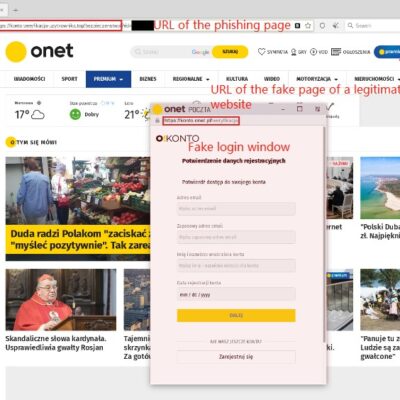
Background Recently, the cyber threat actor known as UNC 1151 group was spotted to use the Browser in the Browser (BitB) technique in its campaigns. This technique is used for phishing attacks by displaying a new browser window containing a fake login panel on the visited website. The window is...
Year: 2022
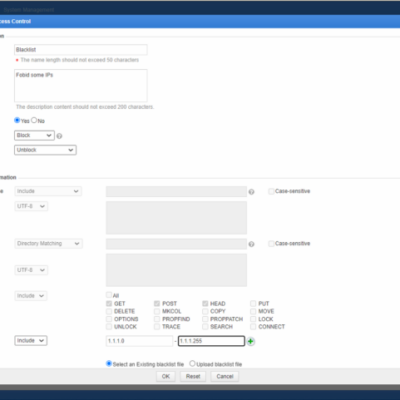
Configuring HTTP Access Control on NSFOCUS WAF
HTTP access control policies can prevent websites from unauthorized and malicious access by controlling over HTTP requests that protected resources respond to. NSFOCUS WAF inspects requests and takes actions when a request matches any of policies you specified. Multiple policies can be applied to a single website and evaluated in...
Critical VMware Product Vulnerability Alerts
Overview Recently, NSFOCUS CERT detected that VMware officially issued a security notice to fix multiple vulnerabilities in products such as VMware Workspace ONE Access, Identity Manager, and VMware vRealize Automation. Attackers can use these vulnerabilities to cause privilege escalation and remote code execution. At present, the official security update has...
NSFOCUS Named as a Sample Vendor for Threat Intelligence Products and Services in 2022 Gartner® report
Company Named in Threat Intelligence Products and Services Category Santa Clara, Calif. August 5, 2022 – We are very proud to announce that NSFOCUS has been named a Sample Vendor in the July 2022 Gartner® Hype Cycle™ for Security Operations in the Threat Intelligence Products and Services category. In this report Gartner...
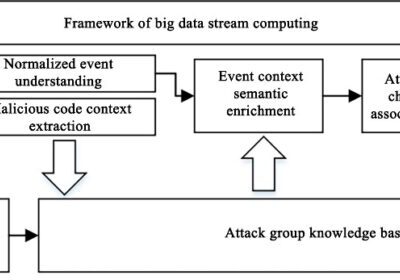
Security Knowledge Graph – APT Group Profiling and Attribution
The security knowledge graph, a knowledge graph specific to the security domain, is the key to realizing cognitive intelligence in cyber security, and it also lays an indispensable technological foundation for dealing with advanced, continuous and complex threats and risks in cyberspace. NSFOCUS will publish a series of articles about...
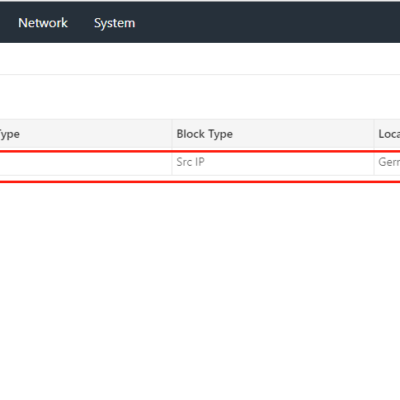
NIPS Blocklist Implementation and Whitelist Priority
The blocklist is matched based on the source IP address, destination IP address, or a combination of source and destination IP addresses of a packet. The blocklist works for TCP and UDP transport layer packets. That is to say, after an IP address is added to the blocklist, the ping...