Overview
In 2020 H1, a total of 1419 vulnerabilities were added to the NSFOCUS Vulnerability Database (NSVD), 714 of which were high-risk vulnerabilities. Among these high-risk vulnerabilities, 184 vulnerabilities were Microsoft-related ones. High-risk vulnerabilities were mainly distributed in major products of Microsoft, Oracle, Adobe, Google, Cisco, IBM, Moxa, Apache, and other vendors.
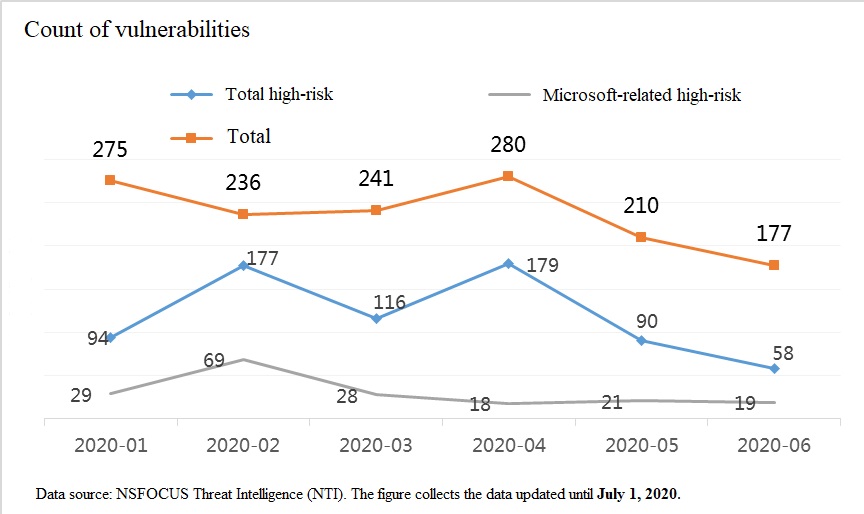
Figure 1-1 Number of new vulnerabilities included in NSVD in 2020 H1
Vulnerability Trend
Vulnerability Categories
714 new high-risk vulnerabilities included in NSVD in 2020 H1 are categorized into code execution, privilege escalation, component security vulnerability, memory corruption, use after free, information leakage, denial of service, product security vulnerability, buffer overflow, command injection, authentication bypass, and heap overflow. Vulnerability numbers are detailed as follows:
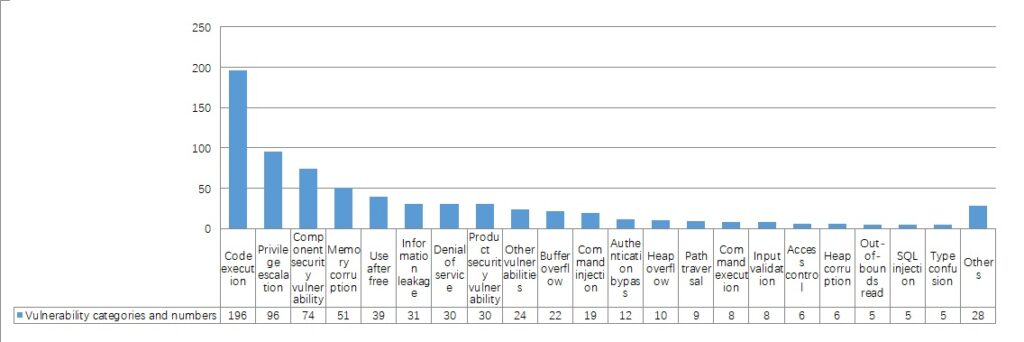
Figure 2-1 Categories and numbers of high-risk vulnerabilities
Vulnerability Distribution
714 high-risk vulnerabilities were mainly distributed in major products of 80 vendors, including Microsoft, Oracle, Adobe, Google, Cisco, IBM, Moxa, and Apache. Details are as follows:
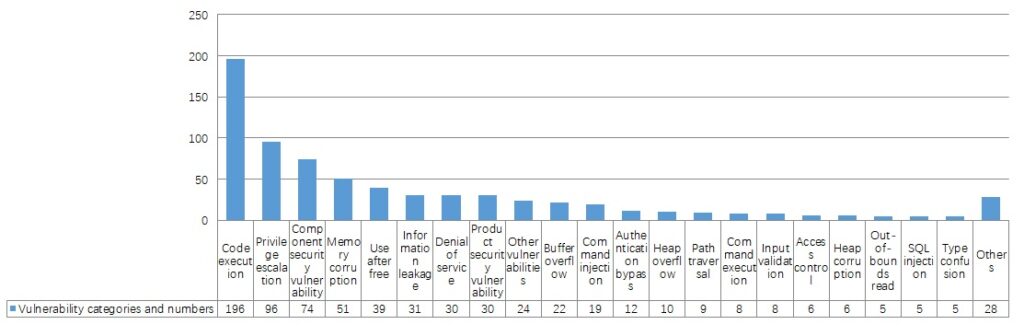
Figure 2-2 Number of high-risk vulnerabilities
184 high-risk vulnerabilities of Microsoft were mainly distributed in widely used products, such as Microsoft Windows, Win32k, Microsoft Edge, ChakraCore, Internet Explorer, SharePoint Server, Microsoft Office, Server Message Block 3.1.1 (SMBv3), Windows Search Indexer, Jet Database Engine, .NET Framework, Media Foundation, and Azure DevOps Server. These vulnerabilities involve memory corruption, privilege escalation, and remote code execution.
