I. Background
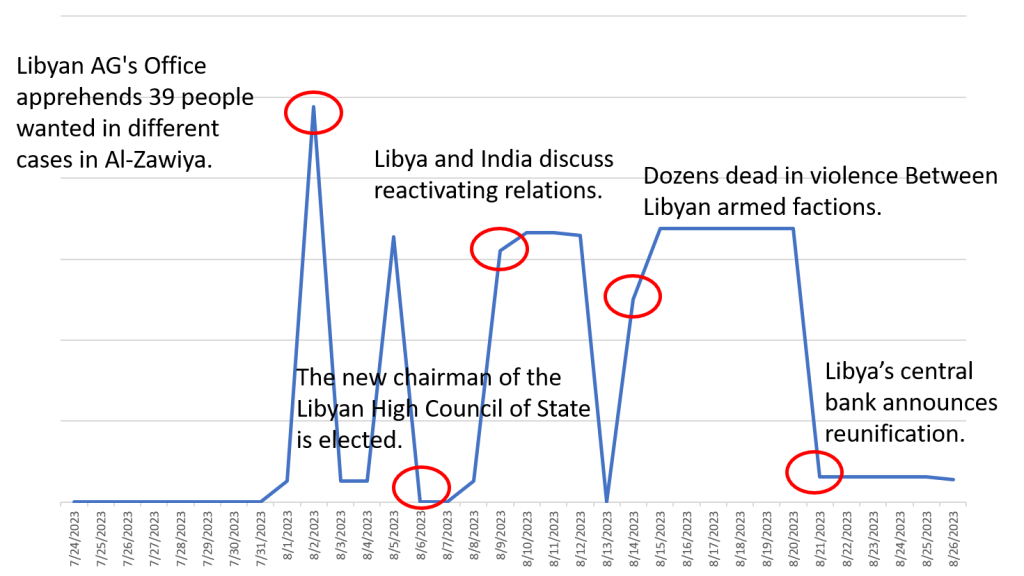
In August, NSFOCUS Global Threat Hunting System spotted an abnormal trend of DDoS attacks against Libya. NSFOCUS Security Labs sorted out the traffic changes of DDoS attacks in August and found that this attack may be related to the turmoil in Libya in August by comparing it with key events in Libya in August. The specific attack trend is as follows:
- August 6: The new chairman of the Libyan High Council of State was elected; the DDoS attacks against Libya spiked on August 2 and 5;
- August 9: A meeting between Libya and India to discuss restoring relations between the two countries, when there was a clear upward trend in DDoS attacks against Libya;
- August 14: An intense armed conflict in Tripoli, Libya’s capital, caused dozens of people to die, and Libya suffered sustained large-scale DDoS attacks from August 14 to 20.
- August 21: The central bank divided by Libya’s civil war reunited, and the trend of DDoS attacks on Libya that day was relatively moderate.
According to observations, the trend of DDoS attacks is closely related to Libya’s complex political environment. Monitoring results show that Libya’s voting network has suffered multiple DDoS attacks, which may undermine voters’ trust in the electoral process and have a certain impact on the outcome of Libya’s presidential election. In this large-scale DDoS attack, the time point of real-world armed forces conflict basically coincides with the trend of DDoS attacks on the cyberspace battlefield. Monitoring revealed also that several government departments in Libya had suffered DDoS attacks, which may have affected the conflict situation to some extent.
II. Typical Attack Events
The DDoS attacks suffered by Libya are mainly carpet-bombing attacks. In this round of DDoS attacks, 97 Class C IP addresses were attacked by carpet-bombing DDoS attacks, including 64 Class C IP addresses in continuous IP segments 41.208.64.0 – 41.208.127.255. This IP segment involves key government infrastructure, education, financial services, the energy industry, and other important sectors, and the attacks are highly targeted.
The carpet-bombing DDoS attack differs from traditional attacks against a single target IP. Attackers use known general attack methods to launch small-traffic DDoS attacks on each IP in the IP segment, so as to exceed the bandwidth limit of access switches and thus affect user services in the entire IP segment. Since the attack traffic of a single IP will not trigger the cleaning threshold of the defense system, this attack method can increase the defense difficulty by escaping the traditional DDoS defense system.
