After the prior two posts (SASE Popular Science Series – Understanding SD-WAN and SASE: The Relationship Between SD-WAN and SASE), you may already have a basic understanding of SD-WAN, which is used for network connections among users, assets and NSFOCUS Cloud in SASE. What security capabilities does NSFOCUS offer then?...
Category: Blog
Atlassian Confluence Remote Code Execution Vulnerability (CVE-2022-26134) Notification
Overview Recently, NSFOCUS CERT detected that Atlassian officially released a security bulletin for Confluence Server and Data Center OGNL injection vulnerability (CVE-2022-26134). Remote attackers can construct OGNL expressions for injection without authentication to execute arbitrary code on Confluence Server or Data Center, with a CVSS score of 10. At present,...
How to Protect MEC from DDoS Attacks in 5G Networks
NSFOCUS at RSAC 2022 Why MEC is so important to the 5G Network? MEC (Multiple-access Edge Computing) is an important part of the 5G architecture, which is a type of distributed computing used to reduce bandwidth and improve response time, allowing operators to deploy their applications from centralized data centers...
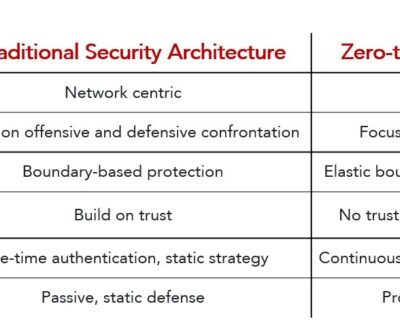
NSFOCUS Empowers ISP/MSP with Zero Trust and Security Access Service Edge (SASE) Solution
Transform One of the most important industry events - RSA Conference 2022 just had its opening both offline and online this year on June 6th, 2022. RSAC 2022 has selected the word “Transform†as the theme this year. It says “The security needs of organizations are expanding, and companies of...
Come and Meet NSFOCUS Next Week at RSA Conference 2022
RSA Conference 2022 will kick off in San Francisco on June 6, 2022. The theme of RSA Conference 2022 is Transform[i], which is a further extension of last year's theme Resilience. Resilience can be the emergency and recovery capabilities of small and medium organizations facing cyber threats, and the survival...
Millions of Devices May Be Affected, and Yeskit Botnet Family Spreads on a Massive Scale by Exploiting F5 BIG-IP Vulnerability
Background On May 4, 2022, F5 issued a security bulletin regarding a remote code execution vulnerability in iControlREST component of BIG-IP products. The CVE number of the vulnerability is CVE-2022-1388. The vulnerability can bypass authentication and remotely execute arbitrary code with a vulnerability score of CVSS up to 9.8....