4.4 Satan: Evolving Ransomware
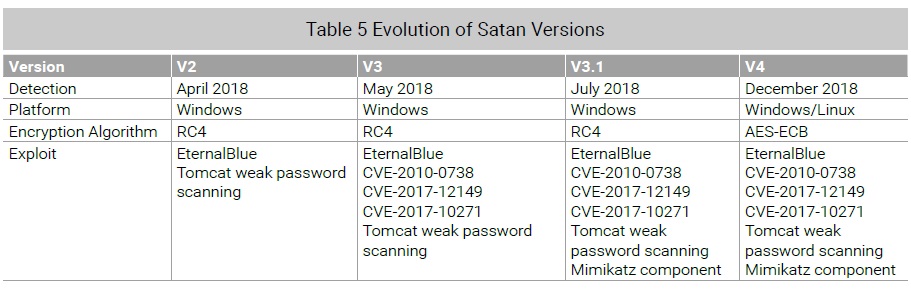
In late April 2018, MalwareHunterTeam reported seeing new ransomware that leveraged EternalBlue to propagate. Through analysis, we found that the ransomware was based on a new version (dubbed V2) of Satan, a ransomware family launched in 2017. The ransom demanded in this version increased from 0.1 to 0.3 Bitcoin. At the same time, a certain variant of IRCBOT also captured download instructions related to this malware. From the instruction set, Satan was confirmed to be the ransomware payload.
An analysis of the ransomware payload reveals that it RC4 is used for its encryption algorithm and stores keys locally. NSFOCUS Fuying Laboratory has developed and released a decryption tool to counter Satan.
At the end of May 2018, version 3 of Satan was released which exploited multiple web-related vulnerabilities, included weak password dictionaries, and added mimikatz as a payload to better exploit compromised devices. Mimikatz is a tool used gather credentials and then exploit vulnerabilities in authentication systems. This version of Satan is the same as V2 during the encryption and ransom stage. Therefore, no update was required to the NSFOCUS Satan decryption tool.
At the end of July 2018, a vendor reported a series of Satan infection events in China. Through analysis, we found that the ransomware had been upgraded to V3.1, with minor changes to its key storage policy. The new version generates random keys and then uploads them to the C&C server. If no network connection is available to the bot, V3.1 uses defaults to the original mechanism of directly writing keys to the end of encrypted files. Fuying Laboratory updated the decryption tool and provided a sample analysis report and remediation recommendations.
In mid-December 2018, NSFOCUS captured Satan V4, which runs on both Windows and Linux. V4 switches from the relatively weak R4 algorithm to the stronger AES-ECB algorithm. The encryption key is then written to the end of files only after being RSA-encrypted. As a result, to recover from this version, the victim must first decrypt the key, which can be found in running memory, and then decrypt the files. This process similar to that used by WanaKiwi developed by Adrien Guinet and Benjamin Delpy.
The following table shows the evolution of Satan.
Extortion remains one of the most lucrative ways of generating profit for hackers. Based on the evolution of the Satan family in 2018, we learned a great deal about the lifecycle of ransom botnets.
These ransomware families are very sophisticated in early versions but then evolve quickly amid the fierce battles between the offensive and defensive sides. This evolution into a more mature product is characterized by modularization and precise engineering, becoming a greater threat to users’ data security.
To be continued.