-
Vulnerability Description
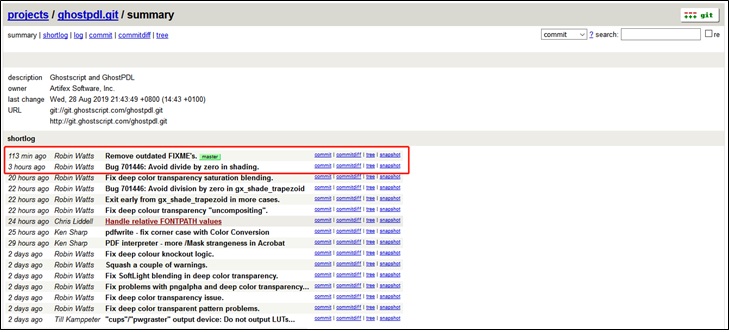
On August 28, 2019, Artifex submitted “Bug 701446: Avoid divide by zero in shading” on the master branch of Ghostscript and announced remediation of four -dSAFER sandbox bypass vulnerabilities. -dSAFER is a security sandbox used by Ghostscript for prevention of insecure PostScript operations.
Ghostscript is a free suite of software based on an interpreter for Adobe System’s PostScript and Portable Document Format (PDF) page description languages. It is widely used as a raster image processor (RIP) for raster computer printers. Currently, it has been ported from Linux to other operating systems, including UNIX, Mac OS X, VMS, Windows, OS/2, and Mac OS classic.
The four vulnerabilities disclosed this time exist respectively in .pdf_hook_DSC_Creator (CVE-2019-14811), .setuserparams2 (CVE-2019-14812), setsystemparams (CVE-2019-14813), and .pdfexectoken (CVE-2019-14817) procedures. An attacker could exploit this vulnerability to gain access to the .forceput operator via a malicious postscript file, bypass the -dSAFER protection, and execute arbitrary commands.
References:
https://access.redhat.com/security/cve/cve-2019-14811
https://access.redhat.com/security/cve/cve-2019-14812
https://access.redhat.com/security/cve/cve-2019-14813
https://access.redhat.com/security/cve/cve-2019-14817
https://www.openwall.com/lists/oss-security/2019/08/28/2
-
Scope of Impact
This vulnerability affects all applications that use Ghostscript to process PostScript contents.
Affected Ghostscript versions:
- Ghostscript before commit f531552c99a04f003412f7a83d4661e927f88d40
Unaffected Ghostscript versions:
- Ghostscript commit f531552c99a04f003412f7a83d4661e927f88d40 and later
-
Recommended Solution
Official Fix
Currently, there has been no official release to fix this vulnerability. Users can use git commands to upgrade their installations to commit f531552c99a04f003412f7a83d4661e927f88d40 or later, or directly pull the master branch code to protect against this vulnerability.
http://git.ghostscript.com/?p=ghostpdl.git;a=summary
For how to fix CVE-2019-14811, CVE-2019-14812, and CVE-2019-14813 vulnerabilities, visit the following link:http://git.ghostscript.com/?p=ghostpdl.git;a=commitdiff;h=885444fcbe10dc42787ecb76686c8ee4dd33bf33For how to fix the CVE-2019-14817 vulnerability, visit the following link:http://git.ghostscript.com/?p=ghostpdl.git;a=commitdiff;h=cd1b1cacadac2479e291efe611979bdc1b3bdb19
Red Hat 7 and 8 distributions have been updated to fix these vulnerabilities. Users are advised to upgrade as soon as possible.
Note: Currently, Red Hat Enterprise Linux 5 and Red Hat Enterprise Linux 6 are out of support. Users of these two distributions should take temporary measures described in section 3.2 to protect against these vulnerabilities.
Workarounds
If users cannot upgrade to the fixed version for the time being, they can take the following measures as temporary protection against these vulnerabilities:
- Configure a security policy on ImageMagick. ImageMagick uses Ghostscript by default as the interpreter to process PostScript contents. Therefore, users can configure a security policy.xml on the ImageMagick component to disable the use of Ghostscript and the processing of PS, EPS, PDF, and XPS file formats. Users can modify the policy configuration file of ImageMagick by adding the following code to <policymap> in the /etc/ImageMagick/policy.xml directory (default location of the policy configuration file).
| <policymap>
<policy domain=”coder” rights=”none” pattern=”PS” /> <policy domain=”coder” rights=”none” pattern=”EPS” /> <policy domain=”coder” rights=”none” pattern=”PDF” /> <policy domain=”coder” rights=”none” pattern=”XPS” /> <policy domain=”delegate” rights=”none” pattern=”gs” /> </policymap> |
- These vulnerabilities may be triggered when Ghostscript processes files in order to generate thumbnails. To avoid this issue, users can delete or rename the /usr/bin/evince-thumbnailer executable.
- Run PDF and PS viewers, such as evince, in a SELinux sandbox using the following command:
| $ sandbox -X evince <untrusted-file.pdf> |
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.