Background
According to the monitoring data from NSFOCUS Fuying Lab, since the outbreak of domestic conflict in Iran in January 2026 and the subsequent escalation of tensions over the nuclear issue between the U.S. and Iran, Iran has been continuously subjected to DDoS attacks. The attack methods have shown diverse characteristics, including both botnet-based attacks and reflection amplification attacks. 259 IP addresses in Iran have been targeted, including 15 national government units, 4 national news units, 4 national network infrastructure facilities, and 12 other institutional websites.
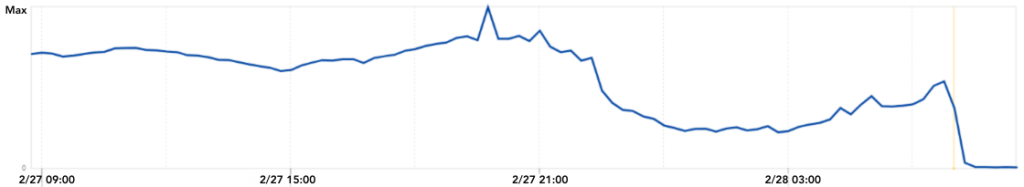
During the period when this article was written, conflicts erupted, and both the U.S. and Israel took military action against Iran. Subsequently, Iran implemented network control measures. Due to the continuous DDoS attacks Iran had suffered earlier, after the breakdown of negotiations, fearing cyberattacks during the conflict, Iran shut down its networks.
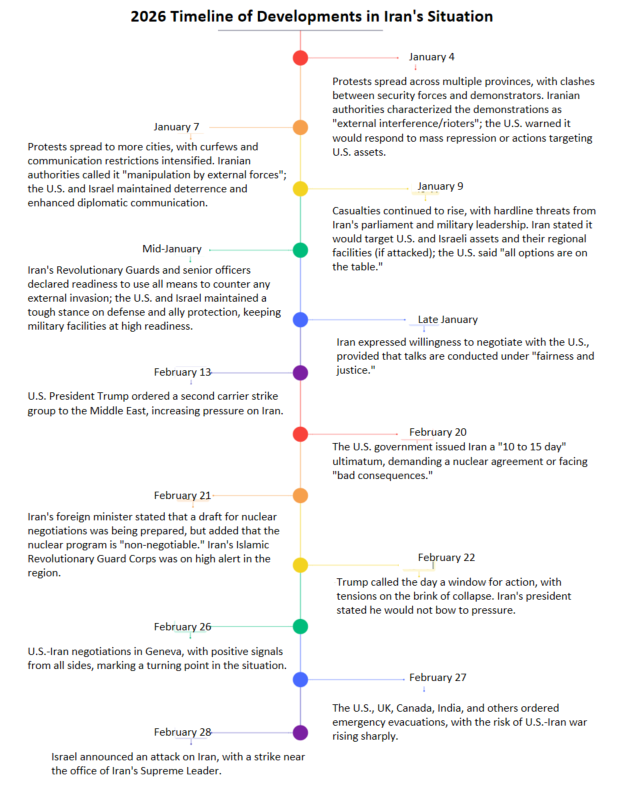
Starting from January 4th, protests erupted in multiple provinces of Iran, leading to conflicts. The government attributed the unrest to “external interference or hooliganism,” and the U.S. issued warnings. The protests escalated into violent crackdowns, resulting in casualties and heightened social tensions, accompanied by a synchronous increase in DDoS attacks. From February 20th, the standoff between the U.S. and Iran continued, with diplomatic and military tensions nearing a critical point, and DDoS attacks resurged. On February 26th, negotiations brought temporary easing, but evacuation of nationals and troop reinforcement actions kept tensions high. At 14:00 on February 28th, Israel announced strikes on Iran, escalating the U.S.-Iran conflict, which led to a further surge in DDoS attacks, prompting Iran to respond by shutting down its internet 1.
Overall, there is a significant correlation between the U.S.-Iran situation and DDoS attack activities. Escalations in real-world tensions often directly drive an increase in cyberattacks. Conversely, fluctuations in cyberattack activities can serve as a reference signal for assessing changes in regional security dynamics. Overall, the relevant DDoS attack activities exhibit clear event-driven characteristics, reflecting a high degree of interconnection between the real world and cyberspace.