Table 1 IP Segments Suffered Carpet-bombing DDoS Attacks in Libya
| Affected IP Segment | Affected Internet Service Provider |
| 41.208.64.0 – 41.208.127.255 | LTT Autonomous System, Tripoli Libya |
| 62.240.32.0 – 62.240.58.255 62.240.60.0 – 62.240.63.255 | LTT Autonomous System, Tripoli Libya |
| 156.38.62.0/24:256 | Al Madar Al Jadeed Joint Stock Company |
| 160.19.101.0/24:256 | Awal Telecom & Technology |
Government Departments
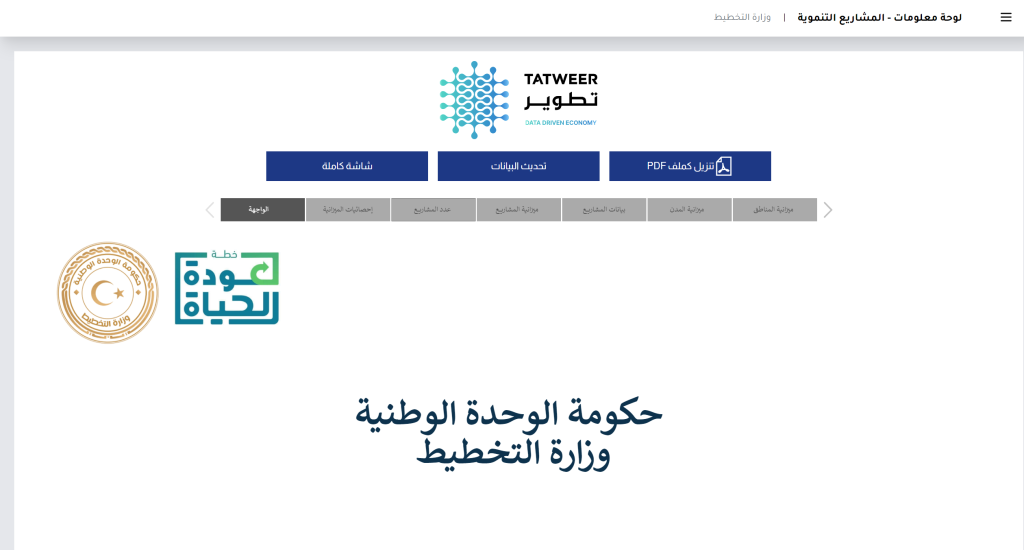
At 20:29:21 on August 1, NSFOCUS’s Global Threat Hunting System detected a reflective DDoS attack against Libya’s Ministry of Planning (planning.gov.ly, 41.208.72.166) using vulnerable services such as DNS, NetAssistant and ONVIF, which lasted until 00:11:43 on August 26.
Libya’s Ministry of Planning is a crucial government entity responsible for outlining the nation’s developmental goals, including many important functions such as national development planning, economic and social research, budgeting and resource allocation, policy formulation and evaluation, international cooperation and aid coordination.
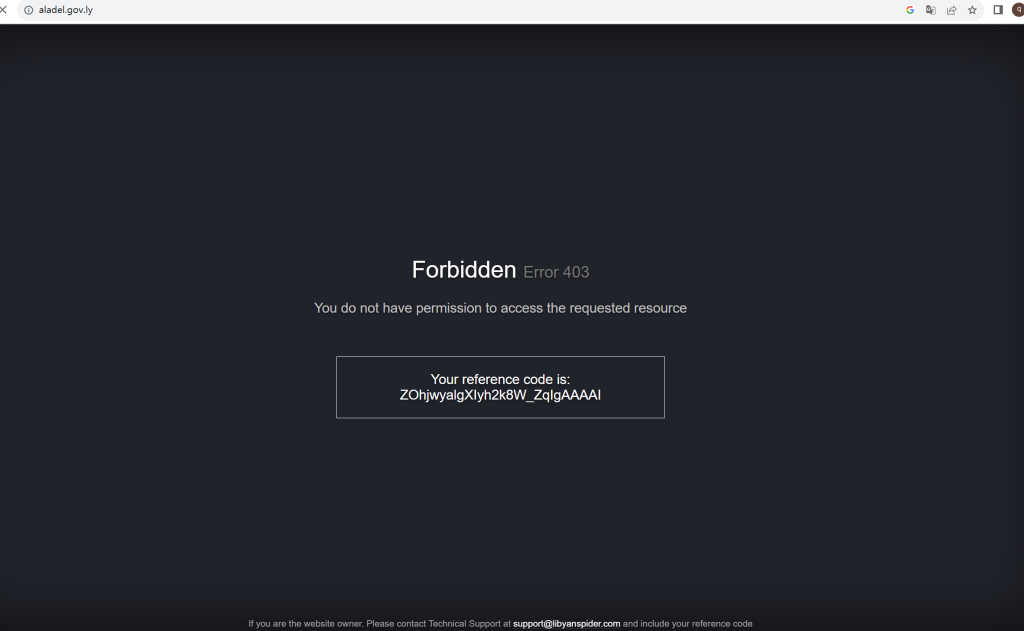
At 20:32:39 on August 1, the system detected a reflective DDoS attack against the official website of the Libya’s Ministry of Justice (aladel.gov.ly, 41.208.72.213) by using vulnerable services such as DNS, NetAssistant and ONVIF. The attack lasted until 00:07:57 on August 26.
