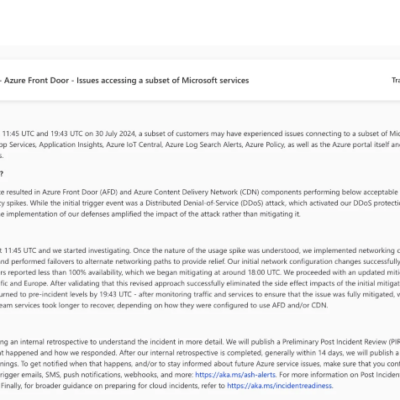
Microsoft acknowledged a service disruption that affected a range of its cloud services on July 30, 2024. The incident, which spanned from 11:45 UTC to 19:43 UTC, saw customers globally experiencing difficulties connecting to services such as Azure App Services, Application Insights, and the Azure portal, among others. The unexpected...
Category: Blog
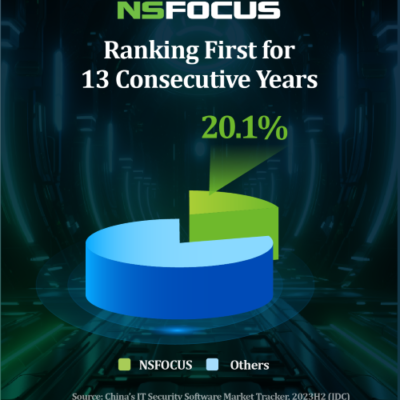
NSFOCUS RSAS New Features Unleashed
NSFOCUS Remote Security Assessment Security (RSAS) is a specialized, all-encompassing vulnerability scanner tailored for clients performing security assessments. It is adept at swiftly identifying a full spectrum of weaknesses within network systems. NSFOCUS RSAS is not just a scanning tool; it's a comprehensive solution that efficiently identifies a plethora of...
Lessons Learned from the CrowdStrike Incident: Strengthening Organizational Resilience
On July 19, 2024, a major global digital catastrophe unfolded as a faulty Windows update led by cybersecurity firm CrowdStrike's Falcon software caused widespread system crashes and service disruptions across vital sectors in over 20 countries. This incident has exposed the deficiencies of Microsoft and its partners in product stability...
TransparentTribe’s Spear-Phishing Targeting Indian Government Departments
Overview Leveraging our global threat hunting system, NSFOCUS Security Research Labs discovered spear-phishing email attacks by the APT group TransparentTribe targeting Indian government departments on February 2, 2024. The timing of these attacks coincides with the presidential election in India, scheduled for April-May of this year, and the bait documents...
JumpServer File Read and Upload Vulnerability (CVE-2024-40628/CVE-2024-40629) Notification
Overview Recently, NSFOCUS CERT detected that JumpServer issued a security announcement and fixed the file reading and uploading vulnerabilities in JumpServer (CVE-2024-40628/CVE-2024-40629). Due to improper permission configuration of the Ansible module in JumpServer, an attacker with a low-privilege account can use the ansible playbook to read arbitrary files in the...
Critical Patch Update Notice in July for All Series of Oracle Products
Overview On July 17, 2024, NSFOCUS CERT detected that Oracle officially released a critical patch update announcement CPU (Critical Patch Update) for July. A total of 397 vulnerabilities of varying degrees were fixed this time. This security update involves Oracle WebLogic Server, Oracle MySQL, Oracle Java SE, Oracle Fusion Middleware,...