136 Oracle vulnerabilities were mainly distributed in components of such products as database servers, application servers, collaboration suites, and e-commerce suites. The WebLogic deserialization vulnerability has drawn much attention from the industry.
131 Adobe vulnerabilities were mainly distributed in Adobe Acrobat, Adobe Reader, Adobe Illustrator, Adobe ColdFusion, Adobe Photoshop, Adobe Bridge, Adobe Framemaker, and Adobe Flash Player.
38 Google vulnerabilities were mainly distributed in Google Chrome Brower and Google Cloud Platform. 26 Cisco vulnerabilities were distributed in Cisco Data Center Network Manager, Cisco FXOS (firewall software), and Cisco UCS Manager Software.
Typical Vulnerabilities
- Oracle WebLogic Server Application Container – JavaEE component vulnerability
CVE-2020-2546
NSFOCUS ID: 45702
Affected versions:
Oracle Fusion Middleware 10.3.6.0.0
Oracle Fusion Middleware 12.1.3.0
Vulnerability description:
Oracle Fusion Middleware is a business creativity platform for enterprises and cloud environments. A vulnerability in Oracle WebLogic Server Application Container – JavaEE component allows unauthenticated attackers to remotely execute commands via the T3 protocol, which is enabled by default to take over Oracle WebLogic Server, thus affecting the confidentiality, integrity, and availability of the component. The vulnerability can be triggered under the default configuration of Oracle WebLogic Server, with no need for administrator authentication and additional interaction.
- Google Chrome V8 type confusion vulnerability
CVE-2020-6814
NSFOCUS ID: 45988
Affected versions:
Google Chrome < 80.0.3987.122
Vulnerability description:
V8 is an open-source JavaScript and WebAssembly engine of Google and is used in Chrome. A type confusion vulnerability in V8 implementation in Google Chrome < 80.0.3987.122 might allow attackers to gain unauthorized access to data, thereby incurring the risk of malicious code execution.
- Apache Kylin remote command execution vulnerability
CVE-2020-1956
NSFOCUS ID: 46860
Affected versions:
Apache Group Kylin 2.3.0 – 2.3.2
Apache Group Kylin 2.4.0 – 2.4.1
Apache Group Kylin 2.5.0 – 2.5.2
Apache Group Kylin 2.6.0 – 2.6.5
Apache Group Kylin 3.0.0 – 3.0.1
Apache Group Kylin 3.0.0-alpha
Apache Group Kylin 3.0.0-alpha2
Apache Group Kylin 3.0.0-beta
Vulnerability description:
Apache Kylin is an open-source distributed analytical data warehouse from Apache Software Foundation (ASF). It is designed to provide online analytical processing (OLAP) capability of SQL interface and multidimensional analysis on Hadoop/Spark to support extremely large datasets. Apache Kylin has some RESTful APIs that will associate OS commands with user-typed strings. As Apache Kylin fails to properly verify user input, an attacker could execute arbitrary system commands without authorization.