Libya’s Ministry of Justice is the government department responsible for overseeing and managing the country’s judicial system. Its responsibilities include formulating and implementing judicial policy, managing the court system, advancing legal reforms, maintaining law and order and ensuring citizens’ legal rights. The Libyan Ministry of Justice plays an important role in Libya’s system of government and is committed to establishing a fair, transparent and effective judicial system that promotes the rule of law and protects the rights and interests of citizens.
Education Sector
Starting at 07:49:15 on 1 August, NSFOCUS’s Global Threat Hunting System detected a reflective DDoS attack using DNS services against the University of Zawia in Libya (zu.edu.ly, 41.208.74.26), which continued until 00:44:49 on 26 August. The University of Zawia is a well-known university located in the city of Zawia, Libya, with rich teaching resources and complete teaching equipment.
Financial Industry
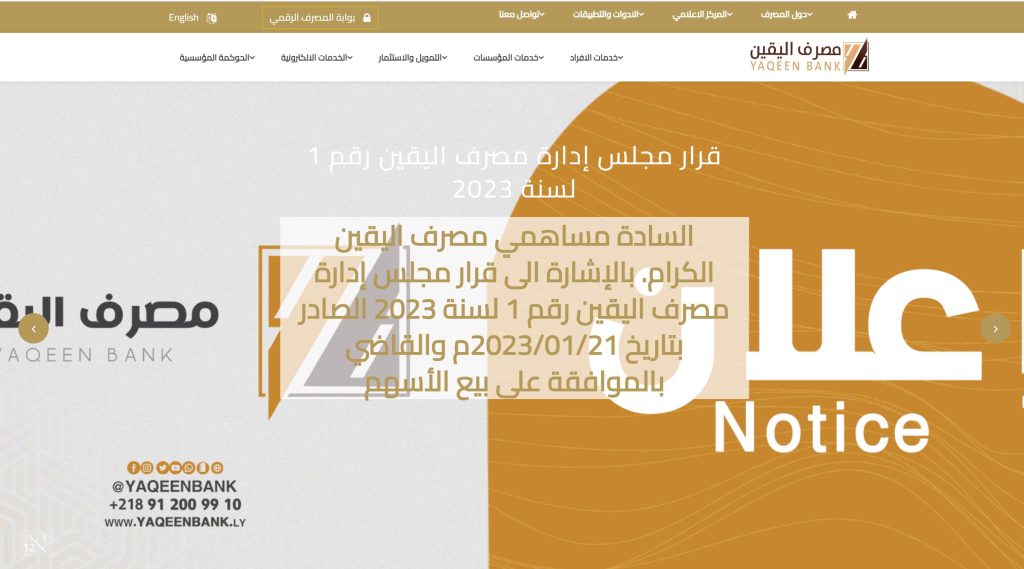
At 20:27:33 on August 1, NSFOCUS’s Global Threat Hunting System detected a reflective DDoS attack against Yaqeen Bank in Libya (yaqeenbank.com, 41.208.71.20) using vulnerable services such as DNS, NetAssistant and ONVIF, which lasted until 00:06:09 on August 26.
Yaqeen Bank is one of the important Islamic banks in Libya and plays an important role in Libya’s financial system. Yaqeen Bank aims to provide innovative and ethical financial solutions for individuals, businesses and institutions in Libya. It was committed to supporting Libya’s economic growth and development while abiding by Islamic financial principles, prohibiting usury and promoting ethical and socially responsible investment practices.
Energy
At 20:26:21 on August 1, NSFOCUS’s Global Threat Hunting System detected a reflective DDoS attack against the website of Libya Petroleum Institute (lpilibya.com, 41.208.72.193) using vulnerable services such as DNS, NetAssistant and ONVIF, which lasted until 14:48 on August 26.
The Libya Petroleum Institute is an important research institution in Libya, focusing on scientific research, technology development and training in the field of oil and gas. Its primary mission is to provide scientific, technical and engineering support for solutions and innovation in Libya’s oil and gas industry. Libya Petroleum Institute has an important position and role in Libya’s oil and gas industry. It plays a key role in promoting the development of petroleum resources, providing technical support and promoting environmental protection, which is of great significance to Libya’s economic and energy development.
Attacks on Election-Related Websites
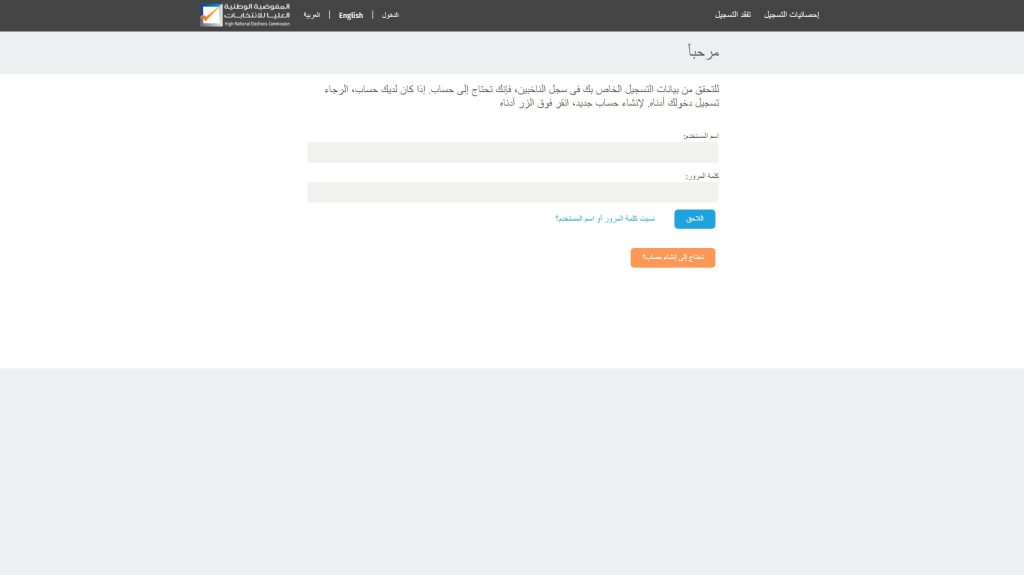
At 07:52:06 on 1 August, NSFOCUS’s Global Threat Hunting System detected a reflective DDoS attack against Libya’s voting network (libyavotes.ly, 41.208.74), which continued until 00:05:48 on 26 August and was suspected of being related to the second round of elections for the chairmanship of Libya’s Supreme National Council of State on 6 August.
