Overview
Recently, NSFOCUS CERT detected that GeoServer and GeoTools issued security announcements and fixed the XPath expression injection vulnerability in GeoServer and GeoTools (CVE-2024-36404). As the GeoTools library API called by GeoServer will pass the attribute name of element type to commons-jxpath library in an insecure manner, this library can execute arbitrary code when parsing XPath expressions. Unauthenticated attackers can realize remote code execution by sending special inputs to the default installed GeoServer and using multiple OGC request parameters. At present, the vulnerability details and PoC have been disclosed. The affected users are advised to take measures for protection as soon as possible.
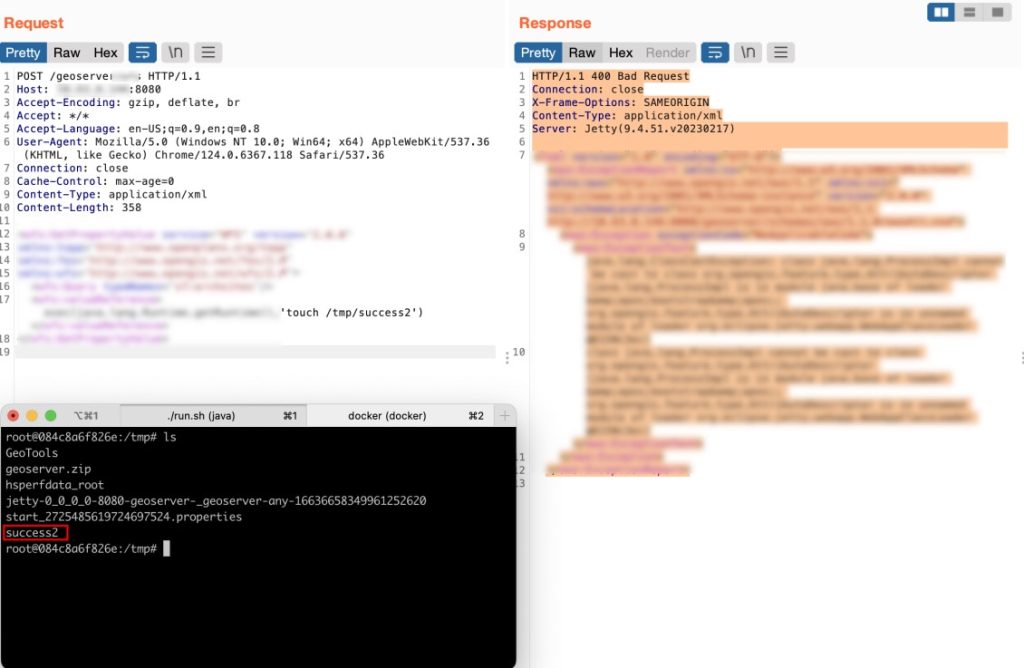
NSFOCUS has successfully reproduced this vulnerability:
Reference link:
https://github.com/geoserver/geoserver/security/advisories/GHSA-6jj6-gm7p-fcvv
https://github.com/geotools/geotools/security/advisories/GHSA-w3pj-wh35-fq8w
Scope of Impact
- GeoServer < 2.23.6
- 2.24.0 <= GeoServer < 2.24.4
- 2.25.0 <= GeoServer < 2.25.2
- GeoTools < 29.6
- 31.0 <= GeoTools < 31.2
- 30.0 <= GeoTools < 30.4
Unaffected version
- GeoServer >= 2.23.6
- GeoServer >= 2.24.4
- GeoServer >= 2.25.2
- GeoTools >= 29.6
- GeoTools >= 30.4
- GeoTools >= 31.2
Mitigation
Official upgrade
1. At present, a new version and security patch have been officially released to fix the above vulnerabilities. Please install updates for protection as soon as possible.
Download link: https://github.com/geoserver/geoserver/tags https://github.com/geotools/geotools/tags
2. You can download the patch versions 2.25.1, 2.24.3, 2.24.2, 2.23.2, 2.21.5, 2.20.7, 2.20.4, 2.19.2, and 2.18.0 from https://geoserver.org to obtain the gt-app-schema, gt-complex, and gt-xsd-core jar files. Replace the corresponding files in WEB-INF/lib of the affected system for restoration.
Other protective measures
If relevant users cannot install updates temporarily, the following measures can be taken for temporary relief: Deleting the gt-complex-x.y.jar file in GeoServer (x.y is the version of GeoTools, such as gt-complex-31.1.jar in GeoServer 2.25.1) will remove vulnerable code from GeoServer, but may compromise some GeoServer functionality. When a gt-complex module is required by an extension in use, it may cause the GeoServer deployment to fail.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.