Attack Overview
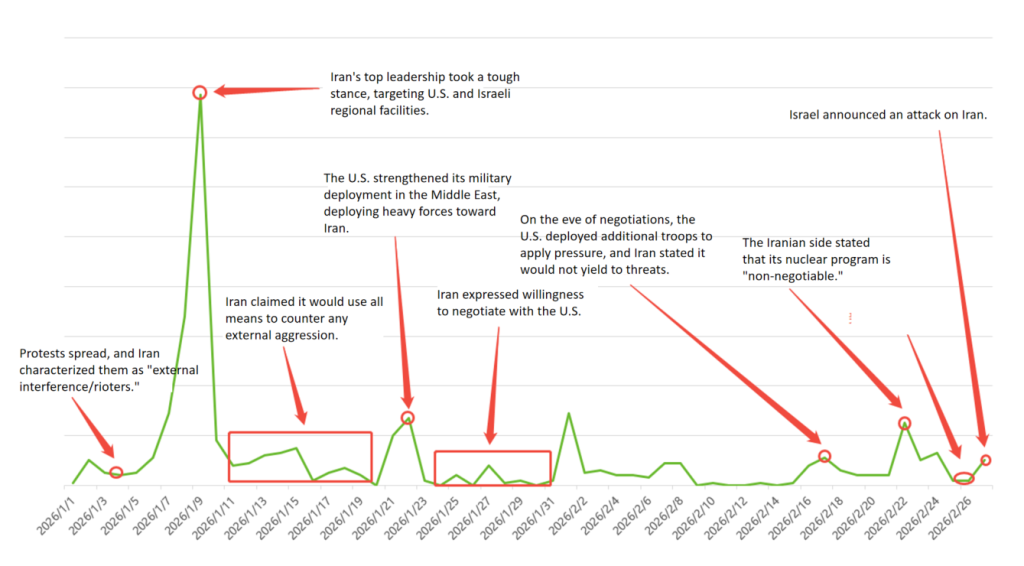
According to monitoring data from NSFOCUS Fuying Lab, since the outbreak of conflicts in multiple provinces of Iran on January 4, the country’s security situation has remained unstable. Correspondingly, DDoS attack activities targeting Iran have occurred frequently, highly synchronizing with real-world situation.
From the data changes in the graph below, there is a notable correlation between real-world events and DDoS attacks:
- Early January: As the situation in Iran gradually escalated, the scale of DDoS attacks generally increased. When Iran designated facilities in the U.S. and Israel regions as key targets, DDoS attack activities reached their peak.
- Mid-to-late January: The real-world situation and Iran’s network restrictions jointly influenced attack trends. In mid-January, Iran publicly stated it would take all measures to counter external interference, which further intensified tensions. Although DDoS attack activities slightly declined, they still remained high. By late January, after Iran signaled its willingness to resolve issues through negotiations, the intensity of attacks significantly decreased, showing a synchronized de-escalation trend.
- From February 1 to 20, the situation in Iran remained relatively stable. Monitoring data showed that DDoS attack activities stayed low, with no significant large-scale attacks. However, after February 21, when Iran again adopted a hardline stance and emphasized that its nuclear program was non-negotiable, DDoS attack activities began to rise once more.
- On February 26, negotiations between the U.S. and Iran began, temporarily easing tensions, and DDoS attack activities also declined accordingly. But on February 27, the USS Gerald R. Ford Aircraft Carrier arrived in Israel, further strengthening regional military deployments. Then, on February 28, Israel announced strikes against Iran, causing regional security risks to escalate. Corresponding to these real-world developments, DDoS attack activities in cyberspace surged again.
