WebSphere Application Server High-Risk Remote Code Execution Vulnerability (CVE-2020-4450) Threat Alert

August 25, 2020
Overview
On June 5, Beijing time, IBM released a security bulletin to announce the fix of a high-risk remote code execution vulnerability (CVE-2020-4450) in WebSphere Application Server (WAS). This vulnerability was caused by deserialization of the Internet Inter-ORB Protocol (IIOP). It is assigned the CVSS base score of 9.8 and therefore is a high-risk one with an extensive impact.
(more…)Botnet Trend Report 2019-7

August 24, 2020
In 2019, ransomware was still a major type of threats that haunted people around the world. As an infamous botnet family, GandCrab generated more than USD 2 billion in ransom payments, simulating the rapid increase of other ransomware.
(more…)2019 Cybersecurity Insights -17

August 21, 2020
Threats Against WS-Discovery
WSD is a multicast discovery protocol to locate services on a local area network (LAN). However, due to device vendors’ design flaw in the implementation, when a normal IP address sends a service discovery packet, devices will also respond to the request. If exposed on the Internet, these devices will be possibly exploited for DDoS reflection attacks. In February 2019, security researchers 1 from Baidu published an article 2 about WSD reflection attacks. This is the first report we have read about such attacks. In a post 3 , ZDNet mentioned that WSD reflection attacks were first reported in May, and in August, many organizations began to use this protocol to launch DDoS attacks. According to Akamai, one of its customers in the gaming industry suffered a WSD reflection attack weighing in at 35 Gbps at peak bandwidth.
Around the world, about 910,000 IP addresses (80% (730,000) were video surveillance devices) provided the WSD service and were thus at risk of being exploited to launch DDoS attacks.
(more…)2019 Cybersecurity Insights -16

August 19, 2020
In this section, we analyzed threats against three major protocols.
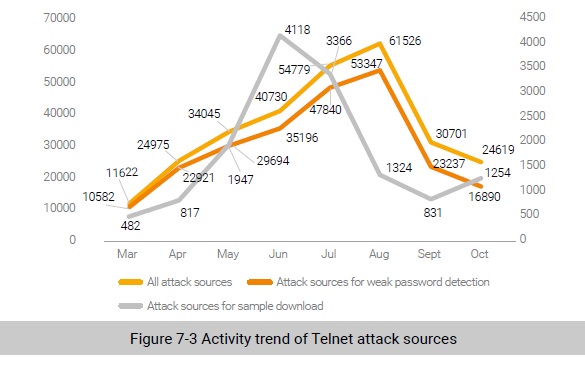
Threats Against Telnet
According to data from NSFOCUS’s threat hunting system, Telnet (available on port 23), targeted by a total of 120,000 attack sources, was the IoT protocol most favored by attackers1 . Figure 7-3 shows the activity trend of Telnet attack sources from March to October in 2019. We can see that the number of Telnet-based attacks increased month by month from March to August, with August seeing the most attack sources (over 60,000) that carried out more than 50,000 weak password detection activities. In addition, June witnessed the most sample download activities (more than 40,000). Overall, attack sources were on the decline in the latter half of 2019.
2020 Mid-Year DDoS Attack Landscape Report-1

August 18, 2020
Summary
- Global distribution of DDoS attacks: U.S. suffered the most DDoS attacks, and Japan received the largest volume of DDoS traffic.
- DDoS attack trend: March and April witnessed the most frequent DDoS attacks, and May saw the peak of attack traffic.
- DDoS attacks and COVID-19 pandemic: DDoS attacks fluctuated noticebly with the worldwide outbreak of the COVID-19 pandemic. Germany and the U.S. were two typical examples.
- Attack lethality: Compared with the first half of 2019, the first half of 2020 experienced a decline in the number of attacks withincreasing magnitute.
- Attack types: SYN flood and UDP flood remained dominant DDoS attacks.
- Attack duration: Short-duration and effective attacks were the norm, with 68% of the attacks lasting less than 5 minutes.
- Attack peak: May was exposed to the strongest attack, with the peak reaching 634.6 Gbps.
- Attack gangs: Among the 15 IP gangs under our continuous monitoring in the first half of 2020, the largest attack utilized 217,000 attack sources.
TP-Link Tapo C200 IP Camera High-Risk Vulnerability Threat Alert

August 18, 2020
Overview
Recently, TP-Link fixed a high-risk vulnerability in the C200 IP camera.
A user’s hashed password can be found in the memory dump by using the discovered Heartbleed vulnerability exposed on TCP port 443. The hash was then used for a pass-the-hash attack by exploiting the login process on the API. This caused a login token called “stok” to be issued, which could be used to authenticate to the device as the user.
Later, an attacker could perform authenticated operations, such as moving the camera’s motor, formatting the SD card, creating an RTSP account to view the camera’s video feed, and disabling the privacy mode.
(more…)Botnet Trend Report 2019-6

August 17, 2020
Overview of DDoS Attacks in 2019
According to the observation of NSFOCUS Security Labs, DDoS botnets in 2019, though with some changes, continued with the same patterns in attack targets, families, and operating platforms overall.
Among the track data of NSFOCUS Security Labs in 2019, there were more than 1.1 million instructions given by DDoS botnet families, 63% of which (over 700,000) were effective ones. According to the Labs’ metrics, these DDoS instructions resulted in over 400,000 attack events.
In terms of geographic locations, the USA was still the most targeted country, followed by China, the UK, and Australia.
(more…)Adobe Releases Updates to Fix High-Risk Vulnerabilities Threat Alert

August 14, 2020
Overview
On July 21, 2020, local time, Adobe released security updates to fix high-risk code execution vulnerabilities in its various products, including Adobe Bridge, Adobe Photoshop, Adobe Prelude, and Adobe Reader Mobile.
For details about the security bulletins and advisories, visit the following link: