
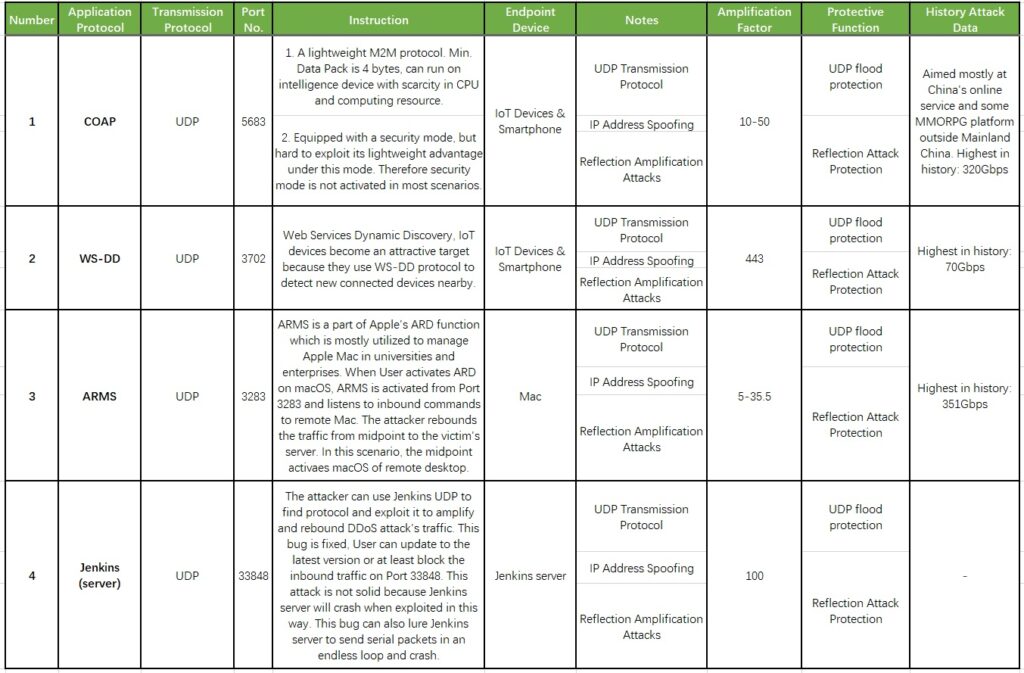
According to ZDNet’s reports, FBI released a warning last week that some new network protocols were used by criminals to launch large-scale DDoS attacks. Three protocols and one Web applications were found as DDoS attack vectors, including CoAP, WS-DD, ARMS and Web-based Jenkins.
CoAP: Constrained Application Protocol
CoAP is a lightweight M2M protocol that can run on intelligence device with scarcity in CPU and computing resource. Simply put, CoAP is very similar with HTTP, however, it does not work on TCP but on UDP, a more lightweight data transmission format that can replace TCP. Like HTTP transferring data and commands (GET, POST, CONNECT, etc.) between clients and servers, CoAP can realize multicasting and command transport with less resource. This makes CoAP an ideal option in a fast-developing IoT device environment. However, like other UDP-based protocols, CoAP is susceptible to IP address spoofing and pack amplification, which is mainly why it can easily be abused by DDoS attacks.
WS-DD: Web Services Dynamic Discovery
WS-DD is a service discovery multicasting protocol inside LAN. Due to its defective design, when receiving discover message from a normal IP address, the device also replies. In addition, the device is exposed on the internet, so it can be used by DDoS attackers. WSD protocol’s port number is 3702. At present, WSD is mentioned as a service discovery protocol in video monitoring equipment’s ONVIF Standard. Some printer equipment also activated the WSD service. In fact, NSFOCUS has already published an early warning on WS-DD. Please refer http://blog.nsfocus.net/ws-discovery-reflection-attack-analysis/
ARMS: Apple Remote Management Service
According to research, web criminals used ARMS (a part of ARD function) to conduct DDoS amplification attacks. After activating ARD, ARMS will start to listen to inbound commands transmitted to remote Apple devices on port 3283. Then, attackers are able to amplify 35.5 times of DDoS attacks. This bug originates from its defective design. When using UDP, Client sends a minimized UDP pack to netAssistant (port number 3283), netAssistant then sends back a hyper UDP pack with Host Identity. There is a massive gap in sizes between Request and Response. Since there is no restriction on Request/Response ratio, any web device with netAssistant activated in public network can be used as a reflection source.
Jenkins: an extensible and open source server that helps automate the parts of software development related to building, testing, and deploying, facilitating continuous integration and continuous delivery. Attackers take advantage of its defect to conduct DDoS attacks. The bug in Jenkins’s codebase is traced as CVE-2020-2100. Although this bug has been fixed in Jenkins v2.219 released earlier, many Jenkins servers are still under this influence.
Other than DNS, NTP, etc., there are some UDP protocols that can be used to conduct reflection amplification attacks. E.g., SSDP, QOTD, SNMP, CHARGEN, LDAP, MEMCACHE, WS-DISCOVERY, etc., UDP is connectionless, so attackers can utilize this feature to attack the Target Host with very little cost, making it incapable of responding to the right requests, even rejecting them. Using UDP to conduct reflection amplification attacks has become very popular in recent years.
In fact, these four new attack forms mentioned by FBI are not so different from other reflection attacks. How shall we defend against UDP attacks like this? In the perspective of algorithm, there are some common solutions:
- Fingerprint learning: detect and learn the Payload from UDP message, extract this content as fingerprint data to determine ACCEPT or DROP commands based on data feature.
- Volatility limits algorithm: learn and build model on the normal service traffic, monitor the traffic and block/limit the ones showing a rapid increase to prevent the impact on normal traffic.
- Rate limits on IP and Port: make flexible and effective solution by combining Source IP, Source Port, Target IP and Target Port.
- Whitelist: add the known UDP reflection protocol into the whitelist such as DNS server IP address. Block Port 53 Request packs from other source IPs so to reduce the impact of attacks.
- Geo filter: based on client’s geographic feature, block the source IP with the least user amount when UDP reflection amplification attacks happen until all source IP requests from abnormal geographic location are rejected, so the traffic can be reduced in a scope that the server can handle.