Attack Targets
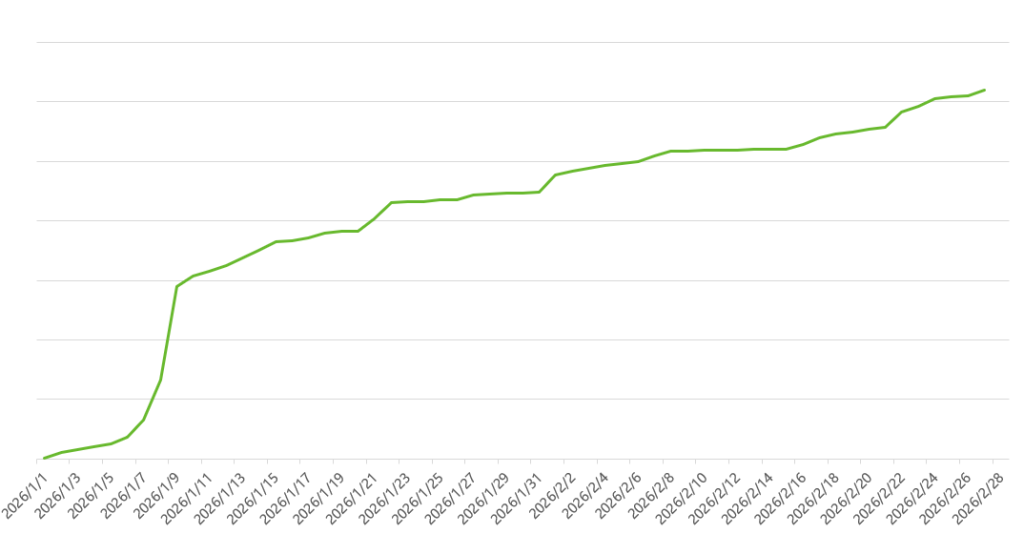
Since January 4, 2026, monitoring has revealed that 259 Iranian domestic IP addresses have been targeted by DDoS attacks. Among these, 23 were critical national targets, including news websites, educational sites, and government platforms, while 12 other organizations were also affected. The targeted entities can be categorized as follows:
- Government Agencies: 15 (e.g., Iran’s official VAT website DNS service ns2.vat.ir, an authoritative domain name server in Iran’s internet infrastructure ns1.valinet.ir, etc.)
- State-Owned Media: 4 (e.g., the official media portal of Iran’s Supreme Leader khamenei.ir, the prominent news website www.tabnak.ir, etc.)
- National Network Infrastructure: 4 (e.g., Iran’s national domain Registration authority IRNIC, authoritative domain name server ns1.valinet.ir, etc.)
- Civilian Institutions and Organizations: 12 (e.g., mobile advertising platforms, etc.)
According to the growth trend, the most significant spike in attacks on Iranian targets occurred on January 9, coinciding with large-scale protests in the capital and multiple regions—the strongest collective action against theocratic rule in recent years. Authorities responded with a heavy crackdown. Afterward, the growth trend slowed, primarily due to shifting tensions between the parties involved and Iran’s internet shutdown measures.
Attacks on the Supreme Leader’s Official Website
From January 29 to February 10, 2026 (GMT+8), monitoring data revealed that the official website of Iran’s Supreme Leader (khamenei.ir) faced multiple waves of cyberattacks. These attacks were launched by the Mirai botnet and its variants, with over 100 attack commands issued during this period. The primary method used was UDP Flood, targeting ports 80 and 443 with high-volume traffic assaults. Each attack command lasted approximately 1 minute, accumulating a total attack duration of over 100 minutes. Key attack incidents include:
- January 29, 2026, 16:50:11 (GMT+8): UDP Flood attack targeting port 443.
- January 31, 2026, 15:30:03 (GMT+8): UDP Flood attack targeting port 443.
- February 1, 2026, 05:20:35 (GMT+8): UDP Flood attack targeting port 443.
- February 2, 2026, 17:11:20 (GMT+8): UDP Flood attack targeting port 1000.
- February 6, 2026, 09:52:16 (GMT+8): UDP Flood attack targeting port 80.
- February 10, 2026, 18:17:03 (GMT+8): UDP Flood attack targeting port 80.
The official website of Iran’s Supreme Leader, khamenei.ir, serves as the primary media portal for Ayatollah Seyyed Ali Khamenei. Operated by the ” Office for the Preservation and Publication of the Works of the Grand Ayatollah Sayyid Ali Khamenei”, it is the authoritative source for information about Iran’s highest government body.
