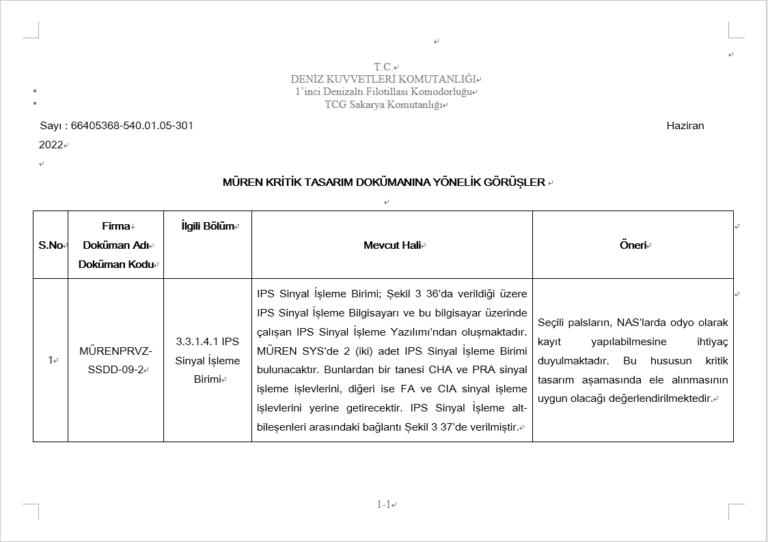
This document records the Turkey Navy’s feedback of a submarine internal system named ” MÃœREN “, and the document date is June 2022.
Another type of phishing document is titled as National Production Integrated Underwater War Management System Pre-Class Application MÜREN-PREVEZE Project (MİLLİ ÜRETİM ENTEGRE SUALTI SAVAŞ YÖNETİM SİSTEMİ PREVEZE SINIFI UYGULAMASI (MÜREN-PREVEZE) PROJESİ). It is from the Information Science and Advanced Information Security Technology Research Center of Scientific and Technological Research Council of Turkey (TÜBİTAK BİLGEM).

This phishing document corresponds to a description file of a software system named ” MÃœREN-PREVEZE “.
After querying relevant keywords, NSFOCUS Security Labs determined that the above two documents were from the Turkey military project “MÃœREN”. This is an underwater combat management system (CMS) carried on submarines, developed by Scientific and Technological Research Council of Turkey (https://bilgem.tubitak.gov.tr/tr/haber/akya-torpidosu-muren-prevezeye-entegre-ediliyor), and has been tested in 2021 and provided to Turkey naval command in 2022 (https://raillynews.com/2021/11/denizaltilari-muren-yonetecek/). Turkey’s navy has great expectations for the MÃœREN project, believing it can promote the localization of Turkey’s navy system and become a key step of Turkey’s national submarine project “MILDEN” (https://www.navalnews.com/naval-news/2021/11/turkeys-new-submarine-cms-muren-to-enter-service-in-2022/)
It can be inferred that the main target of MurenShark’s activities in early August is the relevant personnel of “MÃœREN” project, including the project designers of Scientific and Technological Research Council of Turkey and the project reviewers of Turkey Navy.
According to the information currently available, NSFOCUS Security Labs cannot judge whether this round of attack has achieved its intended purpose. However, it can be seen from the content of the bait documents that MurenShark has successfully invaded the interior of Scientific and Technological Research Council of Turkey through other attacks, and has stolen high-value documents.
