Overview
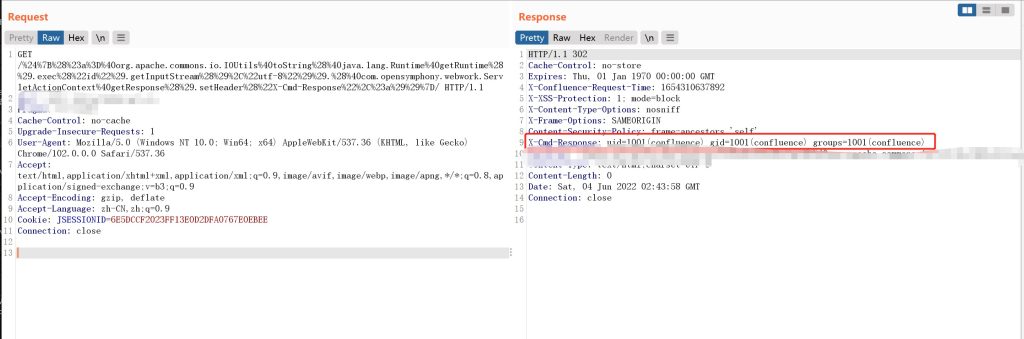
Recently, NSFOCUS CERT detected that Atlassian officially released a security bulletin for Confluence Server and Data Center OGNL injection vulnerability (CVE-2022-26134). Remote attackers can construct OGNL expressions for injection without authentication to execute arbitrary code on Confluence Server or Data Center, with a CVSS score of 10. At present, the details of the vulnerability and the PoC have been publicly disclosed, and it has been detected that it is being exploited in-the-wild. Relevant users are requested to take measures to protect them as soon as possible.
Atlassian Confluence is a professional wiki program produced by Atlassian. It can be used as a knowledge management tool through which collaboration and knowledge sharing among team members can be achieved.
NSFOCUS CERT has successfully reproduced this vulnerability:
Reference link: https://confluence.atlassian.com/doc/confluence-security-advisory-2022-06-02-1130377146.html
Scope of Impact
Affected version
- 1.3.0 <= Confluence Server and Data Center < 7.4.17
- 7.13.0 <= Confluence Server and Data Center < 7.13.7
- 7.14.0 <= Confluence Server and Data Center < 7.14.3
- 7.15.0 <= Confluence Server and Data Center < 7.15.2
- 7.16.0 <= Confluence Server and Data Center < 7.16.4
- 7.17.0 <= Confluence Server and Data Center < 7.17.4
- 7.18.0 <= Confluence Server and Data Center < 7.18.1
Unaffected version
- Confluence Server and Data Center 7.4.17
- Confluence Server and Data Center 7.13.7
- Confluence Server and Data Center 7.14.3
- Confluence Server and Data Center 7.15.2
- Confluence Server and Data Center 7.16.4
- Confluence Server and Data Center 7.17.4
- Confluence Server and Data Center 7.18.1
Vulnerability Detection
Manual detection
Users can check whether the current service is affected by this vulnerability by checking whether the current Confluence version is affected. Click “?” and select “About Confluence” to view the current version.
Vulnerability Mitigation
Officials recommend users to upgrade to the latest version to ensure the security and stability of the service. Download link: https://www.atlassian.com/software/confluence/download-archives
Refer to the table below to upgrade to the corresponding updated version:
| Affected version | Updated version |
| 1.3.0 – 7.4.16 | 7.4.17 |
| 7.13.0 – 7.13.6 | 7.13.7 |
| 7.14.0 – 7.14.2 | 7.14.3 |
| 7.15.0 – 7.15.1 | 7.15.2 |
| 7.16.0 – 7.16.3 | 7.16.4 |
| 7.17.0 – 7.17.3 | 7.17.4 |
| 7.18.0 | 7.18.1 |
Temporary mitigation
If the relevant user is temporarily unable to perform the upgrade operation, the following steps can be taken to alleviate the problem:
For Confluence 7.15.0 – 7.18.0:
If you are running Confluence in a cluster, you will need to repeat this process on each node. You do not need to shut down the entire cluster.
1. Close Confluence.
2. Download xwork-1.0.3-atlassian-10.jar to the Confluence server. Link:
3. Delete or move xwork-1.0.3-atlassian-8.jar out of the Confluence installation directory. file path:
<confluence-install>/confluence/WEB-INF/lib/xwork-1.0.3-atlassian-8.jar
Note: Users are requested not to leave copies of old JAR files in this directory.
4. Copy the downloaded xwork-1.0.3-atlassian-10.jar file to the following directory. Directory path:
<confluence-install>/confluence/WEB-INF/lib/
5. Check whether the permissions of the xwork-1.0.3-atlassian-10.jar file are the same as other files in the same directory.
6. Restart Confluence. Remember, if you’re running Confluence in a cluster, make sure to run this script on all nodes.
For Confluence 7.0.0 – Confluence 7.14.2:
If you are running Confluence in a cluster, you will need to repeat this process on each node. You do not need to shut down the entire cluster.
1. Close Confluence.
2. Download the three files xwork-1.0.3-atlassian-10.jar, webwork-2.1.5-atlassian-4.jar and CachedConfigurationProvider.class to the Confluence Windows server. The links are:
3. Delete or remove xwork-1.0.3.6.jar and webwork-2.1.5-atlassian-3.jar from the Confluence installation directory. The file paths are:
<confluence-install>/confluence/WEB-INF/lib/xwork-1.0.3.6.jar
<confluence-install>/confluence/WEB-INF/lib/webwork-2.1.5-atlassian-3.jar
Note: Users are requested not to leave copies of the above old JAR files in this directory.
4. Copy the downloaded xwork-1.0.3-atlassian-10.jar file to the following directory. Directory path:
 <confluence-install>/confluence/WEB-INF/lib/
5. Copy the downloaded webwork-2.1.5-atlassian-4.jar file to the following directory. Directory path:
<confluence-install>/confluence/WEB-INF/lib/
6. Check that the downloaded new file has the same permissions as other files in the same directory.
7. Change to the following directory
<confluence-install>/confluence/WEB-INF/classes/com/atlassian/confluence/setup
(1) Create a new directory named webwork in the setup directory
(2) Copy CachedConfigurationProvider.class to the created webwork directory. Directory path:
 <confluence-install>/confluence/WEB-INF/classes/com/atlassian/confluence/setup/webwork
(3) Check whether the CachedConfigurationProvider.class file permissions are the same as other files in the same directory.
8. Restart Confluence. Remember, if you’re running Confluence in a cluster, make sure to run this script on all nodes.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.