III. Libya DDoS Attack Analysis
Victim IP Address Distribution
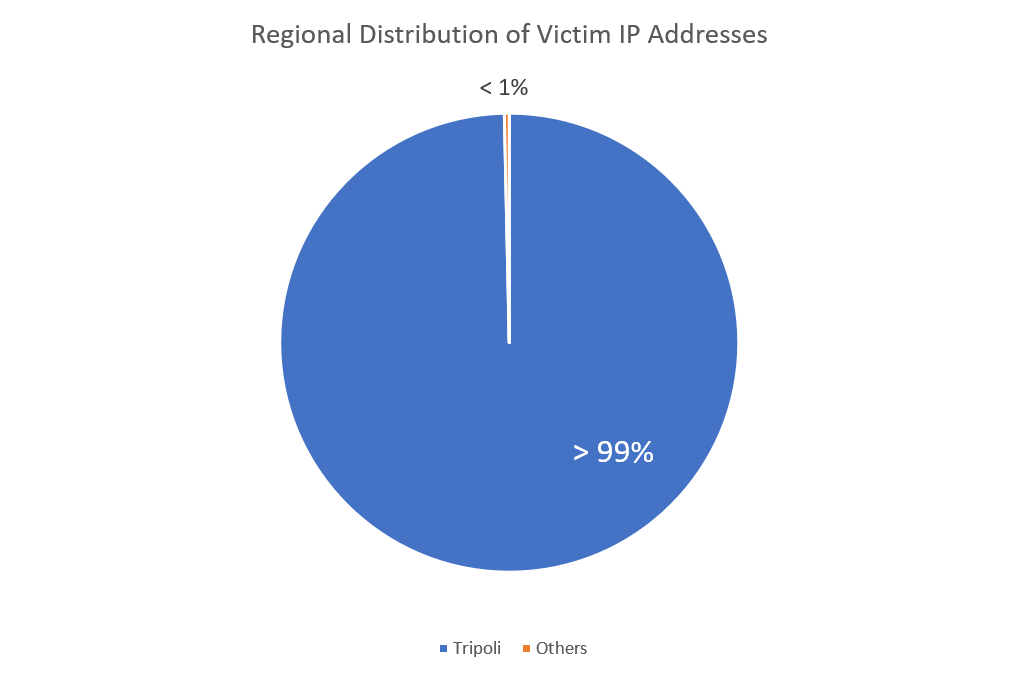
Generally, the geographical distribution of DDoS attacks is positively correlated with the local economic development level and population. In the reflective DDoS attacks against Libya, Tripoli, its capital, as an important political, cultural and economic center of Libya, accounts for more than 99% of the attacks, making it the region where DDoS attacks are most concentrated.
From August 1 to 26, NSFOCUS’s Global Threat Hunting System detected that 25,082 IP addresses/domain names in Libya were attacked by DDoS, accounting for 5.8% of the country’s total of 434,258 public network IP addresses in Libya.
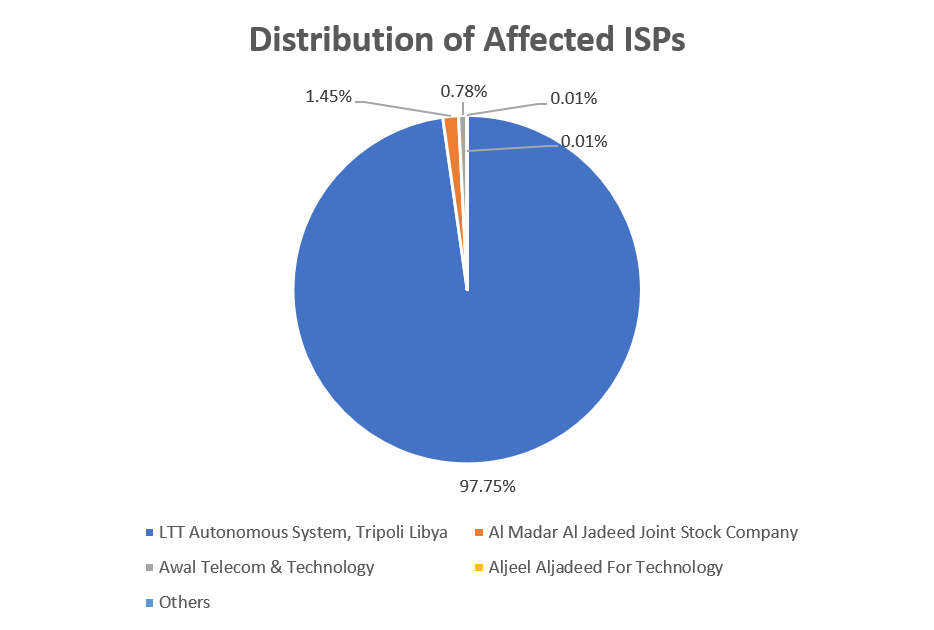
Internet Service Provider Distribution of Victim IP Addresses
With the rapid development of digital technology, network attacks are becoming more and more intense and complex. Internet service providers (ISPs) face an increasing threat of DDoS attacks. In these attack events, the ISPs affected by reflective DDoS attacks in Libya are mainly LTT Autonomous System, accounting for more than 97%.
