Vulnerability Description
On December 2, 2019, Cisco Talos publicly released reports of a remote code execution vulnerability (CVE-2019-5096) and a denial of service vulnerability (CVE-2019-5097) for the GoAhead web server. GoAhead is an open source, simple, lightweight, and powerful embedded Web Server. It is a Web server tailored for embedded real-time operating systems (RTOS) and can run on multiple platforms.
CVE-2019-5096: Some versions of GoAhead Web Server have a remote code execution vulnerability when processing multipart / form-data requests. CVE-2019-5097: Some versions of GoAhead Web Server have a denial of service vulnerability when processing multipart / form-data requests. An attacker constructing a malicious HTTP request may cause the server process to enter an infinite loop. In the case of authentication, it is sent as GET or POST, and the requested resource is not required on the target server.
Reference:
https://talosintelligence.com/vulnerability_reports/TALOS-2019-0888
https://talosintelligence.com/vulnerability_reports/TALOS-2019-0889
Scope of Impact
Affected Versions
- GoAhead Web Server 5.0.1
- GoAhead Web Server 4.1.1
- GoAhead Web Server 3.6.5
Unaffected Versions
- GoAhead Web Server 5.1.0
Vulnerability Detection
Manual Detection
Use the following command to view the Gohead Web Server version currently used:
| ./goahead –version |
Version screenshot:
It is risky if the version affected.
Mitigations
Official Upgrade
At present, the vulnerability has been fixed in the latest 5.1.0 version. The affected users are recommended to upgrade the version as soon as possible. The official download link: https://www.embedthis.com/goahead/download.html
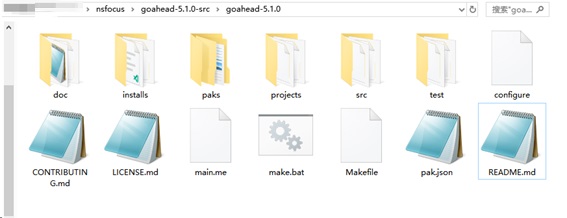
The steps are as follows:
First, make a backup of the website. Go to the link above to download the package that has been fixed. After decompression, enter the program directory. The directory structure is as follows:
Execute the following commands in sequence in the current directory:
| ./configure
make sudo make install |
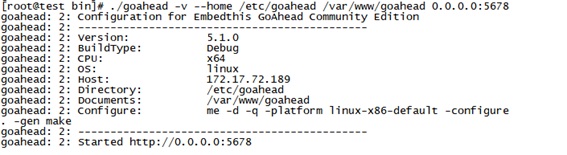
Deploy the backed up website to the website directory, such as: / var / www / goahead. Go to the / build / linux-x64-default / bin directory and use the following command to start the new version of GoAhead Web Server:
| ./goahead -v –home /etc/goahead /var/www/goahead 0.0.0.0:8888 |
Successful startup screenshot:
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.