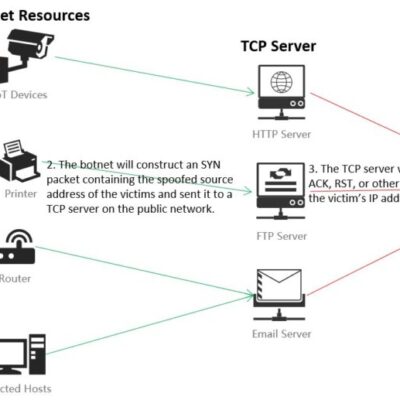
Abstract In August 2021, Kevin Bock and his team from the University of Maryland and the University of Colorado Boulder proposed a new TCP reflective amplification attack method initiated by the middlebox at the USENIX conference. (See more details at https://geneva.cs.umd.edu/papers/usenix-weaponizing-ddos.pdf) In mid-April this year, NSFOCUS spotted that one of...
Category: Blog
NSFOCUS Managed Security Service Case: Response to a Hybrid SYN/ACK Flood Incident
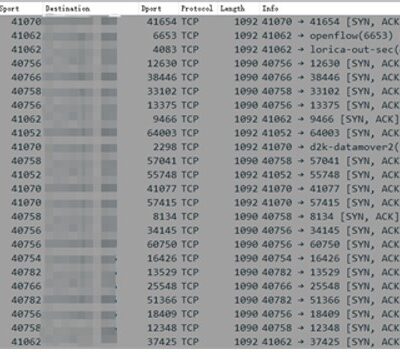
Incident discovered In early 2021, a private cloud service provider in the United States was hit by a massive hybrid SYN Flood attack. As the service provider is a customer of NSFOCUS Cloud DDoS Protection Service and subscribed with Managed Security Service (MSS), the malicious traffic is noticed instantly by...
Multiple OpenSSL Security Vulnerabilities Alerts
Overview Recently, NSFOCUS CERT found that OpenSSL issued a security notice, which fixed multiple security vulnerabilities in OpenSSL products. OpenSSL is an open source software library package. Applications can use this package to communicate securely, avoid eavesdropping, and confirm the identity of the other end of the connection. It is...
NSFOCUS Managed Security Service Case: Protection Policy Tuning for Further Improved Result in a 170Gbps DDoS Incident
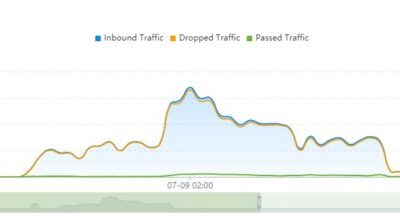
Incident Response On mid-2021, a multinational telecom service provider was attacked by a sudden large-scale DDoS attack with the peak value of 170Gbps with maximum 5Gbps of malicious traffic leakage, with equivalent Mitigation Effect (mitigated malicious traffic/total ingress traffic) stays at least 97%. The service provider did not encounter service...
F5 BIG-IP iControl REST Authentication Bypass Vulnerability (CVE-2022-1388) Alert
Overview Recently, NSFOCUS CERT detected that F5 issued a security bulletin to fix an authentication bypass vulnerability in BIG-IP. Unauthenticated attackers can use the control interface to exploit, through the BIG-IP management interface or its own IP address. Network access to the iControl REST interface to execute arbitrary system commands,...
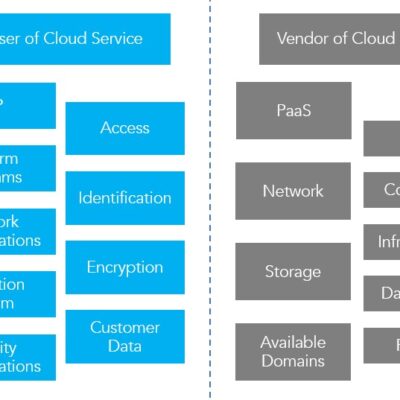
CASB, A Tech “Celebrity” from the Cloud Era
Debut of CASB With cloud computing being a key to industry revolution, more and more enterprises and organizations are discovering the benefits of storing and processing data in the cloud and migrating business systems from local data centers to the cloud. As business systems are migrated to the cloud, the...