As a wind vane of security technology development, RSA 2019 presents new technologies, new products, and new domains among important technological trends and directions, with a special focus on enterprise business security risks and control in sectors such as government, finance, transportation, energy, aviation and aerospace, healthcare, and education.
Based on views of Emily Heath (vice president and chief security officer of United Airlines) and Pete Cooper (strategic advisor of IATA), I would like to take the aviation transportation sector as an example to discuss business security risks and control.
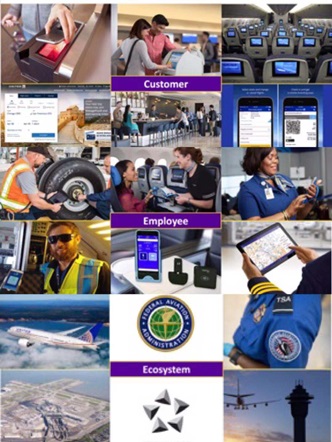
From the perspective of core business of aviation, security considerations in the sector should be around customers, staff, and ecology.
- Customers: ticketing, security check, information inquiry, member service, in-flight entertainment, and in-flight Wi-Fi.
- Staff: air traffic management, flight data communication, aircraft maintenance, identity recognition, and global positioning system (GPS).
- Ecology: aviation companies (airline alliances), airport, aviation supply chain, aviation maintenance, ground stations, satellite communications, aviation data, and parts suppliers.
The above three dimensions constitute an aviation ecosystem. This system involves a wide variety of complicated IT business applications and some mission-critical businesses are strongly related to each other in data dimension. For this reason, cybersecurity in this sector should be more business-oriented to ensure that businesses in multiple domains coordinate in a secure way, rather than just focusing on the infrastructure in a certain dimension.
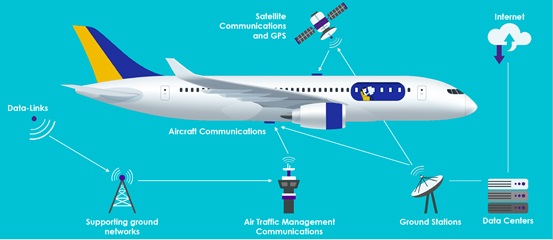
- Data Connections of Aircrafts Above 10,000 Meters
Aircrafts are the focus of aviation security. Their network communications refer chiefly to communications between communication nodes on aircrafts with air traffic management; communication nodes on the control tower, satellite communication nodes, and GPS nodes. The entire flight process consists of taxiing, takeoff, climb, cruise, descending, and landing phases. During different phases, aircrafts will connect to different network nodes for communication, for example, establishing communications with the control tower at the airport in the taxiing, takeoff, descending, and landing phases, and connecting to satellite communication nodes and the ground network through ground stations in the cruise phase.
We can easily find that, from the interconnected perspective of data communications of the complete aviation ecosystem, network communication nodes will access a wide range of nodes to make complicated connections, including remote data connections, connections to the aircraft ground support network, ground base stations, and the data center network, and access to the Internet. Â Therefore, for aircrafts under the coverage of several wireless networks, it seems particularly important to ensure the reliability and integrity of communications of the aviation ecosystem.
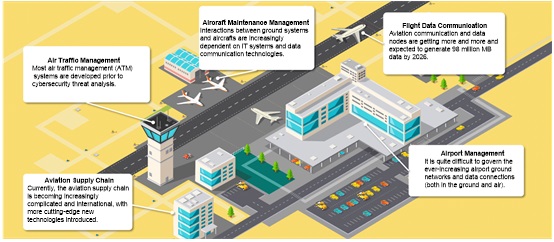
- Complex Threats Against the Aviation Ecosystem
The aviation ecosystem network demands that information systems should be adapted to heterogeneous system integration and should be portable and worth popularizing. Currently, information systems deployed in aviation networks, which are mostly from overseas vendors, connect to the air network management system through dedicated lines of operators. However, the current fact is that deficient security separation mechanisms are deployed between system networks in various ecological domains; most air management information systems are short of ciphering technologies; IT O&M personnel lack security skills. Due to all of these facts, viruses, data theft, and air management information theft risks continue to exist.
General Accounting Office (GAO) strongly criticized that a great number of security vulnerabilities in Federal Aviation Administration (FAA)’s air-ground communications and NAS system may pose threats to the aviation network and its passengers, due to extremely poor information security management.
In addition, data security is one of great challenges to the aviation field. As a large number of aviation systems go live, including the ticketing system, member services, aviation information systems, and remote management systems, data compliance management, data disclosure, and defacement among other numerous security issues have become the biggest headache to the aviation field around the globe for almost two years.
