In 2026, AI agents are being widely used. OpenClaw has become a high-frequency efficiency improvement tool for enterprises and developers with its autonomous decision-making and local execution capabilities. However, several authoritative security agencies have recently issued warnings: OpenClaw is facing multi-dimensional security threats from supply chain poisoning to remote control.
When internal employees privately deploy such “shadow AI” assets, and some malicious Skills (plug-ins) have unauthorized theft of core data, traditional border security lines are facing the risk of failure. In response to this situation, NSFOCUS has combined recent actual combat attacks and defenses with sample analysis and judgment, and based on the deep threat intelligence system, it has output three core capability matrices: OpenClawAI supply chain intelligence, OpenClaw compromise intelligence, and OpenClaw phishing intelligence, providing practical support for enterprises to deal with new AI threats by “knowing their source, following their traces, and breaking their chains”.
Risk 1: “AI supply chain poisoning” under the lack of ecological audit
OpenClaw’s scalability is highly dependent on its open Skills ecosystem (such as ClawHub). Monitoring found that due to the lack of a strict code security review mechanism on third-party platforms, attackers can easily implant backdoor plug-ins, resulting in frequent AI supply chain poisoning incidents.
As early as February this year, NSFOCUS Tianyuan Lab issued an early warning report on the risks of malicious Skills on the ClawHub platform:
Continuous tracking shows that although OpenClaw has officially announced the implementation of security governance, as of now, there are still a large number of high-risk plug-ins surviving, and non-technical employees who lack identification capabilities are very likely to inadvertently introduce risks.
Know the Source: OpenClaw AI Supply Chain Intelligence
NSFOCUS relies on a global sample monitoring network to continuously conduct dynamic cleaning and in-depth behavioral analysis of Skills in the mainstream market. At present, NSFOCUS Intelligence has realized the real-time output of high-risk Skills Blacklist (covering key stealing, remote control backdoors and other categories), and sorted out a “Trusted Skills Library” that has been verified for security for enterprises. Enterprises can use this to establish a risk assessment mechanism on the plug-in installation side, cutting off the poisoning path of the AI supply chain from the source.
Risk 2: “Compromise” after the abuse of AI execution capabilities
Once a malicious skill is triggered or the underlying vulnerability is exploited, an OpenClaw instance is declared compromised. Attackers can use the high authority of AI tools to silently execute system commands, steal browser credentials, and even use them as a springboard to launch horizontal penetration into the intranet.
Follow the Traces: OpenClaw Compromise Intelligence
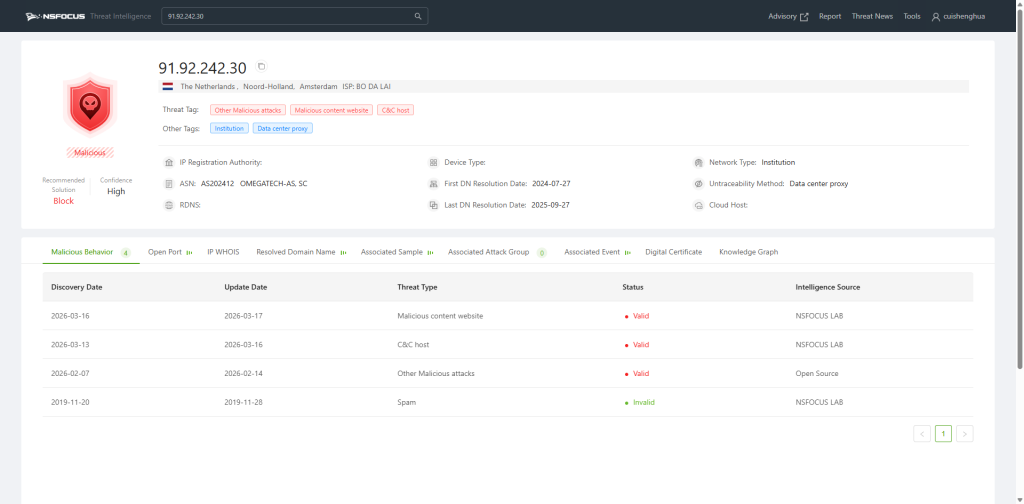
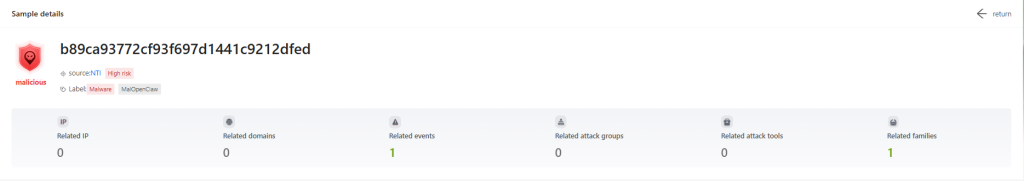
For such high-dimensional attacks, NSFOCUS threat intelligence has extracted and covered high-quality IOCs. At the EDR level, it accurately locates the disk hash of malicious Skills files; at the NDR level, it directly hits the abnormal traffic characteristics of the compromised host actively connecting to the black production C2.