LTT (Libyan Telecommunication and Technology) is an important telecommunication operator in Libya, headquartered in Tripoli, the capital. As Libya’s national telecommunications company, LTT provides a variety of telecommunications services, including fixed-line telephone, mobile communication, Internet access and data services. It has built and maintained an extensive communications infrastructure throughout Libya to meet the communications needs of individuals, businesses and governments.
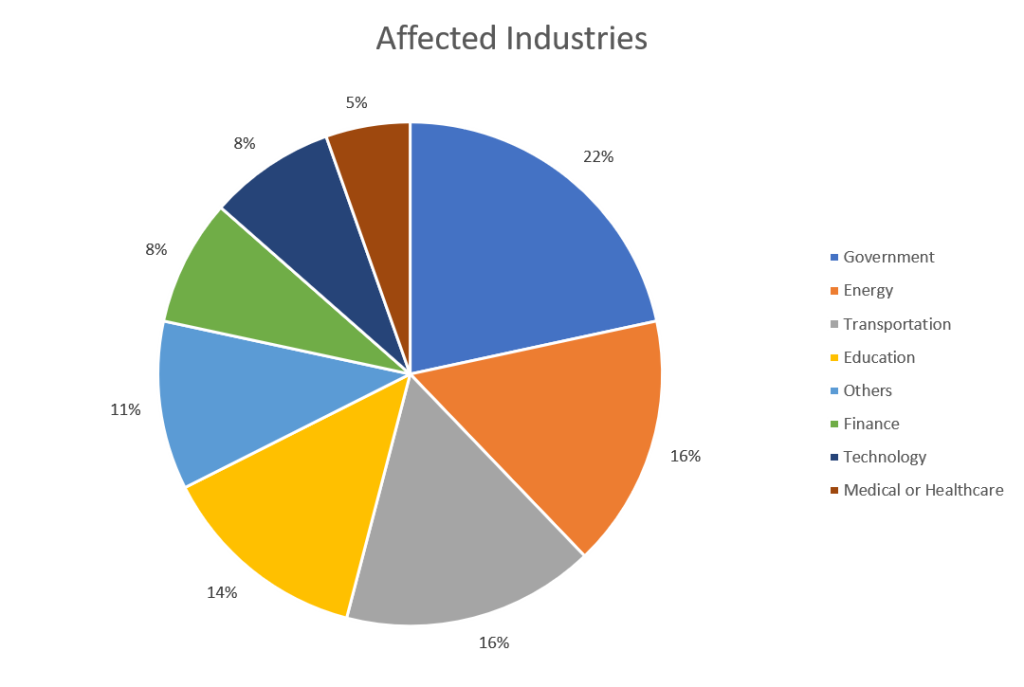
Industry Distribution of Victim IP Addresses
According to NSFOUS’s Global Threat Hunting System data, Libya’s victim IP addresses are distributed across multiple industries. Government, energy, transportation, education and other critical industries suffer serious DDoS attacks, accounting for 68% in total. For these important key industries, DDoS reflection attacks are highly targeted and easily cause the breakdown of target services and serious economic losses.
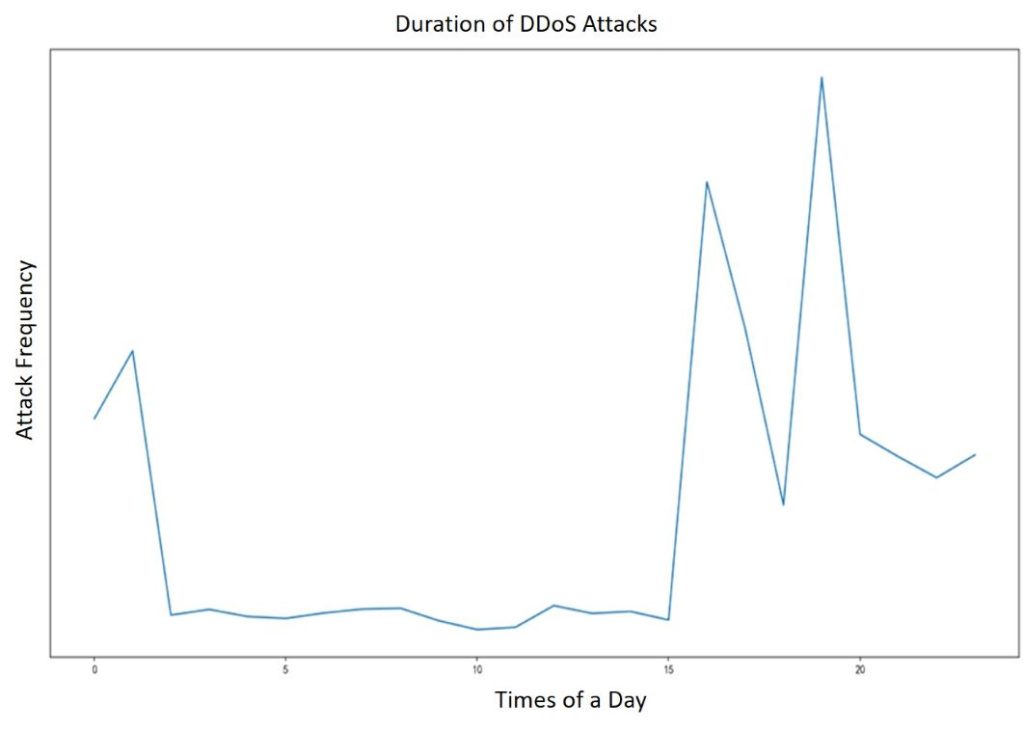
Attack Time Period
Converting the time of these DDoS attacks into local time in Libya, we found that the peak period of attacks occurs between 7:00 and 8:00 p.m., while there are fewer attacks between 2:00 and 15:00 a.m. The active hours of attacks are roughly staggered from the regular working hours (usually 9:00 to 16:00) of government agencies in Libya, which shows that this is an elaborate attack activity.
Specific Victim Domain Name (Partial)
According to the monitoring data of NSFOCUS’s Global Threat Hunting System, the affected domain names involve government websites, energy websites, financial industry and education sectors, which are all important departments in Libya.
Table 2 Some Affected Domain Names in Libya
| Affected Industry | Victim | Domain Name | Attack Start Time |
| Government | Libyan Ministry of Planning | planning.gov.ly | 2023/8/1 20:29 |
| Government | Libyan News Agency | lana.gov.ly | 2023/8/1 07:50 |
| Government | Libyan Ministry of Justice | aladel.gov.ly | 2022/8/1 20:32 |
| Government | Libyan Government Television | tve.gov.ly | 2023/8/1 07:50 |