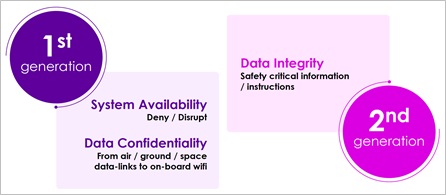
Pete Cooper believes that cyberattacks against the aviation field have went through two phases:
- Phase 1: targeting the availability of the air/ground system and data confidentiality.
- Phase 2: targeting the data integrity, especially in the wake of the release of General Data Protection Regulation (GDPR).
- Building of a Security Architecture Model
Emily Heath sets the following security protection objectives around core business of three dimensions, i.e., customers, personnel, and ecology, of the aviation ecosystem: infrastructure & network security, sensitive data security, mission-critical business security, as well as security of associated communications between aviation ecologies.
| Infrastructure & Network
ü  Computers ü  Servers ü  Networks ü  Cloud environment ü  Applications ü Mobile devices |
Sensitive Data
ü  Personal data ü  Customer/personal data ü  Compliance data (Sarbanes, GDPR) ü  Financial data ü Strategic/corporation data |
Mission-Critical Business Systems
ü  Mission-critical systems of aviation corporations ü  Business systems that hold non-sensitive data ü Systems which may have impact on business or financial affairs |
Aviation Ecologies
ü  Aircraft communication security ü  Airport communication security ü  Third-party & supply chain ü Government agencies & partners |
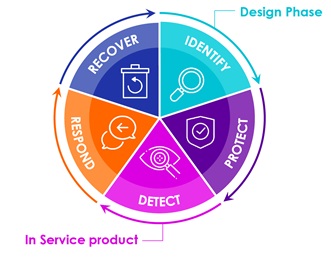
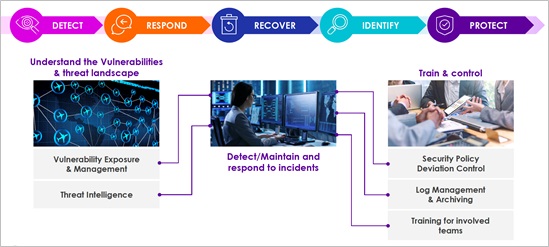
Pete Cooper designs the security architecture from the perspective of security lifecycle, aiming to enhance cybersecurity risk management from identification, detection, protection, response, and recovery dimensions by reference to the Framework for Improving Critical Infrastructure Cybersecurity included in NIST SP 800-53 (Revision 4).
In the above architecture, the identification phase is designed for risk identification. First, a distinction should be made between safety and cybersecurity. Any risks that could cause safety incidents or may intentionally result in cybersecurity incidents should be identified completely.
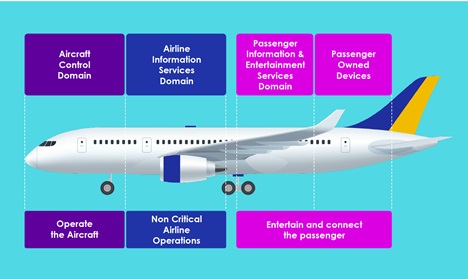
For example, the aircraft cabin network design should take full account of cybersecurity threats and corresponding separation mechanisms.
Generally, an aircraft network is composed of three communication subnets:
- Aircraft control subnet: core network that has direct impact on flight safety. The subnet is responsible for transmitting flight sensing data and operation instructions of the pilot.
- Information service subnet of an aviation corporation: network for communications between crew members.
- Passenger communication subnet: network for communications for passengers on board, consisting of an airborne device subnet (including a network for entertainment and advisory services) and a subnet dedicated for passengers (Wi-Fi for access from mobile phones and tablet devices).
Of the preceding three subnets, the passenger communication subnet is the least trusted and must be physically separated from the other two subnets. For each subnet, network access control and wireless identity authentication should be enhanced. Besides, data security issues (such as data transmission, privacy protection, and data integrity) that may arise during external communication of passengers on board should be taken into account.
The detection, protection, response, and recovery phases involve traditional asset management, security policies, log management, personnel assessment, security awareness training, and response and recovery, laying special stress on the combination of threat monitoring, closed-loop vulnerability management, and threat intelligence. This aligns with our country’s cybersecurity strategy and the direction of security assurance of critical infrastructure.
The preceding views also inform the design concept of the security operation architecture released by NSFOCUS in 2018. Also, NSFOCUS provides corresponding security services and products.
- Summary
At last, Peter Cooper proposed “similar challenges to other critical sectors”, which means that infrastructure in other critical sectors faces similar cybersecurity challenges.
This is the case. For key sectors such as transportation, finance, energy, healthcare, and Internet, the security of the business process logic and the multi-layered business ecology deserves special attention. However, traditional security protection means usually cannot effectively resolve issues with the business logic design or security protection mechanisms fail to focus on business logic defects. In addition, even if the business logic is all right, it is possible that the organizational structure and process supporting business contain security risks.