The DDoS attacks on this website represent a deliberate disruption of Iran’s core channel for authoritative information. These attacks aim to temporarily block the release and public access to official information, creating an information vacuum that facilitates the spread of misinformation. Symbolically, they also challenge Iran’s national authority and cyber defense capabilities, disrupting both domestic and international information dissemination and public opinion guidance. This constitutes a cyber pressure tactic with clear political intent.
Attacks on Iran’s Tabnak News Website
On February 4, 2026 (GMT+8), NSFOCUS detected a DDoS attack on the Iranian news website www.tabnak.ir. The attack was launched by a new variant of the Mirai botnet. Details of the attack are as follows:
- February 4, 2026, 21:55:00 (GMT+8): UDP Flood attack targeting port 80.
Tabnak is a prominent Iranian news and analysis website established in 2009, primarily serving Persian-speaking audiences. It provides in-depth coverage of politics, economics, society, culture, and international affairs, with a focus on major domestic and global issues, including multilateral cooperation mechanisms like the BRICS. Tabnak is one of the most visited and influential Persian-language media platforms.
The DDoS attack on Tabnak not only caused slow response times or temporary inaccessibility but also directly disrupted the efficiency and continuity of public access to information. As a leading comprehensive news platform in Iran, the disruption of Tabnak interferes with the normal flow of information, undermining the timely and stable delivery of critical news to its audience. In the current complex regional and international landscape, such attacks destabilize the public opinion space, posing potential threats to the stable operation of the information ecosystem and introducing uncertainty into the media environment.
Attacks on the Official Website of Varzaneh City, Iran
On February 10, 2026 (GMT+8), monitoring detected a DDoS attack on the official website of Varzaneh City, Iran (varzaneh.ir). Details of the attack are as follows:
- February 10, 2026, 13:37:05 (GMT+8): Attack targeting port 443 using NTP reflection.
Varzaneh is an ancient town in Iran with a history of approximately 5,000 years, located in Isfahan Province. It is renowned for its unique traditional culture and natural landscapes. The city’s official website publishes content such as city maps, municipal project updates, government announcements, and local news, serving as a vital channel for the public to access authoritative government information and stay informed about urban developments.
The DDoS attack on this website directly impacts the public’s ability to access information, delaying or preventing the timely dissemination of government announcements, public service updates, and urban management news, thereby affecting the government’s reputation.
Attacks on Sharif University of Technology
On February 15, 2026 (GMT+8), monitoring detected a DDoS attack on the official website of Sharif University of Technology (sharif.ac.ir). Details of the attack are as follows:
- February 15, 2026, 16:22:04 (GMT+8): Attack targeting port 443 using NTP reflection.
Sharif University of Technology is a leading public research university in Iran, often referred to as the “MIT of Iran” due to its excellence in engineering and physical sciences. Founded in 1966, the university comprises multiple schools, including engineering, computer science, physics, chemistry, mathematics, and management. It is particularly renowned for its strengths in electrical engineering, mechanical engineering, and computer science. Known for its rigorous admission standards, Sharif University attracts top students nationwide and produces influential research, making it a key institution in Iran’s scientific and technological development. It plays a vital role in cultivating high-level engineering, technical, and research talent for the country.
DDoS attacks on this website disrupted teaching, research activities, and external communications, making it difficult for the public to access timely information about admissions, research achievements, and university updates. This negatively impacts the university’s image and reputation.
Attacks on Iran’s National Smart Government Services Portal
On February 20, 2026 (GMT+8), monitoring detected a DDoS attack on Iran’s National Smart Government Services Portal (my.gov.ir). Details of the attack are as follows:
- February 20, 2026, 06:42:15 (GMT+8): Attack targeting port 443 using CLDAP reflection.
Iran’s National Smart Government Services Portal (a unified e-government service platform) is an integrated online portal established by the Iranian government to provide citizens and businesses with convenient, digital government services. Through this platform, users can access a wide range of online services such as tax filings, social security, healthcare, education, and administrative approvals using a single account. The portal consolidates online government service resources, enhancing transparency and efficiency while reducing the time and cost associated with traditional processes.
A DDoS attack on this website not only disrupts the access for citizens and enterprises to essential government services but also risks undermining public trust in the platform.