MurenShark showed a completely different attack tendency in their earlier attacks. In a round of attacks reported by NSFOCUS Security Labs, the organization used a report document related to Dogecoin as the bait to conduct phishing attacks:
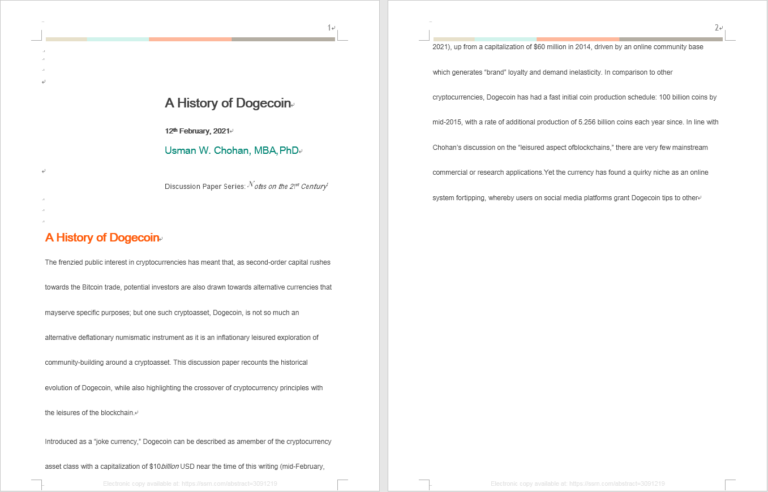
The MurenShark has not exposed any other information in this activity except that the bait document was found in Turkey.
Affected by the national economic policy, the cryptocurrency industry is very popular in Turkey. In combination with the activity track of the organization, NSFOCUS Security Labs infers that this kind of phishing attack is a part of the coarse precision phishing activities organized by MurenShark, and the main target is also Turkey. Hacker organizations usually rely on such bait documents with popular topics to conduct a wide range of information gathering activities, and then sort out high-value information from the obtained intelligence.
Typical Attack Process
MurenShark frequently uses a representative attack process and continues to improve the process and its components.
The following figure shows the typical processes used by the organization in its 2021 activities:
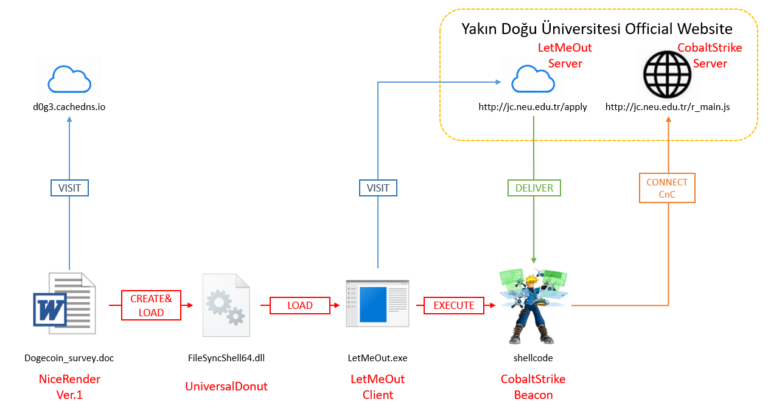
The attack process is composed of three main attack components of MurenShark: NiceRender, UniversalDonut, LetMeOut, the compromised site neu.edu.tr, and the third-party attack tool CobaltStrike, which ultimately achieve the purpose of stealing the data in the victim host and moving horizontally within the domain where the victim host is located.
The following figure shows the improved process used by the organization in recent attacks against Turkey’s navy and scientific research institutions:
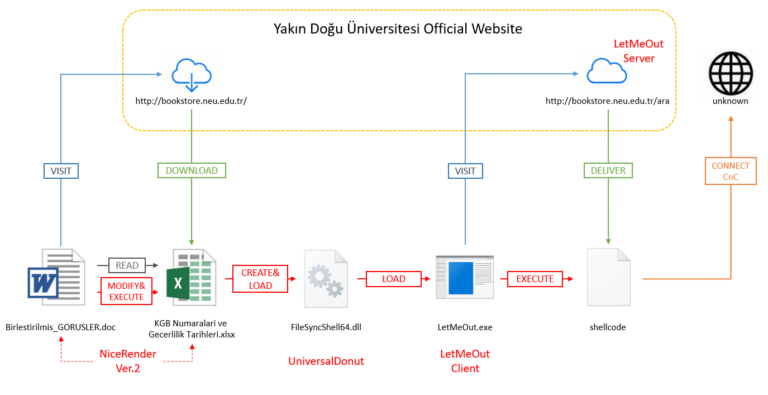
The process also consists of three main components and the same compromised site. The difference is that the MurenShark attacker used the new NiceRender file in the process, and further shortens the life cycle of the process. These operations made it difficult for sandbox security products to reproduce the complete execution process.
Part 2: Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [2]