I. Abstract In September 2023, NSFOCUS global threat hunting system monitored several new botnet variant families developed based on Mirai, among which hailBot, kiraiBot and catDDoS are the most active, are accelerating their spread, and are widely deployed, which has constituted a considerable threat. Through this article, we will disclose...
Tag: DDoS attack
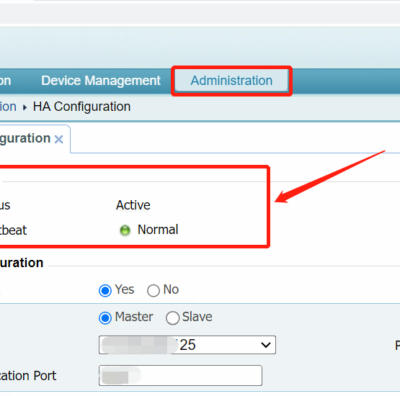
Feature Adaptations on Slave ADSM in a High Availability Environment
Sometimes, to ensure continuous business operations in the event of equipment failure, it is a common practice to configure High Availability (HA) using two ADSM devices. You can configure High Availability (HA) in ADSM by navigating to Administration > Local Settings > HA Configuration. Master: Slave: The master handles all...
Turmoil in Libya: Major Industries Hit by Massive DDoS Attacks
I. Background In August, NSFOCUS Global Threat Hunting System spotted an abnormal trend of DDoS attacks against Libya. NSFOCUS Security Labs sorted out the traffic changes of DDoS attacks in August and found that this attack may be related to the turmoil in Libya in August by comparing it with...
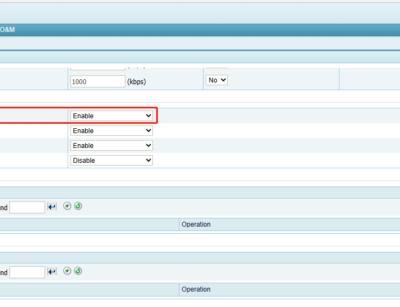
Introduction to ADS’s HTTP Keyword Checking Policy
HTTP Keyword Checking is a process by which ADS controls HTTP traffic through the ADS device. In addition, ADS takes a specific action (Accept, Drop, Disconnect, Add to blacklist, Add to whitelist, or Limit rate) as configured on passing packets whose source IP address and specific fields match the HTTP...
“Save” and “Apply” Buttons on ADS Configuration Page
When working with the ADS, it is important to understand the role of the "Apply " and "Save" buttons located in the upper-right corner of the configuration pages. Apply: Clicking the “Apply†button will apply and enforce the configuration changes, making them effective in the RAM of the ADS. These...
Description of ADS Attack Logs: SYN Flood Logs (Part 1)
Introduction to SYN Flood A three-way handshake is required to establish a TCP connection. First, the client sends a TCP SYN packet to the server. The server responds to the client request with an SYN-ACK packet. Then the server waits and expects an ACK packet from the client. At this...