- IBM WebSphere Application Server remote code execution vulnerability
CVE-2020-4450
NSFOCUS ID: 46867
Affected versions
IBM Websphere Application Server 8.5.x
IBM Websphere Application Server 9.0.x
Vulnerability description:
WebSphere Application Server (WAS) 9.0.x and 8.5.x are prone to a deserialization vulnerability in the handling of the Internet Inter-ORB Protocol (IIOP). By exploiting this vulnerability, an unauthenticated attacker could remotely target the WAS server via IIOP to execute arbitrary code on the target server and gain system privileges, thereby taking control of the server. As WAS enables IIOP by default, attackers could launch remote attacks without authentication. Therefore, this high-risk vulnerability has an extensive impact.
- Apache Dubbo Provider default deserialization remote code execution vulnerability
CVE-2020-1948
NSFOCUS ID: 46973
Affected versions
Apache Dubbo 2.6.0 <= Dubbo Version <= 2.6.
Apache Dubbo 2.7.0 <= Dubbo Version <= 2.7.
Apache Dubbo Dubbo <= 2.5.0
Unaffected versions
Apache Dubbo Dubbo >= 2.7.7
Vulnerability description:
On June 23, 2020, Apache Dubbo released a security bulletin to disclose the remote code execution vulnerability (CVE-2020-1948) caused by the default deserialization of the Provider. An attacker could send RPC requests with a payload of an unrecognized service name or method name and certain malicious parameters. Deserialization of malicious parameters will cause code execution.
Common Exploit Trends
Of all exploits monitored by NTI from January to June 2020, Top 10 vulnerabilities with standard CVE IDs are listed in Table 2-1. NTP ntpd monlist query reflection denial-of-service vulnerability (CVE-2013-5211) was most frequently alerted with a number of 3,698,545. In terms of the vulnerability type, denial-of-service and remote code execution vulnerabilities were dominant.
Table 2-1 Top 10 alerted exploits
| Vulnerability Title | Alert Count |
| NTP ntpd monlist Query Reflection Denial-of-Service Vulnerability (CVE-2013-5211) | 3,698,545 |
| OpenSSl SSLv2 Weak Encryption Communication Method Prone to DROWN Attack (CVE-2016-0800) | 1,758,556 |
| PowerDNS Authoritative Server DNS TKEY Unknown Record Denial-of-Service Vulnerability (CVE-2015-5311) | 1,736,565 |
| Windows SMB Remote Code Execution Vulnerability (Shadow Brokers EternalBlue) (CVE-2017-0144) (MS17-010) | 963,744 |
| GNU Bash Environment Variables Remote Command Execution Vulnerability (CVE-2014-6271) | 621,394 |
| Struts 2 Remote Command Execution Vulnerability (S2-045/S2-046) (CVE-2017-5638) | 607,482 |
| Apache Struts 2 Remote Code Execution Vulnerability (CVE-2013-2251) | 211,906 |
| Pivotal Spring Framework isWritableProperty SpEL Expression Injection Vulnerability (CVE-2018-1273) | 210,084 |
| Apache Tomcat Remote Code Execution Vulnerability (CVE-2017-12615) | 182,967 |
| Oracle WebLogic wls9-async Component Deserialization Remote Command Execution Vulnerabilities (CVE-2019-2725/CVE-2019-2729) | 171,787 |
Top 10 alerts listed in Table 2-2 are mainly related to protocols, databases, and common services. In terms of protocols, Windows SMB most frequently occurred in exploit alerts. In 2020 H1, NSFOCUS detected 96,622,650 Windows SMB login attempts and 70,019,527 successful authentications of Windows SMB protocol users. According to Table 2-1, 963,744 attacks were launched by exploiting the MS 17-010 EternalBlue vulnerability.
Table 2-2 Top 10 alerts
| Alert Information | Alert Count |
| Windows SMB login attempt | 96,622,650 |
| SSH login request authentication | 81,149,871 |
| Successful authentication of Windows SMB protocol users | 70,019,527 |
| Suspicious remote SQL injection attacks on web services | 55,331,911 |
| MS SQL Database users fail to log in to SQL servers | 54,119,971 |
| Authentication of anonymous users of FTP services | 51,706,609 |
| Weak password authentication of FTP service users | 42,173,196 |
| Successful authentication of users for POP3 service login | 31,742,655 |
| Remote cross-site scripting execution attacks on web services | 29,547,180 |
| HTTP basic authentication | 28,938,696 |