| Education | University of Zawia | zu.edu.ly | 2023/8/1 07:49 |
| Education | Bright Star University | bsu.edu.ly | 2023/8/1 07:48 |
| Energy Sector | Libyan Petroleum Institute | lpilibya.com | 2023/8/1 20:26 |
| Energy Sector | National Oil Wells Drilling & Workover Company | nwd.ly | 2023/8/1 20:27 |
| Energy Sector | National Oil Corporation | noc.ly | 2023/8/1 07:27 |
| Financial Services | Ithmaar Financial Services Company | etmar.ly | 2023/8/1 07:50 |
| Financial Services | Bank of Yaqeen | yaqeenbank.com | 2023/8/1 20:27 |
IV. Conclusion
As the digital era rapidly evolves, the landscape of cyber threats intensifies, giving rise to a myriad of new attack types. Among the various attack methods, DDoS attacks stand out, preferred by hackers for their potent combination of destructiveness and stealth. They’ve become a significant weapon in the realm of cyber warfare. In view of the large-scale DDoS attacks in Libya, we concluded as follows:
1. The attacks lasted a long time and affected a wide range of industries, potentially related to the unstable situation in Libya.
According to NSFOCUS’s Global Threat Hunting System, from August 1 to now, many important industries such as government, education, finance and energy in Libya have suffered DDoS attacks. It is obvious that this is a long-lasting and highly targeted DDoS attack activity, which is obviously related to the turbulent situation in Libya in August. The Global Threat Hunting System will continuously monitor the dynamic attacks.
2. Critical infrastructure remains the primary target of large-scale DDoS attacks, and oil companies should pay special attention.
In this large-scale DDoS attack activity, the attacker’s primary targets were national critical infrastructure, including government and administrative systems, financial services, energy supply systems, etc. Libya has the largest oil reserves in Africa, and several of its oil companies have suffered DDoS attacks. Should critical infrastructure fail, it would severely jeopardize the smooth operation of the national framework and could induce prolonged detrimental effects on socio-economic growth.