Debut of CASB
With cloud computing being a key to industry revolution, more and more enterprises and organizations are discovering the benefits of storing and processing data in the cloud and migrating business systems from local data centers to the cloud.
As business systems are migrated to the cloud, the security responsibility of enterprises has also been shifting. Before business goes to the cloud, enterprises deploy in local data centers, solely responsible for all security issues; however, when business systems are migrated from data centers to the cloud, various cloud platforms inevitably assume part of the responsibility to digital security of enterprises, forming a pattern of responsibilities shared and roles played respectively.
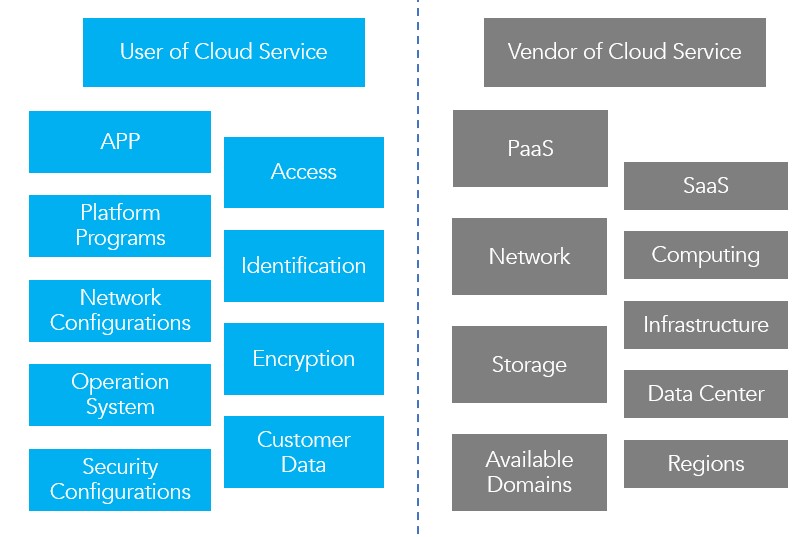
Following the “Responsibility Shared Pattern”, enterprises lose full control of their digital security. Faced with questions including “Are the cloud applications we are using secure and controllable?â€, “Have employees bypassed IT to use unknown cloud applications?â€, “Are employees operating in the cloud in compliance?â€, enterprises are encountering a number of security issues, making it really urgent to build trust between them and various cloud service vendors. It is under such a background that CASB was born.
What is CASB?
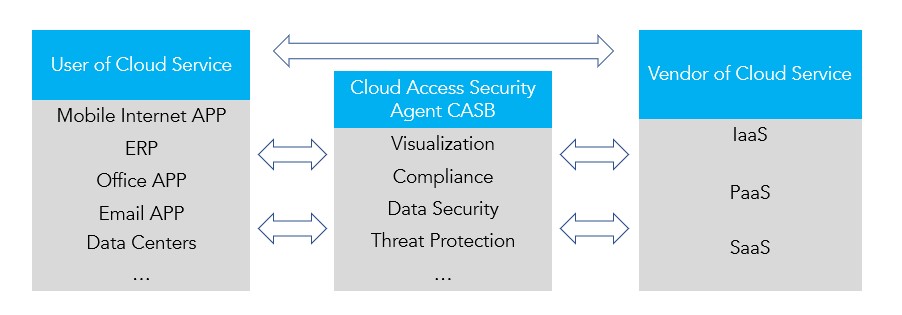
CASB (Cloud Access Security Broker) is an access control node between cloud service consumers (enterprises) and various types of cloud services, to achieve two-way control and protection of data traffic in between. The logical relationship is shown in the figure below.
As an emerging security technology, CASB was first put forward by Gartner in 2012 and has been adopted by cloud security vendors as a popular technology in recent years. In 2016, Gartner also defined CASB as the top information security technology, and in 2019 CASB managed to enter the global cybersecurity buzzword list published by RSA Conference of the year. Obviously, CASB has successfully made itself out and gained influence in the security industry, like a “celebrity†on the internet.
Being a “Celebrity†with Strengths
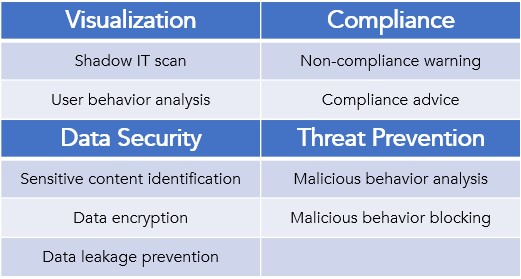
The four pillar functions that support CASB to become a tech-celebrity are: visualization, compliance, data security and threat protection, and the following are their breakdown functions.
First of all, CASB itself maintains a library of known cloud applications that are evaluated in terms of security risk, compliance, etc. Users can choose whether to adopt cloud application services based on its evaluation metric.
Visualization
Users are often unaware of their own cloud service usage platform while using it. CASB’s visualization function helps enterprises visualize who is using which cloud services internally, etc. to effectively detect shadow IT (unauthorized or even unknown use of IT resources); and enable warnings or blocking of risky applications based on built-in and configured policies.
Compliance
There are many compliance requirements in network security, and users’ online behavior needs to comply with regional and corporate codes of conduct. Compliance certification is an important way to improve network security capabilities, and CASB can help enterprises meet compliance requirements even after moving their network systems to the cloud, monitor and retrace operations, access, content, files, etc. of user and administrator, and automatically alert them when important events occur. CASB can also provide trust ratings, content monitoring, and audit logs for cloud service vendors, providing a basis for users to choose a cloud service platform.
Data Protection
With data as the core asset of an enterprise, its protection is a primary concern for both users and vendors. Cloud access security agents can combine multiple dimensions, such as staff, devices, content, and applications, to fully grasp the use and flow of data in the cloud environment and prevent data leakage from the cloud service vendor itself. For example, data is encrypted during the user input process, so that all data in the cloud stay encrypted and secure.
Threat Prevention
CASB monitors and finds malware on the cloud and defends against malware inside the cloud by establishing a threat intelligence database and monitoring cloud-end data and user resource status; it can also control user malicious behavior, such as illegal login.
CASB, as an emerging security capability, is regarded by Gartner as a standard security product like firewall in the future. NSFOCUS SASE is following the technology development trend and adding CASB function to SASE service. Stay tuned to learn more about security capabilities of NSFOCUS SASE.
Related Links:
SASE Popular Science Series: Understanding SD-WAN
SASE Popular Science Series: The Relationship Between SD-WAN and SASE