Attacks on the Website of the Islamic Republic News Agency (IRNA)
Since February 7, 2026 (GMT+8), multiple DDoS attacks have been detected targeting the website of the Islamic Republic News Agency (IRNA) (www.irna.ir). Details of the attacks are as follows:
- February 7, 2026, 00:39:31 (GMT+8): Attack targeting port 443 using NTP reflection.
- February 15, 2026, 06:43:26 (GMT+8): Attack targeting port 80 using SLP reflection.
- February 22, 2026, 01:16:45 (GMT+8): Attack targeting random high ports (6083, 37303, etc.) using NTP reflection.
- February 24, 2026, 04:45:23 (GMT+8): Attack targeting port 80 using SLP reflection.
The Islamic Republic News Agency (IRNA) is one of Iran’s official news agencies, originally established in 1934 as the Pars News Agency and renamed after the 1979 Islamic Revolution. Headquartered in Tehran and affiliated with the Ministry of Culture and Islamic Guidance, IRNA serves as the Iranian government’s primary platform for releasing authoritative domestic and international news, policies, and social updates.
When this website is targeted by DDoS attacks, it can lead to delays in information dissemination and restricted access, hindering the public’s ability to efficiently obtain official news and policy interpretations.
Key Insights from the Events
From the escalating tensions between the U.S. and Iran, phenomena such as network anomalies, communication disruptions, and traffic surges reveal that DDoS attacks have evolved beyond mere “cyber nuisances” into a digital vanguard and strategic signal in geopolitical conflicts. They often precede traditional military actions, serving as tools for probing, pressuring, and shaping the conflict environment.
DDoS has become a low-cost, high-certainty political-military tool. Among various cyberattack methods, it has the lowest technical barrier and the most flexible organizational structure, yet it can produce significant effects in a short time—network outages, paralysis of critical services, and the spread of social anxiety. For this reason, DDoS is often prioritized in the lead-up to conflicts, used to rapidly amplify confrontational postures without immediately incurring high military or political costs.
Cyberspace is becoming a critical lever influencing the physical world. By continuously disrupting networks and information systems—causing power outages, internet blackouts, and communication failures, DDoS attacks effectively destabilize the normal functioning of society. The impact does not stem from the technical sophistication of the attack but rather from the inadequate resilience, redundancy, and sustained countermeasures of the targeted network systems, making them vulnerable to prolonged pressure.
Internet shutdowns serve as direct proof of DDoS effectiveness. When a country chooses to actively or passively restrict network connectivity during a crisis, it signals that cyberattacks have already achieved strategic-level influence. DDoS does not need to destroy systems outright; it only needs to create persistent instability to force opponents into extreme defensive measures—measures that often end up undermining social efficiency and information transparency.
From a temporal perspective, DDoS attacks are most active “before the real war begins.” Monitoring data from multiple sources indicates that cyberspace is at its noisiest before physical conflicts erupt. Its core value lies in shaping the pre-war environment, disrupting judgment, and creating uncertainty, rather than replacing physical warfare itself.
In summary, in modern conflicts, DDoS attacks are no longer just a prelude to war but an integral part of warfare itself; they are no longer merely technical actions but a strategic language with clear intent. Those who can decipher the political motives behind traffic surges may gain an early advantage in predicting the trajectory of conflicts.
When the internet falls silent, it is often not a sign of peace arriving but an indication that more intense confrontation is drawing near.
Reference
[1] https://radar.cloudflare.com/traffic/ir?dateRange=1d
About NSFOCUS Fuying Lab
NSFOCUS Fuying Lab specializes in research on security threat monitoring and countermeasure technologies, covering areas such as advanced persistent threats (APT), botnets, DDoS defense, exploitation of popular service vulnerabilities, threats from black and gray industry chains, and emerging fields like digital assets.
The research objectives of the laboratory are to gain a comprehensive understanding of existing cyber threats, identify and track new and evolving threats, accurately trace and counter these threats, and minimize their risk impact. By doing so, the laboratory aims to provide robust decision-making support for effective threat mitigation and response.
By adopting a research model that combines cutting-edge technical exploration with practical, real-world countermeasures, the Fuying Lab has assisted national agencies in solving multiple APT attack cases. It has been a global pioneer in discovering 8 new APT attack organizations and has handled over 40 APT attack incidents targeting domestic entities. These efforts have made significant contributions to safeguarding national cybersecurity.