In addition, the research team innovatively incorporated “AI abnormal behavior fingerprints” into the intelligence rule base, and NSFOCUS threat intelligence can be quickly synchronized to local devices through the cloud. When illegal external connections or abnormal process calls occur in the intranet, rapid alarms can be implemented and the source of the compromised host can be traced to eliminate the hidden risks of “shadow AI”.
Risk 3: Induced downloads and phishing attacks
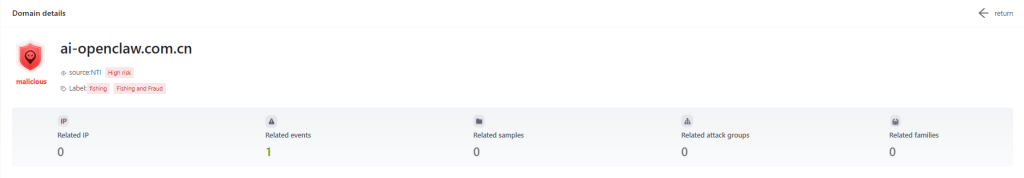
Recent monitoring data shows that black industry gangs are taking advantage of the popularity of OpenClaw to build a large-scale phishing network. Attackers target ordinary business personnel, use SEO to accurately launch high-imitation phishing websites, and trick employees into downloading fake versions of clients bundled with Trojan programs to carry out watering hole attacks.
Break the Chain: OpenClaw Phishing Intelligence
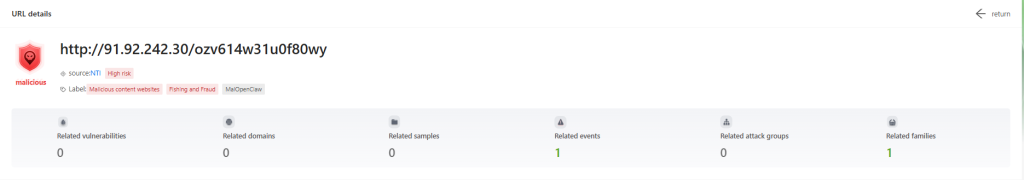
NSFOCUS continues to monitor digital assets and phishing sources involving OpenClaw on the entire network, mapping counterfeit sites and extracting threat intelligence as soon as possible. By linking enterprise border protection equipment, such counterfeit websites are directly identified and blocked on the gateway side to cut off the phishing attack chain.
Building a guardrail for AI applications
The popularity of OpenClaw is inevitable for the development of technology, but its vague trust boundary mechanism is very easy to exploit. At a time when “development and safety are equally important”, facing the “lobster” craze, companies need to focus on their associated security blind spots while enjoying efficiency improvements. The three special intelligence output by NSFOCUS aims to provide full life cycle defense data support for enterprises to deal with AI intelligent agent threats. By accurately identifying risks, extracting high-fidelity IOC and source risk control, a security guardrail is built for the company’s AI applications.